ISO/IEC 18033-3:2010
(Main)Information technology — Security techniques — Encryption algorithms — Part 3: Block ciphers
Information technology — Security techniques — Encryption algorithms — Part 3: Block ciphers
ISO/IEC 18033 specifies encryption systems (ciphers) for the purpose of data confidentiality. ISO/IEC 18033-3:2010 specifies block ciphers. A block cipher is a symmetric encipherment system with the property that the encryption algorithm operates on a block of plaintext, i.e. a string of bits of a defined length, to yield a block of ciphertext. ISO/IEC 18033-3:2010 specifies following algorithms: 64-bit block ciphers: TDEA, MISTY1, CAST-128, HIGHT; 128-bit block ciphers: AES, Camellia, SEED. NOTE The primary purpose of encryption (or encipherment) techniques is to protect the confidentiality of stored or transmitted data. An encryption algorithm is applied to data (often called plaintext or cleartext) to yield encrypted data (or ciphertext); this process is known as encryption. The encryption algorithm needs to be designed so that the ciphertext yields no information about the plaintext except, perhaps, its length. Associated with every encryption algorithm is a corresponding decryption algorithm, which transforms ciphertext back into its original plaintext.
Technologies de l'information — Techniques de sécurité — Algorithmes de chiffrement — Partie 3: Chiffrement par blocs
General Information
- Status
- Published
- Publication Date
- 13-Dec-2010
- Drafting Committee
- ISO/IEC JTC 1/SC 27/WG 2 - Cryptography and security mechanisms
- Current Stage
- 9093 - International Standard confirmed
- Start Date
- 26-Sep-2025
- Completion Date
- 12-Feb-2026
Relations
- Effective Date
- 09-Feb-2026
- Effective Date
- 09-Feb-2026
- Effective Date
- 09-Feb-2026
- Effective Date
- 09-Feb-2026
- Referred By
EN 15684:2020 - Building hardware - Mechatronic cylinders - Requirements and test methods - Effective Date
- 09-Feb-2026
- Referred By
EN 15509:2014 - Electronic fee collection - Interoperability application profile for DSRC - Effective Date
- 09-Feb-2026
- Effective Date
- 09-Feb-2026
- Effective Date
- 09-Feb-2026
- Referred By
EN 16867:2020 - Building hardware - Mechatronic door furniture - Requirements and test methods - Effective Date
- 09-Feb-2026
- Effective Date
- 09-Feb-2026
- Effective Date
- 09-Feb-2026
- Effective Date
- 09-Feb-2026
- Effective Date
- 09-Feb-2026
- Referred By
EN 13757-7:2018 - Communication systems for meters - Part 7: Transport and security services - Effective Date
- 09-Feb-2026
- Effective Date
- 01-Jan-2022
Overview
ISO/IEC 18033-3:2010 - "Information technology - Security techniques - Encryption algorithms - Part 3: Block ciphers" is the international standard that specifies a set of block cipher algorithms for the protection of data confidentiality. The document defines how symmetric block ciphers map fixed-size plaintext blocks to ciphertext blocks under a key, and it standardizes seven specific algorithms across two block sizes (64-bit and 128-bit).
Key algorithms covered:
- 64-bit block ciphers: TDEA, MISTY1, CAST-128, HIGHT
- 128-bit block ciphers: AES, Camellia, SEED
The standard includes algorithm descriptions, encryption/decryption operations, functions, key schedules, test vectors and object identifiers.
Key topics and technical requirements
- Block cipher definitions and terminology - formal definitions of block, block cipher, ciphertext and key.
- Algorithm specifications - complete functional descriptions of each listed cipher (encryption/decryption steps, round functions).
- Key schedules and keying options - for example, TDEA (Triple DES) keying options and supported key lengths (128 or 192 bits as specified).
- Block lengths and supported key sizes - the standard organizes ciphers by block length (64-bit and 128-bit); AES is specified with 128/192/256-bit keys.
- Normative annexes and test vectors - includes a normative description of DES and informative test vectors to validate implementations.
- Object identifiers (OID) - assigned OIDs for each algorithm (Annex B), enabling interoperable identification in protocols.
- Implementation aids - S-box algebraic forms, feature tables and example vectors (Annexes C–E and D).
Practical applications
- Securing stored and transmitted data - use block ciphers standardized here to provide confidentiality in databases, file systems, VPNs, TLS-like protocols and encrypted messaging.
- Cryptographic library development - implementers use the formal algorithm and key-schedule descriptions and test vectors to build compliant, interoperable crypto libraries.
- Product certification and procurement - vendors and evaluators reference ISO/IEC 18033-3 when specifying acceptable block ciphers for compliance or procurement requirements.
- Interoperability in protocols - OIDs and standardized behavior enable consistent algorithm selection across systems and protocols.
Who should use this standard
- Security architects and systems designers selecting encryption primitives.
- Cryptographic engineers and library implementers validating correctness with test vectors.
- QA, compliance and procurement teams assessing supported algorithms.
- Standards bodies and protocol developers requiring normative algorithm references.
Related standards
- ISO/IEC 18033 (series): Part 1 - General; Part 2 - Asymmetric ciphers; Part 4 - Stream ciphers.
- Referenced work: ISO/IEC 9834 (object identifiers), ISO/IEC JTC 1/SC 27 (security techniques).
ISO/IEC 18033-3 is a practical, normative resource for implementing and validating block cipher algorithms used to protect data confidentiality in modern IT systems.
Get Certified
Connect with accredited certification bodies for this standard

BSI Group
BSI (British Standards Institution) is the business standards company that helps organizations make excellence a habit.

Bureau Veritas
Bureau Veritas is a world leader in laboratory testing, inspection and certification services.

DNV
DNV is an independent assurance and risk management provider.
Sponsored listings
Frequently Asked Questions
ISO/IEC 18033-3:2010 is a standard published by the International Organization for Standardization (ISO). Its full title is "Information technology — Security techniques — Encryption algorithms — Part 3: Block ciphers". This standard covers: ISO/IEC 18033 specifies encryption systems (ciphers) for the purpose of data confidentiality. ISO/IEC 18033-3:2010 specifies block ciphers. A block cipher is a symmetric encipherment system with the property that the encryption algorithm operates on a block of plaintext, i.e. a string of bits of a defined length, to yield a block of ciphertext. ISO/IEC 18033-3:2010 specifies following algorithms: 64-bit block ciphers: TDEA, MISTY1, CAST-128, HIGHT; 128-bit block ciphers: AES, Camellia, SEED. NOTE The primary purpose of encryption (or encipherment) techniques is to protect the confidentiality of stored or transmitted data. An encryption algorithm is applied to data (often called plaintext or cleartext) to yield encrypted data (or ciphertext); this process is known as encryption. The encryption algorithm needs to be designed so that the ciphertext yields no information about the plaintext except, perhaps, its length. Associated with every encryption algorithm is a corresponding decryption algorithm, which transforms ciphertext back into its original plaintext.
ISO/IEC 18033 specifies encryption systems (ciphers) for the purpose of data confidentiality. ISO/IEC 18033-3:2010 specifies block ciphers. A block cipher is a symmetric encipherment system with the property that the encryption algorithm operates on a block of plaintext, i.e. a string of bits of a defined length, to yield a block of ciphertext. ISO/IEC 18033-3:2010 specifies following algorithms: 64-bit block ciphers: TDEA, MISTY1, CAST-128, HIGHT; 128-bit block ciphers: AES, Camellia, SEED. NOTE The primary purpose of encryption (or encipherment) techniques is to protect the confidentiality of stored or transmitted data. An encryption algorithm is applied to data (often called plaintext or cleartext) to yield encrypted data (or ciphertext); this process is known as encryption. The encryption algorithm needs to be designed so that the ciphertext yields no information about the plaintext except, perhaps, its length. Associated with every encryption algorithm is a corresponding decryption algorithm, which transforms ciphertext back into its original plaintext.
ISO/IEC 18033-3:2010 is classified under the following ICS (International Classification for Standards) categories: 35.030 - IT Security; 35.040 - Information coding. The ICS classification helps identify the subject area and facilitates finding related standards.
ISO/IEC 18033-3:2010 has the following relationships with other standards: It is inter standard links to EN ISO 14906:2023, CEN/TS 16702-1:2014, CEN/TS 16702-2:2015, EN ISO 13141:2015, EN 15684:2020, EN 15509:2014, EN ISO 13141:2024, CEN ISO/TS 21719-2:2018, EN 16867:2020, CEN/TS 16702-1:2020, EN 16867:2020+A2:2024, CEN/TS 16702-2:2020, EN 16867:2020+A1:2021, EN 13757-7:2018, ISO/IEC 18033-3:2010/Amd 1:2021. Understanding these relationships helps ensure you are using the most current and applicable version of the standard.
ISO/IEC 18033-3:2010 is available in PDF format for immediate download after purchase. The document can be added to your cart and obtained through the secure checkout process. Digital delivery ensures instant access to the complete standard document.
Standards Content (Sample)
INTERNATIONAL ISO/IEC
STANDARD 18033-3
Second edition
2010-12-15
Information technology — Security
techniques — Encryption algorithms —
Part 3:
Block ciphers
Technologies de l'information — Techniques de sécurité — Algorithmes
de chiffrement
Partie 3: Chiffrement par blocs
Reference number
©
ISO/IEC 2010
PDF disclaimer
This PDF file may contain embedded typefaces. In accordance with Adobe's licensing policy, this file may be printed or viewed but
shall not be edited unless the typefaces which are embedded are licensed to and installed on the computer performing the editing. In
downloading this file, parties accept therein the responsibility of not infringing Adobe's licensing policy. The ISO Central Secretariat
accepts no liability in this area.
Adobe is a trademark of Adobe Systems Incorporated.
Details of the software products used to create this PDF file can be found in the General Info relative to the file; the PDF-creation
parameters were optimized for printing. Every care has been taken to ensure that the file is suitable for use by ISO member bodies. In
the unlikely event that a problem relating to it is found, please inform the Central Secretariat at the address given below.
© ISO/IEC 2010
All rights reserved. Unless otherwise specified, no part of this publication may be reproduced or utilized in any form or by any means,
electronic or mechanical, including photocopying and microfilm, without permission in writing from either ISO at the address below or
ISO's member body in the country of the requester.
ISO copyright office
Case postale 56 • CH-1211 Geneva 20
Tel. + 41 22 749 01 11
Fax + 41 22 749 09 47
E-mail copyright@iso.org
Web www.iso.org
Published in Switzerland
ii © ISO/IEC 2010 – All rights reserved
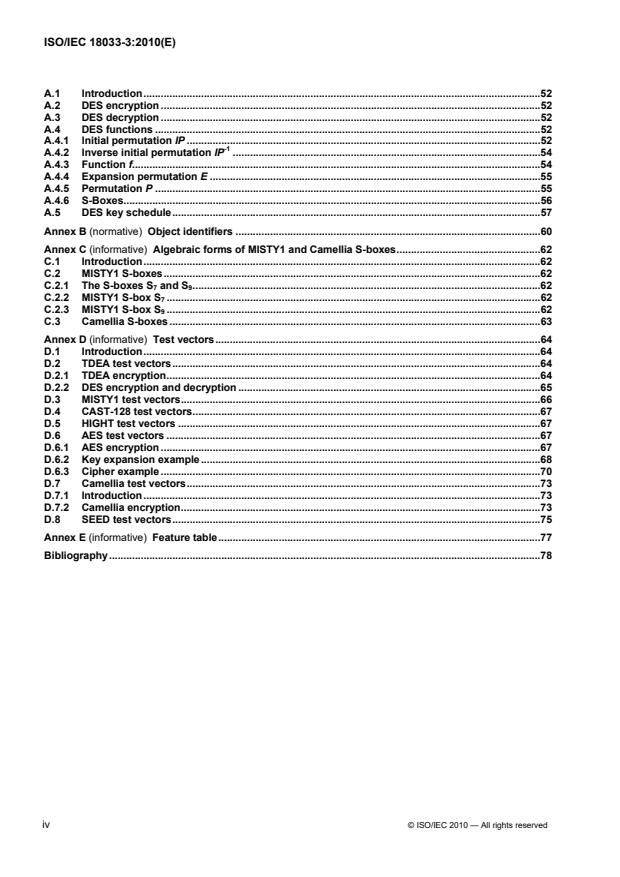
Contents Page
Foreword . v
1 Scope . 1
2 Terms and definitions . 1
3 Symbols . 2
4 64-bit block ciphers . 3
4.1 Introduction . 3
4.2 TDEA . 3
4.2.1 The Triple Data Encryption Algorithm . 3
4.2.2 TDEA encryption/decryption . 3
4.2.3 TDEA keying options . 4
4.3 MISTY1 . 4
4.3.1 The MISTY1 algorithm . 4
4.3.2 MISTY1 encryption . 4
4.3.3 MISTY1 decryption . 5
4.3.4 MISTY1 functions . 5
4.3.5 MISTY1 key schedule . 10
4.4 CAST-128 . 11
4.4.1 The CAST-128 algorithm . 11
4.4.2 CAST-128 encryption . 11
4.4.3 CAST-128 decryption . 11
4.4.4 CAST-128 functions . 11
4.4.5 CAST-128 key schedule . 18
4.5 HIGHT. 20
4.5.1 The HIGHT algorithm . 20
4.5.2 HIGHT encryption . 21
4.5.3 HIGHT decryption . 22
4.5.4 HIGHT functions . 23
4.5.5 HIGHT key schedule . 23
5 128-bit block ciphers . 24
5.1 Introduction . 24
5.2 AES . 24
5.2.1 The AES algorithm . 24
5.2.2 AES encryption . 24
5.2.3 AES decryption . 25
5.2.4 AES transformations . 26
5.2.5 AES key schedule . 30
5.3 Camellia . 32
5.3.1 The Camellia algorithm . 32
5.3.2 Camellia encryption . 32
5.3.3 Camellia decryption . 34
5.3.4 Camellia functions . 37
5.3.5 Camellia key schedule . 43
5.4 SEED . 47
5.4.1 The SEED algorithm . 47
5.4.2 SEED encryption . 47
5.4.3 SEED decryption . 47
5.4.4 SEED functions . 48
5.4.5 SEED key schedule . 50
Annex A (normative) Description of DES . 52
© ISO/IEC 2010 — All rights reserved iii
A.1 Introduction . 52
A.2 DES encryption . 52
A.3 DES decryption . 52
A.4 DES functions . 52
A.4.1 Initial permutation IP . 52
-1
A.4.2 Inverse initial permutation IP . 54
A.4.3 Function f . 54
A.4.4 Expansion permutation E . 55
A.4.5 Permutation P . 55
A.4.6 S-Boxes . 56
A.5 DES key schedule . 57
Annex B (normative) Object identifiers . 60
Annex C (informative) Algebraic forms of MISTY1 and Camellia S-boxes . 62
C.1 Introduction . 62
C.2 MISTY1 S-boxes . 62
C.2.1 The S-boxes S and S . 62
7 9
C.2.2 MISTY1 S-box S . 62
C.2.3 MISTY1 S-box S . 62
C.3 Camellia S-boxes . 63
Annex D (informative) Test vectors . 64
D.1 Introduction . 64
D.2 TDEA test vectors . 64
D.2.1 TDEA encryption . 64
D.2.2 DES encryption and decryption . 65
D.3 MISTY1 test vectors . 66
D.4 CAST-128 test vectors . 67
D.5 HIGHT test vectors . 67
D.6 AES test vectors . 67
D.6.1 AES encryption . 67
D.6.2 Key expansion example . 68
D.6.3 Cipher example . 70
D.7 Camellia test vectors . 73
D.7.1 Introduction . 73
D.7.2 Camellia encryption . 73
D.8 SEED test vectors . 75
Annex E (informative) Feature table . 77
Bibliography . 78
iv © ISO/IEC 2010 — All rights reserved
Foreword
ISO (the International Organization for Standardization) and IEC (the International Electrotechnical
Commission) form the specialized system for worldwide standardization. National bodies that are members
of ISO or IEC participate in the development of International Standards through technical committees
established by the respective organization to deal with particular fields of technical activity. ISO and IEC
technical committees collaborate in fields of mutual interest. Other international organizations, governmental
and non-governmental, in liaison with ISO and IEC, also take part in the work. In the field of information
technology, ISO and IEC have established a joint technical committee, ISO/IEC JTC 1.
International Standards are drafted in accordance with the rules given in the ISO/IEC Directives, Part 2.
The main task of the joint technical committee is to prepare International Standards. Draft International
Standards adopted by the joint technical committee are circulated to national bodies for voting. Publication
as an International Standard requires approval by at least 75 % of the national bodies casting a vote.
Attention is drawn to the possibility that some of the elements of this document may be the subject of patent
rights. ISO and IEC shall not be held responsible for identifying any or all such patent rights.
ISO/IEC 18033-3 was prepared by Joint Technical Committee ISO/IEC JTC 1, Information technology,
Subcommittee SC 27, IT Security techniques.
This second edition cancels and replaces the first edition (ISO/IEC 18033-3:2005), which has been
technically revised. It also incorporates the Technical Corrigenda ISO/IEC 18033-3:2005/Cor.1:2006,
ISO/IEC 18033-3:2005/Cor.2:2007 and ISO/IEC 18033-3:2005/Cor.3:2008.
ISO/IEC 18033 consists of the following parts, under the general title Information technology — Security
techniques — Encryption algorithms:
⎯ Part 1: General
⎯ Part 2: Asymmetric ciphers
⎯ Part 3: Block ciphers
⎯ Part 4: Stream ciphers
© ISO/IEC 2010 — All rights reserved v
INTERNATIONAL STANDARD ISO/IEC 18033-3:2010(E)
Information technology — Security techniques — Encryption
algorithms —
Part 3:
Block ciphers
1 Scope
This part of ISO/IEC 18033 specifies block ciphers. A block cipher maps blocks of n bits to blocks of n bits,
under the control of a key of k bits. A total of seven different block ciphers are defined. They are
categorized in 98H96H96H96HTable 1.
Table 1 — Block ciphers specified
Block length Algorithm name (see #) Key length
TDEA (97H97H97H4.2) 128 or 192 bits
MISTY1 (98H98H98H4.3)
64 bits
CAST-128 (99H99H99H4.4) 128 bits
HIGHT (100H100H100H4.5)
AES (101H101H101H5.2)
128, 192 or 256 bits
128 bits Camellia (102H102H102H5.3)
SEED (103H103H103H5.4)
128 bits
The algorithms specified in this part of ISO/IEC 18033 have been assigned object identifiers in accordance
with ISO/IEC 9834. The list of assigned object identifiers is given in Annex B. Any changes to the
specification of the algorithms resulting in a change of functional behaviour will result in a change of the
object identifier assigned to the algorithm.
2 Terms and definitions
For the purposes of this document, the following terms and definitions apply.
2.1
block
string of bits of defined length
NOTE In this part of ISO/IEC 18033, the block length is either 64 or 128 bits.
[ISO/IEC 18033-1:2005]
2.2
block cipher
symmetric encipherment system with the property that the encryption algorithm operates on a block of
plaintext, i.e. a string of bits of a defined length, to yield a block of ciphertext
[ISO/IEC 18033-1:2005]
© ISO/IEC 2010 — All rights reserved 1
2.3
ciphertext
data which has been transformed to hide its information content
[ISO/IEC 9798-1:1997]
2.4
key
sequence of symbols that controls the operation of a cryptographic transformation (e.g. encipherment,
decipherment)
NOTE In all the ciphers specified in this part of ISO/IEC 18033, keys consist of a sequence of bits.
[ISO/IEC 11770-1:1996]
2.5
n-bit block cipher
block cipher with the property that plaintext blocks and ciphertext blocks are n bits in length
[ISO/IEC 10116:2006]
2.6
plaintext
unenciphered information
[ISO/IEC 9797-1:1999]
3 Symbols
n plaintext/ciphertext bit length for a block cipher
E encryption function with key K
K
D decryption function with key K
K
Nr the number of rounds for the AES algorithm, which is 10, 12 or 14 for the choices of key length
128, 192 or 256 bits respectively
⊕ the bit-wise logical exclusive-OR operation on bit-strings, i.e., if A, B are strings of the same
length then A ⊕ B is the string equal to the bit-wise logical exclusive-OR of A and B
⊗ multiplication of two polynomials (each with degree < 4) modulo x + 1
∧ the bit-wise logical AND operation on bit-strings, i.e., if A, B are strings of the same length then
A B is the string equal to the bit-wise logical AND of A and B
∧
∨ the bit-wise logical OR operation on bit-strings, i.e., if A, B are strings of the same length then
∨
A B is the string equal to the bit-wise logical OR of A and B
|| concatenation of bit strings
• finite field multiplication
<<< the left circular rotation of the operand by i bits
i
>>> the right circular rotation of the operand by i bits
i
2 © ISO/IEC 2010 — All rights reserved
x the bitwise complement of x
a mod n for integers a and n, (a mod n) denotes the (non-negative) remainder obtained when a is
divided by n. Equivalently if b = a mod n, then b is the unique integer satisfying:
(i) 0 ≤ b < n, and
(ii) (b-a) is an integer multiple of n
addition in modular arithmetic, i.e., if A, B are t-bit strings then A B is defined to equal (A+B
t
mod 2 )
subtraction in modular arithmetic, i.e., if A, B are t-bit strings then A B is defined to equal (A-B
t
mod 2 )
4 64-bit block ciphers
4.1 Introduction
In this clause, four 64-bit block ciphers are specified; TDEA (or ‘Triple DES’) in 104H104H104H4.2, MISTY1 in 105H105H105H4.3,
CAST-128 in 4.4, and HIGHT in 4.5.
Users authorized to access data that has been enciphered shall have the key that was used to encipher the
data in order to decipher it. The algorithm for any cipher in this clause is designed to encipher and decipher
blocks of data consisting of 64 bits under control of a 128- (or 192-) bit key. Deciphering shall be
accomplished using the same key as for enciphering.
4.2 TDEA
4.2.1 The Triple Data Encryption Algorithm
The Triple Data Encryption Algorithm (TDEA) is a symmetric cipher that can process data blocks of 64 bits,
using cipher keys with length of 128 (or 192) bits, of which 112 (or 168) bits can be chosen arbitrarily, and
the rest may be used for error detection. The TDEA is commonly known as Triple DES (Data Encryption
Standard).
A TDEA encryption/decryption operation is a compound operation of DES encryption and decryption
operations, where the DES algorithm is specified in Annex A. A TDEA key consists of three DES keys.
4.2.2 TDEA encryption/decryption
4.2.2.1 Encryption/decryption definitions
The TDEA is defined in terms of DES operations, where E is the DES encryption operation for the key K
K
and D is the DES decryption operation for the key K.
K
4.2.2.2 TDEA encryption
The transformation of a 64-bit block P into a 64-bit block C is defined as follows:
C = E (D (E (P))) .
K K K
3 2 1
© ISO/IEC 2010 — All rights reserved 3
4.2.2.3 TDEA decryption
The transformation of a 64-bit block C into a 64-bit block P is defined as follows:
P = D (E (D (C))) .
K K K
1 2 3
4.2.3 TDEA keying options
This part of ISO/IEC 18033 specifies the following keying options for TDEA. The TDEA key comprises the
triple (K , K , K ).
1 2 3
1. Keying Option 1: K , K and K are different DES keys;
1 2 3
2. Keying Option 2: K and K are different DES keys and K = K .
1 2 3 1
NOTE The option that K = K = K , the single-DES equivalent, is not recommended. Furthermore, the use of
1 2 3
keying option 1 is preferred over keying option 2 since it provides additional security at the same performance level
(see [3] for further details).
4.3 MISTY1
4.3.1 The MISTY1 algorithm
The MISTY1 algorithm is a symmetric block cipher that can process data blocks of 64 bits, using a cipher
key with length of 128 bits.
4.3.2 MISTY1 encryption
The encryption operation is as shown in Figure 1. The transformation of a 64-bit block P into a 64-bit block C
is defined as follows (KL, KO and KI are keys):
(1) P = L || R
0 0
KL = KL || KL || … || KL
1 2 10
KO = KO || KO || … || KO
1 2 8
KI = KI || KI || … || KI
1 2 8
(2) for i = 1, 3, …, 7 (increment in steps of 2 because the loop body consists of two rounds):
R = FL(L , KL )
i i-1 i
L = FL(R , KL ) ⊕ FO(R , KO , KI )
i i-1 i+1 i i i
L = R ⊕ FO(L , KO , KI )
i+1 i i i+1 i+1
R = L
i+1 i
for i = 9:
R = FL(L , KL )
i i-1 i
L = FL(R , KL )
i i-1 i+1
(3) C = L || R
9 9
4 © ISO/IEC 2010 — All rights reserved
4.3.3 MISTY1 decryption
The decryption operation is as shown in Figure 2, and is identical in operation to encryption apart from the
following two modifications.
-1
(1) All FL functions are replaced by their inverse functions FL .
(2) The order in which the subkeys are applied is reversed.
4.3.4 MISTY1 functions
4.3.4.1 MISTY1 function definitions
-1
The MISTY1 algorithm uses a number of functions, namely S , S , FI, FO, FL and FL , which are now
7 9
defined.
4.3.4.2 Function FL
The FL function is used in encryption only and is shown in Figure 3. The FL function is defined as follows (X
and Y are data, KL is a key):
(1) X = X || X , KL = KL || KL
32 L R i iL iR
(2) Y = (X ∧ KL ) ⊕ X
R L iL R
(3) Y = X ⊕ (Y ∨ KL )
L L R iR
(4) Y = Y || Y
32 L R
© ISO/IEC 2010 — All rights reserved 5
Plaintext Ciphertext
KL1 KL2 KL10 KL9
-1 -1
FL FL
FL FL
KO1,KI1 KO8,KI8
FO FO
KO2,KI2 KO7,KI7
FO FO
KL3 KL4 KL8 KL7
-1 -1
FL FL
FL FL
KO3,KI3 KO6,KI6
FO FO
KO4,KI4 KO5,KI5
FO FO
KL5 KL6 KL6 KL5
-1 -1
FL FL
FL FL
KO5,KI5 KO4,KI4
FO FO
KO6,KI6 KO3,KI3
FO FO
KL7 KL8 KL4 KL3
-1 -1
FL FL FL FL
KO7,KI7 KO2,KI2
FO FO
KO8,KI8 KO1,KI1
FO FO
KL9 KL10 KL2 KL1
-1 -1
FL FL
FL FL
Ciphertext Plaintext
Figure 1 — The Encryption Procedure Figure 2 — The Decryption Procedure
6 © ISO/IEC 2010 — All rights reserved
-1
4.3.4.3 Function FL
-1
The FL function, which is the inverse to the FL function, is used in decryption only and is shown in Figure 4.
-1
The FL function is defined as follows (X and Y are data, KL is a key):
(1) Y = Y || Y , KL = KL || KL
32 L R i iL iR
(2) X = Y ⊕ (Y ∨ KL )
L L R iR
(3) X = (X ∧ KL ) Y
⊕
R L iL R
(4) X = X || X
32 L R
4.3.4.4 Function FO
The FO function is used in encryption and decryption, and is shown in Figure 5. The FO function is defined
as follows (X and Y are data, KO and KI are keys):
(1) X = L || R
32 0 0
KO = KO || KO || KO || KO , KI = KI || KI || KI
i i1 i2 i3 i4 i i1 i2 i3
(2) for j = 1 to 3 :
R = FI(L ⊕ KO , KI ) ⊕ R
j j-1 ij ij j-1
L = R
j j-1
(3) Y = (L ⊕ KO ) || R
32 3 i4 3
4.3.4.5 Function FI
The FI function is used for encryption, decryption and the key schedule, and is shown in Figure 6, where
Extnd is the operation zero-extended from 7 bits to 9 bits by the concatenation of two bits on the left side,
and Trunc is the operation truncated by two bits on the left side. The FI function is defined as follows (X and
Y are data, KI is a key):
(1) X = L (9 bits) || R (7 bits), KI = KI || KI
16 0 0 ij ijL ijR
(2) R = S (L ) ⊕ Extnd(R )
1 9 0 0
(3) L =R
1 0
(4) R = S7(L ) ⊕ Trunc(R ) ⊕ KI
2 1 1 ijL
(5) L = R ⊕ KI
2 1 ijR
(6) R = S (L ) ⊕ Extnd(R )
3 9 2 2
(7) L = R
3 2
(8) Y = L || R
16 3 3
© ISO/IEC 2010 — All rights reserved 7
X32 Y32
X X Y Y
L R L R
KLiL KLiR
KLiR KLiL
YL YR XL XR
Y32 X32
-1
Figure 3 — The Function FL Figure 4 — The Function FL
X32 X16
L R L R
0 0 0 0
KO
i1
KI
i1 FI S9
Extnd
KOi2
KIi2 FI S
Trunc
KIijL KIijR
KOi3
KI FI S
i3 9
Extnd
KOi4
Y32 Y16
Figure 5 — The Function FO Figure 6 — The Function FI
8 © ISO/IEC 2010 — All rights reserved
4.3.4.6 Lookup Tables S and S
7 9
S is a bijective lookup table that accepts a 7-bit input and yields a 7-bit output. S is a bijective lookup table
7 9
that accepts a 9-bit input and yields a 9-bit output. Tables 2 and 3 define these lookup tables in a
hexadecimal form. S and S can be also described in a simple algebraic form over GF(2) as shown in
7 9
clause C.2.
For example, if the input to S is {53}, then the substitution value would be determined by the intersection of
the row with index ‘5’ and the column with index ‘3’ in Table 2. This would result in S having a value of {57}.
Table 2 — S
0 12 3 4 56789a bcd e f
0 1b 32 33 5a 3b 10 17 54 5b 1a 72 73 6b 2c 66 49
1 1f 24 13 6c 37 2e 3f 4a 5d 0f 40 56 25 51 1c 04
2 0b 46 20 0d 7b 35 44 42 2b 1e 41 14 4b 79 15 6f
3 0e 55 09 36 74 0c 67 53 28 0a 7e 38 02 07 60 29
4 19 12 65 2f 30 39 08 68 5f 78 2a 4c 64 45 75 3d
5 59 48 03 57 7c 4f 62 3c 1d 21 5e 27 6a 70 4d 3a
6 01 6d 6e 63 18 77 23 05 26 76 00 31 2d 7a 7f 61
7 50 22 11 06 47 16 52 4e 71 3e 69 43 34 5c 58 7d
Table 3 — S
0 1 2 3 4 5 6 7 8 9 a b c d e f
00 1c3 0cb 153 19f 1e3 0e9 0fb 035 181 0b9 117 1eb 133 009 02d 0d3
01 0c7 14a 037 07e 0eb 164 193 1d8 0a3 11e 055 02c 01d 1a2 163 118
02 14b 152 1d2 00f 02b 030 13a 0e5 111 138 18e 063 0e3 0c8 1f4 01b
03 001 09d 0f8 1a0 16d 1f3 01c 146 07d 0d1 082 1ea 183 12d 0f4 19e
04 1d3 0dd 1e2 128 1e0 0ec 059 091 011 12f 026 0dc 0b0 18c 10f 1f7
05 0e7 16c 0b6 0f9 0d8 151 101 14c 103 0b8 154 12b 1ae 017 071 00c
06 047 058 07f 1a4 134 129 084 15d 19d 1b2 1a3 048 07c 051 1ca 023
07 13d 1a7 165 03b 042 0da 192 0ce 0c1 06b 09f 1f1 12c 184 0fa 196
08 1e1 169 17d 031 180 10a 094 1da 186 13e 11c 060 175 1cf 067 119
09 065 068 099 150 008 007 17c 0b7 024 019 0de 127 0db 0e4 1a9 052
0a 109 090 19c 1c1 028 1b3 135 16a 176 0df 1e5 188 0c5 16e 1de 1b1
0b 0c3 1df 036 0ee 1ee 0f0 093 049 09a 1b6 069 081 125 00b 05e 0b4
0c 149 1c7 174 03e 13b 1b7 08e 1c6 0ae 010 095 1ef 04e 0f2 1fd 085
0d 0fd 0f6 0a0 16f 083 08a 156 09b 13c 107 167 098 1d0 1e9 003 1fe
0e 0bd 122 089 0d2 18f 012 033 06a 142 0ed 170 11b 0e2 14f 158 131
0f 147 05d 113 1cd 079 161 1a5 179 09e 1b4 0cc 022 132 01a 0e8 004
10 187 1ed 197 039 1bf 1d7 027 18b 0c6 09c 0d0 14e 06c 034 1f2 06e
11 0ca 025 0ba 191 0fe 013 106 02f 1ad 172 1db 0c0 10b 1d6 0f5 1ec
12 10d 076 114 1ab 075 10c 1e4 159 054 11f 04b 0c4 1be 0f7 029 0a4
13 00e 1f0 077 04d 17a 086 08b 0b3 171 0bf 10e 104 097 15b 160 168
© ISO/IEC 2010 — All rights reserved 9
0 1 2 3 4 5 6 7 8 9 a b c d e f
14 0d7 0bb 066 1ce 0fc 092 1c5 06f 016 04a 0a1 139 0af 0f1 190 00a
15 1aa 143 17b 056 18d 166 0d4 1fb 14d 194 19a 087 1f8 123 0a7 1b8
16 141 03c 1f9 140 02a 155 11a 1a1 198 0d5 126 1af 061 12e 157 1dc
17 072 18a 0aa 096 115 0ef 045 07b 08d 145 053 05f 178 0b2 02e 020
18 1d5 03f 1c9 1e7 1ac 044 038 014 0b1 16b 0ab 0b5 05a 182 1c8 1d4
19 018 177 064 0cf 06d 100 199 130 15a 005 120 1bb 1bd 0e0 04f 0d6
1a 13f 1c4 12a 015 006 0ff 19b 0a6 043 088 050 15f 1e8 121 073 17e
1b 0bc 0c2 0c9 173 189 1f5 074 1cc 1e6 1a8 195 01f 041 00d 1ba 032
1c 03d 1d1 080 0a8 057 1b9 162 148 0d9 105 062 07a 021 1ff 112 108
1d 1c0 0a9 11d 1b0 1a6 0cd 0f3 05c 102 05b 1d9 144 1f6 0ad 0a5 03a
1e 1cb 136 17f 046 0e1 01e 1dd 0e6 137 1fa 185 08c 08f 040 1b5 0be
1f 078 000 0ac 110 15e 124 002 1bc 0a2 0ea 070 1fc 116 15c 04c 1c2
4.3.5 MISTY1 key schedule
The key scheduling part accepts a 128-bit key K and yields another 128-bit subkey K’, as shown below. The
figure of the key scheduling part is described in Figure 7.
The key scheduling operation is thus defined as follows.
(1) K = K || K || K || K || K || K || K || K
1 2 3 4 5 6 7 8
(2) for i = 1 to 7:
K’ = FI(K , K )
i i i+1
(3) K’ = FI(K , K )
8 8 1
(4) K’ = K’ || K’ || K’ || K’ || K’ || K’ || K’ || K’
1 2 3 4 5 6 7 8
(5) KO = K , KO = K , KO = K , KO = K , KI = K’ , KI = K’ , KI = K’ , (i = 1,.,8)
i1 i i2 i+2 i3 i+7 i4 i+4 i1 i+5 i2 i+1 i3 i+3
KL = K (odd i) or K’ (even i), KL = K’ (odd i) or K (even i) (i = 1,.,10)
iL (i+1)/2 (i/2)+2 iR (i+1)/2+6 (i/2)+4
NOTE When the value of a suffix is larger than 8, subtract by 8.
K K K K K K K K
1 2 3 4 5 6 7 8
FI FI FI FI FI FI FI FI
K ’ K ’ K ’ K ’ K ’ K ’ K ’ K ’
1 2 3 4 5 6 7 8
Figure 7 — MISTY1 Key Scheduling
10 © ISO/IEC 2010 — All rights reserved
4.4 CAST-128
4.4.1 The CAST-128 algorithm
The CAST-128 algorithm is a symmetric block cipher that can process data blocks of 64 bits, using a cipher
key with length of 128 bits under 16 rounds.
NOTE The key length of the original version of CAST-128 is variable from 40 bits to 128 bits. This part of ISO/IEC
18033, however, specifies its use only with keys of 128 bits.
4.4.2 CAST-128 encryption
The transformation of a 64-bit block P into a 64-bit block C is defined as follows (Km and Kr are keys):
(1) P = L || R
0 0
(2) for i = 1 to 16:
L = R
i i-1
R = L ⊕ f(R ,Km,Kr )
i i-1 i-1 i i
(3) C = R || L
16 16
4.4.3 CAST-128 decryption
The decryption operation is identical to the encryption operation given above, except that the rounds (and
therefore the subkey pairs) are used in reverse order to compute (L , R ) from (R , L ).
0 0 16 16
4.4.4 CAST-128 functions
4.4.4.1 Pairs of Round Keys
CAST-128 uses a pair of subkeys per round: a 32-bit quantity Km is used as a "masking" key and a 5-bit
quantity Kr is used as a "rotation" key.
4.4.4.2 f-functions
Three different round functions are used in the encryption and decryption operations, depending on the
round number. The rounds are as follows (where "D" is the data input to the f function and "Ia" - "Id" are the
most significant byte through least significant byte of I, respectively).
Type 1: I = ((Km + D) <<< )
i Kri
f = ((S1[Ia] ⊕ S2[Ib]) - S3[Ic]) + S4[Id]
Type 2: I = ((Km ⊕ D) <<< )
i Kri
f = ((S1[Ia] - S2[Ib]) + S3[Ic]) ⊕ S4[Id]
Type 3: I = ((Km - D) <<< )
i Kri
f = ((S1[Ia] + S2[Ib]) ⊕ S3[Ic]) - S4[Id]
Rounds 1, 4, 7, 10, 13, and 16 use f function Type 1.
© ISO/IEC 2010 — All rights reserved 11
Rounds 2, 5, 8, 11, and 14 use f function Type 2.
Rounds 3, 6, 9, 12, and 15 use f function Type 3.
4.4.4.3 Substitution Boxes
4.4.4.3.1 The s-boxes S1 to S8
Eight substitution boxes are used: s-boxes S1, S2, S3, and S4 are round function s-boxes; S5, S6, S7, and
S8 are key schedule s- boxes.
4.4.4.3.2 S-Box S1
30fb40d4 9fa0ff0b 6beccd2f 3f258c7a 1e213f2f 9c004dd3 6003e540 cf9fc949
bfd4af27 88bbbdb5 e2034090 98d09675 6e63a0e0 15c361d2 c2e7661d 22d4ff8e
28683b6f c07fd059 ff2379c8 775f50e2 43c340d3 df2f8656 887ca41a a2d2bd2d
a1c9e0d6 346c4819 61b76d87 22540f2f 2abe32e1 aa54166b 22568e3a a2d341d0
66db40c8 a784392f 004dff2f 2db9d2de 97943fac 4a97c1d8 527644b7 b5f437a7
b82cbaef d751d159 6ff7f0ed 5a097a1f 827b68d0 90ecf52e 22b0c054 bc8e5935
4b6d2f7f 50bb64a2 d2664910 bee5812d b7332290 e93b159f b48ee411 4bff345d
fd45c240 ad31973f c4f6d02e 55fc8165 d5b1caad a1ac2dae a2d4b76d c19b0c50
882240f2 0c6e4f38 a4e4bfd7 4f5ba272 564c1d2f c59c5319 b949e354 b04669fe
b1b6ab8a c71358dd 6385c545 110f935d 57538ad5 6a390493 e63d37e0 2a54f6b3
3a787d5f 6276a0b5 19a6fcdf 7a42206a 29f9d4d5 f61b1891 bb72275e aa508167
38901091 c6b505eb 84c7cb8c 2ad75a0f 874a1427 a2d1936b 2ad286af aa56d291
d7894360 425c750d 93b39e26 187184c9 6c00b32d 73e2bb14 a0bebc3c 54623779
64459eab 3f328b82 7718cf82 59a2cea6 04ee002e 89fe78e6 3fab0950 325ff6c2
81383f05 6963c5c8 76cb5ad6 d49974c9 ca180dcf 380782d5 c7fa5cf6 8ac31511
35e79e13 47da91d0 f40f9086 a7e2419e 31366241 051ef495 aa573b04 4a805d8d
548300d0 00322a3c bf64cddf ba57a68e 75c6372b 50afd341 a7c13275 915a0bf5
6b54bfab 2b0b1426 ab4cc9d7 449ccd82 f7fbf265 ab85c5f3 1b55db94 aad4e324
cfa4bd3f 2deaa3e2 9e204d02 c8bd25ac eadf55b3 d5bd9e98 e31231b2 2ad5ad6c
954329de adbe4528 d8710f69 aa51c90f aa786bf6 22513f1e aa51a79b 2ad344cc
7b5a41f0 d37cfbad 1b069505 41ece491 b4c332e6 032268d4 c9600acc ce387e6d
bf6bb16c 6a70fb78 0d03d9c9 d4df39de e01063da 4736f464 5ad328d8 b347cc96
75bb0fc3 98511bfb 4ffbcc35 b58bcf6a e11f0abc bfc5fe4a a70aec10 ac39570a
3f04442f 6188b153 e0397a2e 5727cb79 9ceb418f 1cacd68d 2ad37c96 0175cb9d
c69dff09 c75b65f0 d9db40d8 ec0e7779 4744ead4 b11c3274 dd24cb9e 7e1c54bd
f01144f9 d2240eb1 9675b3fd a3ac3755 d47c27af 51c85f4d 56907596 a5bb15e6
580304f0 ca042cf1 011a37ea 8dbfaadb 35ba3e4a 3526ffa0 c37b4d09 bc306ed9
98a52666 5648f725 ff5e569d 0ced63d0 7c63b2cf 700b45e1 d5ea50f1 85a92872
af1fbda7 d4234870 a7870bf3 2d3b4d79 42e04198 0cd0ede7 26470db8 f881814c
474d6ad7 7c0c5e5c d1231959 381b7298 f5d2f4db ab838653 6e2f1e23 83719c9e
bd91e046 9a56456e dc39200c 20c8c571 962bda1c e1e696ff b141ab08 7cca89b9
1a69e783 02cc4843 a2f7c579 429ef47d 427b169c 5ac9f049 dd8f0f00 5c8165bf
12 © ISO/IEC 2010 — All rights reserved
4.4.4.3.3 S-Box S2
1f201094 ef0ba75b 69e3cf7e 393f4380 fe61cf7a eec5207a 55889c94 72fc0651
ada7ef79 4e1d7235 d55a63ce de0436ba 99c430ef 5f0c0794 18dcdb7d a1d6eff3
a0b52f7b 59e83605 ee15b094 e9ffd909 dc440086 ef944459 ba83ccb3 e0c3cdfb
d1da4181 3b092ab1 f997f1c1 a5e6cf7b 01420ddb e4e7ef5b 25a1ff41 e180f806
1fc41080 179bee7a d37ac6a9 fe5830a4 98de8b7f 77e83f4e 79929269 24fa9f7b
e113c85b acc40083 d7503525 f7ea615f 62143154 0d554b63 5d681121 c866c359
3d63cf73 cee234c0 d4d87e87 5c672b21 071f6181 39f7627f 361e3084 e4eb573b
602f64a4 d63acd9c 1bbc4635 9e81032d 2701f50c 99847ab4 a0e3df79 ba6cf38c
10843094 2537a95e f46f6ffe a1ff3b1f 208cfb6a 8f458c74 d9e0a227 4ec73a34
fc884f69 3e4de8df ef0e0088 3559648d 8a45388c 1d804366 721d9bfd a58684bb
e8256333 844e8212 128d8098 fed33fb4 ce280ae1 27e19ba5 d5a6c252 e49754bd
c5d655dd eb667064 77840b4d a1b6a801 84db26a9 e0b56714 21f043b7 e5d05860
54f03084 066ff472 a31aa153 dadc4755 b5625dbf 68561be6 83ca6b94 2d6ed23b
eccf01db a6d3d0ba b6803d5c af77a709 33b4a34c 397bc8d6 5ee22b95 5f0e5304
81ed6f61 20e74364 b45e1378 de18639b 881ca122 b96726d1 8049a7e8 22b7da7b
5e552d25 5272d237 79d2951c c60d894c 488cb402 1ba4fe5b a4b09f6b 1ca815cf
a20c3005 8871df63 b9de2fcb 0cc6c9e9 0beeff53 e3214517 b4542835 9f63293c
ee41e729 6e1d2d7c 50045286 1e6685f3 f33401c6 30a22c95 31a70850 60930f13
73f98417 a1269859 ec645c44 52c877a9 cdff33a6 a02b1741 7cbad9a2 2180036f
50d99c08 cb3f4861 c26bd765 64a3f6ab 80342676 25a75e7b e4e6d1fc 20c710e6
cdf0b680 17844d3b 31eef84d 7e0824e4 2ccb49eb 846a3bae 8ff77888 ee5d60f6
7af75673 2fdd5cdb a11631c1 30f66f43 b3faec54 157fd7fa ef8579cc d152de58
db2ffd5e 8f32ce19 306af97a 02f03ef8 99319ad5 c242fa0f a7e3ebb0 c68e4906
b8da230c 80823028 dcdef3c8 d35fb171 088a1bc8 bec0c560 61a3c9e8 bca8f54d
c72feffa 22822e99 82c570b4 d8d94e89 8b1c34bc 301e16e6 273be979 b0ffeaa6
61d9b8c6 00b24869 b7ffce3f 08dc283b 43daf65a f7e19798 7619b72f 8f1c9ba4
dc8637a0 16a7d3b1 9fc393b7 a7136eeb c6bcc63e 1a513742 ef6828bc 520365d6
2d6a77ab 3527ed4b 821fd216 095c6e2e db92f2fb 5eea29cb 145892f5 91584f7f
5483697b 2667a8cc 85196048 8c4bacea 833860d4 0d23e0f9 6c387e8a 0ae6d249
b284600c d835731d dcb1c647 ac4c56ea 3ebd81b3 230eabb0 6438bc87 f0b5b1fa
8f5ea2b3 fc184642 0a036b7a 4fb089bd 649da589 a345415e 5c038323 3e5d3bb9
43d79572 7e6dd07c 06dfdf1e 6c6cc4ef 7160a539 73bfbe70 83877605 4523ecf1
4.4.4.3.4 S-Box S3
8defc240 25fa5d9f eb903dbf e810c907 47607fff 369fe44b 8c1fc644 aececa90
beb1f9bf eefbcaea e8cf1950 51df07ae 920e8806 f0ad0548 e13c8d83 927010d5
11107d9f 07647db9 b2e3e4d4 3d4f285e b9afa820 fade82e0 a067268b 8272792e
553fb2c0 489ae22b d4ef9794 125e3fbc 21fffcee 825b1bfd 9255c5ed 1257a240
4e1a8302 bae07fff 528246e7 8e57140e 3373f7bf 8c9f8188 a6fc4ee8 c982b5a5
a8c01db7 579fc264 67094f31 f2bd3f5f 40fff7c1 1fb78dfc 8e6bd2c1 437be59b
99b03dbf b5dbc64b 638dc0e6 55819d99 a197c81c 4a012d6e c5884a28 ccc36f71
© ISO/IEC 2010 — All rights reserved 13
b843c213 6c0743f1 8309893c 0feddd5f 2f7fe850 d7c07f7e 02507fbf 5afb9a04
a747d2d0 1651192e af70bf3e 58c31380 5f98302e 727cc3c4 0a0fb402 0f7fef82
8c96fdad 5d2c2aae 8ee99a49 50da88b8 8427f4a0 1eac5790 796fb449 8252dc15
efbd7d9b a672597d ada840d8 45f54504 fa5d7403 e83ec305 4f91751a 925669c2
23efe941 a903f12e 60270df2 0276e4b6 94fd6574 927985b2 8276dbcb 02778176
f8af918d 4e48f79e 8f616ddf e29d840e 842f7d83 340ce5c8 96bbb682 93b4b148
ef303cab 984faf28 779faf9b 92dc560d 224d1e20 8437aa88 7d29dc96 2756d3dc
8b907cee b51fd240 e7c07ce3 e566b4a1 c3e9615e 3cf8209d 6094d1e3 cd9ca341
5c76460e 00ea983b d4d67881 fd47572c f76cedd9 bda8229c 127dadaa 438a074e
1f97c090 081bdb8a 93a07ebe b938ca15 97b03cff 3dc2c0f8 8d1ab2ec 64380e51
68cc7bfb d90f2788 12490181 5de5ffd4 dd7ef86a 76a2e214 b9a40368 925d958f
4b39fffa ba39aee9 a4ffd30b faf7933b 6d498623 193cbcfa 27627545 825cf47a
61bd8ba0 d11e42d1 cead04f4 127ea392 10428db7 8272a972 9270c4a8 127de50b
285ba1c8 3c62f44f 35c0eaa5 e805d231 428929fb b4fcdf82 4fb66a53 0e7dc15b
1f081fab 108618ae fcfd086d f9ff2889 694bcc11 236a5cae 12deca4d 2c3f8cc5
d2d02dfe f8ef5896 e4cf52da 95155b67 494a488c b9b6a80c 5c8f82bc 89d36b45
3a609437 ec00c9a9 44715253 0a874b49 d773bc40 7c34671c 02717ef6 4feb5536
a2d02fff d2bf60c4 d43f03c0 50b4ef6d 07478cd1 006e1888 a2e53f55 b9e6d4bc
a2048016 97573833 d7207d67 de0f8f3d 72f87b33 abcc4f33 7688c55d 7b00a6b0
947b0001 570075d2 f9bb88f8 8942019e 4264a5ff 856302e0 72dbd92b ee971b69
6ea22fde 5f08ae2b af7a616d e5c98767 cf1febd2 61efc8c2 f1ac2571 cc8239c2
67214cb8 b1e583d1 b7dc3e62 7f10bdce f90a5c38 0ff0443d 606e6dc6 60543a49
5727c148 2be98a1d 8ab41738 20e1be24 af96da0f 68458425 99833be5 600d457d
282f9350 8334b362 d91d1120 2b6d8da0 642b1e31 9c305a00 52bce688 1b03588a
f7baefd5 4142ed9c a4315c11 83323ec5 dfef4636 a133c501 e9d3531c ee353783
4.4.4.3.5 S-Box S4
9db30420 1fb6e9de a7be7bef d273a298 4a4f7bdb 64ad8c57 85510443 fa020ed1
7e287aff e60fb663 095f35a1 79ebf120 fd059d43 6497b7b1 f3641f63 241e4adf
28147f5f 4fa2b8cd c9430040 0cc32220 fdd30b30 c0a5374f 1d2d00d9 24147b15
ee4d111a 0fca5167 71ff904c 2d195ffe 1a05645f 0c13fefe 081b08ca 05170121
80530100 e83e5efe ac9af4f8 7fe72701 d2b8ee5f 06df4261 bb9e9b8a 7293ea25
ce84ffdf f5718801 3dd64b04 a26f263b 7ed48400 547eebe6 446d4ca0 6cf3d6f5
2649abdf aea0c7f5 36338cc1 503f7e93 d3772061 11b638e1 72500e03 f80eb2bb
abe0502e ec8d77de 57971e81 e14f6746 c9335400 6920318f 081dbb99 ffc304a5
4d351805 7f3d5ce3 a6c866c6 5d5bcca9 daec6fea 9f926f91 9f46222f 3991467d
a5bf6d8e 1143c44f 43958302 d0214eeb 022083b8 3fb6180c 18f8931e 281658e6
26486e3e 8bd78a70 7477e4c1 b506e07c f32d0a25 79098b02 e4eabb81 28123b23
69dead38 1574ca16 df871b62 211c40b7 a51a9ef9 0014377b 041e8ac8 09114003
bd59e4d2 e3d156d5 4fe876d5 2f91a340 557be8de 00eae4a7 0ce5c2ec 4db4bba6
e756bdff dd3369ac ec17b035 06572327 99afc8b0 56c8c391 6b65811c 5e146119
6e85cb75 be07c002 c2325577 893ff4ec 5bbfc92d d0ec3b25 b7801ab7 8d6d3b24
20c763ef c366a5fc 9c382880 0ace3205 aac9548a eca1d7c7 041afa32 1d16625a
6701902c 9b757a54 31d477f7 9126b031 36cc6fdb c70b8b46 d9e66a48 56e55a79
026a4ceb 52437eff 2f8f76b4 0df980a5 8674cde3 edda04eb 17a9be04 2c18f4df
14 © ISO/IEC 2010 — All rights reserved
b7747f9d ab2af7b4 efc34d20 2e096b7c 1741a254 e5b6a035 213d42f6 2c1c7c26
61c2f50f 6552daf9 d2c231f8 25130f69 d8167fa2 0418f2c8 001a96a6 0d1526ab
63315c21 5e0a72ec 49bafefd 187908d9 8d0dbd86 311170a7 3e9b640c cc3e10d7
d5cad3b6 0caec388 f73001e1 6c728aff 71eae2a1 1f9af36e cfcbd12f c1de8417
ac07be6b cb44a1d8 8b9b0f56 013988c3 b1c52fca b4be31cd d8782806 12a3a4e2
6f7de532 58fd7eb6 d01ee900 24adffc2 f4990fc5 9711aac5 001d7b95 82e5e7d2
109873f6 6.13E+05 c32d9521 ada121ff 29908415 7fbb977f af9eb3db 29c9ed2a
5ce2a465 a730f32c d0aa3fe8 8a5cc091 d49e2ce7 0ce454a9 d60acd86 015f1919
77079103 dea03af6 78a8565e dee356df 21f05cbe 8b75e387 b3c50651 b8a5c3ef
d8eeb6d2 e523be77 c2154529 2f69efdf afe67afb f470c4b2 f3e0eb5b d6cc9876
39e4460c 1fda8538 1987832f ca007367 a99144f8 296b299e 492fc295 9266beab
b5676e69 9bd3ddda df7e052f db25701c 1b5e51ee f65324e6 6afce36c 0316cc04
8644213e b7dc59d0
...


Questions, Comments and Discussion
Ask us and Technical Secretary will try to provide an answer. You can facilitate discussion about the standard in here.
Loading comments...