ETSI TS 118 111 V2.4.1 (2016-09)
oneM2M; Common Terminology (oneM2M TS-0011 version 2.4.1 Release 2)
oneM2M; Common Terminology (oneM2M TS-0011 version 2.4.1 Release 2)
RTS/oneM2M-000011v200
General Information
Standards Content (Sample)
TECHNICAL SPECIFICATION
oneM2M;
Common Terminology
(oneM2M TS-0011 version 2.4.1 Release 2)
(oneM2M TS-0011 version 2.4.1 Release 2) 2 ETSI TS 118 111 V2.4.1 (2016-09)
Reference
RTS/oneM2M-000011v200
Keywords
IoT, M2M, terminology
ETSI
650 Route des Lucioles
F-06921 Sophia Antipolis Cedex - FRANCE
Tel.: +33 4 92 94 42 00 Fax: +33 4 93 65 47 16
Siret N° 348 623 562 00017 - NAF 742 C
Association à but non lucratif enregistrée à la
Sous-Préfecture de Grasse (06) N° 7803/88
Important notice
The present document can be downloaded from:
http://www.etsi.org/standards-search
The present document may be made available in electronic versions and/or in print. The content of any electronic and/or
print versions of the present document shall not be modified without the prior written authorization of ETSI. In case of any
existing or perceived difference in contents between such versions and/or in print, the only prevailing document is the
print of the Portable Document Format (PDF) version kept on a specific network drive within ETSI Secretariat.
Users of the present document should be aware that the document may be subject to revision or change of status.
Information on the current status of this and other ETSI documents is available at
https://portal.etsi.org/TB/ETSIDeliverableStatus.aspx
If you find errors in the present document, please send your comment to one of the following services:
https://portal.etsi.org/People/CommiteeSupportStaff.aspx
Copyright Notification
No part may be reproduced or utilized in any form or by any means, electronic or mechanical, including photocopying
and microfilm except as authorized by written permission of ETSI.
The content of the PDF version shall not be modified without the written authorization of ETSI.
The copyright and the foregoing restriction extend to reproduction in all media.
© European Telecommunications Standards Institute 2016.
All rights reserved.
TM TM TM
DECT , PLUGTESTS , UMTS and the ETSI logo are Trade Marks of ETSI registered for the benefit of its Members.
TM
3GPP and LTE™ are Trade Marks of ETSI registered for the benefit of its Members and
of the 3GPP Organizational Partners.
GSM® and the GSM logo are Trade Marks registered and owned by the GSM Association.
ETSI
(oneM2M TS-0011 version 2.4.1 Release 2) 3 ETSI TS 118 111 V2.4.1 (2016-09)
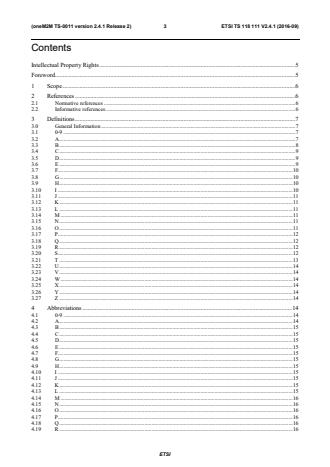
Contents
Intellectual Property Rights . 5
Foreword . 5
1 Scope . 6
2 References . 6
2.1 Normative references . 6
2.2 Informative references . 6
3 Definitions . 7
3.0 General Information . 7
3.1 0-9 . 7
3.2 A . 7
3.3 B . 8
3.4 C . 9
3.5 D . 9
3.6 E . 9
3.7 F. 10
3.8 G . 10
3.9 H . 10
3.10 I . 10
3.11 J . 11
3.12 K . 11
3.13 L . 11
3.14 M . 11
3.15 N . 11
3.16 O . 11
3.17 P. 12
3.18 Q . 12
3.19 R . 12
3.20 S. 12
3.21 T . 13
3.22 U . 14
3.23 V . 14
3.24 W . 14
3.25 X . 14
3.26 Y . 14
3.27 Z . 14
4 Abbreviations . 14
4.1 0-9 . 14
4.2 A . 14
4.3 B . 15
4.4 C . 15
4.5 D . 15
4.6 E . 15
4.7 F. 15
4.8 G . 15
4.9 H . 15
4.10 I . 15
4.11 J . 15
4.12 K . 15
4.13 L . 15
4.14 M . 16
4.15 N . 16
4.16 O . 16
4.17 P. 16
4.18 Q . 16
4.19 R . 16
ETSI
(oneM2M TS-0011 version 2.4.1 Release 2) 4 ETSI TS 118 111 V2.4.1 (2016-09)
4.20 S. 16
4.21 T . 16
4.22 U . 16
4.23 V . 16
4.24 W . 17
4.25 X . 17
4.26 Y . 17
4.27 Z . 17
Annex A (informative): Bibliography . 18
History . 19
ETSI
(oneM2M TS-0011 version 2.4.1 Release 2) 5 ETSI TS 118 111 V2.4.1 (2016-09)
Intellectual Property Rights
IPRs essential or potentially essential to the present document may have been declared to ETSI. The information
pertaining to these essential IPRs, if any, is publicly available for ETSI members and non-members, and can be found
in ETSI SR 000 314: "Intellectual Property Rights (IPRs); Essential, or potentially Essential, IPRs notified to ETSI in
respect of ETSI standards", which is available from the ETSI Secretariat. Latest updates are available on the ETSI Web
server (https://ipr.etsi.org/).
Pursuant to the ETSI IPR Policy, no investigation, including IPR searches, has been carried out by ETSI. No guarantee
can be given as to the existence of other IPRs not referenced in ETSI SR 000 314 (or the updates on the ETSI Web
server) which are, or may be, or may become, essential to the present document.
Foreword
This Technical Specification (TS) has been produced by ETSI Partnership Project oneM2M (oneM2M).
ETSI
(oneM2M TS-0011 version 2.4.1 Release 2) 6 ETSI TS 118 111 V2.4.1 (2016-09)
1 Scope
The present document contains a collection of specialist technical terms, definitions and abbreviations referenced within
the oneM2M specifications.
Having a common collection of definitions and abbreviations related to oneM2M documents will:
• ensure that the terminology is used in a consistent manner across oneM2M documents;
• provide a reader with convenient reference for technical terms that are used across multiple documents.
The present document provides a tool for further work on oneM2M technical documentation and facilitates their
understanding. The definitions and abbreviations as given in the present document are either externally created and
included here, or created internally within oneM2M by the oneM2M TP or its working groups, whenever the need for
precise vocabulary is identified or imported from existing documentation.
In addition in oneM2M Technical Specifications and Technical Reports there are also clauses dedicated for locally
unique definitions and abbreviations.
2 References
2.1 Normative references
References are either specific (identified by date of publication and/or edition number or version number) or
non-specific. For specific references, only the cited version applies. For non-specific references, the latest version of the
referenced document (including any amendments) applies.
Referenced documents which are not found to be publicly available in the expected location might be found at
https://docbox.etsi.org/Reference/.
NOTE: While any hyperlinks included in this clause were valid at the time of publication, ETSI cannot guarantee
their long term validity.
The following referenced documents are necessary for the application of the present document.
Not applicable.
2.2 Informative references
References are either specific (identified by date of publication and/or edition number or version number) or
non-specific. For specific references, only the cited version applies. For non-specific references, the latest version of the
referenced document (including any amendments) applies.
NOTE: While any hyperlinks included in this clause were valid at the time of publication, ETSI cannot guarantee
their long term validity.
The following referenced documents are not necessary for the application of the present document but they assist the
user with regard to a particular subject area.
[i.1] Recommendation ITU-T X.800 (1991): "Security architecture for open system interconnection for
CCIT applications".
[i.2] Recommendation ITU-T X.800/Amd.1 (1996): "Security architecture for open systems
interconnection for CCITT applications. Amendment 1: Layer Two Security Service and
Mechanisms for LANs".
[i.3] ISO/IEC 27001 (2005): "Information technology - Security techniques - Information security
management systems - Requirements".
ETSI
(oneM2M TS-0011 version 2.4.1 Release 2) 7 ETSI TS 118 111 V2.4.1 (2016-09)
[i.4] ISO/IEC 27002 (2005): "Information technology - Security techniques - Code of practice for
information security management".
[i.5] IETF RFC 4949 (2007): "Internet Security Glossary, Version 2".
[i.6] NIST SP800-57 Part 1 (07/2012): "Recommendation for Key Management - General, Rev3".
[i.7] NIST SP800-57 Part 1 (05/2011): "Recommendation for Key Management - General, Rev3".
rd
[i.8] ISO/IEC 13888-1 (07/2009 - 3 ed) Information technology - Security techniques - Non-
repudiation - Part 1: General".
st
[i.9] ISO/IEC 24760-1 (12/2011 - 1 edition): "Information technology - Security techniques - A
framework for identity management - Part 1: terminology and concepts".
st
[i.10] ISO/IEC 27004 (12/2009 - 1 edition): "Information technology - Security techniques -
Information security management - Measurement".
rd
[i.11] ISO/IEC 9798-1 (07/2010 - 3 edition): "Information technology - Security techniques - Entity
authentication -. Part 1: General".
[i.12] ISO/IEC TR 15443-1:2012: "Information technology - Security techniques - Security assurance
framework - Part 1: Introduction and concepts".
TM
[i.13] IEEE 802.15.4 -2003: "IEEE Standard for Local and metropolitan area networks -
Part 15.4: Low-Rate Wireless Personal Area Networks (LR-WPANs)".
[i.14] OMA OMA-TS-LightweightM2M-V1_0-20141111-D: "Lightweight Machine to Machine
Technical Specification".
3 Definitions
3.0 General Information
NOTE 1: Whenever in the present document a term "M2M Xyz" (e.g. M2M Application, M2M Solution, etc.) is
used, then the prefix "M2M" should indicate that - unless otherwise indicated - the term identifies an
entity Xyz that complies with oneM2M specifications.
NOTE 2: For better readability of the present document the prefix "M2M" is ignored when definitions are
alphabetically ordered.
3.1 0-9
Void.
3.2 A
Abstract Information Model: Information Model of common functionalities abstracted from a set of Device
Information Models
Abstraction: process of mapping between a set of Device Information Models and an Abstract Information Model
according to a specified set of rules
Access Control Attributes: set of parameters of the originator, target resource, and environment against which there
could be rules evaluated to control access
NOTE: An example of Access Control Attributes of originator is a role. Examples of Access Control Attributes of
Environment are time, day and IP address. An example of Access Control Attributes of targeted resource
is creation time.
ETSI
(oneM2M TS-0011 version 2.4.1 Release 2) 8 ETSI TS 118 111 V2.4.1 (2016-09)
Access Control Policy: set of privileges which represents access control rules defining allowed entities for certain
operations within specified contexts that each entity has to comply with to grant access to an object
Access Control Role: security attribute associated to an entity defining the ent
...







Questions, Comments and Discussion
Ask us and Technical Secretary will try to provide an answer. You can facilitate discussion about the standard in here.
Loading comments...