CEN/TS 16850:2015
(Main)Societal and Citizen Security - Guidance for managing security in healthcare facilities
Societal and Citizen Security - Guidance for managing security in healthcare facilities
The standard will specify requirements for planning, establishing, implementing, operating, monitoring, reviewing, maintaining and continually improving a documented security management system in healthcare facilities.
Schutz und Sicherheit der Bürger - Leitfaden für das Sicherungsmanagement in Gesundheitseinrichtungen
Sécurité sociétale du citoyen - Lignes directrices pour gérer la sécurité dans les établissements de santé
Družbena varnost in varnost državljanov - Napotki za upravljanje varnosti v zdravstvenih ustanovah
Ta standard določa zahteve za načrtovanje, vzpostavljanje, uvajanje, upravljanje, nadziranje, pregledovanje, vzdrževanje in neprekinjeno izboljševanje dokumentiranega sistema za upravljanje varnosti.
General Information
- Status
- Published
- Publication Date
- 15-Sep-2015
- Technical Committee
- CEN/TC 391 - Societal and Citizen Security
- Drafting Committee
- CEN/TC 391/WG 1 - SMS for Healthcare Facilities
- Current Stage
- 9060 - Closure of 2 Year Review Enquiry - Review Enquiry
- Start Date
- 02-Dec-2022
- Completion Date
- 02-Dec-2022
Overview
CEN/TS 16850:2015 - "Societal and Citizen Security: Guidance for managing security in healthcare facilities" - provides practical guidance for planning, establishing, implementing, operating, monitoring, reviewing and improving a documented security management approach for healthcare settings. The Technical Specification covers protection of people, critical processes, assets and information in hospitals, psychiatric clinics, care homes, outpatient practices and other healthcare facilities. It is not itself a management-system standard but can be applied within one (for example, EN ISO 9001).
Key Topics
The specification addresses the full security lifecycle and technical topics commonly used in healthcare security management:
- Security management policy and creation of a Security Management Plan (SMP)
- Risk management for security: identification, analysis and evaluation aligned with other HCF risk systems
- Governance and leadership: roles, responsibilities and compliance with national legislation
- Operational controls: controlled areas, access control, secure storage, emergency lockdown and vehicle/parking controls
- People-focused measures: staff vetting and training, visitor and patient safety, handling prisoner patients
- Facilities & technology: physical security, building design, fences, CCTV, identity cards, alarms, control rooms
- Incident response & reporting: criteria, incident reports, interfacing with first responders and minimizing recurrence
- Special-case plans: active shooter, child abduction, CBRN incidents, drug diversion, media and aircraft/vehicle threats
- Performance evaluation, exercises and testing to monitor effectiveness and support continual improvement
Practical Applications
CEN/TS 16850:2015 is designed to be actionable for organizations that need to improve or formalize healthcare security:
- Develop or update a Security Management Plan (SMP) and related policies
- Integrate security risk assessments into existing clinical and facility risk frameworks
- Specify technical controls (CCTV, access control, alarms) and operational procedures (lockdown, secure storage)
- Create incident-response procedures and coordinate with emergency services and local law enforcement
- Design security requirements for new construction or refurbishment of healthcare facilities
- Plan training, exercises and performance reviews to validate security measures
Who Should Use It
- Hospital and healthcare facility security managers and directors
- Facility and estates managers, risk managers and compliance officers
- Emergency planners, clinical leads and administrative leaders
- Security consultants, architects and systems integrators working on healthcare projects
- Policymakers and regulators aligning national rules with European guidance
Related Standards
- EN ISO 9001 (quality/management-system integration) - the TS can be implemented as part of such systems.
Note: CEN/TS 16850:2015 was approved for provisional application and may be considered for conversion to a European Standard.
Keywords: CEN/TS 16850:2015, healthcare security, security management, risk management, hospital security, CCTV, access control, incident response, Security Management Plan.
Get Certified
Connect with accredited certification bodies for this standard

BSI Group
BSI (British Standards Institution) is the business standards company that helps organizations make excellence a habit.

TÜV Rheinland
TÜV Rheinland is a leading international provider of technical services.

TÜV SÜD
TÜV SÜD is a trusted partner of choice for safety, security and sustainability solutions.
Sponsored listings
Frequently Asked Questions
CEN/TS 16850:2015 is a technical specification published by the European Committee for Standardization (CEN). Its full title is "Societal and Citizen Security - Guidance for managing security in healthcare facilities". This standard covers: The standard will specify requirements for planning, establishing, implementing, operating, monitoring, reviewing, maintaining and continually improving a documented security management system in healthcare facilities.
The standard will specify requirements for planning, establishing, implementing, operating, monitoring, reviewing, maintaining and continually improving a documented security management system in healthcare facilities.
CEN/TS 16850:2015 is classified under the following ICS (International Classification for Standards) categories: 11.020 - Medical sciences and health care facilities in general; 11.020.99 - Other standards related to health care in general; 13.310 - Protection against crime; 91.040.10 - Public buildings. The ICS classification helps identify the subject area and facilitates finding related standards.
CEN/TS 16850:2015 is available in PDF format for immediate download after purchase. The document can be added to your cart and obtained through the secure checkout process. Digital delivery ensures instant access to the complete standard document.
Standards Content (Sample)
SLOVENSKI STANDARD
01-november-2015
Družbena varnost in varnost državljanov - Napotki za upravljanje varnosti v
zdravstvenih ustanovah
Societal and Citizen Security - Guidance for managing security in healthcare facilities
Schutz und Sicherheit der Bürger - Leitfaden für das Sicherungsmanagement in
Gesundheitseinrichtungen
Sécurité sociétale du citoyen - Lignes directrices pour gérer la sécurité dans les
établissements de santé
Ta slovenski standard je istoveten z: CEN/TS 16850:2015
ICS:
03.100.01 Organizacija in vodenje Company organization and
podjetja na splošno management in general
11.020.99 Drugi standardi v zvezi z Other standards related to
zdravstvom na splošno health care in general
13.310 Varstvo pred kriminalom Protection against crime
2003-01.Slovenski inštitut za standardizacijo. Razmnoževanje celote ali delov tega standarda ni dovoljeno.
CEN/TS 16850
TECHNICAL SPECIFICATION
SPÉCIFICATION TECHNIQUE
September 2015
TECHNISCHE SPEZIFIKATION
ICS 13.310; 91.040.10; 11.020
English Version
Societal and Citizen Security - Guidance for managing
security in healthcare facilities
Sécurité sociétale du citoyen - Lignes directrices pour Schutz und Sicherheit der Bürger - Leitfaden für das
gérer la sécurité dans les établissements de santé Sicherungsmanagement in Gesundheitseinrichtungen
This Technical Specification (CEN/TS) was approved by CEN on 27 July 2015 for provisional application.
The period of validity of this CEN/TS is limited initially to three years. After two years the members of CEN will be requested to
submit their comments, particularly on the question whether the CEN/TS can be converted into a European Standard.
CEN members are required to announce the existence of this CEN/TS in the same way as for an EN and to make the CEN/TS
available promptly at national level in an appropriate form. It is permissible to keep conflicting national standards in force (in
parallel to the CEN/TS) until the final decision about the possible conversion of the CEN/TS into an EN is reached.
CEN members are the national standards bodies of Austria, Belgium, Bulgaria, Croatia, Cyprus, Czech Republic, Denmark, Estonia,
Finland, Former Yugoslav Republic of Macedonia, France, Germany, Greece, Hungary, Iceland, Ireland, Italy, Latvia, Lithuania,
Luxembourg, Malta, Netherlands, Norway, Poland, Portugal, Romania, Slovakia, Slovenia, Spain, Sweden, Switzerland, Turkey and
United Kingdom.
EUROPEAN COMMITTEE FOR STANDARDIZATION
COMITÉ EUROPÉEN DE NORMALISATION
EUROPÄISCHES KOMITEE FÜR NORMUNG
CEN-CENELEC Management Centre: Avenue Marnix 17, B-1000 Brussels
© 2015 CEN All rights of exploitation in any form and by any means reserved Ref. No. CEN/TS 16850:2015 E
worldwide for CEN national Members.
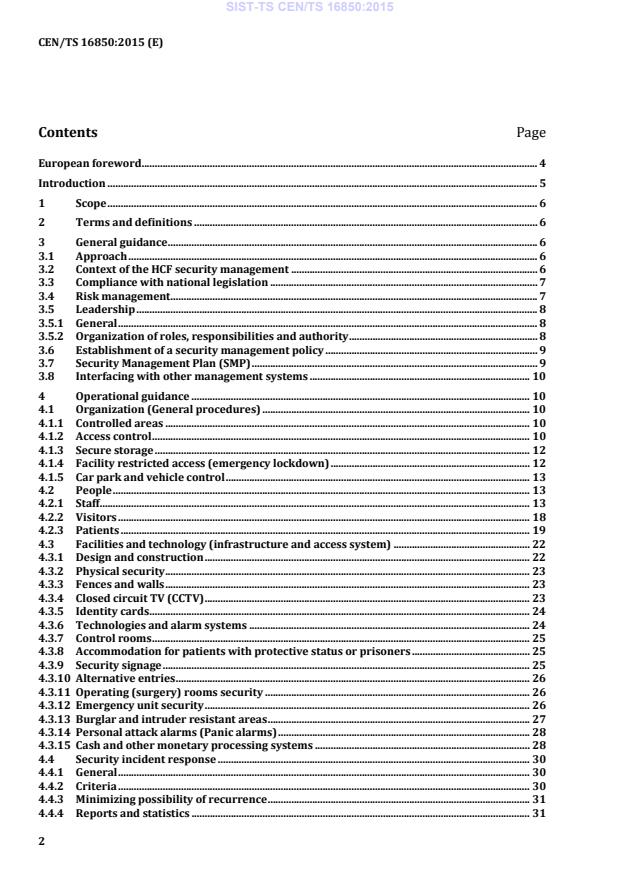
Contents Page
European foreword . 4
Introduction . 5
1 Scope . 6
2 Terms and definitions . 6
3 General guidance . 6
3.1 Approach . 6
3.2 Context of the HCF security management . 6
3.3 Compliance with national legislation . 7
3.4 Risk management . 7
3.5 Leadership . 8
3.5.1 General . 8
3.5.2 Organization of roles, responsibilities and authority . 8
3.6 Establishment of a security management policy . 9
3.7 Security Management Plan (SMP) . 9
3.8 Interfacing with other management systems . 10
4 Operational guidance . 10
4.1 Organization (General procedures) . 10
4.1.1 Controlled areas . 10
4.1.2 Access control . 10
4.1.3 Secure storage . 12
4.1.4 Facility restricted access (emergency lockdown) . 12
4.1.5 Car park and vehicle control . 13
4.2 People . 13
4.2.1 Staff . 13
4.2.2 Visitors . 18
4.2.3 Patients . 19
4.3 Facilities and technology (infrastructure and access system) . 22
4.3.1 Design and construction . 22
4.3.2 Physical security . 23
4.3.3 Fences and walls . 23
4.3.4 Closed circuit TV (CCTV) . 23
4.3.5 Identity cards . 24
4.3.6 Technologies and alarm systems . 24
4.3.7 Control rooms . 25
4.3.8 Accommodation for patients with protective status or prisoners . 25
4.3.9 Security signage . 25
4.3.10 Alternative entries . 26
4.3.11 Operating (surgery) rooms security . 26
4.3.12 Emergency unit security . 26
4.3.13 Burglar and intruder resistant areas . 27
4.3.14 Personal attack alarms (Panic alarms) . 28
4.3.15 Cash and other monetary processing systems . 28
4.4 Security incident response . 30
4.4.1 General . 30
4.4.2 Criteria . 30
4.4.3 Minimizing possibility of recurrence . 31
4.4.4 Reports and statistics . 31
4.4.5 Incident report . 31
4.4.6 Interfacing with first responders and emergency management . 31
4.4.7 Targeted violence . 32
4.5 Plans for special cases . 33
4.5.1 Child abduction . 33
4.5.2 CBRN incident response . 33
4.5.3 Prisoner patients . 33
4.5.4 Offensive weapons and other dangerous equipment . 33
4.5.5 Active shooter . 34
4.5.6 Drug diversion and security of CBRNE substances . 35
4.5.7 Vehicle and aircraft security . 36
4.5.8 Media . 36
5 Performance evaluation . 37
5.1 General . 37
5.2 Management review . 37
6 Exercise and testing . 37
Bibliography . 39
European foreword
This document (CEN/TS 16850:2015) has been prepared by Technical Committee CEN/TC 391
“Societal and Citizen Security”, the secretariat of which is held by NEN.
Attention is drawn to the possibility that some of the elements of this document may be the subject of
patent rights. CEN [and/or CENELEC] shall not be held responsible for identifying any or all such patent
rights.
According to the CEN-CENELEC Internal Regulations, the national standards organizations of the
following countries are bound to announce this Technical Specification: Austria, Belgium, Bulgaria,
Croatia, Cyprus, Czech Republic, Denmark, Estonia, Finland, Former Yugoslav Republic of Macedonia,
France, Germany, Greece, Hungary, Iceland, Ireland, Italy, Latvia, Lithuania, Luxembourg, Malta,
Netherlands, Norway, Poland, Portugal, Romania, Slovakia, Slovenia, Spain, Sweden, Switzerland,
Turkey and the United Kingdom.
Introduction
Security of healthcare facilities is very important for effective and high quality medical treatment. It is a
very wide area and the primary objective of this Technical Specification (TS) is to provide all
responsible persons, within healthcare facility, with guidelines on how to manage security.
This is not a management system standard. This TS is giving an opportunity to be more specific in
proposed security measures, which leads to better security of healthcare facility staff, patient and other
people, who are visiting such a facility. There is also an important fact that this TS is not a closed project
and we are expecting further development of this document.
Management of security in healthcare facilities is a dynamic process and this TS proposes guidelines,
which help responsible persons have a choice from different techniques for how to improve security.
It is important to emphasize that across the European Union there are several regulatory and legislative
limitations for use of security techniques and technologies, so it is important to take these limitations
into account. Use of the guidelines may vary based on the health care system in each country of the
European Union.
1 Scope
This Technical Specification provides guidance for managing security in healthcare facilities. It covers
the protection of people, critical processes, assets and information against security threats.
This Technical Specification applies to hospitals and places that provide healthcare services, such as -
but not limited to - psychiatric clinics, homes for the elderly and institutions for the handicapped. It also
applies to self-employed practicing healthcare professionals. It does not apply to occupational health
and safety and fire safety.
This Technical Specification is not a management system standard. However it can be applied as part of
a management system, such as with EN ISO 9001.
2 Terms and definitions
For the purposes of this document, the following terms and definitions apply.
2.1
controlled area
area which has specific controls to restrict access to authorized persons only
2.2
targeted violence
situation where an individual, individuals or group are identified at risk of violence, usually from
another specific individual such as in cases involving domestic violence
Note 1 to entry: Often, the perpetrator and target are known to each other prior to an incident.
3 General guidance
3.1 Approach
Security management for a healthcare facility (HCF) should:
— be consistent with other policies;
— be documented, implemented and maintained;
— be visibly endorsed by top management;
— provide a framework which enables the specification of security management objectives and
targets;
— be consistent with the organization’s risk management;
— be communicated to all employees, patients and other stakeholders; and
— respect the rights of patients and visitors.
3.2 Context of the HCF security management
The HCF should determine internal and external issues that are relevant to its purpose and that affect
its ability to achieve the intended level of security within the HCF.
The context should be taken into account when establishing, implementing, maintaining and continually
improving the HCF security management (system).
The HCF should identify and document:
— the HCF’s activities, functions, services, products, partnerships, supply chains, resources,
relationships with interested parties, and their relationship with security management; and
— links between the HCF security management system design and the HCF’s other policies, including
its other management strategies and implemented management systems.
3.3 Compliance with national legislation
The HCF should establish and maintain procedure(s) to:
— identify legal, regulatory, and other requirements to which the HCF subscribes related to the HCF
security management;
— determine legal restrictions on certain security procedures based on jurisdiction; and
— determine how these requirements apply to its HCF security management.
The HCF should document this information and keep it up to date.
The HCF should ensure that applicable legal, regulatory and other requirements to which the
organization subscribes are considered in developing, implementing and maintaining its HCF security
management.
NOTE 1 These procedures are in most cases an integral part of management system standards, such as quality
management systems, e.g. EN ISO 9001:2008. In this case, the organization should ensure that specific
requirements for security-related issues, such as requirements for technologies etc. are included.
NOTE 2 The mission of HCF personnel is to provide healthcare and not law enforcement.
3.4 Risk management
Security management is risk management, therefore the security management system should be aligned
with other risk management systems within the HCF. The HCF should establish, implement and
maintain a formal and documented risk assessment process for security risk identification, analysis and
evaluation, in order to:
— identify operational security risks caused by intentional, unintentional and human threats that have
a potential for direct or indirect consequences on the HCF’s objectives, tangible and intangible
assets, and interested parties (threat, vulnerability, and criticality analysis);
— systematically analyse risk likelihood and consequence, and set risk criteria; and
— systematically evaluate and prioritize security risk controls and measures and their related costs.
The HCF should:
— document and keep this information up to date and secure;
— periodically review whether the risk assessment methods are effective for security risk
management;
— re-evaluate risks within the context of changes within the HCF, or made to the HCF’s operating
environment, procedures, functions, services, partnerships, and supply chains;
— evaluate the direct and indirect benefits and costs of options to manage risk and enhance reliability
and security;
— evaluate the actual effectiveness of security risk management measure options;
— ensure that the prioritized risks and impacts are taken into account in establishing, implementing
and operating its HCF security management; and
— evaluate the effectiveness of security risk controls and measures.
NOTE For methods of risk assessment and risk analysis see IEC 31010.
The HCF should establish, implement and maintain a formal and documented communication and
consultation process, consistent with operational security, with all stakeholders in the risk assessment
process to ensure that:
— security risks are adequately identified and communicated;
— interests of other internal and external interested parties are understood;
— dependencies and linkages with subcontractors, third parties providing outsourcing and those
within the supply chain are understood;
— the risk assessment process interfaces well with other management disciplines; and
— risk assessment is being conducted within the appropriate internal and external context and
parameters relevant to the HCF and its interested parties.
The risk assessment should identify activities, operations and processes that need to be managed.
Outputs should include a prioritized risk register identifying measures to mitigate risk and justification
for risk acceptance.
3.5 Leadership
3.5.1 General
Top management should demonstrate leadership and commitment with respect to the HCF security
management by:
— making security management one of the responsibilities of one of the members of top management;
— appointing a responsible person for the healthcare security management with leadership and
technical competence (see 3.5.2);
— supporting relevant management roles to demonstrate their leadership as it applies to their areas
of responsibility (see 3.6);
— ensuring that the resources needed for the HCF security management are available (see 3.6);
— supporting the planning of security measures (see 3.7); and
— directing and supporting persons to contribute to the effectiveness of the HCF security
management (see 4.2.1.6 and 4.2.1.8).
3.5.2 Organization of roles, responsibilities and authority
Top management should ensure that the responsibilities and authorities for relevant roles are assigned
and communicated within the organization.
Top management should ensure that:
— an administrative person, designated by leadership, is charged with primary responsibility for the
security function, e.g. a security manager; and
— provision is made for the professional development of the Security manager.
NOTE Membership in at least one professional security organization and participation in security educational
programs is strongly encouraged.
The security manager:
— should have demonstrated competence in security risk management and knowledge of the
healthcare industry;
— is involved in the planning and building phases of all new facility construction and renovations;
— possesses policy-making authority, and will be in charge of the reviewing and approval process of
the HCF;
— plays a critical leadership role in Healthcare Facilities (HCFs) security management; and
— possesses the authority to immediately and independently address any imminent threat that may
result in serious bodily injury, death, or significant loss of property. This authority should include
standing authorization to deploy and implement timely interim measures.
3.6 Establishment of a security management policy
A security management policy should clearly state the organization's objectives for, and commitment to,
security management, and typically addresses the following:
— the organization's rationale for managing security;
— articulate its objectives related to healthcare facility security;
— links between the organization's objectives and policies and the security management policy;
— accountabilities and responsibilities for managing security;
— the way in which conflicting interests are dealt with;
— commitment to make the necessary resources available to assist those accountable and responsible
for managing security;
— the way in which security management performance will be measured and reported; and
— commitment to review and improve the security management policy and framework periodically
and in response to an event or change in circumstances.
The security management policy should be communicated appropriately.
3.7 Security Management Plan (SMP)
Organizations should develop a Security Management Plan (SMP), based on their risk assessment. The
SMP should include preventive, protective, mitigation, response and recovery measures designed to
provide a safe and secure environment.
The plan should be based on the risk assessment and needs of the HCF.
The SMP should include, but not be limited to:
— a security program mission statement;
— a statement of program authority (e.g. a facility organization chart depicting reporting levels);
— the identification of security sensitive areas;
— an overview of security program duties and activities;
— the documentation system in place (i.e. records & reports);
— a training and exercise program for the security staff and all other staff;
— planned liaison activities with local public safety agencies and other HCFs as appropriate;
— a security organizational chart; and
— a copy of the most recent annual program, evaluation report and plan for improvement.
The SMP should be evaluated periodically, and modified as required. Periodical reviews should be
documented.
3.8 Interfacing with other management systems
Top management and the security managers should ensure that:
— the HCF security management system operates conforming to the requirements of other
implemented management system standards; and
— the performance of the HCF security management is reported to top management.
The HCF should align the security management with other quality, safety and security management
systems, such as Information Security Management System (ISMS).
4 Operational guidance
4.1 Organization (General procedures)
4.1.1 Controlled areas
Based on the risk assessment, certain areas of the HCF are determined to be a controlled areas. A
controlled area may be part or all of a burglar or intruder resistant area. A controlled area should have
means of:
— denying entry to unauthorized persons;
— identifying authorized persons;
— logging entry and - where required - exit of authorized persons; and
— alerting the appropriate authorities in the event of a forced entry or a door opened too long based
on the set down criteria.
4.1.2 Access control
4.1.2.1 General
Access control (entry/exit) - using positive personal identification - is essential for controlled areas. The
methods actually available to control the access are as follows:
— key lockable door using a key management which is strictly controlled by limiting the number of
authorized users and the means of duplicating the keys;
— visual recognition of authorized people (suitable for access control to small areas which are always
occupied, or areas where entry is supervised by a trusted custodian who knows the occupants of
the area well enough to identify them, or is able to do so with the assistance of a security pass or ID
card);
— mechanical code locks (suitable for access control of small to medium areas which are sometimes
left unoccupied);
— electronic access control systems (suitable for larger areas, including several networked areas,
whether occupied or not, or where a reliable and secure audit of entry and exit is required. Passes
or identity cards authenticate bona fide authorized persons;
The highest level of security is provided by biometric recognition systems using personal
characteristics such as fingerprint, hand geometry or eye retina for recognition. For effective
electronic access control, the quality of locking mechanisms, door closers and other peripheral
equipment shall be commensurate with the quality of the recognition system and level of control
required.
— specific access control systems such as interlocking doors.
NOTE Cards (e.g. identity cards) need to be clearly legible.
For other open areas, consideration should be given to the installation of entry/exit control measures to
ensure that:
— only authorized people have unimpeded entry/exit to the building or area;
— visitors are logged and escorted; and
— valuable or vital assets cannot be removed from the controlled area without proper authority.
4.1.2.2 Level of access control
When designing or implementing access control, the HCF should consider:
— the classification or value of material handled or stored;
— the location, size and layout of the area;
— the number of entry/exit points; and
— the number of staff authorized to have access to the area.
4.1.2.3 Access control requirements
Regardless of the entry/exit control method used, persons should only be given the means for
entry/exit if they have:
— a legitimate need for unescorted entry/exit to the area; and
— the appropriate security clearance.
4.1.2.4 Identity cards - receipt and conditions
The issuing process of identity cards should be documented and persons receiving identity cards should
be made aware of the need to:
— wear the identification where required;
— safeguard the identity card;
— report its loss to the issuing responsible person immediately;
— return the identity card on cessation of visits or employment; and
— follow the procedures for its use.
4.1.3 Secure storage
The level of secure storage required to adequately protect classified, sensitive and valuable assets can
only be determined following a risk assessment.
The following factors for the risk assessment of storage help to select the appropriate security container
or secure room:
— the level of classification of information;
— the value and importance of the property to be stored;
— the location (e.g. within a burglar/intruder resistant area);
— the structure and location of the container/building; and
— the entry/exit control system of this area.
4.1.4 Facility restricted access (emergency lockdown)
Emergency situations may require a HCF to immediately or progressively be “locked down" to mitigate
possible harm to patients, staff, and visitors and to protect property. Lockdown situations may result
from internal or external events such as a hostage incident, active shooter, infant abduction, forensic
patient escape, or a man-made or natural disaster.
Restricting movement of individuals into, throughout and out of the HCF during an emergency can be
critical to the safety of patients and staff and to the protection of life-saving supplies, equipment and
infrastructure.
A security risk assessment should be undertaken whenever a lockdown policy is developed or
reviewed. Situations identified by the risk assessment should be evaluated based upon identified
emergency scenarios within the HCFs locality.
Restricted access protocols should consider ‘in place’ physical security measures (electronic access
control, traffic barriers, etc.), on-duty staff members (security and HCF staff) and the availability of
supplemental staff from external resources.
Restricted access protocols should address the following:
— How to limit access for the entire facility. This may be accomplished in progressive stages and may
involve the facility incident command structure;
— The persons authorized to implement the restricted access plan;
— Controlling access to security sensitive areas and high risk departments;
— The process to identify HCF staff and others (fire, law enforcement, public health) that require
access;
— Communication methods for supplemental and on duty personnel;
— Methods for managing internal and external communications;
— Establishing and maintaining perimeters and visitor protocols;
— Obtaining additional security and or law enforcement staff;
— Establishing secure passage routes and shuttle transportation for HCF staff;
— Management of the internal environment during lockdown; and
— Reversing the lockdown and opening areas.
Controlled access plans should be tested and evaluated as part of disaster drills and exercises with
other HCFs and other community agencies with patient representatives. The inclusion of patient
representatives included in these exercises should be considered.
4.1.5 Car park and vehicle control
A program for the control and space allocation of vehicles should be developed and maintained by the
HCF.
Measures for identification of authorized vehicles and access control should be implemented.
EXAMPLES A label, decal or access card system may be used.
Traffic flow and numbers should be investigated and road usage should be optimized with directional
movement restrictions, thereby encouraging separate entry and exit points where possible. Car park
layout and allocations should always consider the relevance of shift-work on parking.
Parking areas should be regularly patrolled by security, and a security escort should be offered between
the workplace and parking areas.
Road use and design shall also make provisions for emergency vehicles and restricted parking spaces
should only be allocated for emergency services vehicles or staff on call for emergency procedures.
Where the risk to personnel is high, security measures such as CCTV and out-door security technologies
and alarms should be used to improve security and safety. Staff and visitor parking should be separate.
4.2 People
4.2.1 Staff
4.2.1.1 Staff selection & screening
The HCF should have a documented program for pre-employment background screening, which
consists of, but is not limited to practice and procedures.
The HCF should uphold legal compliance with law and regulations with regards to screening.
The HCF should appoint the departments/positions who conduct the pre-employment background
screening.
The HCF should repeat the background screening periodically.
The HCF should involve at least the following departments:
— human resources;
— security;
— business or process owners and managers; and
— legal departments.
The HCF should appoint a position, which is responsible for the overall pre-employment background
screening program.
The HCF should appoint positions and departments for whom pre-employment background screening
is mandatory.
The structure of a pre-employment background screening should consist of, but should not be limited
to, a standard employment application form. This application form should contain at least:
— current employment;
— residence address history;
— date of birth;
— employment history;
— prior criminal history (in line with national privacy regulations);
— educational history;
— inquiry as to whether applicant has legal right to work in specific country; and
— disclosure and authorization for background screening.
Applications should be reviewed for completeness and if minimum requirements of the position are
met.
The HCF should perform job interviews. Job interviews are needed to:
— convey critical information to the applicant in order to discourage inappropriate applicants;
— allow for the transfer of missing information from the applicant to the employer;
— permit an assessment of the candidate.
The HCF should maintain several levels of background screening in accordance to the position and/or
department. The HCF should periodically review the screening of persons working on behalf of the
organization.
4.2.1.2 Wearing of identity cards
The HCF should consider the benefits of having staff conspicuously wear their identity cards at all times
whilst in the area for which the identity card is valid. The benefits include the following:
— positive identification of authorized people;
— raising of security consciousness amongst staff;
— assistance in quickly identifying a person who has illegally entered the area;
— clear identification of visitors (i.e. not wearing an authorized identity card);
— stopping unauthorized people appearing as authorized by the simple removal of a visitor's identity
card, or not wearing an identity card at all.
Those who cannot wear identity card because of the requirements of their duties should carry them and
be able to produce them on request.
NOTE Identity cards need to be clearly legible.
4.2.1.3 Workplace violence
The HCF is advised to implement a protocol addressing workplace violence prevention and response.
The protocol should be elaborated based on the following components of an effective safety and
security program, which also apply to prevent workplace violence:
— management commitment and employee involvement;
— worksite analysis;
— hazard reduction and response;
— training;
— record keeping and program evaluation.
A multidisciplinary team should be appointed to develop and maintain the workplace violence program.
The team should have support by the HCF’s top management.
Security should have a clearly defined role in assisting in the HCF's workplace violence program. The
team should receive orientation and training in evaluating and responding.
The HCF should establish a system such as patient record flags, electronic warnings, chart tags, log
books, or verbal census reports that identify patients and clients who may present assaultive or
threatening behavioural challenges.
The HCF should establish policies and procedures prohibiting the carrying of firearms and other
weapons onto the facility with the exception of authorized law enforcement personnel, weapons carried
by the facility’s security and others specifically authorized, such as armoured car personnel.
The HCF is encouraged to post warnings at entrances to the facility as to how violence against staff or
other patients/visitors will be dealt with.
The HCF should incorporate targeted Violence protocols into its Violence in the Workplace policy or
create a separate policy for preventing and responding to targeted violence (including domestic
violence).
4.2.1.4 Contracting
Specific security requirements should be taken into account in contract documents, purchase
agreements and service contracts.
4.2.1.5 Home health security
HCFs providing home health services will develop a security plan to protect staff travelling into the
community to perform their job duties.
HCFs should have a risk assessment process in place, which would allow home health staff to determine
appropriate safeguards associated with a community visit. The risk assessment process may include a
community crime assessment, previous history of the client and use of a location based threat
assessment.
Home health staff should be provided with education and training regarding risk identification and
preventive safeguards. Training should include information and guidelines on security awareness,
crime prevention and defensive measures. Training records should be maintained.
HCFs should develop a communication process to protect home health staff. This should include
proactive check-in and check-out procedures, which would allow staff to make contact during the shift
to help ensure their safety. Cell phones, automated check-in procedures or GPS devices may be
considered as appropriate to facilitate this process.
Security or other appropriate escorts should be available to home health staff providing services in
areas or situations deemed high risk, or as individual situations warrant.
Procedures should be in place for home health staff to follow in the event of a security incident or a
situation in which they have a concern for their security.
HCFs should have a process in place how to respond to missed check-ins.
4.2.1.6 Role of security personnel in patient management
The HCF will develop policies and procedures that identify the responsibilities and scope of activities of
security personnel in performing patient intervention activities. Patient intervention activities include
performing patient watches, holds, restraints and seclusions relative to the medical evaluation or
treatment of patients.
Management of patient care from the time of admission to care to the time of discharge is the
responsibility of clinical care staff.
When security is involved in patient intervention activities, such intervention will be under the
direction and supervision of clinical care staff. Security may take independent action when presented
with circumstances involving a clear and present danger of bodily harm or danger to property.
The long-term use of security as observers or in patient watch situations should be avoided unless
dedicated security-staffing resources have been allocated for this specific purpose. If other security
resources are used, significant efforts should be made to maintain the overall quality of safety on the
campus. Placing patients in restraint or seclusion should also include appropriate clinical staff
monitoring. If security is used to support this monitoring, the appropriate training should be provided.
In general, security should be used to supplement and not replace clinical staff members. The primary
role of security should be to assist in situations where help is needed to gain control of the patient.
4.2.1.7 Restraining by staff
Security personnel may be requested to assist medical staff in physically restraining a patient. Under
these circumstances, written security procedures and concept should specifically cover the
circumstances, authority and procedures as agreed with the HCF top management or management of
medical services.
Restraining procedures shall meet the law and regulatory requirements.
In cases where security personnel assists in restraining or the seclusion of a patient within the facility,
where physical force and/or restraint devices are required, the following will apply:
— There will be continuous supervision, direction and monitoring of security actions by qualified
facility clinical care staff who will be present at all times;
— Restraint devices will be those devices commonly used in the medical care environment which have
been approved by the HCF. Handcuffs and similar law enforcement restraint devices will not be
used unless such medical restraint devices are not readily available, and there is an immediate and
clear danger that the patient may harm himself or others;
NOTE It is recognized that law enforcement restraint devices may not be used in any case in specific
jurisdictions. The use of weapons by security is considered as law enforcement use and not a healthcare
intervention. The use of a weapon by security to protect people or hospital property from harm would be handled
as a criminal activity.
— Security will receive training for their role with established protocols relevant to the patient;
— Watches, holds and restraining patients. Collaborative training with cli
...



Questions, Comments and Discussion
Ask us and Technical Secretary will try to provide an answer. You can facilitate discussion about the standard in here.
Loading comments...