ETSI TR 103 959 V1.1.1 (2024-07)
Cyber Security (CYBER); Critical Security Controls for Effective Cyber Defence; Cloud Sector
Cyber Security (CYBER); Critical Security Controls for Effective Cyber Defence; Cloud Sector
DTR/CYBER-00109
General Information
Standards Content (Sample)
TECHNICAL REPORT
Cyber Security (CYBER);
Critical Security Controls for Effective Cyber Defence;
Cloud Sector
2 ETSI TR 103 959 V1.1.1 (2024-07)
Reference
DTR/CYBER-00109
Keywords
cloud computing, cyber security, cyber-defence,
data centres, information assurance
ETSI
650 Route des Lucioles
F-06921 Sophia Antipolis Cedex - FRANCE
Tel.: +33 4 92 94 42 00 Fax: +33 4 93 65 47 16
Siret N° 348 623 562 00017 - APE 7112B
Association à but non lucratif enregistrée à la
Sous-Préfecture de Grasse (06) N° w061004871
Important notice
The present document can be downloaded from the
ETSI Search & Browse Standards application.
The present document may be made available in electronic versions and/or in print. The content of any electronic and/or
print versions of the present document shall not be modified without the prior written authorization of ETSI. In case of any
existing or perceived difference in contents between such versions and/or in print, the prevailing version of an ETSI
deliverable is the one made publicly available in PDF format on ETSI deliver.
Users should be aware that the present document may be revised or have its status changed,
this information is available in the Milestones listing.
If you find errors in the present document, please send your comments to
the relevant service listed under Committee Support Staff.
If you find a security vulnerability in the present document, please report it through our
Coordinated Vulnerability Disclosure (CVD) program.
Notice of disclaimer & limitation of liability
The information provided in the present deliverable is directed solely to professionals who have the appropriate degree of
experience to understand and interpret its content in accordance with generally accepted engineering or
other professional standard and applicable regulations.
No recommendation as to products and services or vendors is made or should be implied.
No representation or warranty is made that this deliverable is technically accurate or sufficient or conforms to any law
and/or governmental rule and/or regulation and further, no representation or warranty is made of merchantability or fitness
for any particular purpose or against infringement of intellectual property rights.
In no event shall ETSI be held liable for loss of profits or any other incidental or consequential damages.
Any software contained in this deliverable is provided "AS IS" with no warranties, express or implied, including but not
limited to, the warranties of merchantability, fitness for a particular purpose and non-infringement of intellectual property
rights and ETSI shall not be held liable in any event for any damages whatsoever (including, without limitation, damages
for loss of profits, business interruption, loss of information, or any other pecuniary loss) arising out of or related to the use
of or inability to use the software.
Copyright Notification
No part may be reproduced or utilized in any form or by any means, electronic or mechanical, including photocopying and
microfilm except as authorized by written permission of ETSI.
The content of the PDF version shall not be modified without the written authorization of ETSI.
The copyright and the foregoing restriction extend to reproduction in all media.
© ETSI 2024.
All rights reserved.
ETSI
3 ETSI TR 103 959 V1.1.1 (2024-07)
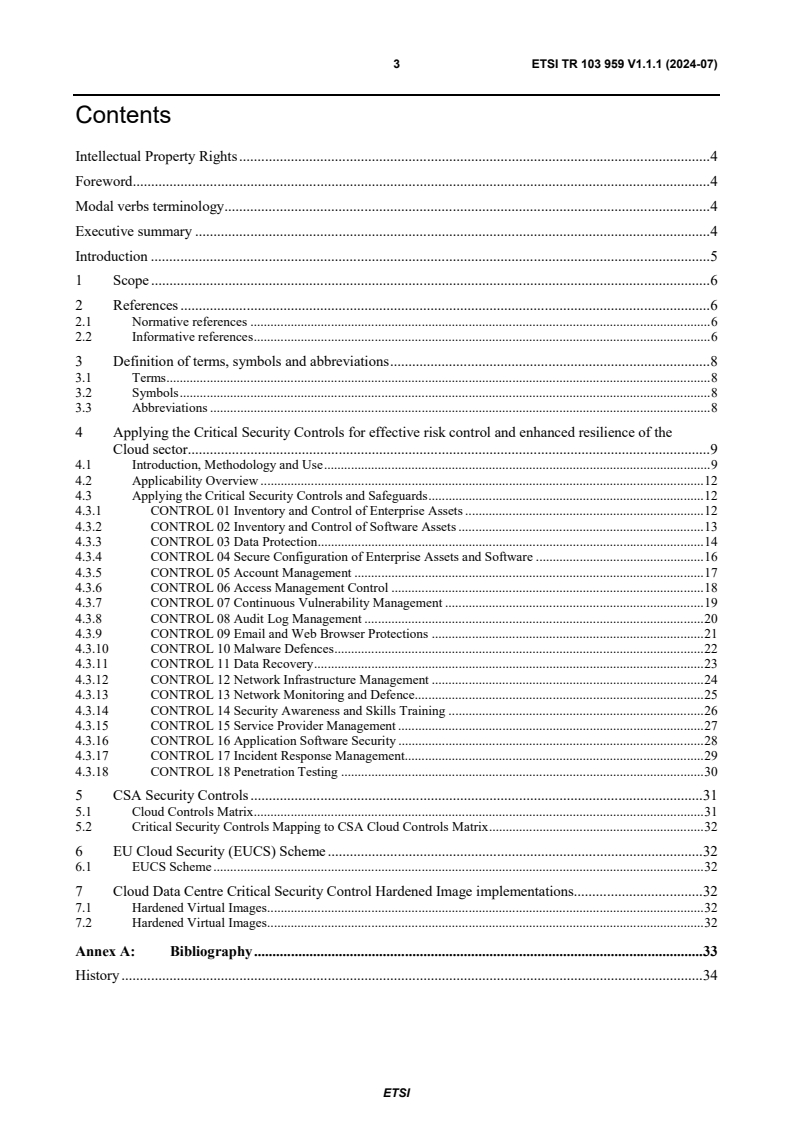
Contents
Intellectual Property Rights . 4
Foreword . 4
Modal verbs terminology . 4
Executive summary . 4
Introduction . 5
1 Scope . 6
2 References . 6
2.1 Normative references . 6
2.2 Informative references . 6
3 Definition of terms, symbols and abbreviations . 8
3.1 Terms . 8
3.2 Symbols . 8
3.3 Abbreviations . 8
4 Applying the Critical Security Controls for effective risk control and enhanced resilience of the
Cloud sector . 9
4.1 Introduction, Methodology and Use . 9
4.2 Applicability Overview . 12
4.3 Applying the Critical Security Controls and Safeguards . 12
4.3.1 CONTROL 01 Inventory and Control of Enterprise Assets . 12
4.3.2 CONTROL 02 Inventory and Control of Software Assets . 13
4.3.3 CONTROL 03 Data Protection . 14
4.3.4 CONTROL 04 Secure Configuration of Enterprise Assets and Software . 16
4.3.5 CONTROL 05 Account Management . 17
4.3.6 CONTROL 06 Access Management Control . 18
4.3.7 CONTROL 07 Continuous Vulnerability Management . 19
4.3.8 CONTROL 08 Audit Log Management . 20
4.3.9 CONTROL 09 Email and Web Browser Protections . 21
4.3.10 CONTROL 10 Malware Defences . 22
4.3.11 CONTROL 11 Data Recovery . 23
4.3.12 CONTROL 12 Network Infrastructure Management . 24
4.3.13 CONTROL 13 Network Monitoring and Defence. 25
4.3.14 CONTROL 14 Security Awareness and Skills Training . 26
4.3.15 CONTROL 15 Service Provider Management . 27
4.3.16 CONTROL 16 Application Software Security . 28
4.3.17 CONTROL 17 Incident Response Management. 29
4.3.18 CONTROL 18 Penetration Testing . 30
5 CSA Security Controls . 31
5.1 Cloud Controls Matrix . 31
5.2 Critical Security Controls Mapping to CSA Cloud Controls Matrix . 32
6 EU Cloud Security (EUCS) Scheme . 32
6.1 EUCS Scheme . 32
7 Cloud Data Centre Critical Security Control Hardened Image implementations. 32
7.1 Hardened Virtual Images . 32
7.2 Hardened Virtual Images . 32
Annex A: Bibliography . 33
History . 34
ETSI
4 ETSI TR 103 959 V1.1.1 (2024-07)
Intellectual Property Rights
Essential patents
IPRs essential or potentially essential to normative deliverables may have been declared to ETSI. The declarations
pertaining to these essential IPRs, if any, are publicly available for ETSI members and non-members, and can be
found in ETSI SR 000 314: "Intellectual Property Rights (IPRs); Essential, or potentially Essential, IPRs notified to
ETSI in respect of ETSI standards", which is available from the ETSI Secretariat. Latest updates are available on the
ETSI Web server (https://ipr.etsi.org/).
Pursuant to the ETSI Directives including the ETSI IPR Policy, no investigation regarding the essentiality of IPRs,
including IPR searches, has been carried out by ETSI. No guarantee can be given as to the existence of other IPRs not
referenced in ETSI SR 000 314 (or the updates on the ETSI Web server) which are, or may be, or may become,
essential to the present document.
Trademarks
The present document may include trademarks and/or tradenames which are asserted and/or registered by their owners.
ETSI claims no ownership of these except for any which are indicated as being the property of ETSI, and conveys no
right to use or reproduce any trademark and/or tradename. Mention of those trademarks in the present document does
not constitute an endorsement by ETSI of products, services or organizations associated with those trademarks.
DECT™, PLUGTESTS™, UMTS™ and the ETSI logo are trademarks of ETSI registered for the benefit of its
Members. 3GPP™ and LTE™ are trademarks of ETSI registered for the benefit of its Members and of the 3GPP
Organizational Partners. oneM2M™ logo is a trademark of ETSI registered for the benefit of its Members and of the ®
oneM2M Partners. GSM and the GSM logo are trademarks registered and owned by the GSM Association.
Foreword
This Technical Report (TR) has been produced by ETSI Technical Committee Cyber Security (CYBER).
Modal verbs terminology
In the present document "should", "should not", "may", "need not", "will", "will not", "can" and "cannot" are to be
interpreted as described in clause 3.2 of the ETSI Drafting Rules (Verbal forms for the expression of provisions).
"must" and "must not" are NOT allowed in ETSI deliverables except when used in direct citation.
Executive summary
Cloud data centres, including cloud edge architectures, have become pervasive worldwide as a critical infrastructure
sector for providing network ICT services and applications. The protection of this infrastructure from cyber security
threats by instituting effective risk control and enhanced resilience has received the global attention of governmental
authorities and industry organizations [i.1] to [i.19]. The present document addresses this protection challenge by
providing guidance on individually applying the most current version of the Critical Security Controls for effective
cyber defence [i.20] to cloud infrastructure. For compliance purposes, the Critical Security Controls have mappings to
almost every known government and industry cyber security framework with extensive implementations for diverse
operating systems and applications [i.22] and [i.23]. Included in the present document is a mapping to Cloud Security
Alliance Security Controls framework together with an enumeration of known Cloud Data Centre OS Hardened Image
implementations.
ETSI
5 ETSI TR 103 959 V1.1.1 (2024-07)
Introduction
The Critical Security Controls are a prioritized set of actions that collectively form a defence-in-depth set of best
practices that mitigate the most common attacks against systems and networks. Under the auspices of the Center for
Internet Security (CIS), the Controls are developed by a community of Information Technology (IT) experts who apply
their first-hand experience as cyber defenders to create these globally accepted security best practices. The experts who
develop the Controls come from a wide range of sectors including, retail, manufacturing, healthcare, education,
government, defence, and others. While the Controls address the general practices that most enterprises should take to
secure their systems, some operational environments may present unique requirements not addressed by the Controls.
The Controls started as a grassroots activity to identify the most common and important real-world cyber-attacks that
affect enterprises every day, translate that knowledge and experience into positive, constructive action for defenders,
and share that information to help enterprises focus their attention on the most fundamental steps they should take to
defend themselves. As the Controls continue to be refined and re-worked through the expert community, the need for
Controls guidance for the cloud sector became clear [i.25], [i.27] and [i.31].
ETSI
6 ETSI TR 103 959 V1.1.1 (2024-07)
1 Scope
The present document applies the latest version of the Critical Security Controls [i.20] for effective risk control and
enhanced resilience of the Cloud Sector and adds mappings to CSA Security Controls and Cloud Data Centre Hardened
Image implementations [i.21].
2 References
2.1 Normative references
Normative references are not applicable in the present document.
2.2 Informative references
References are either specific (identified by date of publication and/or edition number or version number) or
non-specific. For specific references, only the cited version applies. For non-specific references, the latest version of the
referenced document (including any amendments) applies.
NOTE: While any hyperlinks included in this clause were valid at the time of publication ETSI cannot guarantee
their long term validity.
The following referenced documents are not necessary for the application of the present document but they assist the
user with regard to a particular subject area.
[i.1] Directive (EU) 2022/2555 of the European Parliament and of the Council of 14 December 2022 on
measures for a high common level of cybersecurity across the Union, amending Regulation (EU)
No 910/2014 and Directive (EU) 2018/1972, and repealing Directive (EU) 2016/1148 (NIS 2
Directive) (Text with EEA relevance).
[i.2] COM/2020/595 final: "Proposal for a Regulation of the European Parliament and of the Council
on digital operational resilience for the financial sector and amending Regulations (EC)
No 1060/2009, (EU) No 648/2012, (EU) No 600/2014 and (EU) No 909/2014".
[i.3] Directive (EU) 2022/2557 of the European Parliament and of the Council of 14 December 2022 on
the resilience of critical entities and repealing Council Directive 2008/114/EC (Text with EEA
relevance).
[i.4] Regulation (EU) 2019/881 of the European Parliament and of the Council of 17 April 2019 on
ENISA (the European Union Agency for Cybersecurity) and on information and communications
technology cybersecurity certification and repealing Regulation (EU) No 526/2013 (Cybersecurity
Act) (Text with EEA relevance).
[i.5] Council Directive 2008/114/EC of 8 December 2008 on the identification and designation of
European critical infrastructures and the assessment of the need to improve their protection (Text
with EEA relevance).
[i.6] Regulation (EU) 2022/2065 of the European Parliament and of the Council of 19 October 2022 on
a Single Market For Digital Services and amending Directive 2000/31/EC (Digital Services Act)
(Text with EEA relevance).
[i.7] Regulation (EU) 2016/679 of the European Parliament and of the Council of 27 April 2016 on the
protection of natural persons with regard to the processing of personal data and on the free
movement of such data, and repealing Directive 95/46/EC (General Data Protection Regulation)
(Text with EEA relevance).
[i.8] Regulation (EU) 2018/1807 of the European Parliament and of the Council of 14 November 2018
on a framework for the free flow of non-personal data in the European Union.
ETSI
7 ETSI TR 103 959 V1.1.1 (2024-07)
[i.9] Directive (EU) 2016/1148 of the European Parliament and of the Council of 6 July 2016
concerning measures for a high common level of security of network and information systems
across the EU (NIS Directive).
[i.10] COM/2022/68 final: "Proposal for a regulation of the European Parliament and of the Council on
harmonised rules on fair access to and use of data (Data Act)".
[i.11] COM/2012/0529 final: "Communication from the Commission to the European Parliament, the
Council, the European Economic and Social Committee and the Committee of the Regions
Unleashing the Potential of Cloud Computing in Europe".
[i.12] COM/2015/0192 final: Communication from the Commission to the European Parliament, the
Council, the European Economic and Social Committee and the Committee of the Regions A
digital single market strategy for Europe.
[i.13] COM/2016/0176 final: "Communication from the Commission to the European Parliament, the
Council, the European Economic and Social Committee and the Committee of the Regions ICT
Standardisation priorities for the digital single market".
[i.14] COM/2016/0178 final: "Communication from the Commission to the European Parliament, the
Council, the European Economic and Social Committee and the Committee of the Regions
European Cloud Initiative - Building a competitive data and knowledge economy in Europe".
[i.15] COM/2021/118 final: "Communication from the Commission to the European Parliament, the
Council, the European Economic and Social Committee and the Committee of the Regions 2030
Digital Compass: the European way for the Digital Decade".
[i.16] National Cyber Security Centre: "Cloud security guidance".
[i.17] CISA Cybersecurity and Infrastructure Security Agency (Version 2.0): "Cloud Security Technical
Reference Architecture".
[i.18] National Security Agency: "Mitigating Cloud Vulnerabilities".
[i.19] Cloud Security Alliance: "CSA Research Publications".
[i.20] ETSI TR 103 305-1: "Cyber Security (CYBER); Critical Security Controls for Effective
Cyber Defence; Part 1: The Critical Security Controls".
[i.21] ETSI TR 103 305-4: "Cyber Security (CYBER); Critical Security Controls for Effective
Cyber Defence; Part 4: Facilitation Mechanisms".
[i.22] ETSI TR 103 305-5: "Cyber Security (CYBER); Critical Security Controls for Effective Cyber
Defence; Part 5: Privacy and personal data protection enhancement".
[i.23] ETSI TR 103 866: " Cyber Security (CYBER); Implementation of the Revised Network and
Information Security (NIS2) Directive applying Critical Security Controls".
[i.24] Cloud Security Alliance: "Cloud Controls Matrix (CCM)".
[i.25] Center for Internet Security: "Controls Cloud Companion Guide, V8".
[i.26] ENISA Cloud Security.
[i.27] ENISA: "EUCS - Cloud Services Scheme".
[i.28] EU CLOUD COC: "EU Cloud Code of Conduct".
[i.29] Center for Internet Security: "CIS Hardened Images List".
[i.30] Center for Internet Security: "CIS Controls Mapping to Cloud Security Alliance Cloud Control
Matrix".
[i.31] Center for Internet Security: "Shared Responsibility for Cloud Security: What You Need to
Know".
ETSI
8 ETSI TR 103 959 V1.1.1 (2024-07)
3 Definition of terms, symbols and abbreviations
3.1 Terms
For the purposes of the present document, the following terms apply:
cloud sector: model that enables access to a shared pool of computing resources on-demand, and includes data centre,
edge, and associated user hardware and software infrastructure
tokenization: process by which a piece of sensitive data, such as a credit card number, is replaced by a surrogate value
known as a token
3.2 Symbols
Void.
3.3 Abbreviations
For the purposes of the present document, the following abbreviations apply:
AAA Authentication, Authorization, and Auditing
API Application Program Interface
CaaS Containers as a Service
CASB Cloud Access Security Broker
CCM Cloud Controls Matrix
CIS Center for Internet Security
CISA Cybersecurity and Infrastructure Security Agency
CSA Cloud Security Alliance
CSC Critical Security Control
CSP Cloud Service Provider
DevOp Development and Operation
DevSecOp Development, Security and Operation
DHCP Dynamic Host Configuration Protocol
DMARC Domain-based Message Authentication Reporting, and Conformance
DMZ DeMilitarised Zone
DNS Domain Name System
EUCS European Union Cloud Security
FaaS Function as a Service
HSM Hardware Security Model
IaaS Infrastructure as a Service
IaC Infrastructure as Code
ICT Information and Communications Technology
IDS Intrusion Detection Systems
IG Implementation Group
IP Internet Protocol
IPS Intrusion Prevention System
IT Information Technology
JSON JavaScript Object Notation
MFA Multifactor Authentication
OS Operating System
OSCAL Open Security Controls Assessment Language
OT Operational Technology
PaaS Platform as a Service
RBAC Role-Based Access Control
SaaS Software as a Service
SLA Service-Level Agreements
SME Small and Medium Enterprise
STAR Security, Trust Assurance and Risk
ETSI
9 ETSI TR 103 959 V1.1.1 (2024-07)
TLS Transport Layer Security
URL Uniform Resource Locator
VPN Virtual Private Network
YAML YAML Ain't Markup Language
4 Applying the Critical Security Controls for effective
risk control and enhanced resilience of the Cloud
sector
4.1 Introduction, Methodology and Use
While many of the core security concerns of enterprise IT systems are shared within cloud environments, the main
challenge in applying best practices is tied to the fact that these systems typically operate software and hardware under
different assumed security responsibilities. Ensuring and understanding that the Service-Level Agreements (SLAs) and
legal contracts with the Cloud Service Provider (CSP) highlight liability, service levels, breach disclosure, and incident
response timeframes is an important piece of cloud security. The shared security responsibility, as well as the specific
cloud services and deployment models utilized, changes who handles the security requirements and with whom the
assumed security risk resides. CSPs are constantly adding new functional services along with configuration and security
tools to better manage them at a very rapid pace. As new tools become available, the cloud consumer should consider a
hybrid approach using third-party tools along with CSP native security tools that best fit an enterprise's security and
management needs. Enterprise management processes should ensure there is overlap rather than gaps in coverage
between native and third-party tools.
Cloud environments have service models that the applications or services can be classified under. These models have
evolved over time and continue to emerge:
• IaaS (Infrastructure as a Service) is a cloud environment providing computing resources such as virtual
servers, storage, and networking hardware. The consumer utilizes their own software such as operating
systems, middleware, and applications. The underlying cloud infrastructure is managed by the CSP.
• PaaS (Platform as a Service) is a cloud computing environment for development and management of a
consumer's applications. It includes the infrastructure hardware: virtual servers, storage, and networking while
tying in the middleware and development tools to allow the consumer to deploy their applications. It is
designed to support the complete application lifecycle while leaving the management of the underlying
infrastructure to the CSP. In practice, there can be some IaaS/PaaS overlap (or, indeed, PaaS/SaaS).
• SaaS (Software as a Service) is a cloud computing software solution that provides the consumer with access
to a complete software product. The software application resides on a cloud environment and is accessed by
the consumer through the web or an application program interface (API). The consumer can utilize the
application to store and analyse data without having to worry about managing the infrastructure, service, or
software, as that falls to the CSP.
• FaaS (Function as a Service) is a cloud computing service that allows the consumer to develop, manage, and
run their application functionalities without having to manage and maintain any of the infrastructure that is
required. The consumer can execute code in response to events that happen within the CSP or the application
without having to build out or maintain a complex underlying infrastructure.
To complicate things even more, a cloud environment has multiple deployment models:
• Private cloud (on-prem) consists of all the computing resources being hosted and used exclusively in private
tenancy by one consumer (enterprise) within its own offices and data centres. The consumer is responsible for
the operational costs, hardware, software, and the resources required to build and maintain the infrastructure.
This is best used for critical business operations that want to control all access, including physical access, to
the cloud system.
ETSI
10 ETSI TR 103 959 V1.1.1 (2024-07)
• Private cloud (third-party hosted) is a private tenancy cloud system that is hosted by an external third-party
provider. The third-party provides an exclusive use cloud environment for the consumer to deploy applications
and store data on. The third-party provides the hardware, software, servers, supporting infrastructure and
sometimes staff, which offers the customer a reduced, up front capital investment and access to additional
resources as needed. This model can be useful for enterprises that have elastic computing needs; have specific
regulatory requirements that can be met at scale by a third-party much cheaper than on-prem; or for enterprises
that do not wish to make a large capital investment in IT infrastructure and would rather pay as they go.
• Community cloud (shared) is a deployment solution where the computing resources and infrastructure are
shared between several enterprises or community of consumers. The resources can be managed internally or
by a third-party and they can be hosted on-prem or externally. The enterprises share the cost and often have
similar cloud security requirements and business objectives.
• Public cloud is an infrastructure and computing service hosted by a third-party company defined as a CSP and
exists on the CSP's premises. It is available over the internet and the services can be delivered through a self-
service portal. Public cloud is provisioned for open use by the general public and the consumer is provided on-
demand access and scalability without the higher overhead cost of maintaining a private cloud environment,
but gives up private tenancy. The CSP is responsible for the management and maintenance of the system while
the consumer pays only for resources they use. This type of cloud system depends on a "shared security
responsibility model".
• Hybrid cloud is an environment that uses a combination of the two or more cloud deployment models, private
cloud (on-prem), private cloud (third-party hosted), and public cloud with an orchestration service between the
unique deployment models. A hybrid cloud system can provide more flexibility than exclusively utilizing a
public, private, or community cloud system.
Shared Responsibility Model
In the public cloud, there's a shared responsibility between the Cloud Service Provider (CSP) and the user. Security for
things like data classification, network controls, and physical security need clear owners. The division of these
responsibilities is known as the shared responsibility model for cloud security. Figure 4.1-1 portrays how the
responsibilities are shared within different cloud environments.
Figure 4.1-1
Responsibilities under the model will vary depending on the cloud environment within which the user is operating.
Irrespective of the cloud service used (IaaS, PaaS, SaaS, or FaaS), protection of the user organization data is that of the
organization. Additional guidance for implementing a shared responsibility model is available [i.30].
Methodology
ETSI
11 ETSI TR 103 959 V1.1.1 (2024-07)
A consistent approach is needed for analysing the Controls in the context for cloud. For each of the Controls, the
following information is provided:
• Cloud Applicability - The applicability field assesses the degree to which a Control functions within the cloud
space and which service model should be considered.
• Cloud Service and Deployment Considerations - Service and deployment model considerations further
define who is responsible for the Controls within the service model it is applicable to and what the consumer
of the CSP is responsible for.
• Cloud Additional - This is a general area for any additional guidance that also needs to be noted. For instance,
relevant tools, products, or threat information that could be of use can be found here.
Document Use
The present document provides guidance on how to apply the security best practices found in the latest Critical Security
Controls. ETSI TR 103 305-1 [i.20] to any cloud environment from the consumer/customer perspective. For each
top-level Control, there is a brief discussion on how to interpret and apply it in such environments, along with any
unique considerations or differences from common IT environments.
The applicability of specific Controls and Safeguards is addressed, and additional steps needed in any cloud
environment are explained, based on the individual service models. Throughout the present document, the unique
mission/business requirements found in cloud environments are taken into consideration, as well as the unique risks
(vulnerabilities, threats, consequences, and security responsibilities), which in turn drive the priority of the security
requirements (e.g. availability, integrity and confidentiality of process data).
This Technical Report provides guidance to tailor the Controls in the context of a specific IT/Operational Technology
(OT) cloud enterprise as an essential starting point for a security improvement assessment and roadmap. OT is hardware
and software that detects or causes a change through the direct monitoring and/or control of physical devices, processes,
and events in the enterprise. The present document is also aimed at guiding enterprises involved in the agile software
development process via utilization of cloud-based services. DevSecOps, which is short for development, security, and
operations, automates the integration of security at every phase of the software and its underlying infrastructure
development lifecycle, from initial design through integration, testing, deployment, and software delivery. Control 16
will cover these aspects.
As part of the latest Critical Security Controls [i.20], the Implementation Groups (IGs) are a guideline to help
enterprises determine a starting point for implementation of the Controls. Enterprises will, at times, find the need to
implement Safeguards in a higher IG. When integrating new technology into an environment, such as cloud, an
enterprise should fully consider, and assess the security risks and impacts to assets and data. That understanding should
drive the selection and implementation of appropriate Safeguards regardless of IG. Small and Medium size Entities
(SME) are included in IG1.
Figure 4.1-2
ETSI
12 ETSI TR 103 959 V1.1.1 (2024-07)
4.2 Applicability Overview
Table 4.2-1
Applicability of Service Model
Control Safeguard Title IaaS PaaS SaaS FaaS
1 Inventory and Control of Enterprise Assets
2 Inventory and Control of Software Assets
3 Data Protection
4 Secure Configuration of Enterprise Assets and Software
5 Account Management
6 Access Control Management
7 Continuous Vulnerability Management
8 Audit Log Management
9 Email and Web Browser Protections
10 Malware Defences
11 Data Recovery
12 Network Infrastructure Management
13 Network Monitoring and Defence
14 Security Awareness and Skills Training
15 Service Provider Management
16 Application Software Security
17 Incident Response Management
18 Penetration Testing
Applicability Overview for each Service Model:
More than 60 % of Control Safeguards Apply
Between 60 % and 0% of the Control Safeguards Apply
0 %
4.3 Applying the Critical Security Controls and Safeguards
4.3.1 CONTROL 01 Inventory and Control of Enterprise Assets
Cloud Applicability. The first Control is considered the most important because it is necessary to first identify the
systems and devices, including virtual implementations, that need to be secured. Control 1 is about taking inventory.
Understanding and solving the asset inventory and device visibility problem is critical in managing a business security
program. This is challenging in cloud environments due to the shared security responsibility and the cloud service
model utilized.
Table 4.3.1-1
Implementation Applicability of Service
Control 1: Inventory and Control of Enterprise Assets
Groups Model
Asset Security Safeguard Title IG1 IG2 IG3
Safeguard IaaS PaaS SaaS FaaS
Type Function (See [i.20] for description)
Establish and Maintain Detailed
1.1 Devices Identity ● ● ● ● ●
Enterprise Asset Inventory
1.2 Devices Respond Address Unauthorized Assets ● ● ● ● ●
1.3 Devices Detect Utilize an Active Discovery Tool ● ● ● ●
Use Dynamic Host Configuration
1.4 Devices Identify Protocol (DHCP) Logging to Update ● ● ● ●
Enterprise Asset Inventory
1.5 Devices Detect Use a Passive Asset Discovery Tool ● ● ●
When considering deployment models, this Control and Safeguards are applicable for Private (on-prem). For Private
(third-party hosted), Public, and Hybrid deployment models, defer to the service/deployment model(s) the enterprise or
its community are using. See clause 4.1.
ETSI
FaaS
SaaS
PaaS
IaaS
IG3
IG2
IG1
13 ETSI TR 103 959 V1.1.1 (2024-07)
Cloud Service and Deployment Considerations
• On-prem - The local administrator (cloud consumer) is responsible for the security of everything (physical
and virtual servers, room, network, as well as storage, hypervisor, operating systems, etc.).
• IaaS - The administrator (cloud consumer) deploys, operates, and maintains the virtual networks and virtual
machines within this service model but does not manage the underlying cloud infrastructure (physical servers,
physical network, physical storage, hypervisor, etc.) as that is the responsibility of the CSP.
• PaaS - The administrator (cloud consumer) manages the development, testing, and deployment of their
applications. They have full control over the applications and in some cases the host environment settings and
operating systems. The CSP is responsible for the physical servers, physical network, storage, hypervisor, and
operating systems. The shared responsibility model may apply per clause 4.1. DHCP logging, port level access
control might not be applicable.
• SaaS - This is not applicable for the cloud consumer as SaaS and FaaS are under software assets. The CSP is
responsible for everything but the data.
• FaaS - This is not applicable for the cloud consumer as SaaS and FaaS are under software assets. The CSP is
responsible for everything but the data.
Cloud Additional Considerations
• In a cloud environment, assets in on-prem, IaaS, or PaaS service models are virtual and can be in the form of
virtual machines, virtual networks, virtual switches, etc. with limited exceptions such as dedicated Hardware
Security Models (HSMs).
• Due to the nature of virtual systems and the ease to bring online a new virtual asset, it is imperative to maintain
a comprehensive list of all the cloud hardware and virtual assets managed.
• It is always up to the consumer to request documentation outlining how the CSP is securing the infrastructure
and technology that falls under their responsibility.
• When collecting asset inventory, include the criticality of the asset, the operating system and version, when the
asset was discovered, and the asset tag if applicable.
• If containers are considered as FaaS, then the CSP is often not responsible for maintaining security of the
containers or the microservices that run within. Under this circumstance, containers should be treated under
Control 2, below.
4.3.2 CONTROL 02 Inventory and Control of Software Assets
Cloud Applicability. The second Control offers the guidance needed to identify, track, and account for all software
utilized in an environment. This is challenging in cloud environments due to the shared security responsibility and the
cloud service model utilized.
Table 4.3.2-1
Implementation Applicability of
Control 2: Inventory and Control of Software Assets
Groups Service Model
Security Safeguard Title
Safeguard Asset Type
Function (See [i.20] for description)
Establish and Maintain a Software
2.1 Applications Identify ● ● ● ● ● ● ●
Inventory
Ensure Authorized Software is
2.2 Applications Identify ● ● ● ● ● ●
Currently Supported
2.3 Applications Respond Address Unauthorized Software ● ● ● ● ● ● ●
Utilize Automated Software Inventory
2.4 Applications Detect ● ● ● ● ●
Tools
2.5 Applications Protect Allowlist Authorized Software ● ● ● ●
2.6 Applications Protect Allowlist Authorized Libraries ● ● ● ●
2.7 Applications Protect Allowlist Authorized Scripts ● ● ● ●
ETSI
14 ETSI TR 103 959 V1.1.1 (2024-07)
When considering deployment models, these CSC Safeguards are applicable for Private (on-prem). For Private
(third-party hosted), Public, and Hybrid deployment models, implement the service/deployment model(s) the enterprise
or community are using. See also, Shared Responsibility Model, clause 4.1.
Cloud Service and Deployment Considerations
• On-prem - The local administrator is responsible for keeping the inventory of all software utilized regardless
of the service model.
• IaaS - The administrator (cloud consumer) deploys, operates, and maintains the software utilized within this
service model but does not manage the underlying cloud software such as the hypervisor, host operating
system, or applications that provide specific services that are the responsibility of the CSP.
• PaaS - The administrator (cloud consumer) manages the development, testing, and deployment of their
software and applications. They have full control over the applications and in some cases the operating
systems so they are responsible for all software running at this level per the Shared Responsibility Model,
clause 4.1 . The CSP is responsible for the hypervisor and operating systems and other applications that
provide this service. Application whitelisting, whitelisting of libraries, whitelisting of scripts, and segregating
high-risk applications will not be applicable to all PaaS service models.
• SaaS - The administrator (cloud consumer) is responsible for registering the software on the inventory list as
approved. They are also responsible for checking that the vendor still supports and issues updates for the
software, and for keeping a record of this in the software inventory. Tracking software inventory could be
manual.
• FaaS - The administrator (cloud consumer) is responsible for maintaining an inventory of authorized software.
Tracking software inventory could be manual.
Cloud Additional Considerations
• In a cloud environment, running on-prem, IaaS, PaaS, SaaS, or FaaS, the software being used and maintained
has to be inventoried, patched, and monitored when applicable.
• It is imperative to maintain a comprehensive list of these cloud software assets to identify and mitigate any
vulnerabilities and data associated with the software managed.
• It is always up to the consumer to request documentation from the CSP outlining their responsibilities on how
the CSP is securing the infrastructure and technology.
• Also keep in mind that as part of the software inventory, the consumer should include the API endpoints. ®
NOTE: For PaaS using managed Kubernetes services - which is a logical abstraction for a deployed group of
pods in a cluster which all perform the same function - the cloud consumer is responsible for
patches/updates.
• Discovery and inventory capabilities should extend to software running inside containers (in the case of
Containers-as-a-Service). CaaS is considered a subset of IaaS and is found between IaaS and PaaS.
4.3.3 CONTROL 03 Data Protection
Cloud Applicability. The focus of this Control is on data protection and ensuring the privacy and integrity of sensitive
information. The cloud environment is not an exception to private data. If cloud consumers have realized anything
while migrating information to the cloud, it is that protecting data can be more complicated. It is a growing concern for
CSPs and consumers because any data leakage can go undetected for long periods of time.
ETSI
FaaS
SaaS
PaaS
IaaS
IG3
IG2
IG1
15 ETSI TR 103 959 V1.1.1 (2024-07)
Table 4.3.3-1
Implementation Applicability of
Control 3: Data Protection
Groups Service Model
Asset Security Safeguard Title
Safeguard
Type Function (See [i.20] for description)
Establish and Maintain a Data
3.1 Data Identify ● ● ● ● ● ● ●
Management Process
3.2 Data Identify Establish and Maintain a Data Inventory ● ● ● ● ● ● ●
3.3 Data Protect Configure Data Access Control Lists ● ● ● ● ● ● ●
3.4 Data Protect Enforce Data Retention ● ● ● ● ● ● ●
3.5 Data Protect Securely Dispose of Data ● ● ● ● ● ● ●
3.6 Devices Protect Encrypt Data on End-User Devices ● ● ●
Establish and Maintain a Data
3.7 Data Identify ● ● ● ● ● ●
Classification Scheme
3.8 Data Identify Document Data Flows ● ● ●
...







Questions, Comments and Discussion
Ask us and Technical Secretary will try to provide an answer. You can facilitate discussion about the standard in here.
Loading comments...