ISO/IEC 18370-2:2016
(Main)Information technology — Security techniques — Blind digital signatures — Part 2: Discrete logarithm based mechanisms
Information technology — Security techniques — Blind digital signatures — Part 2: Discrete logarithm based mechanisms
ISO/IEC 18370-2:2016 specifies blind digital signature mechanisms, together with mechanisms for three variants of blind digital signatures. The variants are blind digital signature mechanisms with partial disclosure, blind digital signature mechanisms with selective disclosure and traceable blind digital signature mechanisms. The security of all the mechanisms in ISO/IEC 18370-2:2016 is based on the discrete logarithm problem. For each mechanism, ISO/IEC 18370-2:2016 specifies the following: - the process for generating the keys of the entities involved in these mechanisms; - the process for producing blind signatures; - the process for verifying signatures. ISO/IEC 18370-2:2016 specifies another process specific to blind signature mechanisms with selective disclosure, namely, the following: - the presentation process. Furthermore, ISO/IEC 18370-2:2016 specifies other processes specific to traceable blind signature mechanisms, namely, the following: a) the process for tracing requestors; b) the process for tracing signatures; c) the requestor tracing evidence evaluation process (optional); d) the signature tracing evidence evaluation process (optional).
Technologie de l'information — Techniques de sécurité — Signatures numériques en aveugle — Partie 2: Mécanismes fondés sur le logarithme discret
General Information
- Status
- Published
- Publication Date
- 30-Jun-2016
- Drafting Committee
- ISO/IEC JTC 1/SC 27/WG 2 - Cryptography and security mechanisms
- Current Stage
- 9093 - International Standard confirmed
- Start Date
- 19-May-2022
- Completion Date
- 12-Feb-2026
Overview
ISO/IEC 18370-2:2016 - Information technology - Security techniques - Blind digital signatures - Part 2: Discrete logarithm based mechanisms - specifies concrete blind digital signature mechanisms whose security is based on the discrete logarithm problem. Published by ISO/IEC JTC 1/SC 27, this part defines multiple mechanisms and three important variants: partial disclosure, selective disclosure, and traceable blind signatures. For each mechanism the standard specifies the procedures for key generation, blind signature production, and signature verification, plus additional processes where applicable (presentation, tracing and evidence evaluation).
Key topics and requirements
- Mechanisms covered
- Blind signatures (basic blind signing)
- Blind signatures with partial disclosure (signer may embed agreed data)
- Blind signatures with selective disclosure (controlled message choices and a presentation process)
- Traceable blind signatures (requestor and signature tracing, optional evidence evaluation)
- Core processes specified
- Key generation for all entities involved
- Blind signature process (how a requestor obtains a signature without revealing the message)
- Verification process (how verifiers check a signature)
- Presentation process for selective disclosure
- Tracing processes and evidence evaluation for traceable variants
- Security basis
- All mechanisms rely on the discrete logarithm (DL) family of hardness assumptions (including considerations of DDH) and require secure collision-resistant hash functions.
- Implementation guidance
- Annexes provide domain parameter descriptions, conversion functions, special hash functions, numeric examples, and security/parameter guidance (key sizes, hash choices, RNG considerations).
- Scope exclusions
- Key management, certification and random-bit generation techniques are outside the scope (references to ISO/IEC standards for these topics are provided).
Applications and who should use it
ISO/IEC 18370-2 is intended for:
- Cryptographers and protocol designers building privacy-preserving systems
- Developers of anonymous credentials, e-cash, e-voting, and privacy-aware authentication solutions
- Security architects selecting blind signature schemes based on discrete logarithm groups (finite field or elliptic curve)
- Standards bodies and auditors assessing compliance of blind-signature components
Benefits include standardized, interoperable definitions of blind signing workflows and traceability options while preserving requestor privacy under defined cryptographic assumptions.
Related standards
- ISO/IEC 18370-1 - General principles and requirements for blind digital signatures (companion part)
- ISO/IEC 10118, ISO/IEC 18031 - Hash functions and randomness guidance referenced by this part
- Key management and certification references: ISO/IEC 9594-8, ISO/IEC 11770-3, ISO/IEC 15945
Keywords: ISO/IEC 18370-2:2016, blind digital signatures, discrete logarithm, selective disclosure, traceable blind signatures, partial disclosure, key generation, signature verification.
Get Certified
Connect with accredited certification bodies for this standard

BSI Group
BSI (British Standards Institution) is the business standards company that helps organizations make excellence a habit.

Bureau Veritas
Bureau Veritas is a world leader in laboratory testing, inspection and certification services.

DNV
DNV is an independent assurance and risk management provider.
Sponsored listings
Frequently Asked Questions
ISO/IEC 18370-2:2016 is a standard published by the International Organization for Standardization (ISO). Its full title is "Information technology — Security techniques — Blind digital signatures — Part 2: Discrete logarithm based mechanisms". This standard covers: ISO/IEC 18370-2:2016 specifies blind digital signature mechanisms, together with mechanisms for three variants of blind digital signatures. The variants are blind digital signature mechanisms with partial disclosure, blind digital signature mechanisms with selective disclosure and traceable blind digital signature mechanisms. The security of all the mechanisms in ISO/IEC 18370-2:2016 is based on the discrete logarithm problem. For each mechanism, ISO/IEC 18370-2:2016 specifies the following: - the process for generating the keys of the entities involved in these mechanisms; - the process for producing blind signatures; - the process for verifying signatures. ISO/IEC 18370-2:2016 specifies another process specific to blind signature mechanisms with selective disclosure, namely, the following: - the presentation process. Furthermore, ISO/IEC 18370-2:2016 specifies other processes specific to traceable blind signature mechanisms, namely, the following: a) the process for tracing requestors; b) the process for tracing signatures; c) the requestor tracing evidence evaluation process (optional); d) the signature tracing evidence evaluation process (optional).
ISO/IEC 18370-2:2016 specifies blind digital signature mechanisms, together with mechanisms for three variants of blind digital signatures. The variants are blind digital signature mechanisms with partial disclosure, blind digital signature mechanisms with selective disclosure and traceable blind digital signature mechanisms. The security of all the mechanisms in ISO/IEC 18370-2:2016 is based on the discrete logarithm problem. For each mechanism, ISO/IEC 18370-2:2016 specifies the following: - the process for generating the keys of the entities involved in these mechanisms; - the process for producing blind signatures; - the process for verifying signatures. ISO/IEC 18370-2:2016 specifies another process specific to blind signature mechanisms with selective disclosure, namely, the following: - the presentation process. Furthermore, ISO/IEC 18370-2:2016 specifies other processes specific to traceable blind signature mechanisms, namely, the following: a) the process for tracing requestors; b) the process for tracing signatures; c) the requestor tracing evidence evaluation process (optional); d) the signature tracing evidence evaluation process (optional).
ISO/IEC 18370-2:2016 is classified under the following ICS (International Classification for Standards) categories: 35.030 - IT Security; 35.040 - Information coding. The ICS classification helps identify the subject area and facilitates finding related standards.
ISO/IEC 18370-2:2016 is available in PDF format for immediate download after purchase. The document can be added to your cart and obtained through the secure checkout process. Digital delivery ensures instant access to the complete standard document.
Standards Content (Sample)
INTERNATIONAL ISO/IEC
STANDARD 18370-2
First edition
2016-07-01
Information technology — Security
techniques — Blind digital
signatures —
Part 2:
Discrete logarithm based mechanisms
Technologie de l’information — Techniques de sécurité — Signatures
numériques en aveugle —
Partie 2: Mécanismes fondés sur le logarithme discret
Reference number
©
ISO/IEC 2016
© ISO/IEC 2016, Published in Switzerland
All rights reserved. Unless otherwise specified, no part of this publication may be reproduced or utilized otherwise in any form
or by any means, electronic or mechanical, including photocopying, or posting on the internet or an intranet, without prior
written permission. Permission can be requested from either ISO at the address below or ISO’s member body in the country of
the requester.
ISO copyright office
Ch. de Blandonnet 8 • CP 401
CH-1214 Vernier, Geneva, Switzerland
Tel. +41 22 749 01 11
Fax +41 22 749 09 47
copyright@iso.org
www.iso.org
ii © ISO/IEC 2016 – All rights reserved
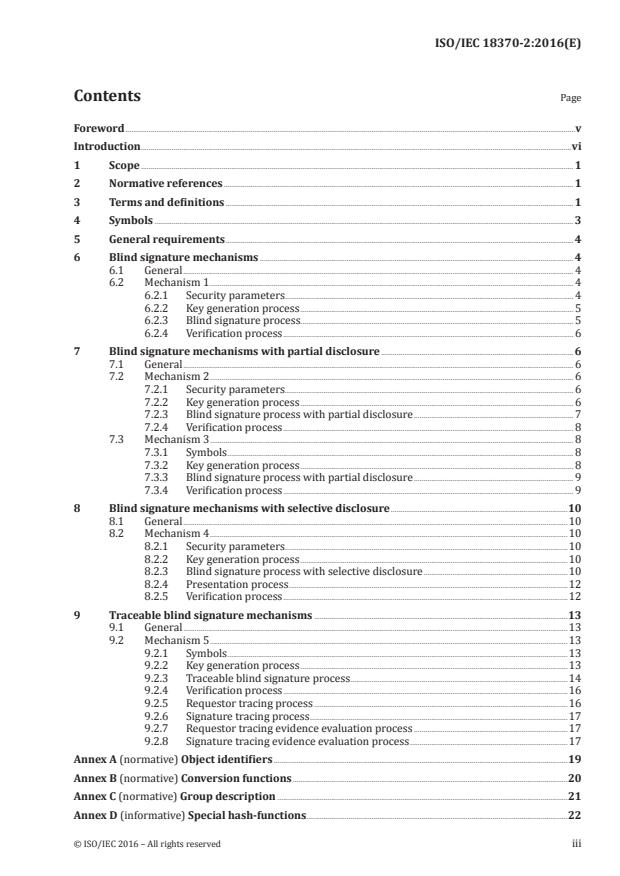
Contents Page
Foreword .v
Introduction .vi
1 Scope . 1
2 Normative references . 1
3 Terms and definitions . 1
4 Symbols . 3
5 General requirements . 4
6 Blind signature mechanisms . 4
6.1 General . 4
6.2 Mechanism 1 . 4
6.2.1 Security parameters . 4
6.2.2 Key generation process . 5
6.2.3 Blind signature process. 5
6.2.4 Verification process . 6
7 Blind signature mechanisms with partial disclosure . 6
7.1 General . 6
7.2 Mechanism 2 . 6
7.2.1 Security parameters . 6
7.2.2 Key generation process . 6
7.2.3 Blind signature process with partial disclosure . 7
7.2.4 Verification process . 8
7.3 Mechanism 3 . 8
7.3.1 Symbols . 8
7.3.2 Key generation process . 8
7.3.3 Blind signature process with partial disclosure . 9
7.3.4 Verification process . 9
8 Blind signature mechanisms with selective disclosure .10
8.1 General .10
8.2 Mechanism 4 .10
8.2.1 Security parameters .10
8.2.2 Key generation process .10
8.2.3 Blind signature process with selective disclosure .10
8.2.4 Presentation process .12
8.2.5 Verification process .12
9 Traceable blind signature mechanisms .13
9.1 General .13
9.2 Mechanism 5 .13
9.2.1 Symbols .13
9.2.2 Key generation process .13
9.2.3 Traceable blind signature process .14
9.2.4 Verification process .16
9.2.5 Requestor tracing process .16
9.2.6 Signature tracing process .17
9.2.7 Requestor tracing evidence evaluation process .17
9.2.8 Signature tracing evidence evaluation process .17
Annex A (normative) Object identifiers .19
Annex B (normative) Conversion functions .20
Annex C (normative) Group description .21
Annex D (informative) Special hash-functions.22
© ISO/IEC 2016 – All rights reserved iii
Annex E (informative) Security considerations and comparison of blind signature mechanisms .24
Annex F (informative) Numerical examples .26
Bibliography .78
iv © ISO/IEC 2016 – All rights reserved
Foreword
ISO (the International Organization for Standardization) and IEC (the International Electrotechnical
Commission) form the specialized system for worldwide standardization. National bodies that are
members of ISO or IEC participate in the development of International Standards through technical
committees established by the respective organization to deal with particular fields of technical
activity. ISO and IEC technical committees collaborate in fields of mutual interest. Other international
organizations, governmental and non-governmental, in liaison with ISO and IEC, also take part in the
work. In the field of information technology, ISO and IEC have established a joint technical committee,
ISO/IEC JTC 1.
The procedures used to develop this document and those intended for its further maintenance are
described in the ISO/IEC Directives, Part 1. In particular the different approval criteria needed for
the different types of document should be noted. This document was drafted in accordance with the
editorial rules of the ISO/IEC Directives, Part 2 (see www.iso.org/directives).
Attention is drawn to the possibility that some of the elements of this document may be the subject
of patent rights. ISO and IEC shall not be held responsible for identifying any or all such patent
rights. Details of any patent rights identified during the development of the document will be in the
Introduction and/or on the ISO list of patent declarations received (see www.iso.org/patents).
Any trade name used in this document is information given for the convenience of users and does not
constitute an endorsement.
For an explanation on the meaning of ISO specific terms and expressions related to conformity
assessment, as well as information about ISO’s adherence to the WTO principles in the Technical
Barriers to Trade (TBT) see the following URL: Foreword - Supplementary information
The committee responsible for this document is ISO/IEC JTC 1, Information technology, Subcommittee
SC 27, IT Security techniques.
ISO/IEC 18370 consists of the following parts, under the general title Information technology — Security
techniques — Blind digital signatures:
— Part 1: General
— Part 2: Discrete logarithm based mechanisms
Further parts may follow.
© ISO/IEC 2016 – All rights reserved v
Introduction
Blind digital signature mechanisms are a special type of digital signature mechanism, as specified in
ISO/IEC 9796 (all parts) and ISO/IEC 14888, which allow a user (a requestor) to obtain a signature from
a signer of the user’s choice, without giving the signer any information about the message that is signed
or the resulting signature.
In some mechanisms, the signer does not completely lose control over the signed message since the
signer can include explicit information in the resulting signature under an agreement with the
requestor. These types of blind signatures are called blind signatures with partial disclosure.
Other mechanisms allow a requestor to receive a blind signature on a message not known to the signer
but the choice of the message is restricted and needs to conform to certain rules. Such mechanisms are
called blind signature mechanisms with selective disclosure.
Depending on the mechanism, it may be possible for an authorized entity to trace a signature to the
requestor who requested it. Such an entity can either identify a signature that resulted from a given
signature request (signature tracing), or link a signature to the receiver who requested it (requestor
tracing). Blind signature mechanisms with tracing features are called traceable blind signature
mechanisms.
ISO/IEC 18370 specifies blind digital signature mechanisms, as well as three variants: blind digital
signature mechanisms with partial disclosure, blind digital signature mechanisms with selective
disclosure and traceable blind digital signature mechanisms. ISO/IEC 18370-1 specifies principles and
requirements for these mechanisms. This part of ISO/IEC 18370 specifies several specific instances of
these mechanisms.
The security of blind digital signature mechanisms and their variants depends on computational
problems believed to be intractable, i.e. problems for which, given current knowledge, finding a solution
is computationally infeasible, such as the integer factorization problem or the discrete logarithm
problem in an appropriate group. The mechanisms specified in this part of ISO/IEC 18370 are based on
the latter problem.
ISO/IEC 18370 does not specify mechanisms for key management or for certification of public keys. A
variety of means are available for obtaining a reliable copy of the public verification key, e.g. a public
key certificate. Techniques for managing keys and certificates are outside the scope of ISO/IEC 18370.
For further information, see ISO/IEC 9594-8, ISO/IEC 11770-3 and ISO/IEC 15945.
This part of ISO/IEC 18370 specifies mechanisms that use a collision resistant hash-function to hash
the message to be blindly signed. ISO/IEC 10118 specifies hash-functions.
The generation of key pairs requires random bits and prime numbers. The generation of signatures
requires random bits. Techniques for producing random bits and prime numbers are outside the scope
of ISO/IEC 18370. For further information, see ISO/IEC 18031 and ISO/IEC 18032.
vi © ISO/IEC 2016 – All rights reserved
INTERNATIONAL STANDARD ISO/IEC 18370-2:2016(E)
Information technology — Security techniques — Blind
digital signatures —
Part 2:
Discrete logarithm based mechanisms
1 Scope
This part of ISO/IEC 18370 specifies blind digital signature mechanisms, together with mechanisms
for three variants of blind digital signatures. The variants are blind digital signature mechanisms with
partial disclosure, blind digital signature mechanisms with selective disclosure and traceable blind
digital signature mechanisms. The security of all the mechanisms in this part of ISO/IEC 18370 is based
on the discrete logarithm problem.
For each mechanism, this part of ISO/IEC 18370 specifies the following:
— the process for generating the keys of the entities involved in these mechanisms;
— the process for producing blind signatures;
— the process for verifying signatures.
This part of ISO/IEC 18370 specifies another process specific to blind signature mechanisms with
selective disclosure, namely, the following:
— the presentation process.
Furthermore, this part of ISO/IEC 18370 specifies other processes specific to traceable blind signature
mechanisms, namely, the following:
a) the process for tracing requestors;
b) the process for tracing signatures;
c) the requestor tracing evidence evaluation process (optional);
d) the signature tracing evidence evaluation process (optional).
2 Normative references
The following documents, in whole or in part, are normatively referenced in this document and are
indispensable for its application. For dated references, only the edition cited applies. For undated
references, the latest edition of the referenced document (including any amendments) applies.
ISO/IEC 10118 (all parts), Information technology — Security techniques — Hash-functions
3 Terms and definitions
For the purposes of this document, the terms and definitions given in ISO/IEC 18370-1 and the
following apply.
3.1
abelian group
group (G, *) such that a * b = b * a for every a and b in G
© ISO/IEC 2016 – All rights reserved 1
3.2
cyclic group
group G of n elements that contains an element a in G, called the generator, of order n
[SOURCE: ISO/IEC 14888-3:2006, 3.2]
3.3
elliptic curve over a finite field
set E of points P = (x, y), where x and y are elements of the finite field (3.6), that satisfy a certain equation,
together with an extra point referred to as the point at infinity
Note 1 to entry: In this part of ISO/IEC 18370, only finite fields containing exactly q elements for a prime q > 3
are considered. In this case, the equation that every point P = (x, y) of E (other than the point at infinity) should
2 3 3 2
satisfy is of the form y = x + ax + b. The finite field elements a and b should satisfy 4a + 27b ≠ 0 (where 0 is
F F
the additive identity element of the finite field).
Note 2 to entry: The set of points E, together with an appropriately defined operation, forms a finite commutative
group (3.5), where the point at infinity is the identity element.
3.4
field
set of elements S and a pair of operations (+,*) defined on S, such that: i) a * (b + c) = a * b + a * c for
every a, b and c in S, ii) S together with + forms an abelian group (3.1) (with identity element 0), and iii)
S excluding 0 together with * forms an abelian group
3.5
finite commutative group
abelian group (3.1) (G, *) with a finite number of elements
0 n+1 n
Note 1 to entry: If a = e, and a = a * a (for n ≥ 0) is defined recursively, the order of a ∈ G is the least positive
n
integer n, such that a = e.
Note 2 to entry: In some cases, such as when G is the set of points on an elliptic curve, arithmetic in the finite set
G is described using additive notation.
3.6
finite field
field (3.4) such that the underlying set of elements is finite
m
Note 1 to entry: For any positive integer, m and a prime p, there exists a finite field containing exactly q = p
elements. This field is unique up to an isomorphism and is denoted by F .
q
[SOURCE: ISO/IEC 18033-2:2006, 3.21]
3.7
group
set of elements G and an operation * defined on the set of elements such that: i) (a * b) * c = a * (b * c) for
every a, b and c in G, ii) there exists an identity element, e in G, such that a * e = e * a = a for every a in G,
-1 -1 -1
and iii) for every a in G, there exists an inverse element, a in G, such that a * a = a * a = e
3.8
security parameters
variables that determine the security strength of a mechanism
2 © ISO/IEC 2016 – All rights reserved
4 Symbols
a ∈ A indicates that element a is in set A
a ‖ b concatenation of data items a and b in the order specified. In cases where the result of
concatenating two or more data items is input to a cryptographic algorithm as part of one
of the mechanisms specified in this part of ISO/IEC 18370, this result shall be composed
so that it can be uniquely resolved into its constituent data strings, i.e. so that there is no
possibility of ambiguity in interpretation. This latter property could be achieved in a vari-
ety of different ways, depending on the application. For example, it could be guaranteed by
a) fixing the length of each of the substrings throughout the domain of use of the mecha-
nism, or b) encoding the sequence of concatenated strings using a method that guarantees
[1]
unique decoding, e.g. using the distinguished encoding rules defined in ISO/IEC 8825-1 .
A ⊆ B indicates that the set A is a subset of or equal to set B
A \ B when A and B are sets, this represents the set of elements present in A but not in B.
|D| bit length of D if D is a bit string, or bit size of D if D is a non-negative number (i.e. 0 if D = 0,
i − 1 i
or the unique integer i such that 2 ≤ D < 2 if D > 0).
E an elliptic curve over the finite field F , for a prime p > 3
p
E(F ) the set of all points (x, y), x ∈ F , y ∈ F , which satisfy the defining equation of the curve E,
p p p
together with the point at infinity, O
E
#E(F ) the order (or cardinality) of E(F )
p p
F the finite field containing exactly p elements
p
g a generator of G
q
gcd(N , N ) the greatest common divisor of integers N and N
1 2 1 2
G a cyclic group of prime order q. For uniformity, the multiplicative notation is used
q
throughout. As such, when using the elliptic curve construction, it should be understood
that ab represents the group addition of points a and b, that a/b represents the group ad-
b
dition of the point a to the additive inverse of the point b, and that a represents the scalar
multiplication of point a by the integer b.
NOTE This part of ISO/IEC 18370 considers two constructions for the group G , in which
q
it is infeasible to compute discrete logarithms. The first is based on a subgroup of a finite
field, and the second is based on elliptic curves over a finite field F , where q is a prime
q
number. Details of these two constructions are provided in Annex C.
H a cryptographic hash-function
I a set of integers
[n]P scalar multiplication operation that takes a positive integer n and a point P on the elliptic
curve E as input and produces as output another point Q on the elliptic curve E, where
Q = [n]P = P + P +…+ P added n - 1 times. The operation satisfies [0]P = O (the point at
E
infinity), and [−n]P = [n](−P).
O the point at infinity on the elliptic curve E
E
P + Q the elliptic curve sum of points P and Q
q a prime number satisfying |q| = l where l is a security parameter
q q
© ISO/IEC 2016 – All rights reserved 3
Z the set of integers in [0, p − 1] with arithmetic defined modulo p
p
*
Z the set of integers U with 0 < U < N and gcd(U, N) = 1, with arithmetic defined modulo N
N
∏ a product of the values a for which i ∈ I
(i ∈ I) i i
[x, y] the set of integers from x to y inclusive, if x, y are integers satisfying x ≤ y
an ordered list of values to be hashed
...
5 General requirements
In order to use any of the mechanisms specified in this part of ISO/IEC 18370, the following requirements
shall be met.
— Each entity involved in a blind signature mechanism shall be aware of the public domain parameters.
— Each entity shall have access to an authentic copy of the necessary public keys, such as the public
verification key.
— Each requestor in a traceable blind signature mechanism shall have a distinguishing identifier that
is unambiguously bound to the private requestor key. The distinguishing identifier for a requestor
can be the public requestor key.
— Both signer and requestor shall have the means to generate integers uniformly at random from a
given range. Techniques for generation of sequences of random bits are specified in ISO/IEC 18031.
A method for converting a string of bits to an integer in a given range is specified in Annex B.
— A collision-resistant hash-function such as one of those specified in ISO/IEC 10118 shall be used.
Before issuing a blind signature, the signer might wish to authenticate the requestor. ISO/IEC 18370 does
not specify mechanisms for entity authentication. For this purpose, the use of one of the mechanisms
specified in ISO/IEC 9798 is recommended.
For traceable blind signature mechanisms, this part of ISO/IEC 18370 does not specify in which
circumstances a requestor tracing process or a signature tracing process is used.
6 Blind signature mechanisms
6.1 General
Clause 6 specifies a blind signature mechanism.
NOTE The mechanism in Clause 6 is based on Reference [23] and the associated security analysis is given in
Reference [26].
6.2 Mechanism 1
6.2.1 Security parameters
The following symbols apply in the specification of this mechanism:
— k, l : security parameters.
q
The parties should agree on the security parameters in use. Guidance for parameter choice is given in
Annex E.
4 © ISO/IEC 2016 – All rights reserved
6.2.2 Key generation process
The key generation process of a blind signature mechanism consists of the following procedures:
a) generating domain parameters;
b) generating a private signature key and a public verification key.
The first procedure is executed once when the domain is set up. The second procedure is executed for
each signer within the domain, where the outputs are a private signature key and the corresponding
public verification key.
The set of domain parameters includes the following parameters:
— q: a prime number where |q| = l ;
q
— G : a cyclic group of prime order q;
q
— g : a random generator of G ;
1 q
— g : a random generator of G different from g ;
2 q 1
NOTE 1 An example of recommended parameters for typical security levels is provided in E.2.
NOTE 2 A method for selecting random generators is given in ISO/IEC 14888-3:2006, D.2.2.
— H: a hash-function that outputs a k-bit message digest.
The pair of keys of the signer is computed as follows.
a) The signer picks two integers, x and x , uniformly at random from the range [1, q − 1].
1 2
−−xx
b) The signer computes yg= g .
The signature key is the pair (x , x ) and the verification key is y.
1 2
6.2.3 Blind signature process
A blind signature process is an interactive protocol between a signer and a requestor. By executing the
signing protocol, the requestor obtains a valid signature of a message of the requestor’s choice in such a
way that the signer learns nothing about the message or the resulting signature.
The signature process involves the following steps. The message to be blindly signed is denoted by m,
*
where m ∈ {0, 1} .
a) The signer picks two integers, w and w , uniformly at random from the range [0, q − 1].
1 2
ww
b) The signer computes ag= g .
c) The signer sends a to the requestor.
d) The requestor receives a from the signer.
e) The requestor picks an integer α uniformly at random from the range [0, q − 1].
f) The requestor picks an integer β uniformly at random from the range [0, q − 1].
g) The requestor picks an integer γ uniformly at random from the range [0, q − 1].
α β −γ
h) The requestor computes a′ = a g g y .
1 2
i) The requestor computes c′ = H(m ‖ a′).
j) The requestor computes c = c′ + γ mod q.
© ISO/IEC 2016 – All rights reserved 5
k) The requestor sends c to the signer.
l) The signer receives c from the requestor.
m) The signer computes r = w + c x mod q.
1 1 1
n) The signer computes r = w + c x mod q.
2 2 2
o) The signer sends r and r to the requestor.
1 2
p) The requestor receives r and r from the signer.
1 2
q) The requestor checks that the values r and r have been correctly computed by verifying that
1 2
rr c
ag= gy . If this verification fails, the requestor outputs reject and stops.
r) The requestor computes r ′ = r + α mod q.
1 1
s) The requestor computes r ′ = r + β mod q.
2 2
t) The requestor sets the signature to σ = (c′, r ′, r ′).
1 2
6.2.4 Verification process
On input of a message, m, a signature σ = (c′, r ′, r ′), domain parameters, and the verification key, y, the
1 2
verification process involves the following steps.
rr
c
12′′ ′
′′
a) The verifier computes ag= gy .
b) The verifier computes c″ = H(m ‖ a″).
c) If c″ = c′ then return 1 (valid).
d) Else return 0 (invalid).
7 Blind signature mechanisms with partial disclosure
7.1 General
Clause 7 specifies two blind signature mechanisms with partial disclosure.
NOTE The mechanism in 7.2 is based on Reference [14], in which security proofs can also be found. The
mechanism given in 7.3 is based on a scheme originally specified in Reference [17] and the associated security
analysis is given in Reference [18].
7.2 Mechanism 2
7.2.1 Security parameters
The following symbol applies in the specification of this mechanism:
— l : a security parameter.
q
7.2.2 Key generation process
The key generation process of a blind signature mechanism consists of the following procedures:
a) generating domain parameters;
b) generating a private signature key and a public verification key.
6 © ISO/IEC 2016 – All rights reserved
The set of domain parameters includes the following parameters:
— q: a prime number satisfying |q| = l ;
q
— G : a cyclic group of prime order q;
q
— g: a random generator of G ;
q
— F: {0, 1}* → G a cryptographic hash-function, where the discrete logarithm of value F(x) in base g
q
shall be unknown;
— H: {0, 1}* → [0, q − 1] a hash-function.
NOTE 1 An example of recommended parameters for typical security levels is provided in E.2.
NOTE 2 Examples of how to construct F and H are provided in Annex D.
The pair of keys of the signer is computed as follows.
a) The signer picks an integer, x, uniformly at random from the range [1, q − 1].
x
b) The signer computes y = g .
The signature key is x and the verification key is y.
7.2.3 Blind signature process with partial disclosure
The signature process involves the following steps. The message to be blindly signed is denoted by m,
where m ∈ {0, 1}*, and the common information is denoted by info, where info ∈ {0, 1}*.
a) The signer picks three integers, u, s, d, uniformly at random from the range [0, q − 1], and computes
z = F(info).
u s d
b) The signer computes a = g , b = g z .
c) The signer sends a, b to the requestor.
d) The requestor receives a, b from the signer.
e) The requestor picks two integers, t and t , uniformly at random from the range [0, q − 1].
1 2
f) The requestor picks two integers, t and t , uniformly at random from the range [0, q − 1].
3 4
g) The requestor computes z = F(info).
tt t t
12 3 4
′
h) The requestor computes a′ = ag yb, =bg z .
i) The requestor computes e′ = H(a′ ‖ b′ ‖ z ‖ m) ∈ [0, q − 1].
j) The requestor computes e = e′ − t − t mod q.
2 4
k) The requestor sends e to the signer.
l) The signer receives e from the requestor.
m) The signer computes c = e − d mod q.
n) The signer computes r = u − cx mod q.
o) The signer sends r, c, s, d to the requestor.
p) The requestor receives r, c, s, d from the signer.
© ISO/IEC 2016 – All rights reserved 7
q) The requestor checks that the values r, c, s, d have been correctly computed by verifying that
r c s d
a = g y , b = g z , e = c + d mod q. If this verification fails, the requestor outputs reject and stops.
r) The requestor computes r′ = r + t , c′ = c + t mod q.
1 2
s) The requestor computes s′ = s + t , d′ = d + t mod q.
3 4
t) The requestor sets the signature to σ = (r′, c′, s′, d′).
7.2.4 Verification process
On input of a message, m, a common information, info, a signature, σ = (r′, c′, s′, d′), domain parameters,
and the verification key, y, the verification process involves the following steps.
r′ c′ s′ d′
a) The verifier computes z = F(info), a′ = g y , b′ = g z .
b) The verifier computes e′ = H(a′ ‖ b′ ‖ z ‖ m).
c) If e′ = c′ + d′ mod q then return 1 (valid).
d) Else return 0 (invalid).
7.3 Mechanism 3
7.3.1 Symbols
The following symbol applies in the specification of this mechanism:
— l : a security parameter.
q
7.3.2 Key generation process
The key generation process of a blind signature mechanism consists of the following procedures:
a) generating domain parameters;
b) generating a private signature key and a public verification key.
The set of domain parameters includes the following parameters:
— q: a prime number satisfying |q| = l ;
q
— G : a cyclic group of prime order q;
q
— g : a random generator of G ;
1 q
— g : a random generator of G different from g ;
2 q 1
— H: {0, 1}* → [0, q − 1] a cryptographic hash-function;
— H : {0, 1}* → [0, q − 1] a cryptographic hash-function.
NOTE 1 An example of recommended parameters for typical security levels is provided in E.2.
NOTE 2 Examples of how to construct H and H are provided in Annex D.
The pair of keys of the signer is computed as follows.
a) The signer picks an integer, x, uniformly at random from the range [1, q − 1].
x
b) The signer computes y = g .
1 1
x
c) The signer computes y = g .
2 2
8 © ISO/IEC 2016 – All rights reserved
The signature key is x and the verification key is the pair (y , y ).
1 2
7.3.3 Blind signature process with partial disclosure
The signature process involves the following steps. The message to be blindly signed is denoted by m,
where m ∈ {0, 1}*, and the common information is denoted by info, where info ∈ {0, 1}*.
a) The signer picks an integer, ω, uniformly at random from the range [0, q − 1].
H ()info
b) The signer computes gg= g .
M 12
ω
c) The signer computes t′ = g .
M
d) The signer sends t′ to the signer.
e) The requestor receives t′ from the signer.
f) The requestor picks two integers, λ and μ, uniformly at random from the range [0, q − 1].
H ()info
g) The requestor computes gg= g .
M 12
H ()info
h) The requestor computes yy= y .
M 12
λ μ
i) The requestor computes t = t′ g y .
M M M
j) The requestor computes c = H(t ‖ info ‖ m).
M
k) The requestor computes c′ = c − μ mod q.
l) The requestor sends c′ to the signer.
m) The signer receives c′ from the requestor.
n) The signer computes r′ = ω − c′x mod q.
o) The signer sends r′ to the requestor.
p) The requestor receives r′ from the signer.
r′ c′
q) The requestor checks that the value r′ has been correctly computed by verifying that t′ = g y .
M M
If this verification fails, the requestor outputs reject and stops.
r) The requestor computes r = r′ + λ mod q.
s) The requestor sets the signature to σ = (c, r).
7.3.4 Verification process
On input of a message, m, a common information, info, a signature, σ = (c, r), domain parameters, and the
verification key, (y , y ), the verification process involves the following steps.
1 2
r c
H ()info H ()info
a) The verifier computes t″ = gg yy .
( 12) ( 12)
b) The verifier computes c″ = H(t″ ‖ info ‖ m).
c) If c = c″ then return 1 (valid).
d) Else return 0 (invalid).
© ISO/IEC 2016 – All rights reserved 9
8 Blind signature mechanisms with selective disclosure
8.1 General
Clause 8 specifies a blind signature mechanism with selective disclosure.
NOTE The mechanism in Clause 8 is based on Reference [16].
8.2 Mechanism 4
8.2.1 Security parameters
The following symbol applies in the specification of this mechanism:
— l : a security parameter.
q
8.2.2 Key generation process
The key generation process of a blind signature mechanism with selective disclosure consists of the
following procedures:
a) generating domain parameters;
b) generating a private signature key and a public verification key.
The first procedure is executed once when the domain is set up. The second procedure is executed for
each signer within the domain. The outputs are a private signature key and the corresponding public
verification key.
The set of domain parameters includes the following parameters:
— q: a prime number satisfying |q| = l ;
q
— G : a cyclic group of prime order q;
q
— g: a random generator of G ;
q
— n: an integer indicating the number of messages to be signed by the signer;
— g ,…, g , g : n + 1: random generators of G , different from each other’s and from g, and where t is a
1 n t q
special index for the token message.
The pair of keys of the signer is computed as follows.
a) The signer picks an integer, y , uniformly at random from the range [1, q − 1].
y
b) The signer computes gg= .
The signature key is the element y and the verification key is g .
0 0
8.2.3 Blind signature process with selective disclosure
A blind signature process with selective disclosure is an interactive process between a signer and
a requestor. By executing the signing process, the requestor obtains a valid signature on a vector of
messages known to the signer, and a message and public key known only to the requestor, in such a way
that the signer learns nothing about the resulting signature. The resulting public key and signature is
called a token. The token can be presented to a verifier using the corresponding private key as described
in 8.2.5.
10 © ISO/IEC 2016 – All rights reserved
The signature process involves the following steps. The message vector to be signed is denoted by
(x ,…, x , x ) where the x ∈ [0, q − 1] (t is a special token index), and the requestor’s message is denoted
1 n t i
by PI, where PI ∈ {0, 1}*.
x
x x
1 n t
a) The signer and the requestor both computeγ = gg .gg ∈G .
01 n t q
y
b) The signer computes σγ= .
z
c) The signer picks an integer, w, uniformly at random from the range [0, q − 1].
w
d) The signer computes σ = g .
a
w
e) The signer computes σ = γ .
b
f) The requestor picks an integer, α, uniformly at random from the range [1, q − 1].
g) The requestor picks an integer, β , uniformly at random from the range [0, q − 1].
h) The requestor picks an integer, β , uniformly at random from the range [0, q − 1].
α
i) The requestor computes h = γ .
ββ
j) The requestor computes tg= g .
β
k) The requestor computesth= .
−1
l) The requestor computes α mod q.
m) The signer sends (σ , σ , σ ) to the requestor.
z a b
n) The requestor receives (σ , σ , σ ) from the signer.
z a b
α
o) The requestor computes σ′ = σ .
z z
p) The requestor computes σ′ = t σ .
a 1 a
β α
′ ′
q) The requestor computesσσ= t σ .
bz 2 b
r) The requestor computes σ′ = H(h ‖ PI ‖ σ′ ‖ σ′ ‖ σ′ ) mod q.
c z a b
s) The requestor computes σ = σ′ + β mod q.
c c 1
t) The requestor sends σ to the signer.
c
u) The signer receives σ from the requestor.
c
v) The signer computes σ = σ y + w mod q.
r c 0
w) The signer sends σ to the requestor.
r
x) The requestor receives σ from the signer.
r
y) The requestor computes σ′ = σ + β mod q.
r r 2
σ′ −σ′
r c
′′ ′
z) The requestor verifies that σσ = gh g σ . If this verification fails, the requestor
() ()
ab 0 z
outputs reject and stops.
aa) The requestor outputs the token consisting of the public key, h, and the signature (σ′ , σ′ , σ′ ), and
z c r
−1
the corresponding private key, α .
© ISO/IEC 2016 – All rights reserved 11
8.2.4 Presentation process
A blind signature with selective disclosure presentation process is performed by the requestor. By
executing the presentation process, the requestor creates a presentation proof containing a subset of
the signed message vector.
The presentation process takes the following input parameters:
— D ⊆ {1, …, n} the set of disclosed messages indices;
— U = {1, …, n} \ D the set of undisclosed messages indices;
*
— (m, m ) ∈ {0, 1} , the two part message to be signed by the requestor;
d
NOTE The message to be signed is separated into two parts, m and m , to allow extension mechanisms,
d
not defined herein, to use a second-factor to sign part of the protocol message, m , without seeing the all of
d
the protocol details.
— h, the token public key;
−1
— α ∈ [0, q − 1], the token private key;
— (x ,…, x ), the signed messages where the x ∈ [0, q − 1].
1 n i
The presentation process involves the following steps.
a) The requestor picks an integer, w , uniformly at random from the range [0, q − 1].
b) For each i ∈ U, the requestor picks an integer, w , uniformly at random from the range [0, q − 1].
i
w w
0 i
c) The requestor computesaH=∏hg .
i
iU∈
()
d) The requestor computes UID = H(h ‖ σ′ ‖ σ′ ‖ σ′ ).
t z c r
e) The requestor computes c = H(UID ‖ a ‖ D ‖ xi∈D ‖ Ø ‖ Ø ‖ Ø ‖ Ø ‖ Ø ‖ Ø ‖ m) where Ø is
p t {}
i
the null value, a zero-length octet string.
f) The requestor computes c = Hc ,m mod q.
( )
pd
−1
g) The requestor computes r = c α + w mod q.
0 0
h) For each i ∈ U, the requestor computes r = −c x + w mod q.
i i i
i) The requestor outputs the presentation proof {x } , x , a, r , {r } .
i i ∈ D t 0 i i ∈ U
8.2.5 Verification process
A blind signature with selective disclosure verification process is performed by the verifier.
The verification process takes the following input parameters:
— D ⊆ {1, …, n} the set of disclosed messages indices;
— U = {1, …, n} − D the set of undisclosed messages indices;
*
— (m, m ) ∈ {0, 1} , the two part message signed by the requestor;
d
NOTE The message to be signed is separated into two parts, m and m , to allow extension mechanisms,
d
not defined herein, to use a second-factor to sign part of the protocol message, m , without seeing all of the
d
protocol details.
— h, the token public key;
12 © ISO/IEC 2016 – All rights reserved
— PI ∈ {0, 1}*, the requestor’s information message;
— (σ′ , σ′ , σ′ ), the token signature;
z c r
— {x } , x , a, r , {r } , the presentation proof.
i i ∈ D t 0 i i ∈ U
The verification process involves the following steps.
a) The verifier verifies that h ≠ 1. If this verification fails, the verifier outputs invalid and stops.
′ −σ′ ′ −σ′
σ σ
r c r c
′ ′′
b) The verifier verifies that σσ=HhPI gg h σ mod q. If this verification fails,
cz( 0 z )
the verifier outputs invalid and stops.
c) The verifier computes UID = H(h ‖ σ′ ‖ σ′ ‖ σ′ ).
t z c r
d) The verifier computes c = H(UID ‖ a ‖ D ‖ xi∈D ‖ Ø ‖ Ø ‖ Ø ‖ Ø ‖ Ø ‖ Ø ‖ m).
p t {}
i
e) The verifier computes c = Hc ,m mod q.
)
(
pd
−c
x x r r
t ii 0
f) The verifier verifies that aH=∏gg gh ∏ g . If this verification fails,
0 t i i
iD∈ iU∈
() ()
the verifier outputs invalid, and valid otherwise.
9 Traceable blind signature mechanisms
9.1 General
Clause 9 specifies a traceable blind signature mechanism.
NOTE The mechanism in Clause 9 is based on Reference [19], in which security proofs can also be found.
9.2 Mechanism 5
9.2.1 Symbols
The following symbol applies in the specification of this mechanism:
— l : a security parameter.
q
9.2.2 Key generation process
The key generation process of a fair blind signature mechanism consists of five procedures that shall be
executed in the following order for mechanism 5:
a) gene
...


Questions, Comments and Discussion
Ask us and Technical Secretary will try to provide an answer. You can facilitate discussion about the standard in here.
Loading comments...