ISO/IEC 27018:2014
(Main)Information technology — Security techniques — Code of practice for protection of personally identifiable information (PII) in public clouds acting as PII processors
Information technology — Security techniques — Code of practice for protection of personally identifiable information (PII) in public clouds acting as PII processors
ISO/IEC 27018:2014 establishes commonly accepted control objectives, controls and guidelines for implementing measures to protect Personally Identifiable Information (PII) in accordance with the privacy principles in ISO/IEC 29100 for the public cloud computing environment. In particular, ISO/IEC 27018:2014 specifies guidelines based on ISO/IEC 27002, taking into consideration the regulatory requirements for the protection of PII which might be applicable within the context of the information security risk environment(s) of a provider of public cloud services. ISO/IEC 27018:2014 is applicable to all types and sizes of organizations, including public and private companies, government entities, and not-for-profit organizations, which provide information processing services as PII processors via cloud computing under contract to other organizations. The guidelines in ISO/IEC 27018:2014 might also be relevant to organizations acting as PII controllers; however, PII controllers can be subject to additional PII protection legislation, regulations and obligations, not applying to PII processors. ISO/IEC 27018:2014 is not intended to cover such additional obligations.
Technologies de l'information — Techniques de sécurité — Code de bonnes pratiques pour la protection des informations personnelles identifiables (PII) dans l'informatique en nuage public agissant comme processeur de PII
General Information
- Status
- Withdrawn
- Publication Date
- 28-Jul-2014
- Withdrawal Date
- 28-Jul-2014
- Drafting Committee
- ISO/IEC JTC 1/SC 27/WG 5 - Identity management and privacy technologies
- Current Stage
- 9599 - Withdrawal of International Standard
- Start Date
- 15-Jan-2019
- Completion Date
- 12-Feb-2026
Relations
- Effective Date
- 23-Apr-2020
Get Certified
Connect with accredited certification bodies for this standard

BSI Group
BSI (British Standards Institution) is the business standards company that helps organizations make excellence a habit.

Bureau Veritas
Bureau Veritas is a world leader in laboratory testing, inspection and certification services.

DNV
DNV is an independent assurance and risk management provider.
Sponsored listings
Frequently Asked Questions
ISO/IEC 27018:2014 is a standard published by the International Organization for Standardization (ISO). Its full title is "Information technology — Security techniques — Code of practice for protection of personally identifiable information (PII) in public clouds acting as PII processors". This standard covers: ISO/IEC 27018:2014 establishes commonly accepted control objectives, controls and guidelines for implementing measures to protect Personally Identifiable Information (PII) in accordance with the privacy principles in ISO/IEC 29100 for the public cloud computing environment. In particular, ISO/IEC 27018:2014 specifies guidelines based on ISO/IEC 27002, taking into consideration the regulatory requirements for the protection of PII which might be applicable within the context of the information security risk environment(s) of a provider of public cloud services. ISO/IEC 27018:2014 is applicable to all types and sizes of organizations, including public and private companies, government entities, and not-for-profit organizations, which provide information processing services as PII processors via cloud computing under contract to other organizations. The guidelines in ISO/IEC 27018:2014 might also be relevant to organizations acting as PII controllers; however, PII controllers can be subject to additional PII protection legislation, regulations and obligations, not applying to PII processors. ISO/IEC 27018:2014 is not intended to cover such additional obligations.
ISO/IEC 27018:2014 establishes commonly accepted control objectives, controls and guidelines for implementing measures to protect Personally Identifiable Information (PII) in accordance with the privacy principles in ISO/IEC 29100 for the public cloud computing environment. In particular, ISO/IEC 27018:2014 specifies guidelines based on ISO/IEC 27002, taking into consideration the regulatory requirements for the protection of PII which might be applicable within the context of the information security risk environment(s) of a provider of public cloud services. ISO/IEC 27018:2014 is applicable to all types and sizes of organizations, including public and private companies, government entities, and not-for-profit organizations, which provide information processing services as PII processors via cloud computing under contract to other organizations. The guidelines in ISO/IEC 27018:2014 might also be relevant to organizations acting as PII controllers; however, PII controllers can be subject to additional PII protection legislation, regulations and obligations, not applying to PII processors. ISO/IEC 27018:2014 is not intended to cover such additional obligations.
ISO/IEC 27018:2014 is classified under the following ICS (International Classification for Standards) categories: 35.030 - IT Security; 35.040 - Information coding. The ICS classification helps identify the subject area and facilitates finding related standards.
ISO/IEC 27018:2014 has the following relationships with other standards: It is inter standard links to ISO/IEC 27018:2019. Understanding these relationships helps ensure you are using the most current and applicable version of the standard.
ISO/IEC 27018:2014 is available in PDF format for immediate download after purchase. The document can be added to your cart and obtained through the secure checkout process. Digital delivery ensures instant access to the complete standard document.
Standards Content (Sample)
INTERNATIONAL ISO/IEC
STANDARD 27018
First edition
2014-08-01
Information technology — Security
techniques — Code of practice for
protection of personally identifiable
information (PII) in public clouds
acting as PII processors
Technologies de l’information — Techniques de sécurité — Code de
bonnes pratiques pour la protection des informations personnelles
identifiables (PII) dans l’informatique en nuage public agissant
comme processeur de PII
Reference number
©
ISO/IEC 2014
© ISO/IEC 2014
All rights reserved. Unless otherwise specified, no part of this publication may be reproduced or utilized otherwise in any form
or by any means, electronic or mechanical, including photocopying, or posting on the internet or an intranet, without prior
written permission. Permission can be requested from either ISO at the address below or ISO’s member body in the country of
the requester.
ISO copyright office
Case postale 56 • CH-1211 Geneva 20
Tel. + 41 22 749 01 11
Fax + 41 22 749 09 47
E-mail copyright@iso.org
Web www.iso.org
Published in Switzerland
ii © ISO/IEC 2014 – All rights reserved
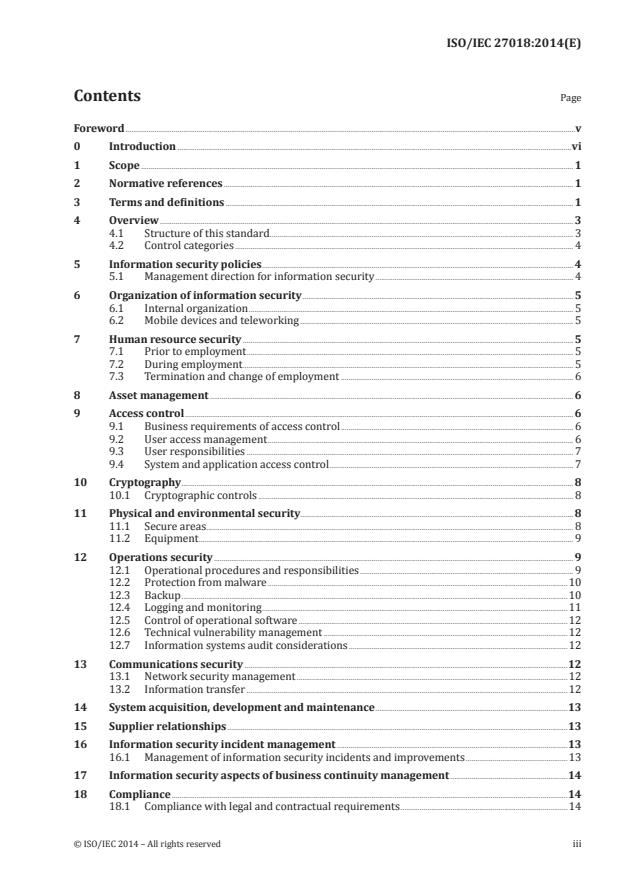
Contents Page
Foreword .v
0 Introduction .vi
1 Scope . 1
2 Normative references . 1
3 Terms and definitions . 1
4 Overview . 3
4.1 Structure of this standard . 3
4.2 Control categories . 4
5 Information security policies . 4
5.1 Management direction for information security . 4
6 Organization of information security . 5
6.1 Internal organization . 5
6.2 Mobile devices and teleworking . 5
7 Human resource security . 5
7.1 Prior to employment . 5
7.2 During employment . 5
7.3 Termination and change of employment . 6
8 Asset management . 6
9 Access control . 6
9.1 Business requirements of access control . 6
9.2 User access management . 6
9.3 User responsibilities . 7
9.4 System and application access control . 7
10 Cryptography . 8
10.1 Cryptographic controls . 8
11 Physical and environmental security . 8
11.1 Secure areas . 8
11.2 Equipment . 9
12 Operations security . 9
12.1 Operational procedures and responsibilities . 9
12.2 Protection from malware .10
12.3 Backup .10
12.4 Logging and monitoring .11
12.5 Control of operational software .12
12.6 Technical vulnerability management .12
12.7 Information systems audit considerations .12
13 Communications security .12
13.1 Network security management .12
13.2 Information transfer .12
14 System acquisition, development and maintenance .13
15 Supplier relationships .13
16 Information security incident management .13
16.1 Management of information security incidents and improvements .13
17 Information security aspects of business continuity management .14
18 Compliance .14
18.1 Compliance with legal and contractual requirements .14
© ISO/IEC 2014 – All rights reserved iii
18.2 Information security reviews .14
Annex A (normative) Public cloud PII processor extended control set for PII protection .15
Bibliography .23
iv © ISO/IEC 2014 – All rights reserved
Foreword
ISO (the International Organization for Standardization) and IEC (the International Electrotechnical
Commission) form the specialized system for worldwide standardization. National bodies that are
members of ISO or IEC participate in the development of International Standards through technical
committees established by the respective organization to deal with particular fields of technical
activity. ISO and IEC technical committees collaborate in fields of mutual interest. Other international
organizations, governmental and non-governmental, in liaison with ISO and IEC, also take part in the
work. In the field of information technology, ISO and IEC have established a joint technical committee,
ISO/IEC JTC 1.
The procedures used to develop this document and those intended for its further maintenance are
described in the ISO/IEC Directives, Part 1. In particular the different approval criteria needed for
the different types of document should be noted. This document was drafted in accordance with the
editorial rules of the ISO/IEC Directives, Part 2 (see www.iso.org/directives).
Attention is drawn to the possibility that some of the elements of this document may be the subject
of patent rights. ISO and IEC shall not be held responsible for identifying any or all such patent rights.
Details of any patent rights identified during the development of the document will be in the Introduction
and/or on the ISO list of patent declarations received (see www.iso.org/patents).
Any trade name used in this document is information given for the convenience of users and does not
constitute an endorsement.
For an explanation on the meaning of ISO specific terms and expressions related to conformity
assessment, as well as information about ISO’s adherence to the WTO principles in the Technical Barriers
to Trade (TBT) see the following URL: Foreword - Supplementary information
The committee responsible for this document is ISO/IEC JTC 1, Information technology, Subcommittee
SC 27, IT Security techniques.
© ISO/IEC 2014 – All rights reserved v
0 Introduction
0.1 Background and context
Cloud service providers who process Personally Identifiable Information (PII) under contract to their
customers have to operate their services in ways that allow both parties to meet the requirements of
applicable legislation and regulations covering the protection of PII. The requirements and the way in
which the requirements are divided between the cloud service provider and its customers vary according
to legal jurisdiction, and according to the terms of the contract between the cloud service provider
and the customer. Legislation which governs how PII is allowed to be processed (i.e. collected, used,
transferred and disposed of) is sometimes referred to as data protection legislation; PII is sometimes
referred to as personal data or personal information. The obligations falling on a PII processor vary
from jurisdiction to jurisdiction, which makes it challenging for businesses providing cloud computing
services to operate multinationally.
A public cloud service provider is a ‘PII processor’ when it processes PII for and according to the instructions
of a cloud service customer. The cloud service customer, who has the contractual relationship with the
public cloud PII processor, can range from a natural person, a ‘PII principal’, processing his or her own
PII in the cloud, to an organization, a ‘PII controller’, processing PII relating to many PII principals. The
cloud service customer might authorize one or more cloud service users associated with it to use the
services made available to it under its contract with the public cloud PII processor. Note that the cloud
service customer has authority over the processing and use of the data. A cloud service customer who is
also a PII controller might be subject to a wider set of obligations governing the protection of PII than the
public cloud PII processor. Maintaining the distinction between PII controller and PII processor relies
on the public cloud PII processor having no data processing objectives other than those set by the cloud
service customer with respect to the PII it processes and the operations necessary to achieve the cloud
service customer’s objectives.
NOTE Where the public cloud PII processor is processing cloud service customer account data, it might be
acting as a PII controller for this purpose. This International Standard does not cover such activity.
The intention of this International Standard, when used in conjunction with the information security
objectives and controls in ISO/IEC 27002, is to create a common set of security categories and controls
that can be implemented by a public cloud computing service provider acting as a PII processor. It has
the following objectives.
— To help the public cloud service provider to comply with applicable obligations when acting as a PII
processor, whether such obligations fall on the PII processor directly or through contract.
— To enable the public cloud PII processor to be transparent in relevant matters so that cloud service
customers can select well-governed cloud-based PII processing services.
— To assist the cloud service customer and the public cloud PII processor in entering into a contractual
agreement.
— To provide cloud service customers with a mechanism for exercising audit and compliance rights
and responsibilities in cases where individual cloud service customer audits of data hosted in a
multi-party, virtualized server (cloud) environment might be impractical technically and might
increase risks to those physical and logical network security controls in place.
This International Standard does not replace applicable legislation and regulations, but can assist by
providing a common compliance framework for public cloud service providers, in particular those that
operate in a multinational market.
0.2 PII protection controls for public cloud computing services
This International Standard is designed for organizations to use as a reference for selecting PII
protection controls within the process of implementing a cloud computing information security
management system based on ISO/IEC 27001, or as a guidance document for implementing commonly
accepted PII protection controls for organizations acting as public cloud PII processors. In particular,
vi © ISO/IEC 2014 – All rights reserved
this International Standard has been based on ISO/IEC 27002, taking into consideration the specific
risk environment(s) arising from those PII protection requirements which might apply to public cloud
computing service providers acting as PII processors.
Typically an organization implementing ISO/IEC 27001 is protecting its own information assets.
However, in the context of PII protection requirements for a public cloud service provider acting as a
PII processor, the organization is protecting the information assets entrusted to it by its customers.
Implementation of the controls of ISO/IEC 27002 by the public cloud PII processor is both suitable
for this purpose and necessary. This International Standard augments the ISO/IEC 27002 controls to
accommodate the distributed nature of the risk and the existence of a contractual relationship between
the cloud service customer and the public cloud PII processor. This International Standard augments
ISO/IEC 27002 in two ways:
— implementation guidance applicable to public cloud PII protection is provided for certain of the
existing ISO/IEC 27002 controls, and
— Annex A provides a set of additional controls and associated guidance intended to address public
cloud PII protection requirements not addressed by the existing ISO/IEC 27002 control set.
Most of the controls and guidance in this International Standard will also apply to a PII controller.
However, the PII controller will, in most cases, be subject to additional obligations not specified here.
0.3 PII protection requirements
It is essential that an organization identifies its requirements for the protection of PII. There are three
main sources of requirement, as given below.
a) Legal, Statutory, Regulatory and Contractual Requirements: One source is the legal, statutory,
regulatory and contractual requirements and obligations that an organization, its trading partners,
contractors and service providers have to satisfy, and their socio-cultural responsibilities and
operating environment. It should be noted that legislation, regulations and contractual commitments
made by the PII processor might mandate the selection of particular controls and might also
necessitate specific criteria for implementing those controls. These requirements can vary from
one jurisdiction to another.
b) Risks: Another source is derived from assessing risks to the organization associated with PII, taking
into account the organization’s overall business strategy and objectives. Through a risk assessment,
threats are identified, vulnerability to and likelihood of occurrence is evaluated and potential impact
is estimated. ISO/IEC 27005 provides information security risk management guidance, including
advice on risk assessment, risk acceptance, risk communication, risk monitoring and risk review.
ISO/IEC 29134 provides guidance on privacy impact assessment.
c) Corporate policies: While many aspects covered by a corporate policy are derived from legal and
socio-cultural obligations, an organization might also choose voluntarily to go beyond the criteria
that are derived from the requirements of a).
0.4 Selecting and implementing controls in a cloud computing environment
Controls can be selected from this International Standard (which includes by reference the controls
from ISO/IEC 27002, creating a combined reference control set for the sector or application defined
by the scope). If required, controls can also be selected from other control sets, or new controls can be
designed to meet specific needs as appropriate.
NOTE A PII processing service provided by a public cloud PII processor could be considered as an application
of cloud computing rather than as a sector in itself. Nevertheless, the term ‘sector-specific’ is used in this
International Standard, as this is the conventional term used within other standards in the ISO/IEC 27000 series.
The selection of controls is dependent upon organizational decisions based on the criteria for risk
acceptance, risk treatment options, and the general risk management approach applied to the organization
and, through contractual agreements, its customers and suppliers, and will also be subject to all relevant
© ISO/IEC 2014 – All rights reserved vii
national and international legislation and regulations. Where controls from this International Standard
are not selected, this needs to be documented with justification for the omission.
Further, the selection and implementation of controls is dependent upon the public cloud provider’s
actual role in the context of the whole cloud computing reference architecture (see ISO/IEC 17789). Many
different organizations can be involved in providing infrastructure and application services in a cloud
computing environment. In some circumstances, selected controls can be unique to a particular service
category of the cloud computing reference architecture. In other instances, there can be shared roles
in implementing security controls. Contractual agreements need to clearly specify the PII protection
responsibilities of all organizations involved in providing or using the cloud services, including the
public cloud PII processor, its sub-contractors and the cloud service customer.
The controls in this International Standard can be considered as guiding principles and applicable for
most organizations. They are explained in more detail below along with implementation guidance.
Implementation can be made simpler if requirements for the protection of PII have been considered
in the design of the public cloud PII processor’s information system, services and operations. Such
consideration is an element of the concept that is often called “Privacy by Design”. The bibliography lists
relevant documents such as ISO/IEC 29101.
0.5 Developing additional guidelines
This International Standard can be regarded as a starting point for developing PII protection guidelines.
It is possible that not all of the controls and guidance in this code of practice will be applicable.
Furthermore, additional controls and guidelines not included in this International Standard might be
required. When documents are developed containing additional guidelines or controls, it might be
useful to include cross-references to clauses in this International Standard where applicable to facilitate
compliance checking by auditors and business partners.
0.6 Lifecycle considerations
PII has a natural lifecycle, from creation and origination through storage, processing, use and transmission
to its eventual destruction or decay. The risks to PII can vary during its lifetime but protection of PII
remains important to some extent at all stages.
PII protection requirements need to be taken into account as existing and new information systems are
managed through their lifecycle.
viii © ISO/IEC 2014 – All rights reserved
INTERNATIONAL STANDARD ISO/IEC 27018:2014(E)
Information technology — Security techniques — Code
of practice for protection of personally identifiable
information (PII) in public clouds acting as PII processors
1 Scope
This International Standard establishes commonly accepted control objectives, controls and guidelines
for implementing measures to protect Personally Identifiable Information (PII) in accordance with the
privacy principles in ISO/IEC 29100 for the public cloud computing environment.
In particular, this International Standard specifies guidelines based on ISO/IEC 27002, taking into
consideration the regulatory requirements for the protection of PII which might be applicable within
the context of the information security risk environment(s) of a provider of public cloud services.
This International Standard is applicable to all types and sizes of organizations, including public and
private companies, government entities and not-for-profit organizations, which provide information
processing services as PII processors via cloud computing under contract to other organizations.
The guidelines in this International Standard might also be relevant to organizations acting as PII
controllers; however, PII controllers might be subject to additional PII protection legislation, regulations
and obligations, not applying to PII processors. This International Standard is not intended to cover such
additional obligations.
2 Normative references
The following documents, in whole or in part, are normatively referenced in this document and are
indispensable for its application. For dated references, only the edition cited applies. For undated
references, the latest edition of the referenced document (including any amendments) applies.
ISO/IEC 17788 | Rec. ITU-T Y.3500, Information technology — Cloud computing — Overview and
1)
vocabulary
ISO/IEC 27000:2014, Information technology — Security techniques — Information security management
systems — Overview and vocabulary
ISO/IEC 27001:2013, Information technology — Security techniques — Information security management
systems — Requirements
ISO/IEC 27002:2013, Information technology — Security techniques — Code of practice for information
security controls
ISO/IEC 29100:2011, Information technology — Security techniques — Privacy framework
3 Terms and definitions
For the purposes of this document, the terms and definitions given in ISO/IEC 17788, ISO/IEC 27000 and
the following apply.
1) To be published.
© ISO/IEC 2014 – All rights reserved 1
3.1
data breach
compromise of security that leads to the accidental or unlawful destruction, loss, alteration, unauthorized
disclosure of, or access to protected data transmitted, stored or otherwise processed
2)
[SOURCE: ISO/IEC 27040:— , 3.7]
3.2
personally identifiable information
PII
any information that (a) can be used to identify the PII principal to whom such information relates, or
(b) is or might be directly or indirectly linked to a PII principal
Note 1 to entry: To determine whether a PII principal is identifiable, account should be taken of all the means
which can reasonably be used by the privacy stakeholder holding the data, or by any other party, to identify that
natural person.
[SOURCE: ISO/IEC 29100:2011, 2.9]
Note 2 to entry: This definition is included to define the term PII as used in this International Standard. A public
cloud PII processor is typically not in a position to know explicitly whether information it processes falls into any
specified category unless this is made transparent by the cloud service customer.
3.3
PII controller
privacy stakeholder (or privacy stakeholders) that determines the purposes and means for processing
personally identifiable information (PII) other than natural persons who use data for personal purposes
Note 1 to entry: A PII controller sometimes instructs others (e.g. PII processors) to process PII on its behalf while
the responsibility for the processing remains with the PII controller.
[SOURCE: ISO/IEC 29100:2011, 2.10]
3.4
PII principal
natural person to whom the personally identifiable information (PII) relates
Note 1 to entry: Depending on the jurisdiction and the particular PII protection and privacy legislation, the
synonym “data subject” can also be used instead of the term “PII principal”.
[SOURCE: ISO/IEC 29100:2011, 2.11]
3.5
PII processor
privacy stakeholder that processes personally identifiable information (PII) on behalf of and in
accordance with the instructions of a PII controller
[SOURCE: ISO/IEC 29100:2011, 2.12]
3.6
processing of PII
operation or set of operations performed upon personally identifiable information (PII)
Note 1 to entry: Examples of processing operations of PII include, but are not limited to, the collection, storage,
alteration, retrieval, consultation, disclosure, anonymization, pseudonymization, dissemination or otherwise
making available, deletion or destruction of PII.
[SOURCE: ISO/IEC 29100:2011, 2.23]
2) To be published.
2 © ISO/IEC 2014 – All rights reserved
3.7
public cloud service provider
party which makes cloud services available according to the public cloud model
4 Overview
4.1 Structure of this standard
This International Standard has a structure similar to that of ISO/IEC 27002. In cases where objectives
and controls specified in ISO/IEC 27002 are applicable without a need for any additional information,
only a reference is provided to ISO/IEC 27002. Additional controls and associated implementation
guidance applicable to PII protection for cloud computing service providers are described in Annex A
(normative).
In cases where controls need additional guidance applicable to PII protection for cloud computing
service providers, this is given under the heading Public cloud PII protection implementation guidance. In
some cases, further relevant information that enhances the additional guidance is provided under the
heading Other information for public cloud PII protection.
As shown in Table 1, such sector-specific guidance and information is included in the categories defined
in ISO/IEC 27002. Clause numbers, which have been aligned with the corresponding clause numbers in
ISO/IEC 27002, are as indicated in the table.
Table 1 — Location of sector-specific guidance and other information for implementing controls
in ISO/IEC 27002
Clause Title Remarks
number
5 Information security policies Sector-specific implementation guidance and other informa-
tion is provided.
6 Organization of information security Sector-specific implementation guidance is provided.
7 Human resource security Sector-specific implementation guidance and other informa-
tion is provided.
8 Asset management No additional sector-specific implementation guidance or
other information is provided.
9 Access control Sector-specific implementation guidance is provided,
together with a cross-reference to control(s) in Annex A.
10 Cryptography Sector-specific implementation guidance is provided.
11 Physical and environmental security Sector-specific implementation guidance is provided,
together with a cross-reference to control(s) in Annex A.
12 Operations security Sector-specific implementation guidance is provided.
13 Communications security Sector-specific implementation guidance is provided,
together with a cross-reference to control(s) in Annex A.
14 System acquisition, development and No additional sector-specific implementation guidance or
maintenance other information is provided.
15 Supplier relationships No additional sector-specific implementation guidance or
other information is provided.
16 Information security incident man- Sector-specific implementation guidance is provided.
agement
17 Information security aspects of busi- No additional sector-specific implementation guidance or
ness continuity management other information is provided.
18 Compliance Sector-specific implementation guidance is provided,
together with a cross-reference to control(s) in Annex A.
© ISO/IEC 2014 – All rights reserved 3
4.2 Control categories
In line with ISO/IEC 27002, each main control category contains:
a) a control objective stating what is to be achieved; and
b) one or more controls that can be applied to achieve the control objective.
Control descriptions are structured as follows:
Control
Defines the specific control statement to satisfy the control objective.
Public cloud PII protection implementation guidance
Provides more detailed information to support the implementation of the control and meeting the
control objectives. The guidance may not be entirely suitable or sufficient in all situations, and may
not fulfil the organization’s specific control requirements. Alternative or additional controls, or other
forms of risk treatment (avoiding, transferring or accepting risks), may therefore be appropriate.
Other information for public cloud PII protection
Provides further information that may need to be considered, such as legal considerations and
references to other standards.
5 Information security policies
5.1 Management direction for information security
The objective specified in ISO/IEC 27002:2013, 5.1 applies.
5.1.1 Policies for information security
Control 5.1.1 and the associated implementation guidance and other information specified in
ISO/IEC 27002 apply. The following sector-specific guidance also applies.
Public cloud PII protection implementation guidance
The information security policies should be augmented by a statement concerning support for and
commitment to achieving compliance with applicable PII protection legislation and the contractual
terms agreed between the public cloud PII processor and its clients (cloud service customers).
Contractual agreements should clearly allocate responsibilities between the public cloud PII processor,
its sub-contractors and the cloud service customer, taking into account the type of cloud service in
question (e.g. a service of an IaaS, PaaS or SaaS category of the cloud computing reference architecture).
For example, the allocation of responsibility for application layer controls may differ depending on
whether the public cloud PII processor is providing a SaaS service or rather is providing a PaaS or IaaS
service upon which the cloud service customer can build or layer its own applications.
Other information for public cloud PII protection
In some jurisdictions the public cloud PII processor is directly subject to PII protection legislation.
Elsewhere, PII protection legislation applies to the PII controller only.
A mechanism to ensure the public cloud PII processor is obliged to support and manage compliance is
provided by the contract between the cloud service customer and the public cloud PII processor. The
contract could call for independently audited compliance, acceptable to the cloud service customer, e.g.
via the implementation of the relevant controls in this International Standard and in ISO/IEC 27002.
4 © ISO/IEC 2014 – All rights reserved
5.1.2 Review of the policies for information security
Control 5.1.2 and the associated implementation guidance specified in ISO/IEC 27002 apply.
6 Organization of information security
6.1 Internal organization
The objective specified in ISO/IEC 27002:2013, 6.1 applies.
6.1.1 Information security roles and responsibilities
Control 6.1.1 and the associated implementation guidance and other information specified in
ISO/IEC 27002 apply. The following sector-specific guidance also applies.
Public cloud PII protection implementation guidance
The public cloud PII processor should designate a point of contact for use by the cloud service customer
regarding the processing of PII under the contract.
6.1.2 Segregation of duties
Control 6.1.2 and the associated implementation guidance and other information specified in
ISO/IEC 27002 apply.
6.1.3 Contact with authorities
Control 6.1.3 and the associated implementation guidance and other information specified in
ISO/IEC 27002 apply.
6.1.4 Contact with special interest groups
Control 6.1.4 and the associated implementation guidance and other information specified in
ISO/IEC 27002 apply.
6.1.5 Information security in project management
Control 6.1.5 and the associated implementation guidance specified in ISO/IEC 27002 apply.
6.2 Mobile devices and teleworking
The objective specified in, and the contents of, ISO/IEC 27002:2013, 6.2 apply.
7 Human resource security
7.1 Prior to employment
The objective specified in, and the contents of, ISO/IEC 27002:2013, 7.1 apply.
7.2 During employment
The objective specified in ISO/IEC 27002:2013, 7.2 applies.
© ISO/IEC 2014 – All rights reserved 5
7.2.1 Management responsibilities
Control 7.2.1 and the associated implementation guidance and other information specified in
ISO/IEC 27002 apply.
7.2.2 Information security awareness, education and training
Control 7.2.2 and the associated implementation guidance and other information specified in
ISO/IEC 27002 apply. The following sector-specific guidance also applies.
Public cloud PII protection implementation guidance
Measures should be put in place to make relevant staff aware of the possible consequences on the
public cloud PII processor (e.g. legal consequences, loss of business and brand or reputational damage),
on the staff member (e.g. disciplinary consequences) and on the PII principal (e.g. physical, material
and emotional consequences) of breaching privacy or security rules and procedures, especially those
addressing the handling of PII.
Other information for public cloud PII protection
In some jurisdictions, the public cloud PII processor may be subject to legal sanctions, including
substantial fines directly from the local PII protection authority. In other jurisdictions the use of
International Standards such as this in setting up the contract between the public cloud PII processor
and the cloud service customer should help establish a basis for contractual sanctions for a breach of
security rules and procedures.
7.2.3 Disciplinary process
Control 7.2.3 and the associated implementation guidance and other information specified in
ISO/IEC 27002 apply.
7.3 Termination and change of employment
The objective specified in, and the contents of, ISO/IEC 27002:2013, 7.3 apply.
8 Asset management
The objectives specified in, and the contents of, ISO/IEC 27002:2013, Clause 8 apply.
9 Access control
9.1 Business requirements of access control
The objective specified in, and the contents of, ISO/IEC 27002:2013, 9.1 apply.
9.2 User access management
The objective specified in ISO/IEC 27002:2013, 9.2 applies. The following sector-specific guidance also
applies to the implementation of all of the controls under this subclause (9.2).
Public cloud PII protection implementation guidance
In the context of the service categories of the cloud computing reference architecture, the cloud service
customer may be responsible for some or all aspects of access management for cloud service users under
its control. Where appropriate, the public cloud PII processor should enable the cloud service customer
to manage access by cloud service users under the cloud service customer’s control, such as by providing
administrative rights to manage or terminate access.
6 © ISO/IEC 2014 – All rights reserved
9.2.1 User registration and de-registration
Control 9.2.1 and the associated implementation guidance and other information specified in
ISO/IEC 27002 apply. The following sector-specific guidance also applies.
Public cloud PII protection implementation guidance
Procedures for user registration and de-registration should address the situation where user access
control is compromised, such as the corruption or compromise of passwords or other user registration
data (e.g. as a result of inadvertent disclosure).
NOTE Individual jurisdictions may impose specific requirements regarding the frequency of checks for
unused authentication credentials. Organizations operating in these jurisdictions should ensure that they comply
with these requirements.
9.2.2 User access provisioning
Control 9.2.2 and the associated implementation guidance and other information specified in
ISO/IEC 27002 apply.
9.2.3 Management of privileged access rights
Control 9.2.3 and the associated implementation guidance and other information specified in
ISO/IEC 27002 apply.
9.2.4 Management of secret authentication information of users
Control 9.2.4 and the associated implementation guidance and other information specified in
ISO/IEC 27002 apply.
9.2.5 Review of user access rights
Control 9.2.5 and the associated implementation guidance and other information specified in
ISO/IEC 27002 apply.
9.2.6 Removal or adjustment of access rights
Control 9.2.6 and the associated implementation guidance and other information specified in
ISO/IEC 27002 apply.
9.3 User responsibilities
The objective specified in ISO/IEC 27002:2013, 9.3 applies.
9.3.1 Use of secret authentication information
Control 9.3.1 and the associated implementation guidance specified in ISO/IEC 27002 apply.
9.4 System and application access control
The objective specified in ISO/IEC 27002:2013, 9.4 applies.
9.4.1 Information access restriction
Control 9.4.1 and the associated implementation guidance specified in ISO/IEC 27002 apply.
NOTE Additional controls and guidance relevant to information access restriction can be found in A.10.13.
© ISO/IEC 2014 – All rights reserved 7
9.4.2 Secure log-on procedures
Control 9.4.2 and the associated implementation guidance and other information specified in
ISO/IEC 27002 apply. The following sector-specific guidance also applies.
Public cloud PII protection implementation guidance
Where required, the public cloud PII processor should provide secure log-on procedures for any accounts
requested by the cloud service customer for cloud service users under its control.
9.4.3 Password management system
Control 9.4.3 and the associated implementation guidance and other information specified in
ISO/IEC 27002 apply.
9.4.4 Use of privileged utility programs
Control 9.4.4 and the associated implementation guidance and other information specified in
ISO/IEC 27002 apply.
9.4.5 Access control to program source code
Control 9.4.5 and the associated implementation guidance and other information specified in
ISO/IEC 27002 apply.
10 Cryptography
10.1 Cryptographic controls
The objective specified in ISO/IEC 27002:2013, 10.1 applies.
10.1.1 Policy on the use of cryptographic controls
Control 10.1.1 and the associated implementation guidance and other information specified in
ISO/IEC 27002 apply. The following sector-specific guidance also applies.
Public cloud PII protection implementation guidance
The public cloud PII processor should provide information to the cloud service customer regarding the
circumstances in which it uses cryptography to protect the PII it processes. The public cloud PII processor
should also provide information to the cloud service customer about any capabilities it provides that
may assist the cloud service customer in applying its own cryptographic protection.
NOTE In some jurisdictions it may be required to apply cryptography to protect particular kinds of PII, such
as health data concerning a PII principal, resident registration numbers, passport numbers and driver’s licence
numbers.
10.1.2 Key management
Control 10.1.2 and the associated implementation guidance and other information specified in
ISO/IEC 27002 apply.
11 Physical and environmental security
11.1 Secure areas
The objective specified in, and the contents of, ISO/IEC 27002:2013, 11.1 apply.
8 © ISO/IEC 2014 – All rights reserved
11.2 Equipment
The objective specified in ISO/IEC 27002
...

Questions, Comments and Discussion
Ask us and Technical Secretary will try to provide an answer. You can facilitate discussion about the standard in here.
Loading comments...