ISO/IEC 27000:2016
(Main)Information technology — Security techniques — Information security management systems — Overview and vocabulary
Information technology — Security techniques — Information security management systems — Overview and vocabulary
ISO/IEC 27000:2016 the overview of information security management systems, and terms and definitions commonly used in the ISMS family of standards. This International Standard is applicable to all types and sizes of organization (e.g. commercial enterprises, government agencies, not-for-profit organizations).
Technologies de l'information — Techniques de sécurité — Systèmes de gestion de sécurité de l'information — Vue d'ensemble et vocabulaire
ISO/IEC 27000:2016 offre une vue d'ensemble des systèmes de management de la sécurité de l'information, ainsi que des termes et définitions d'usage courant dans la famille de normes du SMSI. La présente Norme internationale est applicable à tous les types et à toutes les tailles d'organismes (par exemple: les entreprises commerciales, les organismes publics, les organismes à but non lucratif).
General Information
- Status
- Withdrawn
- Publication Date
- 14-Feb-2016
- Withdrawal Date
- 14-Feb-2016
- Drafting Committee
- ISO/IEC JTC 1/SC 27/WG 1 - Information security management systems
- Current Stage
- 9599 - Withdrawal of International Standard
- Start Date
- 07-Feb-2018
- Completion Date
- 12-Feb-2026
Relations
- Effective Date
- 10-Jun-2017
- Effective Date
- 03-May-2014
ISO/IEC 27000:2016 - Information technology -- Security techniques -- Information security management systems -- Overview and vocabulary
REDLINE ISO/IEC 27000:2016 - Information technology -- Security techniques -- Information security management systems -- Overview and vocabulary
ISO/IEC 27000:2016 - Technologies de l'information -- Techniques de sécurité -- Systemes de gestion de sécurité de l'information -- Vue d'ensemble et vocabulaire
Get Certified
Connect with accredited certification bodies for this standard

BSI Group
BSI (British Standards Institution) is the business standards company that helps organizations make excellence a habit.

Bureau Veritas
Bureau Veritas is a world leader in laboratory testing, inspection and certification services.

DNV
DNV is an independent assurance and risk management provider.
Sponsored listings
Frequently Asked Questions
ISO/IEC 27000:2016 is a standard published by the International Organization for Standardization (ISO). Its full title is "Information technology — Security techniques — Information security management systems — Overview and vocabulary". This standard covers: ISO/IEC 27000:2016 the overview of information security management systems, and terms and definitions commonly used in the ISMS family of standards. This International Standard is applicable to all types and sizes of organization (e.g. commercial enterprises, government agencies, not-for-profit organizations).
ISO/IEC 27000:2016 the overview of information security management systems, and terms and definitions commonly used in the ISMS family of standards. This International Standard is applicable to all types and sizes of organization (e.g. commercial enterprises, government agencies, not-for-profit organizations).
ISO/IEC 27000:2016 is classified under the following ICS (International Classification for Standards) categories: 01.040.35 - Information technology (Vocabularies); 03.100.70 - Management systems; 35.030 - IT Security; 35.040 - Information coding. The ICS classification helps identify the subject area and facilitates finding related standards.
ISO/IEC 27000:2016 has the following relationships with other standards: It is inter standard links to ISO/IEC 27000:2018, ISO/IEC 27000:2014. Understanding these relationships helps ensure you are using the most current and applicable version of the standard.
ISO/IEC 27000:2016 is available in PDF format for immediate download after purchase. The document can be added to your cart and obtained through the secure checkout process. Digital delivery ensures instant access to the complete standard document.
Standards Content (Sample)
INTERNATIONAL ISO/IEC
STANDARD 27000
Fourth edition
2016-02-15
Information technology — Security
techniques — Information security
management systems — Overview
and vocabulary
Technologies de l’information — Techniques de sécurité — Systèmes de
gestion de sécurité de l’information — Vue d’ensemble et vocabulaire
Reference number
©
ISO/IEC 2016
© ISO/IEC 2016, Published in Switzerland
All rights reserved. Unless otherwise specified, no part of this publication may be reproduced or utilized otherwise in any form
or by any means, electronic or mechanical, including photocopying, or posting on the internet or an intranet, without prior
written permission. Permission can be requested from either ISO at the address below or ISO’s member body in the country of
the requester.
ISO copyright office
Ch. de Blandonnet 8 • CP 401
CH-1214 Vernier, Geneva, Switzerland
Tel. +41 22 749 01 11
Fax +41 22 749 09 47
copyright@iso.org
www.iso.org
ii © ISO/IEC 2016 – All rights reserved
Contents Page
Foreword .v
0 Introduction . 1
0.1 Overview . 1
0.2 ISMS family of standards . 1
0.3 Purpose of this International Standard . 2
1 Scope . 2
2 Terms and definitions . 2
3 Information security management systems .14
3.1 General .14
3.2 What is an ISMS? .14
3.2.1 Overview and principles .14
3.2.2 Information.15
3.2.3 Information security .15
3.2.4 Management .15
3.2.5 Management system .16
3.3 Process approach .16
3.4 Why an ISMS is important .16
3.5 Establishing, monitoring, maintaining and improving an ISMS .17
3.5.1 Overview .17
3.5.2 Identifying information security requirements .17
3.5.3 Assessing information security risks .18
3.5.4 Treating information security risks . .18
3.5.5 Selecting and implementing controls .18
3.5.6 Monitor, maintain and improve the effectiveness of the ISMS .19
3.5.7 Continual improvement .19
3.6 ISMS critical success factors .20
3.7 Benefits of the ISMS family of standards .20
4 ISMS family of standards .21
4.1 General information .21
4.2 Standards describing an overview and terminology .22
4.2.1 ISO/IEC 27000 (this International Standard) .22
4.3 Standards specifying requirements .22
4.3.1 ISO/IEC 27001 .22
4.3.2 ISO/IEC 27006 .22
4.4 Standards describing general guidelines .22
4.4.1 ISO/IEC 27002 .22
4.4.2 ISO/IEC 27003 .23
4.4.3 ISO/IEC 27004 .23
4.4.4 ISO/IEC 27005 .23
4.4.5 ISO/IEC 27007 .23
4.4.6 ISO/IEC TR 27008 .23
4.4.7 ISO/IEC 27013 .24
4.4.8 ISO/IEC 27014 .24
4.4.9 ISO/IEC TR 27016 .24
4.5 Standards describing sector-specific guidelines .25
4.5.1 ISO/IEC 27010 .25
4.5.2 ISO/IEC 27011 .25
4.5.3 ISO/IEC TR 27015 .25
4.5.4 ISO/IEC 27017 .25
4.5.5 ISO/IEC 27018 .26
4.5.6 ISO/IEC TR 27019 .26
4.5.7 ISO 27799 .26
© ISO/IEC 2016 – All rights reserved iii
Annex A (informative) Verbal forms for the expression of provisions.28
Annex B (informative) Term and term ownership .29
Bibliography .33
iv © ISO/IEC 2016 – All rights reserved
Foreword
ISO (the International Organization for Standardization) and IEC (the International Electrotechnical
Commission) form the specialized system for worldwide standardization. National bodies that are
members of ISO or IEC participate in the development of International Standards through technical
committees established by the respective organization to deal with particular fields of technical
activity. ISO and IEC technical committees collaborate in fields of mutual interest. Other international
organizations, governmental and non-governmental, in liaison with ISO and IEC, also take part in the
work. In the field of information technology, ISO and IEC have established a joint technical committee,
ISO/IEC JTC 1.
The procedures used to develop this document and those intended for its further maintenance are
described in the ISO/IEC Directives, Part 1. In particular the different approval criteria needed for
the different types of document should be noted. This document was drafted in accordance with the
editorial rules of the ISO/IEC Directives, Part 2 (see www.iso.org/directives).
Attention is drawn to the possibility that some of the elements of this document may be the subject
of patent rights. ISO and IEC shall not be held responsible for identifying any or all such patent
rights. Details of any patent rights identified during the development of the document will be in the
Introduction and/or on the ISO list of patent declarations received (see www.iso.org/patents).
Any trade name used in this document is information given for the convenience of users and does not
constitute an endorsement.
For an explanation on the meaning of ISO specific terms and expressions related to conformity
assessment, as well as information about ISO’s adherence to the WTO principles in the Technical
Barriers to Trade (TBT) see the following URL: Foreword - Supplementary information
The committee responsible for this document is ISO/IEC JTC 1, Information technology, SC 27, IT
Security techniques.
This fourth edition cancels and replaces the third edition (ISO/IEC 27000:2014), which has been
technically revised.
© ISO/IEC 2016 – All rights reserved v
INTERNATIONAL STANDARD ISO/IEC 27000:2016(E)
Information technology — Security techniques —
Information security management systems — Overview
and vocabulary
0 Introduction
0.1 Overview
International Standards for management systems provide a model to follow in setting up and
operating a management system. This model incorporates the features on which experts in the field
have reached a consensus as being the international state of the art. ISO/IEC JTC 1/SC 27 maintains an
expert committee dedicated to the development of international management systems standards for
information security, otherwise known as the Information Security Management System (ISMS) family
of standards.
Through the use of the ISMS family of standards, organizations can develop and implement a framework
for managing the security of their information assets including financial information, intellectual
property, and employee details, or information entrusted to them by customers or third parties. These
standards can also be used to prepare for an independent assessment of their ISMS applied to the
protection of information.
0.2 ISMS family of standards
The ISMS family of standards (see Clause 4) is intended to assist organizations of all types and sizes
to implement and operate an ISMS and consists of the following International Standards, under the
general title Information technology — Security techniques (given below in numerical order):
— ISO/IEC 27000, Information security management systems — Overview and vocabulary
— ISO/IEC 27001, Information security management systems — Requirements
— ISO/IEC 27002, Code of practice for information security controls
— ISO/IEC 27003, Information security management system implementation guidance
— ISO/IEC 27004, Information security management — Measurement
— ISO/IEC 27005, Information security risk management
— ISO/IEC 27006, Requirements for bodies providing audit and certification of information security
management systems
— ISO/IEC 27007, Guidelines for information security management systems auditing
— ISO/IEC TR 27008, Guidelines for auditors on information security controls
— ISO/IEC 27009, Sector-specific application of ISO/IEC 27001 — Requirements
— ISO/IEC 27010, Information security management for inter-sector and inter-organizational
communications
— ISO/IEC 27011, Information security management guidelines for telecommunications organizations
based on ISO/IEC 27002
— ISO/IEC 27013, Guidance on the integrated implementation of ISO/IEC 27001 and ISO/IEC 20000-1
© ISO/IEC 2016 – All rights reserved 1
— ISO/IEC 27014, Governance of information security
— ISO/IEC TR 27015, Information security management guidelines for financial services
— ISO/IEC TR 27016, Information security management — Organizational economics
— ISO/IEC 27017, Code of practice for information security controls based on ISO/IEC 27002 for cloud
services
— ISO/IEC 27018, Code of practice for protection of personally identifiable information (PII) in public
clouds acting as PII processors
— ISO/IEC 27019, Information security management guidelines based on ISO/IEC 27002 for process
control systems specific to the energy utility industry
NOTE The general title “Information technology — Security techniques” indicates that these International
Standards were prepared by Joint Technical Committee ISO/IEC JTC 1, Information technology, Subcommittee
SC 27, IT Security techniques.
International Standards not under the same general title that are also part of the ISMS family of
standards are as follows:
— ISO 27799, Health informatics — Information security management in health using ISO/IEC 27002
0.3 Purpose of this International Standard
This International Standard provides an overview of information security management systems and
defines related terms.
NOTE Annex A provides clarification on how verbal forms are used to express requirements and/or guidance
in the ISMS family of standards.
The ISMS family of standards includes standards that
a) define requirements for an ISMS and for those certifying such systems,
b) provide direct support, detailed guidance and/or interpretation for the overall process to establish,
implement, maintain, and improve an ISMS,
c) address sector-specific guidelines for ISMS, and
d) address conformity assessment for ISMS.
The terms and definitions provided in this International Standard
— cover commonly used terms and definitions in the ISMS family of standards,
— do not cover all terms and definitions applied within the ISMS family of standards, and
— do not limit the ISMS family of standards in defining new terms for use.
1 Scope
This International Standard provides the overview of information security management systems, and
terms and definitions commonly used in the ISMS family of standards. This International Standard is
applicable to all types and sizes of organization (e.g. commercial enterprises, government agencies, not-
for-profit organizations).
2 Terms and definitions
For the purposes of this document, the following terms and definitions apply.
2 © ISO/IEC 2016 – All rights reserved
2.1
access control
means to ensure that access to assets is authorized and restricted based on business and security
requirements (2.63)
2.2
analytical model
algorithm or calculation combining one or more base measures (2.10) and/or derived measures (2.22)
with associated decision criteria (2.21)
2.3
attack
attempt to destroy, expose, alter, disable, steal or gain unauthorized access to or make unauthorized
use of an asset
2.4
attribute
property or characteristic of an object (2.55) that can be distinguished quantitatively or qualitatively
by human or automated means
[SOURCE: ISO/IEC 15939:2007, 2.2, modified — “entity” has been replaced by “object” in the definition.]
2.5
audit
systematic, independent and documented process (2.61) for obtaining audit evidence and evaluating it
objectively to determine the extent to which the audit criteria are fulfilled
Note 1 to entry: An audit can be an internal audit (first party) or an external audit (second party or third party),
and it can be a combined audit (combining two or more disciplines).
Note 2 to entry: “Audit evidence” and “audit criteria” are defined in ISO 19011.
2.6
audit scope
extent and boundaries of an audit (2.5)
[SOURCE: ISO 19011:2011, 3.14, modified — Note 1 to entry has been deleted.]
2.7
authentication
provision of assurance that a claimed characteristic of an entity is correct
2.8
authenticity
property that an entity is what it claims to be
2.9
availability
property of being accessible and usable upon demand by an authorized entity
2.10
base measure
measure (2.47) defined in terms of an attribute (2.4) and the method for quantifying it
[SOURCE: ISO/IEC 15939:2007, 2.3, modified — Note 2 to entry has been deleted.]
Note 1 to entry: A base measure is functionally independent of other measures (2.47).
2.11
competence
ability to apply knowledge and skills to achieve intended results
© ISO/IEC 2016 – All rights reserved 3
2.12
confidentiality
property that information is not made available or disclosed to unauthorized individuals, entities, or
processes (2.61)
2.13
conformity
fulfilment of a requirement (2.63)
Note 1 to entry: The term “conformance” is synonymous but deprecated.
2.14
consequence
outcome of an event (2.25) affecting objectives (2.56)
[SOURCE: ISO Guide 73:2009, 3.6.1.3, modified]
Note 1 to entry: An event (2.25) can lead to a range of consequences.
Note 2 to entry: A consequence can be certain or uncertain and in the context of information security (2.33) is
usually negative.
Note 3 to entry: Consequences can be expressed qualitatively or quantitatively.
Note 4 to entry: Initial consequences can escalate through knock-on effects.
2.15
continual improvement
recurring activity to enhance performance (2.59)
2.16
control
measure that is modifying risk (2.68)
[SOURCE: ISO Guide 73:2009, 3.8.1.1]
Note 1 to entry: Controls include any process (2.61), policy (2.60), device, practice, or other actions which
modify risk (2.68).
Note 2 to entry: Controls may not always exert the intended or assumed modifying effect.
2.17
control objective
statement describing what is to be achieved as a result of implementing controls (2.16)
2.18
correction
action to eliminate a detected nonconformity (2.53)
2.19
corrective action
action to eliminate the cause of a nonconformity (2.53) and to prevent recurrence
2.20
data
collection of values assigned to base measures (2.10), derived measures (2.22) and/or indicators (2.30)
[SOURCE: ISO/IEC 15939:2007, 2.4, modified — Note 1 to entry has been added.]
Note 1 to entry: This definition applies only within the context of ISO/IEC 27004.
4 © ISO/IEC 2016 – All rights reserved
2.21
decision criteria
thresholds, targets, or patterns used to determine the need for action or further investigation, or to
describe the level of confidence in a given result
[SOURCE: ISO/IEC 15939:2007, 2.7]
2.22
derived measure
measure (2.47) that is defined as a function of two or more values of base measures (2.10)
[SOURCE: ISO/IEC 15939:2007, 2.8, modified — Note 1 to entry has been deleted.]
2.23
documented information
information required to be controlled and maintained by an organization (2.57) and the medium on
which it is contained
Note 1 to entry: Documented information can be in any format and media and from any source.
Note 2 to entry: Documented information can refer to
— the management system (2.46), including related processes (2.61);
— information created in order for the organization (2.57) to operate (documentation);
— evidence of results achieved (records).
2.24
effectiveness
extent to which planned activities are realized and planned results achieved
2.25
event
occurrence or change of a particular set of circumstances
[SOURCE: ISO Guide 73:2009, 3.5.1.3, modified — Note 4 to entry has been deleted.]
Note 1 to entry: An event can be one or more occurrences, and can have several causes.
Note 2 to entry: An event can consist of something not happening.
Note 3 to entry: An event can sometimes be referred to as an “incident” or “accident”.
2.26
executive management
person or group of people who have delegated responsibility from the governing body (2.29) for
implementation of strategies and policies to accomplish the purpose of the organization (2.57)
Note 1 to entry: Executive management is sometimes called top management (2.84) and can include Chief
Executive Officers, Chief Financial Officers, Chief Information Officers, and similar roles.
2.27
external context
external environment in which the organization seeks to achieve its objectives (2.56)
[SOURCE: ISO Guide 73:2009, 3.3.1.1]
Note 1 to entry: External context can include the following:
— the cultural, social, political, legal, regulatory, financial, technological, economic, natural and competitive
environment, whether international, national, regional or local;
— key drivers and trends having impact on the objectives (2.56) of the organization (2.57);
© ISO/IEC 2016 – All rights reserved 5
— relationships with, and perceptions and values of, external stakeholders (2.82).
2.28
governance of information security
system by which an organization’s (2.57) information security (2.33) activities are directed and controlled
2.29
governing body
person or group of people who are accountable for the performance (2.59) and conformance of the
organization (2.57)
Note 1 to entry: Governing body can in some jurisdictions be a board of directors.
2.30
indicator
measure (2.47) that provides an estimate or evaluation of specified attributes (2.4) derived from an
analytical model (2.2) with respect to defined information needs (2.31)
2.31
information need
insight necessary to manage objectives (2.56), goals, risks and problems
[SOURCE: ISO/IEC 15939:2007, 2.12]
2.32
information processing facilities
any information processing system, service or infrastructure, or the physical location housing it
2.33
information security
preservation of confidentiality (2.12), integrity (2.40) and availability (2.9) of information
Note 1 to entry: In addition, other properties, such as authenticity (2.8), accountability, non-repudiation (2.54),
and reliability (2.62) can also be involved.
2.34
information security continuity
processes (2.61) and procedures for ensuring continued information security (2.33) operations
2.35
information security event
identified occurrence of a system, service or network state indicating a possible breach of information
security (2.33) policy (2.60) or failure of controls (2.16), or a previously unknown situation that may be
security relevant
2.36
information security incident
single or a series of unwanted or unexpected information security events (2.35) that have a significant
probability of compromising business operations and threatening information security (2.33)
2.37
information security incident management
processes (2.61) for detecting, reporting, assessing, responding to, dealing with, and learning from
information security incidents (2.36)
2.38
information sharing community
group of organizations (2.57) that agree to share information
Note 1 to entry: An organization (2.57) can be an individual.
6 © ISO/IEC 2016 – All rights reserved
2.39
information system
applications, services, information technology assets, or other information handling components
2.40
integrity
property of accuracy and completeness
2.41
interested party
person or organization (2.57) that can affect, be affected by, or perceive themselves to be affected by a
decision or activity
2.42
internal context
internal environment in which the organization (2.57) seeks to achieve its objectives
[SOURCE: ISO Guide 73:2009, 3.3.1.2]
Note 1 to entry: Internal context can include the following:
— governance, organizational structure, roles and accountabilities;
— policies (2.60), objectives (2.56), and the strategies that are in place to achieve them;
— the capabilities, understood in terms of resources and knowledge (e.g. capital, time, people, processes (2.61),
systems and technologies);
— information systems (2.39), information flows and decision-making processes (2.61) (both formal and informal);
— relationships with, and perceptions and values of, internal stakeholders (2.82);
— the organization’s (2.57) culture;
— standards, guidelines and models adopted by the organization (2.57);
— form and extent of contractual relationships.
2.43
ISMS project
structured activities undertaken by an organization (2.57) to implement an ISMS
2.44
level of risk
magnitude of a risk (2.68) expressed in terms of the combination of consequences (2.14) and their
likelihood (2.45)
[SOURCE: ISO Guide 73:2009, 3.6.1.8, modified — “or combination of risks” has been deleted in the
definition.]
2.45
likelihood
chance of something happening
[SOURCE: ISO Guide 73:2009, 3.6.1.1, modified — Notes 1 and 2 to entry have been deleted.]
2.46
management system
set of interrelated or interacting elements of an organization (2.57) to establish policies (2.60) and
objectives (2.56) and processes (2.61) to achieve those objectives
Note 1 to entry: A management system can address a single discipline or several disciplines.
© ISO/IEC 2016 – All rights reserved 7
Note 2 to entry: The system elements include the organization’s structure, roles and responsibilities,
planning, operation.
Note 3 to entry: The scope of a management system may include the whole of the organization (2.57), specific and
identified functions of the organization (2.57), specific and identified sections of the organization (2.57), or one
or more functions across a group of organizations (2.57).
2.47
measure
variable to which a value is assigned as the result of measurement (2.48)
[SOURCE: ISO/IEC 15939:2007, 2.15, modified]
Note 1 to entry: The term “measures” is used to refer collectively to base measures (2.10), derived measures (2.22),
and indicators (2.30).
2.48
measurement
process (2.61) to determine a value
Note 1 to entry: In the context of information security (2.33), the process (2.61) of determining a value requires
information about the effectiveness (2.24) of an information security (2.33) management system (2.46) and its
associated controls (2.16) using a measurement method (2.50), a measurement function (2.49), an analytical model
(2.2), and decision criteria (2.21).
2.49
measurement function
algorithm or calculation performed to combine two or more base measures (2.10)
[SOURCE: ISO/IEC 15939:2007, 2.20]
2.50
measurement method
logical sequence of operations, described generically, used in quantifying an attribute (2.4) with respect
to a specified scale (2.80)
[SOURCE: ISO/IEC 15939:2007, 2.22, modified — Note 2 to entry has been deleted.]
Note 1 to entry: The type of measurement method depends on the nature of the operations used to quantify an
attribute (2.4). Two types can be distinguished as follows:
— subjective: quantification involving human judgment;
— objective: quantification based on numerical rules.
2.51
measurement results
one or more indicators (2.30) and their associated interpretations that address an information need (2.31)
2.52
monitoring
determining the status of a system, a process (2.61) or an activity
Note 1 to entry: To determine the status, there may be a need to check, supervise or critically observe.
2.53
nonconformity
non-fulfilment of a requirement (2.63)
2.54
non-repudiation
ability to prove the occurrence of a claimed event (2.25) or action and its originating entities
8 © ISO/IEC 2016 – All rights reserved
2.55
object
item characterized through the measurement (2.48) of its attributes (2.4)
2.56
objective
result to be achieved
Note 1 to entry: An objective can be strategic, tactical, or operational.
Note 2 to entry: Objectives can relate to different disciplines (such as financial, health and safety, and
environmental goals) and can apply at different levels (such as strategic, organization-wide, project, product and
process (2.61).
Note 3 to entry: An objective can be expressed in other ways, e.g. as an intended outcome, a purpose, an
operational criterion, as an information security (2.33) objective or by the use of other words with similar
meaning (e.g. aim, goal, or target).
Note 4 to entry: In the context of information security (2.33) management systems (2.46), information security
(2.33) objectives are set by the organization, consistent with the information security (2.33) policy (2.60), to
achieve specific results.
2.57
organization
person or group of people that has its own functions with responsibilities, authorities and relationships
to achieve its objectives (2.56)
Note 1 to entry: The concept of organization includes but is not limited to sole-trader, company, corporation, firm,
enterprise, authority, partnership, charity or institution, or part or combination thereof, whether incorporated
or not, public or private.
2.58
outsource
make an arrangement where an external organization (2.57) performs part of an organization’s (2.57)
function or process (2.61)
Note 1 to entry: An external organization is outside the scope of the management system (2.46), although the
outsourced function or process (2.61) is within the scope.
2.59
performance
measurable result
Note 1 to entry: Performance can relate either to quantitative or qualitative findings.
Note 2 to entry: Performance can relate to the management of activities, processes (2.61), products (including
services), systems or organizations (2.57).
2.60
policy
intentions and direction of an organization (2.57) as formally expressed by its top management (2.84)
2.61
process
set of interrelated or interacting activities which transforms inputs into outputs
2.62
reliability
property of consistent intended behaviour and results
© ISO/IEC 2016 – All rights reserved 9
2.63
requirement
need or expectation that is stated, generally implied or obligatory
Note 1 to entry: “Generally implied” means that it is custom or common practice for the organization (2.57) and
interested parties that the need or expectation under consideration is implied.
Note 2 to entry: A specified requirement is one that is stated, for example in documented information (2.23).
2.64
residual risk
risk (2.68) remaining after risk treatment (2.79)
Note 1 to entry: Residual risk can contain unidentified risk (2.68).
Note 2 to entry: Residual risk can also be known as “retained risk”.
2.65
review
activity undertaken to determine the suitability, adequacy and effectiveness (2.24) of the subject matter
to achieve established objectives (2.54)
[SOURCE: ISO Guide 73:2009, 3.8.2.2, modified — Note 1 to entry has been deleted.]
2.66
review object
specific item being reviewed
2.67
review objective
statement describing what is to be achieved as a result of a review (2.65)
2.68
risk
effect of uncertainty on objectives
[SOURCE: ISO Guide 73:2009, 1.1, modified]
Note 1 to entry: An effect is a deviation from the expected — positive or negative.
Note 2 to entry: Uncertainty is the state, even partial, of deficiency of information related to, understanding or
knowledge of, an event (2.25), its consequence (2.14), or likelihood (2.45).
Note 3 to entry: Risk is often characterized by reference to potential events (2.25) and consequences (2.14), or a
combination of these.
Note 4 to entry: Risk is often expressed in terms of a combination of the consequences (2.14) of an event (2.25)
(including changes in circumstances) and the associated likelihood (2.45) of occurrence.
Note 5 to entry: In the context of information security (2.33) management systems (2.46), information security
(2.33) risks can be expressed as effect of uncertainty on information security (2.33) objectives (2.56).
Note 6 to entry: Information security (2.33) risk is associated with the potential that threats (2.83) will exploit
vulnerabilities (2.89) of an information asset or group of information assets and thereby cause harm to an
organization (2.57).
2.69
risk acceptance
informed decision to take a particular risk (2.68)
[SOURCE: ISO Guide 73:2009, 3.7.1.6]
Note 1 to entry: Risk acceptance can occur without risk treatment (2.79) or during the process (2.61) of risk
treatment (2.79).
10 © ISO/IEC 2016 – All rights reserved
Note 2 to entry: Accepted risks (2.68) are subject to monitoring (2.52) and review (2.65).
2.70
risk analysis
process (2.61) to comprehend the nature of risk (2.68) and to determine the level of risk (2.44)
[SOURCE: ISO Guide 73:2009, 3.6.1]
Note 1 to entry: Risk analysis provides the basis for risk evaluation (2.74) and decisions about risk treatment (2.79).
Note 2 to entry: Risk analysis includes risk estimation.
2.71
risk assessment
overall process (2.61) of risk identification (2.75), risk analysis (2.70) and risk evaluation (2.74)
[SOURCE: ISO Guide 73:2009, 3.4.1]
2.72
risk communication and consultation
continual and iterative processes (2.61) that an organization conducts to provide, share or obtain
information, and to engage in dialogue with stakeholders (2.82) regarding the management of risk (2.68)
Note 1 to entry: The information can relate to the existence, nature, form, likelihood (2.45), significance,
evaluation, acceptability and treatment of risk (2.68).
Note 2 to entry: Consultation is a two-way process (2.51) of informed communication between an organization
(2.57) and its stakeholders (2.82) on an issue prior to making a decision or determining a direction on that issue.
Consultation is
— a process (2.61) which impacts on a decision through influence rather than power and
— an input to decision making, not joint decision making.
2.73
risk criteria
terms of reference against which the significance of risk (2.68) is evaluated
[SOURCE: ISO Guide 73:2009, 3.3.1.3]
Note 1 to entry: Risk criteria are based on organizational objectives, and external (2.27) and internal context (2.42).
Note 2 to entry: Risk criteria can be derived from standards, laws, policies (2.60) and other requirements (2.63).
2.74
risk evaluation
process (2.61) of comparing the results of risk analysis (2.70) with risk criteria (2.73) to determine
whether the risk (2.68) and/or its magnitude is acceptable or tolerable
[SOURCE: ISO Guide 73:2009, 3.7.1]
Note 1 to entry: Risk evaluation assists in the decision about risk treatment (2.79).
2.75
risk identification
process (2.61) of finding, recognizing and describing risks (2.68)
[SOURCE: ISO Guide 73:2009, 3.5.1]
Note 1 to entry: Risk identification involves the identification of risk sources, events (2.25), their causes and their
potential consequences (2.14).
Note 2 to entry: Risk identification can involve historical data, theoretical analysis, informed and expert opinions,
and stakeholders’ (2.82) needs.
© ISO/IEC 2016 – All rights reserved 11
2.76
risk management
coordinated activities to direct and control an organization (2.57) with regard to risk (2.68)
[SOURCE: ISO Guide 73:2009, 2.1]
2.77
risk management process
systematic application of management policies (2.60), procedures and practices to the activities of
communicating, consulting, establishing the context and identifying, analysing, evaluating, treating,
monitoring and reviewing risk (2.68)
[SOURCE: ISO Guide 73:2009, 3.1, modified — Note 1 to entry has been added.]
Note 1 to entry: ISO/IEC 27005 uses the term “process” (2.61) to describe risk management overall. The elements
within the risk management (2.76) process (2.61) are termed “activities”.
2.78
risk owner
person or entity with the accountability and authority to manage a risk (2.68)
[SOURCE: ISO Guide 73:2009, 3.5.1.5]
2.79
risk treatment
process (2.61) to modify risk (2.68)
[SOURCE: ISO Guide 73:2009, 3.8.1, modified — “decision” has been replaced by “choice” in Note 1 to
entry.]
Note 1 to entry: Risk treatment can involve the following:
— avoiding the risk (2.68) by deciding not to start or continue with the activity that gives rise to the risk (2.68);
— taking or increasing risk (2.68) in order to pursue an opportunity;
— removing the risk (2.68) source;
— changing the likelihood (2.45);
— changing the consequences (2.14);
— sharing the risk (2.68) with another party or parties (including contracts and risk financing);
— retaining the risk (2.68) by informed choice.
Note 2 to entry: Risk treatments that deal with negative consequences (2.14) are sometimes referred to as “risk
mitigation”, “risk elimination”, “risk prevention” and “risk reduction”.
Note 3 to entry: Risk treatment can create new risks (2.68) or modify existing risks (2.68).
2.80
scale
ordered set of values, continuous or discrete, or a set of categories to which the attribute (2.4) is mapped
[SOURCE: ISO/IEC 15939:2007, 2.35, modified]
Note 1 to entry: The type of scale depends on the nature of the relationship between values on the scale. Four
types of scale are commonly defined as follows:
— nominal: the measurement (2.48) values are categorical;
— ordinal: the measurement (2.48) values are rankings;
12 © ISO/IEC 2016 – All rights reserved
— interval: the measurement (2.48) values have equal distances corresponding to equal quantities of the
attribute (2.4);
— ratio: the measurement (2.48) values have equal distances corresponding to equal quantities of the attribute
(2.4), where the value of zero corresponds to none of the attribute.
These are just examples of the types of scale.
2.81
security implementation standard
document specifying authorized ways for realizing security
2.82
stakeholder
person or organization (2.57) that can affect, be affected by, or perceive themselves to be affected by a
decision or activity
[SOURCE: ISO Guide 73:2009, 3.2.1.1, modified — Note 1 to entry has been deleted.]
2.83
threat
potential cause of an unwanted incident, which may result in harm to a system or organization (2.57)
2.84
top management
person or group of people who directs and controls an organization (2.57) at the highest level
Note 1 to entry: Top management has the power to delegate authority and provide resources within the
organization (2.57).
Note 2 to entry: If the scope of the management system (2.46) covers only part of an organization (2.57), then top
management refers to those who direct and control that part of the organization (2.57).
2.85
trusted information communication entity
autonomous organization (2.57) supporting information exchange within an information sharing
community (2.38)
2.86
unit of measurement
particular quantity, defined and adopted by convention, with which other quantities of the same kind
are compared in order to express their magnitude relative to that quantity
[SOURCE: ISO/IEC 15939:2007, 2.40, modified]
2.87
validation
confirmation, through the provision of objective evidence, that the requirements (2.63) for a specific
intended use or application have been fulfilled
[SOURCE: ISO 9000:2015, 3.8.12, modified]
2.88
verification
confirmation, through the provision of objective evidence, that specified requirements (2.63) have
been fulfilled
[SOURCE: ISO 9000:2015, 3.8.4]
Note 1 to entry: This could also be called compliance testing.
© ISO/IEC 2016 – All rights reserved 13
2.89
vulnerability
weakness of an asset or control (2.16) that can be exploited by one or more threats (2.83)
3 Information security management systems
3.1 General
Organizations of all types and sizes:
a) collect, process, store, and transmit information;
b) recognize that information, and related processes, systems, networks and people are important
assets for achieving organization objectives;
c) face a range of risks that may affect the functioning of assets; and
d) address their perceived risk exposure by implementing information security controls.
All information held and processed by an organization is subject to threats of attack, error, nature (for
example, flood or fire), etc., and is subject to vulnerabilities inherent in its use. The term information
security is generally based on information being considered as an asset which has a value requiring
appropriate protection, for example, against the loss of availability, confidentiality and integrity.
Enabling accurate and complete information to be available in a timely manner to those with an
authorized need is a catalyst for business e
...
INTERNATIONAL ISO/IEC
STANDARD 27000
Redline version
compares Fourth edition to
Third edition
Information technology — Security
techniques — Information security
management systems — Overview
and vocabulary
Technologies de l’information — Techniques de sécurité — Systèmes de
gestion de sécurité de l’information — Vue d’ensemble et vocabulaire
Reference number
ISO/IEC 27000:redline:2016(E)
©
ISO/IEC 2016
ISO/IEC 27000:redline:2016(E)
IMPORTANT — PLEASE NOTE
This is a mark-up copy and uses the following colour coding:
Text example 1 — indicates added text (in green)
— indicates removed text (in red)
Text example 2
— indicates added graphic figure
— indicates removed graphic figure
1.x . — Heading numbers containg modifications are highlighted in yellow in
the Table of Contents
All changes in this document have yet to reach concensus by vote and as such should only
be used internally for review purposes.
DISCLAIMER
This Redline version provides you with a quick and easy way to compare the main changes
between this edition of the standard and its previous edition. It doesn’t capture all single
changes such as punctuation but highlights the modifications providing customers with
the most valuable information. Therefore it is important to note that this Redline version is
not the official ISO standard and that the users must consult with the clean version of the
standard, which is the official standard, for implementation purposes.
© ISO/IEC 2016, Published in Switzerland
All rights reserved. Unless otherwise specified, no part of this publication may be reproduced or utilized otherwise in any form
or by any means, electronic or mechanical, including photocopying, or posting on the internet or an intranet, without prior
written permission. Permission can be requested from either ISO at the address below or ISO’s member body in the country of
the requester.
ISO copyright office
Ch. de Blandonnet 8 • CP 401
CH-1214 Vernier, Geneva, Switzerland
Tel. +41 22 749 01 11
Fax +41 22 749 09 47
copyright@iso.org
www.iso.org
ii © ISO/IEC 2016 – All rights reserved
ISO/IEC 27000:redline:2016(E)
Contents Page
Foreword .v
0 Introduction .vi
1 Scope . 1
2 Terms and definitions . 1
3 Information security management systems .12
3.1 Introduction General .12
3.2 What is an ISMS? .13
3.2.1 Overview and principles .13
3.2.2 Information.13
3.2.3 Information security .14
3.2.4 Management .14
3.2.5 Management system .14
3.3 Process approach .14
3.4 Why an ISMS is important .15
3.5 Establishing, monitoring, maintaining and improving an ISMS .16
3.5.1 Overview .16
3.5.2 Identifying information security requirements .16
3.5.3 Assessing information security risks .16
3.5.4 Treating information security risks . .17
3.5.5 Selecting and implementing controls .17
3.5.6 Monitor, maintain and improve the effectiveness of the ISMS .18
3.5.7 Continual improvement .18
3.6 ISMS critical success factors .18
3.7 Benefits of the ISMS family of standards .19
4 ISMS family of standards .19
4.1 General information .19
4.2 Standards describing an overview and terminology .21
4.2.1 ISO/IEC 27000 (this document International Standard) .21
4.3 Standards specifying requirements .21
4.3.1 ISO/IEC 27001 .21
4.3.2 ISO/IEC 27006 .21
4.4 Standards describing general guidelines .22
4.4.1 ISO/IEC 27002 .22
4.4.2 ISO/IEC 27003 .22
4.4.3 ISO/IEC 27004 .22
4.4.4 ISO/IEC 27005 .22
4.4.5 ISO/IEC 27007 .22
4.4.6 ISO/IEC TR 27008 .23
4.4.7 ISO/IEC 27013 .23
4.4.8 ISO/IEC 27014 .23
4.4.9 ISO/IEC TR 27016 .23
4.5 Standards describing sector-specific guidelines .24
4.5.1 ISO/IEC 27010 .24
4.5.2 ISO/IEC 27011 .24
4.5.3 ISO/IEC TR 27015 .24
4.5.4 ISO/IEC 27017 .25
4.5.5 ISO/IEC 27018 .25
4.5.6 ISO/IEC TR 27019 .25
4.5.4 4.5.7 ISO 27799 .26
Annex A (informative) Verbal forms for the expression of provisions.27
© ISO/IEC 2016 – All rights reserved iii
ISO/IEC 27000:redline:2016(E)
Annex B (informative) Term and term ownership .28
Bibliography .32
iv © ISO/IEC 2016 – All rights reserved
ISO/IEC 27000:redline:2016(E)
Foreword
ISO (the International Organization for Standardization) and IEC (the International Electrotechnical
Commission) form the specialized system for worldwide standardization. National bodies that are
members of ISO or IEC participate in the development of International Standards through technical
committees established by the respective organization to deal with particular fields of technical
activity. ISO and IEC technical committees collaborate in fields of mutual interest. Other international
organizations, governmental and non-governmental, in liaison with ISO and IEC, also take part in the
work. In the field of information technology, ISO and IEC have established a joint technical committee,
ISO/IEC JTC 1.
International Standards areThe procedures used to develop this document and those intended for its
further maintenance are described in the ISO/IEC Directives, Part 1. In particular the different approval
criteria needed for the different types of document should be noted. This document was drafted
in accordance with the rules given ineditorial rules of the ISO/IEC Directives, Part 2 (see www.iso.
org/directives).
The main task of the joint technical committee is to prepare International Standards. Draft International
Standards adopted by the joint technical committee are circulated to national bodies for voting.
Publication as an International Standard requires approval by at least 75 % of the national bodies
casting a vote.
Attention is drawn to the possibility that some of the elements of this document may be the subject
of patent rights. ISO and IEC shall not be held responsible for identifying any or all such patent rights.
Details of any patent rights identified during the development of the document will be in the Introduction
and/or on the ISO list of patent declarations received (see www.iso.org/patents).
Any trade name used in this document is information given for the convenience of users and does not
constitute an endorsement.
For an explanation on the meaning of ISO specific terms and expressions related to conformity
assessment, as well as information about ISO’s adherence to the WTO principles in the Technical Barriers
to Trade (TBT) see the following URL: Foreword - Supplementary information
ISO/IEC 27000 was prepared by Joint Technical CommitteeThe committee responsible for this document
is ISO/IEC JTC 1, Information technology, Subcommittee SC 27, IT Security techniques.
This thirdfourth edition cancels and replaces the secondthird edition (ISO/IEC 27000:20122014), which
has been technically revised.
© ISO/IEC 2016 – All rights reserved v
ISO/IEC 27000:redline:2016(E)
0 Introduction
0.1 Overview
International Standards for management systems provide a model to follow in setting up and operating
a management system. This model incorporates the features on which experts in the field have reached a
consensus as being the international state of the art. ISO/IEC JTC 1/SC 27 maintains an expert committee
dedicated to the development of international management systems standards for information security,
otherwise known as the Information Security Management System (ISMS) family of standards.
Through the use of the ISMS family of standards, organizations can develop and implement a framework
for managing the security of their information assets including financial information, intellectual
property, and employee details, or information entrusted to them by customers or third parties. These
standards can also be used to prepare for an independent assessment of their ISMS applied to the
protection of information.
0.2 ISMS family of standards
The ISMS family of standards (see Clause 4) is intended to assist organizations of all types and sizes to
implement and operate an ISMS and consists of the following International Standards, under the general
title Information technology — Security techniques (given below in numerical order):
— ISO/IEC 27000, Information security management systems — Overview and vocabulary
— ISO/IEC 27001, Information security management systems — Requirements
— ISO/IEC 27002, Code of practice for information security controls
— ISO/IEC 27003, Information security management system implementation guidance
— ISO/IEC 27004, Information security management — Measurement
— ISO/IEC 27005, Information security risk management
— ISO/IEC 27006, Requirements for bodies providing audit and certification of information security
management systems
— ISO/IEC 27007, Guidelines for information security management systems auditing
— ISO/IEC TR 27008, Guidelines for auditors on information security controls
— ISO/IEC 27009, Sector-specific application of ISO/IEC 27001 — Requirements
— ISO/IEC 27010, Information security management for inter-sector and inter-organizational
communications
— ISO/IEC 27011, Information security management guidelines for telecommunications organizations
based on ISO/IEC 27002
— ISO/IEC 27013, Guidance on the integrated implementation of ISO/IEC 27001 and ISO/IEC 20000-1
— ISO/IEC 27014, Governance of information security
— ISO/IEC TR 27015, Information security management guidelines for financial services
— ISO/IEC TR 27016, Information security management — Organizational economics
— ISO/IEC 27017, Code of practice for information security controls based on ISO/IEC 27002 for cloud services
— ISO/IEC 27018, Code of practice for protection of personally identifiable information (PII) in public
clouds acting as PII processors
vi © ISO/IEC 2016 – All rights reserved
ISO/IEC 27000:redline:2016(E)
— ISO/IEC 27019, Information security management guidelines based on ISO/IEC 27002 for process
control systems specific to the energy utility industry
NOTE The general title “Information technology — Security techniques” indicates that these
standardsInternational Standards were prepared by Joint Technical Committee ISO/IEC JTC 1, Information
technology, Subcommittee SC 27, IT Security techniques.
International Standards not under the same general title that are also part of the ISMS family of standards
are as follows:
— ISO 27799:2008, Health informatics — Information security management in health using ISO/IEC 27002
0.3 Purpose of this International Standard
This International Standard provides an overview of information security management systems and
defines related terms.
NOTE Annex A provides clarification on how verbal forms are used to express requirements and/or guidance
in the ISMS family of standards.
The ISMS family of standards includes standards that:
a) define requirements for an ISMS and for those certifying such systems;,
b) provide direct support, detailed guidance and/or interpretation for the overall process to establish,
implement, maintain, and improve an ISMS;,
c) address sector-specific guidelines for ISMS;, and
d) address conformity assessment for ISMS.
The terms and definitions provided in this International Standard:
— cover commonly used terms and definitions in the ISMS family of standards;,
— do not cover all terms and definitions applied within the ISMS family of standards;, and
— do not limit the ISMS family of standards in defining new terms for use.
© ISO/IEC 2016 – All rights reserved vii
INTERNATIONAL STANDARD ISO/IEC 27000:redline:2016(E)
Information technology — Security techniques —
Information security management systems — Overview
and vocabulary
1 Scope
This International Standard provides the overview of information security management systems, and
terms and definitions commonly used in the ISMS family of standards. This International Standard is
applicable to all types and sizes of organization (e.g. commercial enterprises, government agencies, not-
for-profit organizations).
2 Terms and definitions
For the purposes of this document, the following terms and definitions apply.
2.1
access control
means to ensure that access to assets is authorized and restricted based on business and security
requirements requirements (2.63)
2.2
analytical model
algorithm or calculation combining one or more base measures (2.10) and/or derived measures (2.22)
with associated decision criteria decision criteria (2.21)
2.3
attack
attempt to destroy, expose, alter, disable, steal or gain unauthorized access to or make unauthorized
use of an asset
2.4
attribute
property or characteristic of an object (2.55) that can be distinguished quantitatively or qualitatively
by human or automated means
[SOURCE: ISO/IEC 15939:2007, modified – “entity” 2.2, modified — “entity” has been replaced by
“object” “object” in the definition.]
2.5
audit
systematic, independent and documented process (2.61) for obtaining audit evidence and evaluating it
objectively to determine the extent to which the audit criteria are fulfilled
Note 1 to entry: An audit can be an internal audit (first party) or an external audit (second party or third party),
and it can be a combined audit (combining two or more disciplines).
Note 2 to entry: “Audit evidence” and “audit criteria” are defined in ISO 19011 ISO 19011.
2.6
audit scope
extent and boundaries of an audit (2.5)
[SOURCE: ISO 19011:2011, 3.14, modified — Note 1 to entry has been deleted.]
© ISO/IEC 2016 – All rights reserved 1
ISO/IEC 27000:redline:2016(E)
2.7
authentication
provision of assurance that a claimed characteristic of an entity is correct
2.8
authenticity
property that an entity is what it is claims to be
2.9
availability
property of being accessible and usable upon demand by an authorized entity
2.10
base measure
measure (2.47) defined in terms of an attribute (2.4) and the method for quantifying it
[SOURCE: ISO/IEC 15939:2007, 2.3, modified — Note 2 to entry has been deleted.]
Note 1 to entry: A base measure is functionally independent of other measures measures (2.47).
2.11
competence
ability to apply knowledge and skills to achieve intended results
2.12
confidentiality
property that information is not made available or disclosed to unauthorized individuals, entities, or
processes (2.61)
2.13
conformity
fulfilment of a requirement (2.63)
Note 1 to entry: The term “conformance” is synonymous but deprecated.
2.14
consequence
outcome of an event (2.25) affecting objectives (2.56)
[SOURCE: ISO Guide 73:2009, 3.6.1.3, modified]
Note 1 to entry: An event event (2.25) can lead to a range of consequences.
Note 2 to entry: A consequence can be certain or uncertain and in the context of information security information
security (2.33) is usually negative.
Note 3 to entry: Consequences can be expressed qualitatively or quantitatively.
Note 4 to entry: Initial consequences can escalate through knock-on effects.
2.15
continual improvement
recurring activity to enhance performance (2.59)
2.16
control
measure that is modifying risk (2.68)
[SOURCE: ISO Guide 73:2009, 3.8.1.1]
Note 1 to entry: Controls include any process process (2.61), policy policy (2.60), device, practice, or other actions
which modify risk risk (2.68).
2 © ISO/IEC 2016 – All rights reserved
ISO/IEC 27000:redline:2016(E)
Note 2 to entry: Controls may not always exert the intended or assumed modifying effect.
2.17
control objective
statement describing what is to be achieved as a result of implementing controls (2.16)
2.18
correction
action to eliminate a detected nonconformity (2.53)
2.19
corrective action
action to eliminate the cause of a nonconformity (2.53) and to prevent recurrence
2.20
data
collection of values assigned to base measures (2.10), derived measures (2.22) and/or indicators (2.30)
[SOURCE: ISO/IEC 15939:2007, 2.4, modified — Note 1 to entry has been added.]
Note 1 to entry: This definition applies only within the context of ISO/IEC 27004:2009 ISO/IEC 27004.
2.21
decision criteria
thresholds, targets, or patterns used to determine the need for action or further investigation, or to
describe the level of confidence in a given result
[SOURCE: ISO/IEC 15939:2007, 2.7]
2.22
derived measure
measure (2.47) that is defined as a function of two or more values of base measures (2.10)
[SOURCE: ISO/IEC 15939:2007, 2.8, modified — Note 1 to entry has been deleted.]
2.23
documented information
information required to be controlled and maintained by an organization (2.57) and the medium on
which it is contained
Note 1 to entry: Documented information can be in any format and media and from any source.
Note 2 to entry: Documented information can refer to
— the management system (2.46), including related processes (2.61);
— information created in order for the organizationorganization (2.57) to operate (documentation);
— evidence of results achieved (records).
2.24
effectiveness
extent to which planned activities are realized and planned results achieved
2.25
event
occurrence or change of a particular set of circumstances
[SOURCE: ISO Guide 73:2009, 3.5.1.3, modified — Note 4 to entry has been deleted.]
Note 1 to entry: An event can be one or more occurrences, and can have several causes.
Note 2 to entry: An event can consist of something not happening.
© ISO/IEC 2016 – All rights reserved 3
ISO/IEC 27000:redline:2016(E)
Note 3 to entry: An event can sometimes be referred to as an “incident” or “accident”.
2.26
executive management
person or group of people who have delegated responsibility from the governing body (2.29) for
implementation of strategies and policies to accomplish the purpose of the organization (2.57)
Note 1 to entry: Executive management is sometimes called top management top management (2.84) and can
include Chief Executive Officers, Chief Financial Officers, Chief Information Officers, and similar roles.
2.27
external context
external environment in which the organization seeks to achieve its objectives objectives (2.56)
[SOURCE: ISO Guide 73:2009, 3.3.1.1]
Note 1 to entry: External context can include the following:
— the cultural, social, political, legal, regulatory, financial, technological, economic, natural and competitive
environment, whether international, national, regional or local;
— key drivers and trends having impact on the objectives (2.56) of the organization (2.57); and
— relationships with, and perceptions and values of, external stakeholders (2.82).
2.28
governance of information security
system by which an organization’s (2.57)information security (2.33) information security activities are
directed and controlled
2.29
governing body
person or group of people who are accountable for the performance (2.59) and conformance of the
organization (2.57)
Note 1 to entry: Governing body can in some jurisdictions be a board of directors.
2.30
indicator
measure (2.47) that provides an estimate or evaluation of specified attributes (2.4) derived from an
analytical model (2.2) with respect to defined information needs (2.31)
2.31
information need
insight necessary to manage objectives objectives (2.56), goals, risks and problems
[SOURCE: ISO/IEC 15939:2007, 2.12]
2.32
information processing facilities
any information processing system, service or infrastructure, or the physical location housing it
2.33
information security
preservation of confidentiality (2.12), integrity (2.40) and availability (2.9) of information
Note 1 to entry: In addition, other properties, such as authenticity (2.8), accountability, non-repudiation (2.54),
and reliability (2.62) can also be involved.
2.34
information security continuity
processes (2.61) and procedures for ensuring continued information security (2.33) operations
4 © ISO/IEC 2016 – All rights reserved
ISO/IEC 27000:redline:2016(E)
2.35
information security event
identified occurrence of a system, service or network state indicating a possible breach of information
security policy (2.33) policy (2.60) or failure of controls controls (2.16), or a previously unknown
situation that may be security relevant
2.36
information security incident
single or a series of unwanted or unexpected information security events (2.35) that have a significant
probability of compromising business operations and threatening information security (2.33)
2.37
information security incident management
processes (2.61) for detecting, reporting, assessing, responding to, dealing with, and learning from
information security incidents (2.36)
2.38
information sharing community
group of organizations organizations (2.57) that agree to share information
Note 1 to entry: An organization organization (2.57) can be an individual.
2.39
information system
applications, services, information technology assets, or other information handling components
2.40
integrity
property of accuracy and completeness
2.41
interested party
person or organization (2.57) that can affect, be affected by, or perceive themselves to be affected by a
decision or activity
2.42
internal context
internal environment in which the organization organization (2.57) seeks to achieve its objectives
[SOURCE: ISO Guide 73:2009, 3.3.1.2]
Note 1 to entry: Internal context can include the following:
— governance, organizational structure, roles and accountabilities;
— policiespolicies (2.60), objectivesobjectives (2.56), and the strategies that are in place to achieve them;
— the capabilities, understood in terms of resources and knowledge (e.g. capital, time, people, processesprocesses
(2.61), systems and technologies);
— information systemsinformation systems (2.39), information flows and decision-making processesprocesses
(2.61) (both formal and informal);
— relationships with, and perceptions and values of, internal stakeholdersstakeholders (2.82);
— the organization’sorganization’s (2.57) culture;
— standards, guidelines and models adopted by the organizationorganization (2.57); and
— form and extent of contractual relationships.
© ISO/IEC 2016 – All rights reserved 5
ISO/IEC 27000:redline:2016(E)
2.43
ISMS project
structured activities undertaken by an organization (2.57) to implement an ISMS
2.44
level of risk
magnitude of a risk (2.68) expressed in terms of the combination of consequences (2.14) and their
likelihood (2.45)
[SOURCE: ISO Guide 73:2009, 3.6.1.8, modified — “ “or combination of risks,” ” has been deleted in
the definition.]
2.45
likelihood
chance of something happening
[SOURCE: ISO Guide 73:2009, 3.6.1.1, modified — Notes 1 and 2 to entry have been deleted.]
2.46
management system
set of interrelated or interacting elements of an organization (2.57) to establish policies (2.60) and
objectives (2.56) and processes (2.61) to achieve those objectives
Note 1 to entry: A management system can address a single discipline or several disciplines.
Note 2 to entry: The system elements include the organization’s structure, roles and responsibilities, planning,
operation, etc .
Note 3 to entry: The scope of a management system may include the whole of the organization organization (2.57),
specific and identified functions of the organization organization (2.57), specific and identified sections of the
organization organization (2.57), or one or more functions across a group of organizations organizations (2.57).
2.47
measure
variable to which a value is assigned as the result of measurement (2.48)
[SOURCE: ISO/IEC 15939:2007, 2.15, modified]
Note 1 to entry: The term “measures” is used to refer collectively to base measures base measures (2.10), derived
measures derived measures (2.22), and indicators indicators (2.30).
2.48
measurement
process (2.61) to determine a value
Note 1 to entry: In the context of information security (2.33), the process process (2.61) of determining a value
requires information about the effectiveness (2.24) of an information security information security (2.33)
management system (2.46) and its associated controls (2.16) using a measurement method (2.50), a measurement
function (2.49), an analytical model (2.2), and decision criteria (2.21).
2.49
measurement function
algorithm or calculation performed to combine two or more base measures (2.10)
[SOURCE: ISO/IEC 15939:2007, 2.20]
6 © ISO/IEC 2016 – All rights reserved
ISO/IEC 27000:redline:2016(E)
2.50
measurement method
logical sequence of operations, described generically, used in quantifying an attribute (2.4) with respect
to a specified scale (2.80)
[SOURCE: ISO/IEC 15939:2007, 2.22, modified — Note 2 to entry has been deleted.]
Note 1 to entry: The type of measurement method depends on the nature of the operations used to quantify an
attribute attribute (2.4). Two types can be distinguished as follows:
— subjective: quantification involving human judgment;
— objective: quantification based on numerical rules.
2.51
measurement results
one or more indicators (2.30) and their associated interpretations that address an information need (2.31)
2.52
monitoring
determining the status of a system, a process (2.61) or an activity
Note 1 to entry: To determine the status, there may be a need to check, supervise or critically observe.
2.53
nonconformity
non-fulfilment of a requirement (2.63)
2.54
non-repudiation
ability to prove the occurrence of a claimed event event (2.25) or action and its originating entities
2.55
object
item characterized through the measurement (2.48) of its attributes (2.4)
2.56
objective
result to be achieved
Note 1 to entry: An objective can be strategic, tactical, or operational.
Note 2 to entry: Objectives can relate to different disciplines (such as financial, health and safety, and environmental
goals) and can apply at different levels (such as strategic, organization-wide, project, product and process (2.61).
Note 3 to entry: An objective can be expressed in other ways, e.g. as an intended outcome, a purpose, an operational
criterion, as an information security information security (2.33) objective or by the use of other words with similar
meaning (e.g. aim, goal, or target).
Note 4 to entry: In the context of information security management systems information security (2.33) management
systems (2.46), information security information security (2.33) objectives are set by the organization, consistent
with the information security policy information security (2.33) policy (2.60), to achieve specific results.
2.57
organization
person or group of people that has its own functions with responsibilities, authorities and relationships
to achieve its o bjectives objectives (2.56)
Note 1 to entry: The concept of organization includes but is not limited to sole-trader, company, corporation, firm,
enterprise, authority, partnership, charity or institution, or part or combination thereof, whether incorporated
or not, public or private.
© ISO/IEC 2016 – All rights reserved 7
ISO/IEC 27000:redline:2016(E)
2.58
outsource
make an arrangement where an external organization (2.57) performs part of an
organization’s organization’s (2.57) function or process (2.61)
Note 1 to entry: An external organization is outside the scope of the management system (2.46), although the
outsourced function or process process (2.61) is within the scope.
2.59
performance
measurable result
Note 1 to entry: Performance can relate either to quantitative or qualitative findings.
Note 2 to entry: Performance can relate to the management of activities, processes (2.61), products (including
services), systems or organizations (2.57).
2.60
policy
intentions and direction of an organization (2.57) as formally expressed by its top management (2.84)
2.61
process
set of interrelated or interacting activities which transforms inputs into outputs
2.62
reliability
property of consistent intended behaviour and results
2.63
requirement
need or expectation that is stated, generally implied or obligatory
Note 1 to entry: “Generally implied” means that it is custom or common practice for the organization organization
(2.57) and interested parties that the need or expectation under consideration is implied.
Note 2 to entry: A specified requirement is one that is stated, for example in documented information documented
information (2.23).
2.64
residual risk
risk (2.68) remaining after risk treatment (2.79)
Note 1 to entry: Residual risk can contain unidentified risk risk (2.68).
Note 2 to entry: Residual risk can also be known as “retained risk”.
2.65
review
activity undertaken to determine the suitability, adequacy and effectiveness (2.24) of the subject matter
to achieve established objectives objectives (2.54)
[SOURCE: ISO Guide 73:2009, 3.8.2.2, modified — Note 1 to entry has been deleted.]
2.66
review object
specific item being reviewed
2.67
review objective
statement describing what is to be achieved as a result of a review review (2.65)
8 © ISO/IEC 2016 – All rights reserved
ISO/IEC 27000:redline:2016(E)
2.68
risk
effect of uncertainty on objectives
[SOURCE: ISO Guide 73:2009, 1.1, modified]
Note 1 to entry: An effect is a deviation from the expected — positive or negative.
Note 2 to entry: Uncertainty is the state, even partial, of deficiency of information related to, understanding
or knowledge of, an event ( 2.25) event (2.25), its consequence ( 2.14) consequence (2.14), or likelihood
( 2.45) likelihood (2.45).
Note 3 to entry: Risk is often characterized by reference to potential events ( 2.25) events (2.25) and consequences
( 2.14) consequences (2.14), or a combination of these.
Note 4 to entry: Risk is often expressed in terms of a combination of the consequences ( 2.14) consequences (2.14)
of an event event (2.25) (including changes in circumstances) and the associated likelihood ( 2.45) likelihood (2.45)
of occurrence.
Note 5 to entry: In the context of information security management systems information security (2.33)
management systems (2.46), information security information security (2.33) risks can be expressed as effect of
uncertainty on information security objectives information security (2.33)objectives (2.56).
Note 6 to entry: Information security Information security (2.33) risk is associated with the potential that threats
(2.83) will exploit vulnerabilities (2.89) of an information asset or group of information assets and thereby cause
harm to an organization organization (2.57).
2.69
risk acceptance
informed decision to take a particular risk (2.68)
[SOURCE: ISO Guide 73:2009, 3.7.1.6]
Note 1 to entry: Risk acceptance can occur without risk treatment (2.79) or during the process process (2.61) of
risk treatment risk treatment (2.79).
Note 2 to entry: Accepted risks risks (2.68) are subject to monitoring (2.52) and review (2.65).
2.70
risk analysis
process process (2.61) to comprehend the nature of risk (2.68) and to determine the level of risk (2.44)
[SOURCE: ISO Guide 73:2009, 3.6.1]
Note 1 to entry: Risk analysis provides the basis for risk evaluation (2.74) and decisions about risk treatment (2.79).
Note 2 to entry: Risk analysis includes risk estimation.
2.71
risk assessment
overall process (2.61) of risk identification (2.75), risk analysis (2.70) and risk evaluation (2.74)
[SOURCE: ISO Guide 73:2009, 3.4.1]
2.72
risk communication and consultation
continual and iterative processes processes (2.61) that an organization conducts to provide, share or obtain
information, and to engage in dialogue with stakeholders (2.82) regarding the management of risk (2.68)
Note 1 to entry: The information can relate to the existence, nature, form, likelihood likelihood (2.45), significance,
evaluation, acceptability and treatment of risk risk (2.68).
© ISO/IEC 2016 – All rights reserved 9
ISO/IEC 27000:redline:2016(E)
Note 2 to entry: Consultation is a two-way process process (2.51) of informed communication between an
organization organization (2.57) and its stakeholders stakeholders (2.82) on an issue prior to making a decision or
determining a direction on that issue. Consultation is:
— a processprocess (2.61) which impacts on a decision through influence rather than power and
— an input to decision making, not joint decision making.
2.73
risk criteria
terms of reference against which the significance of risk (2.68) is evaluated
[SOURCE: ISO Guide 73:2009, 3.3.1.3]
Note 1 to entry: Risk criteria are based on organizational objectives, and external external (2.27) and internal
context internal context (2.42).
Note 2 to entry: Risk criteria can be derived from standards, laws, policies policies (2.60) and other
requirements requirements (2.63).
2.74
risk evaluation
process (2.61) of comparing the results of risk analysis (2.70) with risk criteria (2.73) to determine
whether the risk (2.68) and/or its magnitude is acceptable or tolerable
[SOURCE: ISO Guide 73:2009, 3.7.1]
Note 1 to entry: Risk evaluation assists in the decision about risk treatment (2.79).
2.75
risk identification
process process (2.61) of finding, recognizing and describing risks (2.68)
[SOURCE: ISO Guide 73:2009, 3.5.1]
Note 1 to entry: Risk identification involves the identification of risk sources, events events (2.25), their causes
and their potential consequences consequences (2.14).
Note 2 to entry: Risk identification can involve historical data, theoretical analysis, informed and expert opinions,
and stakeholders’ stakeholders’ (2.82) needs.
2.76
risk management
coordinated activities to direct and control an organization (2.57) with regard to risk (2.68)
[SOURCE: ISO Guide 73:2009, 2.1]
2.77
risk management process
systematic application of management policies policies (2.60), procedures and practices to the activities
of communicating, consulting, establishing the context and identifying, analysing, evaluating, treating,
monitoring and reviewing risk (2.68)
[SOURCE: ISO Guide 73:2009, 3.1, modified — Note 1 to entry has been added.]
Note 1 to entry: ISO/IEC 27005 ISO/IEC 27005 uses the term ‘ “process” (2.61’ ) to describe risk management
overall. The elements within the risk management process risk management (2.76) process (2.61) are termed
‘activities’ “activities”.
2.78
risk owner
person or entity with the accountability and authority to manage a risk (2.68)
[SOURCE: ISO Guide 73:2009, 3.5.1.5]
10 © ISO/IEC 2016 – All rights reserved
ISO/IEC 27000:redline:2016(E)
2.79
risk treatment
process (2.61) to modify risk (2.68)
[SOURCE: ISO Guide 73:2009, 3.8.1, modified — “decision” has been replaced by “choice” in Note 1 to entry.]
Note 1 to entry: Risk treatment can involve the following:
— avoiding the riskrisk (2.68) by deciding not to start or continue with the activity that gives rise to the risk (2.68);
— taking or increasing riskrisk (2.68) in order to pursue an opportunity;
— removing the riskrisk (2.68) source;
— changing the likelihoodlikelihood (2.45);
— changing the consequencesconsequences (2.14);
— sharing the riskrisk (2.68) with another party or parties (including contracts and risk financing); and
— retaining the riskrisk (2.68) by informed choice.
Note 2 to entry: Risk treatments that deal with negative consequences (2.14) are sometimes referred to as “risk
mitigation”, “risk elimination”, “risk prevention” and “risk reduction”.
Note 3 to entry: Risk treatment can create new risks risks (2.68) or modify existing risks risks (2.68).
2.80
scale
ordered set of values, continuous or discrete, or a set of categories to which the attribute (2.4) is mapped
[SOURCE: ISO/IEC 15939:2007, 2.35, modified]
Note 1 to entry: The type of scale depends on the nature of the relationship between values on the scale. Four
types of scale are commonly defined as follows:
— nominal: the measurementmeasurement (2.48) values are categorical;
— ordinal: the measurementmeasurement (2.48) values are rankings;
— interval: the measurementmeasurement (2.48) values have equal distances corresponding to equal quantities
of the attributeattribute (2.4);
— ratio: the measurementmeasurement (2.48) values have equal distances corresponding to equal quantities of
the attributeattribute (2.4), where the value of zero corresponds to none of the attribute.
These are just examples of the types of scale.
2.81
security implementation standard
document specifying authorized ways for realizing security
2.82
stakeholder
person or organization organization (2.57) that can affect, be affected by, or perceive themselves to be
affected by a decision or activity
[SOURCE: ISO Guide 73:2009, 3.2.1.1, modified — Note 1 to entry has been deleted.]
2.83
threat
potential cause of an unwanted incident, which may result in harm to a system or
organization
...
NORME ISO/IEC
INTERNATIONALE 27000
Quatrième édition
2016-02-15
Technologies de l’information —
Techniques de sécurité — Systèmes de
gestion de sécurité de l’information —
Vue d’ensemble et vocabulaire
Information technology — Security techniques — Information
security management systems — Overview and vocabulary
Numéro de référence
©
ISO/IEC 2016
DOCUMENT PROTÉGÉ PAR COPYRIGHT
© ISO/IEC 2016, Publié en Suisse
Droits de reproduction réservés. Sauf indication contraire, aucune partie de cette publication ne peut être reproduite ni utilisée
sous quelque forme que ce soit et par aucun procédé, électronique ou mécanique, y compris la photocopie, l’affichage sur
l’internet ou sur un Intranet, sans autorisation écrite préalable. Les demandes d’autorisation peuvent être adressées à l’ISO à
l’adresse ci-après ou au comité membre de l’ISO dans le pays du demandeur.
ISO copyright office
Ch. de Blandonnet 8 • CP 401
CH-1214 Vernier, Geneva, Switzerland
Tel. +41 22 749 01 11
Fax +41 22 749 09 47
copyright@iso.org
www.iso.org
ii © ISO/IEC 2016 – Tous droits réservés
Sommaire Page
Avant-propos .v
0 Introduction . 1
0.1 Vue d’ensemble . 1
0.2 La famille de normes du SMSI . 1
0.3 Objet de la présente Norme internationale . 2
1 Domaine d’application . 2
2 Termes et définitions . 3
3 Systèmes de management de la sécurité de l’information .15
3.1 Généralités .15
3.2 Qu’est-ce qu’un SMSI? .15
3.2.1 Vue d’ensemble et principes .15
3.2.2 L’information .16
3.2.3 Sécurité de l’information .16
3.2.4 Management .17
3.2.5 Système de management .17
3.3 Approche processus .17
3.4 Raisons expliquant pourquoi un SMSI est important .17
3.5 Établissement, surveillance, maintenance et amélioration d’un SMSI .18
3.5.1 Vue d’ensemble .18
3.5.2 Identifier les exigences liées à la sécurité de l’information .19
3.5.3 Apprécier les risques liés à la sécurité de l’information.19
3.5.4 Traiter les risques liés à la sécurité de l’information .20
3.5.5 Sélectionner et mettre en œuvre les mesures de sécurité .20
3.5.6 Surveiller, mettre à jour et améliorer l’efficacité du SMSI .21
3.5.7 Amélioration continue .21
3.6 Facteurs critiques de succès du SMSI .22
3.7 Avantages de la famille de normes du SMSI.22
4 La famille de normes du SMSI .23
4.1 Information générales .23
4.2 Normes donnant une vue d’ensemble et décrivant la terminologie .24
4.2.1 ISO/IEC 27000 (la présente Norme internationale) .24
4.3 Normes spécifiant des exigences .24
4.3.1 ISO/IEC 27001 .24
4.3.2 ISO/IEC 27006 .24
4.4 Normes décrivant des lignes directrices générales .25
4.4.1 ISO/IEC 27002 .25
4.4.2 ISO/IEC 27003 .25
4.4.3 ISO/IEC 27004 .25
4.4.4 ISO/IEC 27005 .25
4.4.5 ISO/IEC 27007 .25
4.4.6 ISO/IEC/TR 27008 .26
4.4.7 ISO/IEC 27013 .26
4.4.8 ISO/IEC 27014 .26
4.4.9 ISO/IEC/TR 27016 .27
4.5 Normes décrivant des lignes directrices propres à un secteur .27
4.5.1 ISO/IEC 27010 .27
4.5.2 ISO/IEC 27011 .27
4.5.3 ISO/IEC/TR 27015 .27
4.5.4 ISO/IEC 27017 .28
4.5.5 ISO/IEC 27018 .28
4.5.6 ISO/IEC/TR 27019 .28
4.5.7 ISO 27799 .29
© ISO/IEC 2016 – Tous droits réservés iii
Annexe A (informative) Formes verbales utilisées pour exprimer des dispositions .30
Annexe B (informative) Termes et propriété des termes .31
Bibliographie .35
iv © ISO/IEC 2016 – Tous droits réservés
Avant-propos
L’ISO (Organisation internationale de normalisation) et l’IEC (Commission électrotechnique
internationale) forment le système spécialisé de la normalisation mondiale. Les organismes nationaux
membres de l’ISO ou de l’IEC participent à l’élaboration de Normes internationales par l’intermédiaire de
comités techniques créés par l’organisme concerné pour traiter de domaines particuliers à une activité
technique. Les comités techniques de l’ISO et de l’IEC collaborent dans des domaines d’intérêt commun.
D’autres organismes internationaux, gouvernementaux et non gouvernementaux, en liaison avec l’ISO
et l’IEC participent également aux travaux. Dans le domaine des technologies de l’information, l’ISO et
l’IEC ont créé un comité technique mixte, l’ISO/IEC JTC 1.
Les procédures utilisées pour élaborer le présent document et celles destinées à sa mise à jour sont
décrites dans les Directives ISO/IEC, Partie 1. Il convient, en particulier, de prendre note des différents
critères d’approbation requis pour les différents types de document. Le présent document a été rédigé
conformément aux règles de rédaction données dans les Directives ISO/IEC, Partie 2 (voir http://www.
iso.org/directives).
L’attention est appelée sur le fait que certains des éléments du présent document peuvent faire l’objet de
droits de propriété intellectuelle ou de droits analogues. L’ISO ne saurait être tenue pour responsable
de ne pas avoir identifié de tels droits de propriété et averti de leur existence. Les détails concernant
les références aux droits de propriété intellectuelle ou autres droits analogues identifiés lors de
l’élaboration du document sont indiqués dans l’Introduction et/ou dans la liste des déclarations de
brevets reçues par l’ISO (voir www.iso.org/brevets).
Les appellations commerciales éventuellement mentionnées dans le présent document sont données
pour information, par souci de commodité, à l’intention des utilisateurs et ne sauraient constituer un
engagement.
Pour une explication de la signification des termes et expressions spécifiques de l’ISO liés à
l’évaluation de la conformité, ou pour toute information au sujet de l’adhésion de l’ISO aux principes
de l’OMC concernant les obstacles techniques au commerce (OTC), voir le lien suivant: Avant-propos —
Informations supplémentaires.
Le comité chargé de l’élaboration du présent document est l’ISO/IEC JTC 1, Technologies de l’information,
sous-comité SC 27, Techniques de sécurité des technologies de l’information.
Cette quatrième édition annule et remplace la troisième édition (ISO/IEC 27000:2014), qui a fait l’objet
d’une révision technique.
© ISO/IEC 2016 – Tous droits réservés v
NORME INTERNATIONALE ISO/IEC 27000:2016(F)
Technologies de l’information — Techniques de sécurité
— Systèmes de gestion de sécurité de l’information — Vue
d’ensemble et vocabulaire
0 Introduction
0.1 Vue d’ensemble
Les Normes internationales relatives aux systèmes de management fournissent un modèle en matière
d’établissement et d’exploitation d’un système de management. Ce modèle comprend les caractéristiques
que les experts dans le domaine s’accordent à reconnaître comme reflétant l’état de l’art au niveau
international. Le sous-comité ISO/IEC JTC 1/SC 27 bénéficie de l’expérience d’un comité d’experts
qui se consacre à l’élaboration des Normes internationales sur les systèmes de management pour la
sécurité de l’information, connues également comme famille de normes du Système de Management de
la Sécurité de l’Information (SMSI).
Grâce à l’utilisation de la famille de normes du SMSI, les organismes peuvent élaborer et mettre en œuvre
un cadre de référence pour gérer la sécurité de leurs actifs informationnels, y compris les informations
financières, la propriété intellectuelle, les informations sur les employés, ou les informations qui leur
sont confiées par des clients ou des tiers. Ils peuvent également utiliser ces normes pour se préparer à
une évaluation indépendante de leurs SMSI en matière de protection de l’information.
0.2 La famille de normes du SMSI
La famille de normes du SMSI (voir Article 4) a pour objet d’aider les organismes de tous types et
de toutes tailles à déployer et à exploiter un SMSI. Elle se compose des Normes internationales
suivantes (indiquées ci-dessous par ordre numérique) regroupées sous le titre général Technologies de
l’information — Techniques de sécurité:
— ISO/IEC 27000, Systèmes de management de la sécurité de l’information — Vue d’ensemble et vocabulaire
— ISO/IEC 27001, Systèmes de management de la sécurité de l’information — Exigences
— ISO/IEC 27002, Code de bonnes pratiques pour le management de la sécurité de l’information
— ISO/IEC 27003, Lignes directrices pour la mise en œuvre du système de management de la sécurité de
l’information
— ISO/IEC 27004, Management de la sécurité de l’information — Mesurage
— ISO/IEC 27005, Gestion des risques liés à la sécurité de l’information
— ISO/IEC 27006, Exigences pour les organismes procédant à l’audit et à la certification des systèmes de
management de la sécurité de l’information
— ISO/IEC 27007, Lignes directrices pour l’audit des systèmes de management de la sécurité de l’information
— ISO/IEC/TR 27008, Lignes directrices pour les auditeurs des contrôles de sécurité de l’information
— ISO/IEC 27009, Application de l’ISO/IEC 27001 à un secteur spécifique — Exigences
— ISO/IEC 27010, Gestion de la sécurité de l’information des communications intersectorielles et
interorganisationnelles
— ISO/IEC 27011, Lignes directrices du management de la sécurité de l’information pour les organismes
de télécommunications sur la base de l’ISO/IEC 27002
— ISO/IEC 27013, Guide sur la mise en œuvre intégrée de l’ISO/IEC 27001 et ISO/IEC 20000-1
— ISO/IEC 27014, Gouvernance de la sécurité de l’information
— ISO/IEC/TR 27015, Lignes directrices pour le management de la sécurité de l’information pour les
services financiers
— ISO/IEC/TR 27016, Management de la sécurité de l’information — Économie organisationnelle
— ISO/IEC 27017, Code de bonnes pratiques pour les contrôles de sécurité de l’information fondés sur
l’ISO/IEC 27002 pour les services du nuage
— ISO/IEC 27018, Code de bonnes pratiques pour la protection des informations personnelles identifiables
(PII) dans l’informatique en nuage public agissant comme processeur de PII
— ISO/IEC 27019, Lignes directrices de management de la sécurité de l’information fondées sur
l’ISO/IEC 27002 pour les systèmes de contrôle des processus spécifiques à l’industrie de l’énergie
NOTE Le titre général « Technologies de l’information — Techniques de sécurité » indique que ces Normes
internationales ont été élaborées par le comité technique mixte ISO/IEC JTC 1, Technologies de l’information,
sous-comité SC 27, Techniques de sécurité des technologies de l’information.
Les Normes internationales qui font également partie de la famille de normes du SMSI, mais qui ne sont
pas regroupées sous le même titre général, sont les suivantes:
— ISO 27799, Informatique de santé — Management de la sécurité de l’information relative à la santé en
utilisant l’ISO/IEC 27002
0.3 Objet de la présente Norme internationale
La présente Norme internationale offre une vue d’ensemble des systèmes de management de la sécurité
de l’information et définit les termes qui s’y rapportent.
NOTE L’Annexe A fournit des éclaircissements sur la façon dont les formes verbales sont utilisées pour
exprimer des exigences et/ou des préconisations dans la famille de normes du SMSI.
La famille de normes du SMSI comporte des normes qui:
a) définissent les exigences relatives à un SMSI et à ceux qui certifient de tels systèmes;
b) apportent des informations directes, des préconisations et/ou une interprétation détaillées
concernant le processus général visant à établir, mettre en œuvre, maintenir et améliorer un SMSI;
c) présentent des lignes directrices propres à des secteurs particuliers en matière de SMSI;
d) traitent de l’évaluation de la conformité d’un SMSI.
Les termes et les définitions fournis dans la présente Norme internationale:
— couvrent les termes et les définitions d’usage courant dans la famille de normes du SMSI;
— ne couvrent pas l’ensemble des termes et des définitions utilisés dans la famille de normes du SMSI;
— ne limitent pas la famille de normes du SMSI en définissant de nouveaux termes à utiliser.
1 Domaine d’application
La présente Norme internationale offre une vue d’ensemble des systèmes de management de la sécurité
de l’information, ainsi que des termes et définitions d’usage courant dans la famille de normes du SMSI.
2 © ISO/IEC 2016 – Tous droits réservés
La présente Norme internationale est applicable à tous les types et à toutes les tailles d’organismes (par
exemple: les entreprises commerciales, les organismes publics, les organismes à but non lucratif).
2 Termes et définitions
Pour les besoins du présent document, les termes et définitions suivants s’appliquent:
2.1
contrôle d’accès
moyens mis en œuvre pour assurer que l’accès aux actifs est autorisé et limité selon les exigences (2.63)
propres à la sécurité et à l’activité métier
2.2
modèle analytique
algorithme ou calcul combinant une ou plusieurs mesures élémentaires (2.10) et/ou mesures
dérivées (2.22) avec les critères de décision associés (2.21)
2.3
attaque
tentative de détruire, de rendre public, de modifier, d’invalider, de voler ou d’utiliser sans autorisation
un actif, ou de faire un usage non autorisé de celui-ci
2.4
attribut
propriété ou caractéristique d’un objet (2.55) qui peut être distingué quantitativement ou
qualitativement par des moyens humains ou automatiques
[SOURCE: ISO/IEC 15939:2007, 2.2, modifiée — Le terme « entité » a été remplacé par « objet » dans la
définition.]
2.5
audit
processus (2.61) méthodique, indépendant et documenté permettant d’obtenir des preuves d’audit et de
les évaluer de manière objective pour déterminer dans quelle mesure les critères d’audit sont satisfaits
Note 1 à l’article: Un audit peut être interne (audit de première partie), externe (audit de seconde ou de tierce
partie) ou combiné (associant deux disciplines ou plus).
Note 2 à l’article: Les termes « preuves d’audit » et « critères d’audit » sont définis dans l’ISO 19011.
2.6
champ de l’audit
étendue et limites d’un audit (2.5)
[SOURCE: ISO 19011:2011, 3.14, modifiée — Suppression de la note 1 à l’article.]
2.7
authentification
méthode permettant de garantir qu’une caractéristique revendiquée pour une entité est correcte
2.8
authenticité
propriété selon laquelle une entité est ce qu’elle revendique être
2.9
disponibilité
propriété d’être accessible et utilisable à la demande par une entité autorisée
© ISO/IEC 2016 – Tous droits réservés 3
2.10
mesure élémentaire
mesure (2.47) définie en fonction d’un attribut (2.4) et de la méthode de mesurage spécifiée pour le
quantifier
[SOURCE: ISO/IEC 15939:2007, 2.3, modifiée — Suppression de la note 2 à l’article.]
Note 1 à l’article: Une mesure élémentaire est fonctionnellement indépendante des autres mesures (2.47).
2.11
compétence
capacité à appliquer des connaissances et des aptitudes pour obtenir les résultats escomptés
2.12
confidentialité
propriété selon laquelle l’information n’est pas diffusée ni divulguée à des personnes, des entités ou des
processus (2.61) non autorisés
2.13
conformité
satisfaction d’une exigence (2.63)
Note 1 à l’article: Le terme anglais « conformance » est un synonyme, mais il est déconseillé.
2.14
conséquence
effet d’un événement (2.25) affectant les objectifs (2.56)
[SOURCE: Guide ISO 73:2009, 3.6.1.3, modifié]
Note 1 à l’article: Un événement (2.25) peut entraîner une série de conséquences.
Note 2 à l’article: Une conséquence peut être certaine ou incertaine. Dans le contexte de la sécurité de l’information
(2.33), elle est généralement négative.
Note 3 à l’article: Les conséquences peuvent être exprimées de façon qualitative ou quantitative.
Note 4 à l’article: Des conséquences initiales peuvent déclencher des réactions en chaîne.
2.15
amélioration continue
activité régulière destinée à améliorer les performances (2.59)
2.16
mesure de sécurité
mesure qui modifie un risque (2.68)
[SOURCE: Guide ISO 73:2009, 3.8.1.1]
Note 1 à l’article: Les mesures de sécurité comprennent tous les processus (2.61), politiques (2.60), dispositifs,
pratiques ou autres actions qui modifient un risque (2.68).
Note 2 à l’article: Les mesures de sécurité ne peuvent pas toujours aboutir à la modification voulue ou supposée.
2.17
objectif d’une mesure de sécurité
déclaration décrivant ce qui est attendu de la mise en œuvre des mesures de sécurité (2.16)
2.18
correction
action visant à éliminer une non-conformité (2.53) détectée
4 © ISO/IEC 2016 – Tous droits réservés
2.19
action corrective
action visant à éliminer la cause d’une non-conformité (2.53) et à empêcher qu’elle ne se répète
2.20
données
ensemble des valeurs attribuées aux mesures élémentaires (2.10), mesures dérivées (2.22) et/ou aux
indicateurs (2.30)
[SOURCE: ISO/IEC 15939:2007, 2.4, modifiée — Ajout de la note 1 à l’article.]
Note 1 à l’article: Cette définition s’applique uniquement dans le contexte de l’ISO/IEC 27004.
2.21
critères de décision
seuils, cibles ou modèles utilisés pour déterminer la nécessité d’une action ou d’un complément
d’enquête, ou pour décrire le niveau de confiance dans un résultat donné
[SOURCE: ISO/IEC 15939:2007, 2.7]
2.22
mesure dérivée
mesure (2.47) définie en fonction d’au moins deux mesures élémentaires (2.10)
[SOURCE: ISO/IEC 15939:2007, 2.8, modifiée — Suppression de la note 1 à l’article.]
2.23
informations documentées
informations devant être contrôlées et mises à jour par un organisme (2.57) et le support sur lequel
elles sont stockées
Note 1 à l’article: Les informations documentées peuvent être dans n’importe quel format, sur n’importe quel
support et provenir de n’importe quelle source.
Note 2 à l’article: Les informations documentées peuvent se rapporter:
— au système de management (2.46) et aux processus (2.61) associés;
— aux informations créées pour permettre à l’organisme (2.57) de fonctionner (documentation);
— aux preuves des résultats obtenus (enregistrements).
2.24
efficacité
niveau de réalisation des activités planifiées et d’obtention des résultats escomptés
2.25
événement
occurrence ou changement d’un ensemble particulier de circonstances
[SOURCE: Guide ISO 73:2009, 3.5.1.3, modifié — Suppression de la note 4 à l’article.]
Note 1 à l’article: Un événement peut être unique ou se reproduire. Il peut avoir plusieurs causes.
Note 2 à l’article: Un événement peut consister en quelque chose qui ne se produit pas.
Note 3 à l’article: Un événement peut parfois être qualifié « d’incident » ou « d’accident ».
© ISO/IEC 2016 – Tous droits réservés 5
2.26
management exécutif
personne ou groupe de personnes ayant reçu des instances dirigeantes (2.29) la responsabilité de la
mise en œuvre des stratégies et politiques afin d’atteindre les objectifs de l’organisme (2.57)
Note 1 à l’article: Le management exécutif est parfois appelé la direction (2.84). Il peut comprendre les présidents
directeurs généraux, les directeurs financiers, les directeurs des systèmes d’information et autres fonctions
similaires.
2.27
contexte externe
environnement externe dans lequel l’organisme cherche à atteindre ses objectifs (2.56)
[SOURCE: Guide ISO 73:2009, 3.3.1.1]
Note 1 à l’article: Le contexte externe peut inclure les aspects suivants:
— l’environnement culturel, social, politique, légal, réglementaire, financier, technologique, économique,
naturel et concurrentiel, au niveau international, national, régional ou local;
— les facteurs clés et tendances ayant un impact déterminant sur les objectifs (2.56) de l’organisme (2.57);
— les relations avec les parties prenantes (2.82) externes, les perceptions et valeurs relatives à celles-ci.
2.28
gouvernance de la sécurité de l’information
système par lequel un organisme (2.57) conduit et supervise les activités liées à la sécurité de
l’information (2.33)
2.29
instances dirigeantes
personne ou groupe de personnes ayant la responsabilité des performances (2.59) et de la conformité de
l’organisme (2.57)
Note 1 à l’article: Dans certaines juridictions, les instances dirigeantes peuvent être constituées d’un conseil
d’administration.
2.30
indicateur
mesure (2.47) qui fournit une estimation ou une évaluation des attributs (2.4) spécifiés à partir d’un
modèle analytique (2.2) concernant les besoins d’information (2.31) définis
2.31
besoin d’information
information nécessaire pour gérer les objectifs (2.56), les buts, les risques et les problèmes
[SOURCE: ISO/IEC 15939:2007, 2.12]
2.32
moyens de traitement de l’information
tout système, service ou infrastructure de traitement de l’information, ou le local les abritant
2.33
sécurité de l’information
protection de la confidentialité (2.12), de l’intégrité (2.40) et de la disponibilité (2.9) de l’information
Note 1 à l’article: En outre, d’autres propriétés, telles que l’authenticité (2.8), l’imputabilité, la non-répudiation (2.54)
et la fiabilité (2.62) peuvent également être concernées.
2.34
continuité de la sécurité de l’information
processus (2.61) et procédures visant à assurer la continuité des opérations liées à la sécurité de
l’information (2.33)
6 © ISO/IEC 2016 – Tous droits réservés
2.35
événement lié à la sécurité de l’information
occurrence identifiée de l’état d’un système, d’un service ou d’un réseau indiquant une faille possible
dans la politique (2.60) de sécurité de l’information (2.33) ou un échec des mesures de sécurité (2.16), ou
encore une situation inconnue jusqu’alors et pouvant relever de la sécurité
2.36
incident lié à la sécurité de l’information
un ou plusieurs événements liés à la sécurité de l’information (2.35), indésirables ou inattendus,
présentant une probabilité forte de compromettre les opérations liées à l’activité de l’organisme et de
menacer la sécurité de l’information (2.33)
2.37
gestion des incidents liés à la sécurité de l’information
processus (2.61) visant à détecter, rapporter, apprécier, gérer et résoudre les incidents liés à la sécurité de
l’information (2.36), ainsi qu’à en tirer des enseignements
2.38
communauté de partage d’informations
groupe d’organismes (2.57) qui s’accordent pour partager les informations
Note 1 à l’article: Un organisme (2.57) peut être un individu.
2.39
système d’information
applications, services, actifs informationnels ou autres composants permettant de gérer l’information
2.40
intégrité
propriété d’exactitude et de complétude
2.41
partie intéressée
personne ou organisme (2.57) susceptible d’affecter, d’être affecté ou de se sentir lui-même affecté par
une décision ou une activité
2.42
contexte interne
environnement interne dans lequel l’organisme (2.57) cherche à atteindre ses objectifs
[SOURCE: Guide ISO 73:2009, 3.3.1.2]
Note 1 à l’article: Le contexte interne peut inclure les aspects suivants:
— la gouvernance, la structure organisationnelle, les rôles et les responsabilités;
— les politiques (2.60), objectifs (2.56) et stratégies mises en place pour atteindre ces derniers;
— les capacités, en termes de ressources et de connaissances (par exemple: capital, temps, personnel,
processus (2.61), systèmes et technologies);
— les systèmes d’information (2.39), flux d’information et processus (2.61) de prise de décision (formels et
informels);
— les relations avec les parties prenantes (2.82) internes, les perceptions et valeurs associées à celles-ci;
— la culture de l’organisme (2.57);
— les normes, lignes directrices et modèles adoptés par l’organisme (2.57);
— la forme et l’étendue des relations contractuelles.
© ISO/IEC 2016 – Tous droits réservés 7
2.43
projet SMSI
activités structurées entreprises par un organisme (2.57) pour déployer un SMSI
2.44
niveau de risque
importance d’un risque (2.68) exprimée en termes de combinaison des conséquences (2.14) et de leur
vraisemblance (2.45)
[SOURCE: Guide ISO 73:2009, 3.6.1.8, modifié — Suppression de « ou combinaison de risques » de la
définition.]
2.45
vraisemblance
possibilité qu’un événement survienne
[SOURCE: Guide ISO 73:2009, 3.6.1.1, modifié — Suppression des notes 1 et 2 à l’article.]
2.46
système de management
ensemble d’éléments corrélés ou interactifs d’un organisme (2.57) visant à établir des politiques (2.60),
des objectifs (2.56) et des processus (2.61) permettant d’atteindre ces objectifs
Note 1 à l’article: Un système de management peut recouvrir une ou plusieurs disciplines.
Note 2 à l’article: Les éléments du système comprennent la structure de l’organisme, les rôles et responsabilités,
la planification et les opérations.
Note 3 à l’article: Le domaine d’application d’un système de management peut comprendre l’organisme (2.57)
dans son ensemble, certaines des fonctions spécifiques et identifiées de l’organisme (2.57), certaines des
sections spécifiques et identifiées de l’organisme (2.57), ou bien une ou plusieurs fonctions au sein d’un groupe
d’organismes (2.57).
2.47
mesure
variable à laquelle on attribue une valeur correspondant au résultat du mesurage (2.48)
[SOURCE: ISO/IEC 15939:2007, 2.15, modifiée]
Note 1 à l’article: Le terme « mesures » est utilisé pour désigner collectivement les mesures élémentaires (2.10),
les mesures dérivées (2.22) et les indicateurs (2.30).
2.48
mesurage
processus (2.61) permettant de déterminer une valeur
Note 1 à l’article: Dans le contexte de la sécurité de l’information (2.33), le processus (2.61) de détermination d’une
valeur nécessite des informations concernant l’efficacité (2.24) d’un système de management (2.46) de la sécurité
de l’information (2.33) et des mesures de sécurité (2.16) associées à l’aide d’une méthode de mesurage (2.50), d’une
fonction de mesurage (2.49), d’un modèle analytique (2.2) et de critères de décision (2.21).
2.49
fonction de mesurage
algorithme ou calcul utilisé pour combiner au moins deux mesures élémentaires (2.10)
[SOURCE: ISO/IEC 15939:2007, 2.20]
8 © ISO/IEC 2016 – Tous droits réservés
2.50
méthode de mesurage
suite logique d’opérations décrites de manière générique qui permettent de quantifier un attribut (2.4)
selon une échelle (2.80) spécifiée
[SOURCE: ISO/IEC 15939:2007, 2.22, modifiée — Suppression de la note 2 à l’article.]
Note 1 à l’article: Le type de méthode de mesurage employé dépend de la nature des opérations utilisées pour
quantifier un attribut (2.4). On peut en distinguer deux:
— le type subjectif: quantification faisant appel au jugement humain;
— le type objectif: quantification fondée sur des règles numériques.
2.51
résultats de mesurage
un ou plusieurs indicateurs (2.30) et les interprétations associées, répondant à un besoin
d’information (2.31)
2.52
surveillance
détermination du statut d’un système, d’un processus (2.61) ou d’une activité
Note 1 à l’article: Pour déterminer le statut, il peut s’avérer nécessaire de vérifier, de superviser ou d’observer de
manière critique.
2.53
non-conformité
non-satisfaction d’une exigence (2.63)
2.54
non-répudiation
capacité à prouver l’occurrence d’un événement (2.25) ou d’une action donnée(e) et des entités qui en
sont à l’origine
2.55
objet
élément caractérisé par le mesurage (2.48) de ses attributs (2.4)
2.56
objectif
résultat à atteindre
Note 1 à l’article: Un objectif peut être stratégique, tactique ou opérationnel.
Note 2 à l’article: Les objectifs peuvent concerner différentes disciplines (par exemple: finance, santé, sécurité ou
environnement) et différents niveaux (par exemple: au niveau stratégique, à l’échelle de l’organisme, au niveau
d’un projet, d’un produit et d’un processus (2.61).
Note 3 à l’article: Un objectif peut être exprimé de différentes manières, par exemple: résultat recherché, but à
atteindre, critère opérationnel, objectif en matière de sécurité de l’information (2.33), ou à l’aide d’autres mots de
sens similaire (par exemple: intention ou cible).
Note 4 à l’article: Dans le contexte des systèmes de management (2.46) de la sécurité de l’information (2.33), les
objectifs de sécurité de l’information (2.33) sont définis par l’organisme, conformément à la politique (2.60) de
sécurité de l’information (2.33), afin d’obtenir des résultats spécifiques.
© ISO/IEC 2016 – Tous droits réservés 9
2.57
organisme
personne ou groupe de personnes qui exerce ses propres fonctions associées aux responsabilités,
pouvoirs et relations nécessaires pour atteindre ses objectifs (2.56)
Note 1 à l’article: Le concept d’organisme inclut, sans s’y limiter, les travailleurs indépendants, compagnies,
sociétés, firmes, entreprises, autorités, partenariats, œuvres de bienfaisance ou institutions, ou toute partie ou
combinaison de ceux-ci, constituée en société de capitaux ou ayant un autre statut, de droit privé ou public.
2.58
externaliser
prendre des dispositions pour qu’un organisme (2.57) externe prenne en charge une partie des fonctions
ou des processus (2.61) d’un organisme (2.57)
Note 1 à l’article: Un organisme externe se situe hors du domaine d’application du système de management (2.46),
mais les fonctions ou processus (2.61) externalisés entrent dans le cadre de celui-ci.
2.59
performance
résultat mesurable
Note 1 à l’article: La performance peut se rapporter à des observations quantitatives ou qualitatives.
Note 2 à l’article: La performance peut se rapporter au management des activités, des processus (2.61), des
produits (y compris les services), des systèmes ou des organismes (2.57).
2.60
politique
intentions et orientation d’un organisme (2.57) telles que formalisées par sa direction (2.84)
2.61
processus
ensemble d’activités corrélées ou interactives qui transforme des éléments d’entrée en éléments de sortie
2.62
fiabilité
propriété relative à un comportement et des résultats prévus et cohérents
2.63
exigence
besoin ou attente formulé, généralement implicite ou obligatoire
Note 1 à l’article: « Généralement implicite » signifie qu’il est habituel ou courant, pour l’organisme (2.57) et les
parties intéressées, que le besoin ou l’attente en question soit implicite.
Note 2 à l’article: Une exigence spécifiée est une exigence formulée, par exemple une information documentée (2.23).
2.64
risque résiduel
risque (2.68) subsistant après le traitement du risque (2.79)
Note 1 à l’article: Un risque résiduel peut inclure un risque (2.68) non identifié.
Note 2 à l’article: Un risque résiduel peut également être appelé « risque conservé ».
2.65
revue
activité entreprise afin de déterminer l’adaptation, l’adéquation et l’efficacité (2.24) de l’objet étudié
pour atteindre les objectifs (2.54) établis
[SOURCE: Guide ISO 73:2009, 3.8.2.2, modifié — Suppression de la note 1 à l’article.]
10 © ISO/IEC 2016 – Tous droits réservés
2.66
objet de revue
élément spécifique soumis à la revue
2.67
objectif de revue
déclaration décrivant le résultat attendu d’une revue (2.65)
2.68
risque
effet de l’incertitude sur l’atteinte des objectifs
[SOURCE: Guide ISO 73:2009, 1.1, modifié]
Note 1 à l’article: Un effet est un écart, positif ou négatif, par rapport à une attente.
Note 2 à l’article: L’incertitude est l’état, même partiel, de défaut d’information concernant la compréhension ou
la connaissance d’un événement (2.25), de ses conséquences (2.14) ou de sa vraisemblance (2.45).
Note 3 à l’article: Un risque est souvent caractérisé en référence à des événements (2.25) et des conséquences (2.14)
potentiels ou à une combinaison des deux.
Note 4 à l’article: Un risque est souvent exprimé en termes de combinaison des conséquences (2.14) d’un événement
(2.25) (incluant des changements de circonstances) et de sa vraisemblance (2.45).
Note 5 à l’article: Dans le contexte des systèmes de management (2.46) de la sécurité de l’information (2.33),
les risques liés à la sécurité de l’information (2.33) peuvent être exprimés comme l’effet de l’incertitude sur les
objectifs (2.56) de sécurité de l’information (2.33).
Note 6 à l’article: Le risque lié à la sécurité de l’information (2.33) est associé à la possibilité que des menaces (2.83)
exploitent les vulnérabilités (2.89) d’un actif ou d’un groupe d’actifs informationnels et nuisent donc à un
organisme (2.57).
2.69
acceptation du risque
décision argumentée en faveur de la prise d’un risque (2.68) particulier
[SOURCE: Guide ISO 73:2009, 3.7.1.6]
Note 1 à l’article: L’acceptation du risque peut avoir lieu sans traitement du risque (2.79) ou lors du processus (2.61)
de traitement du risque (2.79).
Note 2 à l’article: Les risques (2.68) acceptés font l’objet d’une surveillance (2.52) et d’une revue (2.65).
2.70
analyse du risque
processus (2.61) mis en œuvre pour comprendre la nature d’un risque (2.68) et pour déterminer le
niveau de risque (2.44)
[SOURCE: Guide ISO 73:2009, 3.6.1]
Note 1 à l’article: L’analyse du risque fournit la base de l’évaluation du risque (2.74) et des décisions relatives au
traitement du risque (2.79).
Note 2 à l’article: L’analyse du risque inclut l’estimation du risque.
2.71
appréciation du risque
ensemble du processus (2.61) d’identification du risque (2.75), d’analyse du risque (2.70) et d’évaluation
du risque (2.74)
[SOURCE: Guide ISO 73:2009, 3.4.1]
© ISO/IEC 2016 – Tous droits réservés 11
2.72
communication et concertation relatives au risque
processus (2.61) itératifs et continus mis en œuvre par un organisme afin de fournir, partager ou obtenir
des informations et d’engager un dialogue avec les parties prenantes (2.82) en ce qui concerne la gestion
du risque (2.68)
Note 1 à l’article: Ces informations peuvent concerner l’existence, la nature, la forme, la vraisemblance (2.45),
l’importance, l’évaluation, l’acceptabilité et le traitement du risque (2.68).
Note 2 à l’article: La concertation est un processus (2.51) de communication argumentée à double sens entre un
organisme (2.57) et ses parties prenantes (2.82) sur une question donnée avant de prendre une décision ou de
déterminer une orientation concernant cette question. La concertation est:
— un processus (2.61) dont l’effet sur une décision s’exerce par l’influence plutôt que par le pouvoir, et
— une contribution à une prise de décision, et non une prise de décision conjointe.
2.73
critères de risque
termes de référence vis-à-vis desquels l’importance d’un risque (2.68) est évaluée
[SOURCE: Guide ISO 73:2009, 3.3.1.3]
Note 1 à l’article: Les critères de risque sont fondés sur les objectifs de l’organisme et sur le contexte externe (2.27)
et interne (2.42).
Note 2 à l’article: Les critères de risque peuvent être issus de normes, de lois, de politiques (2.60) et d’autres
exigences (2.63).
2.74
évaluation du risque
processus (2.61) de comparaison des résultats de l’analyse du risque (2.70) avec les critères du
risque (2.73) afin de déterminer si le risque (2.68) et/ou son importance sont acceptables ou tolérables
[SOURCE: Guide ISO 73:2009, 3.7.1]
Note 1 à l’article: L’évaluation du risque aide à la prise de décision relative au traitement du risque (2.79).
2.75
identification du risque
processus (2.61) de recherche, de reconnaissance et de description des risques (2.68)
[SOURCE: Guide ISO 73:2009, 3.5.1]
Note 1 à l’article: L’identification du risque comprend l’identification des sources de risque, des événements (2.25),
de leurs causes et de leurs conséquences (2.14) potentielles.
Note 2 à l’article: L’identification du risque peut faire appel à des données historiques, des analyses théoriques
et des avis d’experts et autres personnes compétentes, et tenir compte des besoins des parties prenantes (2.82).
2.76
management du risque
activités coordonnées visant à diriger et contrôler un organisme (2.57) vis-à-vis du risque (2.68)
[SOURCE: Guide ISO 73:2009, 2.1]
12 © ISO/IEC 2016 – Tous droits réservés
2.77
processus de management du risque
application systématique de politiques (2.60), procédures et pratiques de management aux activités de
communication, de concertation, d’établissement du contexte, et aux activités d’identification, d’analyse,
d’évaluation, de traitement, de surveillance et de revue du risque (2.68)
[SOURCE: Guide ISO 73:2009, 3.1, modifié — Ajout de la note 1 à l’article.]
Note 1 à l’article: L’ISO/IEC 27005 emploie le terme « processus » (2.61) pour décrire le management du risque
dans sa globalité. Les éléments qui composent le processus (2.61) de management du risque (2.76) sont appelés
« activités ».
Note 2 à l’article:
Note 3 à l’article:
2.78
propriétaire du risque
personne ou entité ayant la responsabilité du risque (2.68) et ayant autorité pour le gérer
[SOURCE: Guide ISO 73:2009, 3.5.1.5]
2.79
traitement du risque
processus (2.61) destiné à modifier un risque (2.68)
[SOURCE: Guide ISO 73:2009, 3.8.1, modifié — « décision » a été remplacé par « choix » dans la note 1 à
l’article.]
Not
...

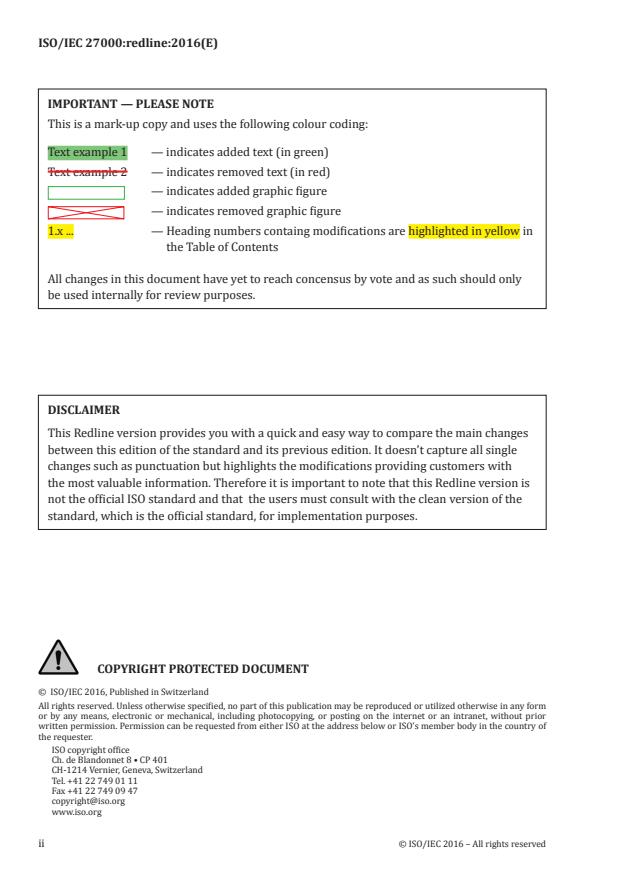
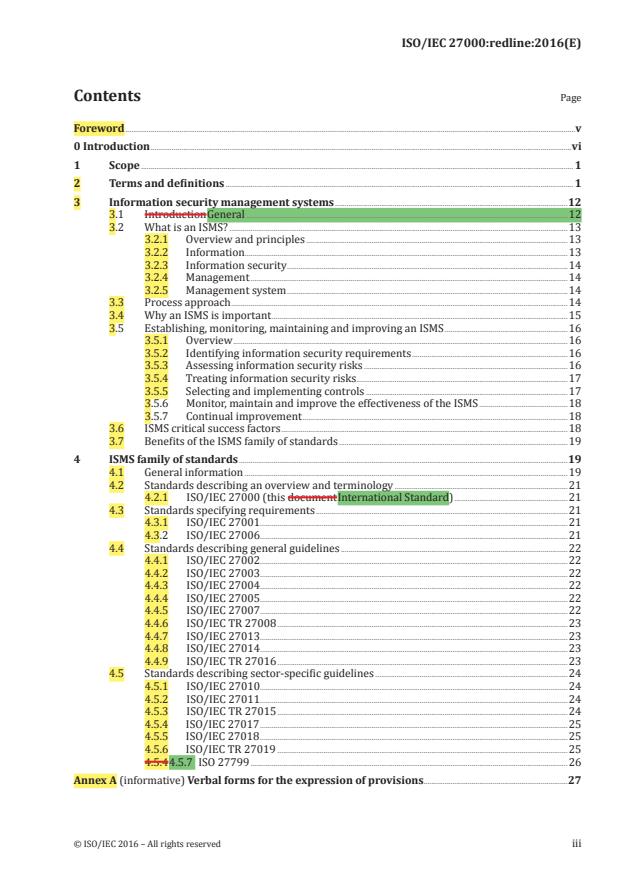


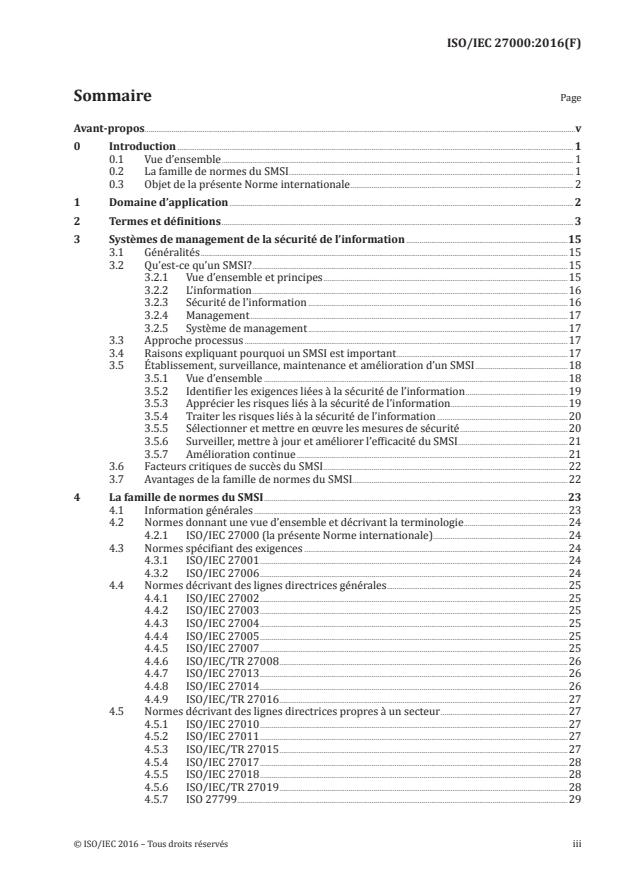
Questions, Comments and Discussion
Ask us and Technical Secretary will try to provide an answer. You can facilitate discussion about the standard in here.
Loading comments...