ISO/IEC 15944-8:2012
(Main)Information technology — Business operational view — Part 8: Identification of privacy protection requirements as external constraints on business transactions
Information technology — Business operational view — Part 8: Identification of privacy protection requirements as external constraints on business transactions
ISO/IEC 15944-8:2012 has been developed to support modelling generic international requirements for identifying and providing privacy protection of personal information throughout any kind of information and communications technology (ICT) based business transaction where the individual has the role of a buyer. It provides users and designers with a methodology and tools addressing requirements imposed by jurisdictional domains. ISO/IEC 15944-8:2012 takes the "business operational view" (BOV) aspects developed in ISO/IEC 14662, together with, in particular, ISO/IEC 15944-1 and ISO/IEC 15944-5 as well as many other international references. ISO/IEC 15944 models the requirements of jurisdictional domains as external constraints upon the creation, use, interchange, and information life-cycle management of data. ISO/IEC 15944-8:2012 addresses the wider context of the public policy requirements of jurisdictional domains controlling the use of personal information (PI). These include regulations for consumer protection, privacy protection, individual accessibility, etc. ISO/IEC 15944-8:2012 identifies and expands upon eleven generic, primitive, international principles that have been associated with privacy protection by international, regional, and UN member states' requirements. It models them with respect to the "collaboration space" of a business transaction and commitment exchange involving an individual acting in the role of a "buyer". It provides principles and rules governing the establishment, management and use of identifiers of that individual, including the use of legally recognized names (LRNs), recognized individual identity (rii), and methods of non-identification such as the use of anonymization and pseudonymization of personal information. ISO/IEC 15944-8:2012 also sets out principles governing information life-cycle management (ILCM) as well as the rules and associated coded domains for obtaining informed consent for collection, specifying state changes, records retention, record deletion and related matters in support of privacy protection requirements.
Technologies de l'information — Vue opérationnelle d'affaires — Partie 8: Identification des exigences de protection de la vie privée en tant que contraintes externes sur les transactions d'affaires
General Information
- Status
- Withdrawn
- Publication Date
- 28-Mar-2012
- Technical Committee
- ISO/IEC JTC 1/SC 32 - Data management and interchange
- Drafting Committee
- ISO/IEC JTC 1/SC 32/WG 1 - eBusiness
- Current Stage
- 9599 - Withdrawal of International Standard
- Start Date
- 11-Feb-2026
- Completion Date
- 21-Mar-2026
Relations
- Effective Date
- 07-Jul-2022
Overview
ISO/IEC 15944-8:2012 - Information technology - Business operational view - Part 8 - defines a methodology for identifying privacy protection requirements as external constraints on ICT-based business transactions where an individual acts as a buyer. Built on the Business Operational View (BOV) and Open-edi concepts, the standard models jurisdictional public-policy constraints (privacy, consumer protection, accessibility, human rights) as requirements that affect creation, use, interchange and life-cycle management of personal information (PI). It explicitly identifies eleven generic international privacy principles and provides templates, rules and coded domains to support consistent privacy design and compliance.
Key topics and technical requirements
- Eleven fundamental privacy principles (e.g., preventing harm, accountability, purpose limitation, informed consent, data minimization, retention limits, accuracy, safeguards, openness, access, complaint/challenge) and their application to business transactions.
- Collaboration space modelling for Open-edi scenarios - buyer, seller and regulator roles - to map where privacy constraints apply in transaction lifecycles.
- Identifiers and identity rules: principles for establishing, managing and using identifiers, legally recognized names (LRNs), recognized individual identity (rii), and registration authority (RA) considerations.
- Non‑identification methods: rules governing anonymization and pseudonymization of personal information in transactions.
- Information Life‑Cycle Management (ILCM): integrated principles for state changes, records retention, deletion and time/date referencing to meet jurisdictional privacy rules.
- Data tagging/labelling and coded domains for specifying permitted state changes and retention policies that enforce privacy constraints.
- Templates and conformance: scenario templates for specifying privacy requirements in Open-edi use cases and conformance statements for implementers.
Practical applications and users
ISO/IEC 15944-8:2012 is intended for:
- Privacy architects and data protection officers designing compliant data flows across jurisdictions.
- Business analysts and e‑commerce solution designers mapping privacy constraints into transaction models (Open-edi/BOV).
- System integrators and software vendors implementing identifier, consent and retention controls in ICT systems.
- Regulators and policy makers aligning public policy requirements with technical transaction models.
- Compliance teams and auditors using templates and conformance guidance to verify that transaction processes meet jurisdictional privacy requirements.
Practical uses include designing privacy-aware e‑commerce workflows, specifying PI tagging and retention policies, defining consent mechanisms, and modeling cross-border data restrictions.
Related standards
- ISO/IEC 15944‑1 and ISO/IEC 15944‑5 (related parts of the multipart eBusiness standard)
- ISO/IEC 14662 (Open‑edi Reference Model) These form the BOV/Open‑edi foundation on which 15944‑8 models privacy as external constraints.
Keywords: ISO/IEC 15944-8:2012, privacy protection, business transactions, jurisdictional domains, information life‑cycle management, anonymization, pseudonymization, informed consent, identifiers, Open-edi, Business Operational View (BOV).
Buy Documents
ISO/IEC 15944-8:2012 - Information technology — Business operational view — Part 8: Identification of privacy protection requirements as external constraints on business transactions/29/2012
ISO/IEC 15944-8:2012 - Information technology -- Business operational view
Get Certified
Connect with accredited certification bodies for this standard

BSI Group
BSI (British Standards Institution) is the business standards company that helps organizations make excellence a habit.

NYCE
Mexican standards and certification body.
Sponsored listings
Frequently Asked Questions
ISO/IEC 15944-8:2012 is a standard published by the International Organization for Standardization (ISO). Its full title is "Information technology — Business operational view — Part 8: Identification of privacy protection requirements as external constraints on business transactions". This standard covers: ISO/IEC 15944-8:2012 has been developed to support modelling generic international requirements for identifying and providing privacy protection of personal information throughout any kind of information and communications technology (ICT) based business transaction where the individual has the role of a buyer. It provides users and designers with a methodology and tools addressing requirements imposed by jurisdictional domains. ISO/IEC 15944-8:2012 takes the "business operational view" (BOV) aspects developed in ISO/IEC 14662, together with, in particular, ISO/IEC 15944-1 and ISO/IEC 15944-5 as well as many other international references. ISO/IEC 15944 models the requirements of jurisdictional domains as external constraints upon the creation, use, interchange, and information life-cycle management of data. ISO/IEC 15944-8:2012 addresses the wider context of the public policy requirements of jurisdictional domains controlling the use of personal information (PI). These include regulations for consumer protection, privacy protection, individual accessibility, etc. ISO/IEC 15944-8:2012 identifies and expands upon eleven generic, primitive, international principles that have been associated with privacy protection by international, regional, and UN member states' requirements. It models them with respect to the "collaboration space" of a business transaction and commitment exchange involving an individual acting in the role of a "buyer". It provides principles and rules governing the establishment, management and use of identifiers of that individual, including the use of legally recognized names (LRNs), recognized individual identity (rii), and methods of non-identification such as the use of anonymization and pseudonymization of personal information. ISO/IEC 15944-8:2012 also sets out principles governing information life-cycle management (ILCM) as well as the rules and associated coded domains for obtaining informed consent for collection, specifying state changes, records retention, record deletion and related matters in support of privacy protection requirements.
ISO/IEC 15944-8:2012 has been developed to support modelling generic international requirements for identifying and providing privacy protection of personal information throughout any kind of information and communications technology (ICT) based business transaction where the individual has the role of a buyer. It provides users and designers with a methodology and tools addressing requirements imposed by jurisdictional domains. ISO/IEC 15944-8:2012 takes the "business operational view" (BOV) aspects developed in ISO/IEC 14662, together with, in particular, ISO/IEC 15944-1 and ISO/IEC 15944-5 as well as many other international references. ISO/IEC 15944 models the requirements of jurisdictional domains as external constraints upon the creation, use, interchange, and information life-cycle management of data. ISO/IEC 15944-8:2012 addresses the wider context of the public policy requirements of jurisdictional domains controlling the use of personal information (PI). These include regulations for consumer protection, privacy protection, individual accessibility, etc. ISO/IEC 15944-8:2012 identifies and expands upon eleven generic, primitive, international principles that have been associated with privacy protection by international, regional, and UN member states' requirements. It models them with respect to the "collaboration space" of a business transaction and commitment exchange involving an individual acting in the role of a "buyer". It provides principles and rules governing the establishment, management and use of identifiers of that individual, including the use of legally recognized names (LRNs), recognized individual identity (rii), and methods of non-identification such as the use of anonymization and pseudonymization of personal information. ISO/IEC 15944-8:2012 also sets out principles governing information life-cycle management (ILCM) as well as the rules and associated coded domains for obtaining informed consent for collection, specifying state changes, records retention, record deletion and related matters in support of privacy protection requirements.
ISO/IEC 15944-8:2012 is classified under the following ICS (International Classification for Standards) categories: 35.240.60 - IT applications in transport; 35.240.63 - IT applications in trade. The ICS classification helps identify the subject area and facilitates finding related standards.
ISO/IEC 15944-8:2012 has the following relationships with other standards: It is inter standard links to ISO/IEC 15944-8:2026. Understanding these relationships helps ensure you are using the most current and applicable version of the standard.
ISO/IEC 15944-8:2012 is available in PDF format for immediate download after purchase. The document can be added to your cart and obtained through the secure checkout process. Digital delivery ensures instant access to the complete standard document.
Standards Content (Sample)
INTERNATIONAL ISO/IEC
STANDARD 15944-8
First edition
2012-04-01
Information technology — Business
Operational View —
Part 8:
Identification of privacy protection
requirements as external constraints on
business transactions
Technologies de l'information — Vue opérationnelle d'affaires —
Partie 8: Identification des exigences de protection de la vie privée en
tant que contraintes externes sur les transactions d'affaires
Reference number
©
ISO/IEC 2012
© ISO/IEC 2012
All rights reserved. Unless otherwise specified, no part of this publication may be reproduced or utilized in any form or by any means,
electronic or mechanical, including photocopying and microfilm, without permission in writing from either ISO at the address below or
ISO's member body in the country of the requester.
ISO copyright office
Case postale 56 CH-1211 Geneva 20
Tel. + 41 22 749 01 11
Fax + 41 22 749 09 47
E-mail copyright@iso.org
Web www.iso.org
Published in Switzerland
ii © ISO/IEC 2012 – All rights reserved
Contents Page
Foreword . vii
0 Introduction . viii
0.1 Purpose and overview . viii
0.1.1 ISO/IEC 14662 "Open-edi Reference Model" . viii
0.1.2 ISO/IEC 15944-1 “Business Agreement Semantic Descriptive Techniques” (“Business
Operational View (BOV”)) . x
0.2 Introducing the use of "Person", "organization" and "party" in the context of business
transaction and commitment exchange . xi
0.3 Importance and role of terms and definitions . xiii
0.4 Importance of the two classes of constraints of the Business Transaction Model (BTM) . xiii
0.5 Need for a standard based on rules and guidelines . xiv
0.6 Use of "jurisdictional domain", and "jurisdiction" (and "country") in the context of
business transaction and commitment exchange . xv
0.7 Use of "identifier" as "identifier (in business transaction)" to prevent ambiguity . xvi
0.8 Use of “privacy protection” in the context of business transaction and commitment
exchange . xvi
0.9 Organization and description of this document . xvii
1 Scope . 1
1.1 Statement of scope . 1
1.2 Exclusions . 2
1.2.1 Functional Services View (FSV) . 2
1.2.2 Internal behaviour of organizations (and public administration) . 2
1.2.3 “organization Person” . 2
1.2.4 Overlap of and/or conflict among jurisdictional domains as sources of privacy protection
requirements . 2
1.2.5 Publicly available personal information. 3
1.3 Aspects currently not addressed . 4
1.4 IT-systems environment neutrality . 7
2 Normative references . 9
2.1 ISO/IEC, ISO and ITU . 9
2.2 Referenced specifications . 10
3 Terms and definitions . 11
4 Symbols and abbreviations . 41
5 Fundamental principles and assumptions governing privacy protection requirements in
business transactions involving individuals (external constraints perspective) . 43
5.1 Introduction . 43
5.2 Exceptions to the application of the privacy protection principles . 46
5.3 Fundamental Privacy Protection Principles . 46
5.3.1 Privacy Protection Principle 1: Preventing Harm . 46
5.3.2 Privacy Protection Principle 2: Accountability . 47
5.3.3 Privacy Protection Principle 3: Identifying Purposes . 50
5.3.4 Privacy Protection Principle 4: Informed Consent . 50
5.3.5 Privacy Protection Principle 5: Limiting Collection . 52
5.3.6 Privacy Protection Principle 6: Limiting Use, Disclosure and Retention . 54
5.3.7 Privacy Protection Principle 7: Accuracy . 57
5.3.8 Privacy Protection Principle 8: Safeguards . 58
5.3.9 Privacy Protection Principle 9: Openness . 59
5.3.10 Principle Protection Principle 10: Individual Access . 60
5.3.11 Privacy Protection Principle 11: Challenging Compliance . 62
© ISO/IEC 2012 – All rights reserved iii
5.4 Requirement for tagging (or labelling) data elements in support of privacy protection
requirements .63
6 Collaboration space and privacy protection .65
6.1 Introduction .65
6.2 Basic Open-edi collaboration space: Buyer and seller .65
6.3 Collaboration space: The role of buyer (as individual), seller and regulator .66
7 Public policy requirements of jurisdictional domains .69
7.1 Introduction .69
7.2 Jurisdictional domains and public policy requirements .69
7.2.1 Privacy protection.70
7.2.2 Person and external constraints: Consumer protection .72
7.2.3 Individual accessibility .73
7.2.4 Human rights .74
7.2.5 Privacy as a right of an “individual” and not the right of an organization or public
administration .74
8 Principles and rules governing the establishment, management and use of identities of
an individual .77
8.1 Introduction .77
8.2 Rules governing the establishment of personae, identifiers and signatures of an
individual .78
8.3 Rules governing the assignment of unique identifiers to an individual by Registration
Authorities (RAs) .84
8.4 Rules governing individual identity, authentication, recognition, and use .85
8.5 Legally recognized individual identifies (LRIIs) .90
9 Person component – individual sub-type .93
9.1 Introduction .93
9.2 Role qualification of a Person as an individual .93
9.3 Persona and legally recognized names (LRNs) of an individual .94
9.4 Truncation of legally recognized names of individuals .94
9.5 Rules governing anonymization of individuals in a business transaction .95
9.6 Rules governing pseudonymization of personal information in a business transaction .97
10 Process component .99
10.1 Introduction .99
10.2 Planning .99
10.3 Identification .99
10.4 Negotiation . 100
10.5 Actualization . 100
10.6 Post-Actualization . 100
11 Data component . 101
11.1 Introduction . 101
11.2 Rules governing the role of Business Transaction Identifier (BTI) in support of privacy
protection requirements . 101
11.3 Rules governing state of change management of business transactions in support of
privacy protection requirements . 102
11.4 Rules governing records retention of personal information in a business transaction . 102
11.5 Rules governing time/date referencing of personal information in a business transaction . 103
12 Template for identifying privacy protection requirements on business transactions . 105
12.1 Introduction and basic principles . 105
12.2 Template structure and contents . 105
12.3 Template for specifying the scope of an Open-edi scenario . 106
12.4 Consolidated template of attributes of Open-edi scenarios, roles and information bundles . 113
13 Conformance statement . 119
13.1 Introduction . 119
13.2 Conformance to the ISO/IEC 14662 Open-edi Reference Model and the multipart
ISO/IEC 15944 eBusiness standard . 119
13.3 Conformance to ISO/IEC 15944-8 . 119
iv © ISO/IEC 2012 – All rights reserved
Annex A (normative) Consolidated list of terms and definitions with cultural adaptability: ISO
English and ISO French language equivalency . 120
A.1 Introduction . 120
A.2 ISO English and ISO French . 120
A.3 Cultural adaptability and quality control. 120
A.4 Organization of Annex A – Consolidated list in matrix form . 121
A.5 Consolidated list of ISO/IEC 15944-8 terms and definitions . 122
Annex B (normative) Consolidated set of rules in existing Parts of ISO/IEC 15944 of particular
relevance to privacy protection requirements as external constraints on business
transactions . 185
B.1 Introduction . 185
B.2 Organization of Annex B: Consolidated list in matrix form . 185
B.3 Consolidated list of rules in ISO/IEC 15944-1 pertaining to external constraints relevant to
supporting privacy protection requirements . 186
B.4 Consolidated list of rules in ISO/IEC 15944-2 pertaining to external constraints of
relevance to supporting privacy protection requirements . 189
B.5 Consolidated list of rules in ISO/IEC 15944-5 pertaining to external constraints of
relevance to supporting privacy protection requirements . 190
B.6 Consolidated list of rules in ISO/IEC 15944-7 pertaining to external constraints of
relevance to supporting privacy protection requirements . 194
Annex C (normative) Business Transaction Model (BTM): Classes of constraints . 200
Annex D (normative) Integrated set of information life cycle management (ILCM) principles in
support of information law compliance . 205
D.1 Introduction . 205
D.2 Purpose . 205
D.3 Approach . 206
D.4 Integrated set of information life cycle management (ILCM) principles . 206
Annex E (normative) Key existing concepts and definitions applicable to the establishment,
management, and use of identities of a single individual. 209
Annex F (normative) Coded domains for specifying state change and record retention
management in support of privacy protection requirements . 211
F.1 Introduction . 211
F.2 State changes . 212
F.2.1 Introduction . 212
F.2.2 Specification of state changes allowed to personal information . 213
F.2.3 Store change type . 214
F.3 Records retention . 216
F.4 Records destruction . 218
Bibliography . 220
© ISO/IEC 2012 – All rights reserved v
Figures Page
Figure 1 — Open-edi environment – Open-edi Reference Model . ix
Figure 2 — Integrated view - Business operational requirements: External constraints focus. xi
Figure 3 — Primary sources for privacy protection principles . 45
Figure 4 — Concept of a business collaboration . 66
Figure 5 — Privacy collaboration space (of a business transaction) including the role of a regulator . 68
Figure 6 — Common public policy requirements, i.e., external constraints, applying to a
business transaction where the “buyer” is an “individual” . 70
Figure 7 — Illustration of relationships of links of a (real world) individual to (its) persona (e)
to identification schemas and resulting identifiers to associated Person signatures —
in the context of different business transactions and governing rules . 80
Figure 8 — Illustration of range of links between personae and identifiers of an individual
identity(ies) of an individual . 86
Figure 9 — Illustration of two basic options for establishment of a recognized individual identity (rii) 89
Figure C.1 — Business Transaction Model - Fundamental components (Graphic illustration) . 200
Figure C.2 — UML-based Representation of Figure C.1 — Business Transaction Model . 201
Figure C.3 — Business Transaction Model: Classes of constraints . 204
Tables Page
Table 1 — Template for specifying the scope of an Open-edi scenario . 106
Table 2 — Consolidated template of attributes of Open-edi scenarios, roles and information
bundles . 113
Table F.1 — ISO/IEC 15944-5:05 Codes for specifying state changes allowed for the values of
Information Bundles and Semantic Components . 213
Table F.2 — ISO/IEC 15944-5:06 Codes representing store change type for Information Bundles and
Semantic Components . 215
Table F.3 — ISO/IEC 15944-5:02 Codes Representing Specification of Records Retention
Responsibility . 216
Table F.4 — ISO/IEC 15944-5:04 Codes representing retention triggers . 218
Table F.5 — ISO/IEC 15944-5:03 Codes representing disposition of recorded information . 219
vi © ISO/IEC 2012 – All rights reserved
Foreword
ISO (the International Organization for Standardization) and IEC (the International Electrotechnical
Commission) form the specialized system for worldwide standardization. National bodies that are members of
ISO or IEC participate in the development of International Standards through technical committees
established by the respective organization to deal with particular fields of technical activity. ISO and IEC
technical committees collaborate in fields of mutual interest. Other international organizations, governmental
and non-governmental, in liaison with ISO and IEC, also take part in the work. In the field of information
technology, ISO and IEC have established a joint technical committee, ISO/IEC JTC 1.
International Standards are drafted in accordance with the rules given in the ISO/IEC Directives, Part 2.
The main task of the joint technical committee is to prepare International Standards. Draft International
Standards adopted by the joint technical committee are circulated to national bodies for voting. Publication as
an International Standard requires approval by at least 75 % of the national bodies casting a vote.
Attention is drawn to the possibility that some of the elements of this document may be the subject of patent
rights. ISO and IEC shall not be held responsible for identifying any or all such patent rights.
ISO/IEC 15944-8 was prepared by Joint Technical Committee ISO/IEC JTC 1, Information technology,
Subcommittee SC 32, Data management and interchange.
ISO/IEC 15944 consists of the following parts, under the general title Information technology — Business
Operational View:
Part 1: Operational aspects of Open-edi for implementation
Part 2: Registration of scenarios and their components as business objects
Part 4: Business transaction scenarios — Accounting and economic ontology
Part 5: Identification and referencing of requirements of jurisdictional domains as sources of external
constraints
Part 6: Technical introduction to e-Business modelling [Technical Report]
Part 7: eBusiness vocabulary
Part 8: Identification of privacy protection requirements as external constraints on business transactions
Part 10: Coded domains
The following parts are under preparation:
Part 3: Open-edi description techniques (OeDTs)
Part 9: Traceability framework
© ISO/IEC 2012 – All rights reserved vii
0 Introduction
0.1 Purpose and overview
Modelling business transactions using scenarios and scenario components is done by specifying the
applicable constraints on the data content using explicitly stated rules. The Open-edi Reference Model
identified two basic classes of constraints, "internal constraints" and "external constraints". External
constraints apply to most business transactions. {See Clause 0.4 and Annex E}
Jurisdictional domains are the primary source of external constraints on business transactions. Privacy
protection requirements in turn are a common requirement of most jurisdictional domains, although they may
also result from explicit scenario demands from or on the parties involved in a business transaction.
(Requirements for secrecy or confidentiality are not addressed in this part of ISO/IEC 15944, unless they are
implicitly needed to apply privacy protection requirements to data).
This part of ISO/IEC 15944 describes the business semantic descriptive techniques needed to support privacy
protection requirements when modelling business transactions using the external constraints of jurisdictional
domains
In addition to the existing strategic directions of "portability" and "interoperability", the added strategic direction
of ISO/IEC JTC1 of "cultural adaptability" is also supported in this part of ISO/IEC 15944. The external
constraints of jurisdictional domains as a primary factor in choice and use of language and application of
public policy are also addressed.
0.1.1 ISO/IEC 14662 "Open-edi Reference Model"
The ISO/IEC 14662 Open-edi Reference Model states the conceptual architecture necessary for carrying out
electronic business transactions among autonomous parties. That architecture identifies and describes the
need to have two separate and related views of the business transaction.
The first is the Business Operational View (BOV). The second is the Functional Service View (FSV). Figure 1
from ISO/IEC 14662:2010 illustrates the Open-edi environment. {For definitions of the terms used in Figure 1,
please see Clause 3 below}
The ISO/IEC 14462 Open-edi Reference Model serves as the basis of the 2000 Memorandum of Understanding
(MOU) among ISO, IEC, ITU and the UN/ECE concerning standardization in the field of electronic business.
{See http://www.itu.int//ITU-T/e-business/files/mou.pdf }
ISO/IEC 14662:2010 (3rd ed. E/F) "Information technology — Open-edi Reference Model/Technologies de
l'information — Modèle de référence EDI-ouvert".
viii © ISO/IEC 2012 – All rights reserved
B
Open-edi Reference Model
U
S
Business
Operational View
I
Comply with
N
BOV RELATED
Business aspects
E Covered by
STANDARDS
of
S
business transactions
S
Viewed as
T
Inter-related
R
A
View
Functional Service
N
S
Information technology
Comply with
A
FSV RELATED
aspects of
C
Covered by
STANDARDS
Business transactions
T
I
O
N
S
Figure 1 — Open-edi environment – Open-edi Reference Model
ISO/IEC 14662:2010, Clause 5 states:
"The intention is that the sending, by an Open-edi Party, of information from a scenario, conforming to
Open-edi standards, shall allow the acceptance and processing of that information in the context of that
scenario by one or more Open-edi Parties by reference to the scenario and without the need for
agreement.
However, the legal requirements and/or liabilities resulting from the engagement of an organization in any
Open-edi transaction may be conditioned by the competent legal environment(s) of the formation of a
legal interchange agreement between the participating organizations. Open-edi Parties need to observe
rule-based behaviour and possess the ability to make commitments in Open-edi, (e.g., business,
operational, technical, legal, and/or audit perspectives)".
In addition, Annex A of the ISO/IEC 14662:2010 "Open-edi Reference Model" contains Figure A.1
"Relationships of Open-edi standardization areas with other standards and import of the legal environment".
This part of ISO/IEC 15944 is a BOV standard which focuses on the legal environment for the application of
privacy and/or data protection from an Open-edi perspective, and, as required follow-up standards
development in support of the "Open-edi Reference Model".
ISO/IEC 15944-5 is used to identify the means by which laws and regulations impacting scenarios and
scenario components, as external constraints, may be modelled and represented. The primary source of
these external constraints is jurisdictional domains.
ISO/IEC 15944-1 creates rules for creating the specification of external constraints when modelling business
transactions through scenarios, scenario attributes and scenario components. Several parts of ISO/IEC 15944
are used as input to this part. They are consolidated in this part of ISO/IEC 15944 in Annex B.
ISO/IEC 15944-1:2011 in Clause 7 "Guidelines for scoping Open-edi Scenarios" states in Clause 7.1:
"The approach taken is that of identifying the most primitive common components of a business
transaction and then moving from the general to the more detailed, the simplest aspects to the more
© ISO/IEC 2012 – All rights reserved ix
complex, from no external constraints on a business transaction to those which incorporate external
constraints, from no special requirements on functional services to specific requirements, and so on".
This part of ISO/IEC 15944 focuses on addressing commonly definable aspects of external constraints that
relate to privacy and data protection when the source is a jurisdictional domain. A useful characteristic of
external constraints is that, at the sectoral level, national and international levels, etc., focal points and
recognized authorities often already exist. The rules and common business practices in many sectoral areas
are already known. Use of this part of ISO/IEC 15944 (and related standards) addresses the transformation of
these external constraints (business rules) into specified, registered, and re-useable scenarios and scenario
components.
0.1.2 ISO/IEC 15944-1 “Business Agreement Semantic Descriptive Techniques” (“Business
Operational View (BOV”))
ISO/IEC 15944-1 states the requirements of the BOV aspects of Open-edi in support of electronic business
transactions. They shall be taken into account in the development of business semantic descriptive
techniques for modelling e-business transactions and components thereof as re-useable business objects.
They include:
commercial frameworks and associated requirements;
legal frameworks and associated requirements;
public policy requirements particularly those of a generic nature such as consumer protection, privacy,
accommodation of handicapped/disabled;
requirements arising from the need to support cultural adaptability. This includes meeting localization and
multilingual requirements, (e.g., as may be required by a particular jurisdictional domain or desired to
provide a good, service and/or right in a particular market. Here one needs the ability to distinguish, the
specification of scenarios, scenario components, and their semantics, in the context of making
commitments, between:
a) the use of unique, unambiguous and linguistically neutral identifiers (often as composite identifiers) at
the information technology (IT) interface level among the IT systems of participation parties on the
one hand; and, on the other,
b) their multiple human interface equivalent (HIE) expressions in a presentation form appropriate to the
Persons involved in the making of the resulting commitments.
Figure 2 shows an integrated view of these business operational requirements. It is based on Figure 3 from
ISO/IEC 15944-1. Since the focus of this part of ISO/IEC 15944 is that of external constraints for which
jurisdictional domains are the primary source these primary sources have been shaded in Figure 2 below).
x © ISO/IEC 2012 – All rights reserved
Sources of Requirements on the Business Operational View (BOV) aspects of Open-edi
which need to be integrated and/or taken into account
Business Transactions
Commercial Legal
(Open-edi based)
Framework & Framework &
Requirements Requirements
o Characteristics of Open-edi
Rule-Based
Commitment Exchange
Unambiguous Identification
Business Transaction
Model (BTM)
Key Components
Information
Technology
Public Policy
Person
Requirements
Req’mts
& Standards
(Privacy
Process
protection,
Consumer, c.) Data
Telecom-
Business Transaction Model:
munications
Classes of Constraints
Req’mts &
Specification, Identification &
Standards
Classification of Open-edi
scenarios (and components)
FSV Business Demands on
Sectoral (&
Open-edi Support Infrastructure
cross-sectoral)
Open-edi Scenario Templates
Req’mts
ISO & Other
Standards
Environments
Cultural Adaptability
Localization &
Multilingualism
(IT vs Human Interface)
Functional Services View (FSV)
Figure 2 — Integrated view - Business operational requirements: External constraints focus
0.2 Introducing the use of "Person", "organization" and "party" in the context of business
transaction and commitment exchange
In electronic business transactions, whether undertaken on a for profit or not-for-profit basis, the key element
is commitment exchange among Persons made among their Decision Making Applications (DMAs) of the
© ISO/IEC 2012 – All rights reserved xi
Information Technology Systems (IT Systems) acting on behalf of "Persons". "Persons" are the only entities
able to make commitments . Clause 0.4 in ISO/IEC 15944-1 states:
"When the ISO/IEC 14662 Open-edi Reference Model standard was being developed, the "Internet" and
"WWW" were an embryonic stage and their impact on private and public sector organizations was not
fully understood.”
The Business Operational View (BOV) was therefore defined as:
“perspective of business transactions limited to those aspects regarding the making of business
decisions and commitments among organizations which are needed for the description of a business
transaction".
The ISO/IEC 6523 definition of "organization" was used in the first edition (1997) of ISO/IEC 14662. The fact
that today Open-edi, through the Internet and WWW, also involves "individuals" has been taken into account
nd
in the development of the 2 and subsequent editions. ISO/IEC 15944-1 defines the term "commitment”.
However, the definition of the term "Open-edi Party" previously used proved not to be specific enough to
satisfy scenario specifications when the legal aspects of commitment were considered. In many instances
commitments were noted as being actually among IT systems acting under the direction of those legally
capable of making commitment, rather than actually the individuals acting in their own capacities. It was also
recognized that in some jurisdictions a commitment could be made by "artificial" persons such as corporate
bodies. Finally, it was noted that there are occasions where agents act, either under the instruction of a
principal, or as a result of requirement(s) laid down by a jurisdiction, or where an individual is prevented by a
relevant jurisdiction from being able to make a commitment in their own right, (e.g., a minor), and this must be
incorporated into the standard.
To address these extended requirements the additional concept and term of "Person", has been defined. A
Person is defined such that they are capable of having the appropriate legal and regulatory constraints applied
to them.
There are three categories of Person as a role player in Open-edi, namely: (1) the Person as "individual", (2)
the Person as "organization", and (3) the Person as "public administration". There are also three basic (or
primitive) roles of Persons in business transactions, namely: "buyer", "seller", and "regulator".
When modelling business transactions, jurisdictional domains prescribe their external constraints in the role of
"regulator" and execute them as "public administration". {See further below Clause 6.3}
While “public administration” is one of the three distinct sub-types of Person, most of the rules applicable to
“organization” also apply to “public administration”. In addition, an unincorporated seller is also deemed to
function as an “organization”. Consequently, the use of “organization” throughout this part of ISO/IEC 15944
also covers “public administration”. Where it is necessary to bring forward specific rules, constraints,
properties, etc., which apply specifically to “public administration”, this is stated explicitly.
The requirements of jurisdictional domains are specified through the use of sets of "Codes representing X.”
Such sets of codes are created and maintained by Source Authorities via a rulebase with resulting coded
domains in the form of data elements whose permitted values represent predefined semantics in a structured
form, i.e., as a type of semantic component. Jurisdictional domains serve as Source Authorities for such
coded domains.
These three categories of Person also identify the possible Source Authorities for coded domains. Source
Authorities for coded domains are therefore either "organizations" or "public administrations".
Throughout this part of ISO/IEC 15944:
rd
See further Clause 5.2 "Functional Services View" in ISO/IEC 14662:2010 "Open-edi Reference Model" (3 edition).
The text in this section is based on existing text in Section "0.3" in ISO/IEC 15944-1:2011 and ISO/IEC 14662:2010
rd
(3 edition).
xii © ISO/IEC 2012 – All rights reserved
the use of Person with a capital "P" represents Person as a defined term, i.e., as the entity within an
Open-edi Party that carries the legal responsibility for making commitment(s);
"individual", "organization", and "public administration" are defined terms representing the three common
sub-types of "Person"; and,
the words "person(s)" and/or "party(ies)" are used in their generic contexts independent of roles of
"Person" as defined in the ISO/IEC 14662 and ISO/IEC 15944-1 standards. A "party" to a business
transaction has the properties and behaviours of a "Person".
0.3 Importance and role of terms and definitions
ISO/IEC Directives Part 2 provide for “Terms and definitions” as a “Technical normative element,” necessary
for the understanding of certain terms used in the document, where the words have special, extended or
technical meaning.
The ISO/IEC 15944 multipart standard sets out the processes for achieving a common understanding of the
Business Operational View (BOV) from commercial, legal, ICT, public policy and cross-sectoral perspectives.
It is therefore important to check and confirm that a “common understanding” in any one of these domains is
also unambiguously understood as identical in the others.
This sub-clause is included in each part of ISO/IEC 15944 to emphasize that harmonized terms and
definitions are essential to the continuity of the overall standard. Definitions and their assigned terms should
be established as early as possible in the development process. Comments on any definition/term pair should
address the question of changes needed to avoid possible misinterpretation. Definitions may need to be
amended/improved as part of the harmonization of definitions and their assigned terms among the various
parts of ISO/IEC 15944.
In order to minimize ambiguity in the definitions and their associated terms, each definition and its associated
term has been made available in at least one language other than English in the part in which it is introduced.
In this context, it is noted that ISO/IEC 15944-7 eBusiness vocabulary already also contains human interface
equivalents (HIEs) in ISO Chinese, ISO French, and ISO Russian.
Normative Annex A “Consolidated list of terms and definitions with cultural adaptability: ISO English and ISO
French language equivalency” is derived from Clause 3 of each part of ISO/IEC 15944. Annex A is repeated
in each part of ISO/IEC 15944 as a convenient reference. The designation ISO before a natural language
refers to the use of that natural language in ISO standards, and has no other meaning.
0.4 Importance of the two classes of constraints of the Business Transaction Model (BTM)
The BTM has two classes of constraints; namely:
1) those which are "self-imposed" and agreed to as commitments among the parties themselves, i.e.,
"internal constraints"; and,
2) those which are imposed on the parties to a business transaction based on the nature of the good, service
and/or rights exchanged, the nature of the commitment made among the parties (including ability to make
All the terms and definitions of the current editions of the ISO/IEC 14669 Open-edi Reference Model and the
multipart ISO/IEC 15944 eBusiness standard have been consolidated in ISO/IEC 15944-7:2009. A primary reason for
having “Terms and definitions” in a standard is because one cannot assume that there exists a common understanding,
worldwide, for a specific concept. And even if one assumes that such an understanding exists, then having such a
common definition in Clause 3 serves to formally and explicitly affirm (re-affirm) such a common understanding, i.e.,
ensure that all parties concerned share this common understanding as stated through the text of the definitions in
Clause 3.
Canada has committed to maintain this comprehensive list in a database as the reference file for Annex A. This
Annex A reference file will insure the consistency of definitions and their assigned terms among the various parts in the
on-going harmonization effort. {See also ISO/IEC 15944-7 e-Business Vocabulary}
© ISO/IEC 2012 – All rights reserved xiii
commitments, the location, inf
...
INTERNATIONAL ISO/IEC
STANDARD 15944-8
First edition
2012-04-01
Information technology — Business
Operational View —
Part 8:
Identification of privacy protection
requirements as external constraints on
business transactions
Technologies de l'information — Vue opérationnelle d'affaires —
Partie 8: Identification des exigences de protection de la vie privée en
tant que contraintes externes sur les transactions d'affaires
Reference number
©
ISO/IEC 2012
© ISO/IEC 2012
All rights reserved. Unless otherwise specified, no part of this publication may be reproduced or utilized in any form or by any means,
electronic or mechanical, including photocopying and microfilm, without permission in writing from either ISO at the address below or
ISO's member body in the country of the requester.
ISO copyright office
Case postale 56 CH-1211 Geneva 20
Tel. + 41 22 749 01 11
Fax + 41 22 749 09 47
E-mail copyright@iso.org
Web www.iso.org
Published in Switzerland
ii © ISO/IEC 2012 – All rights reserved
Contents Page
Foreword . vii
0 Introduction . viii
0.1 Purpose and overview . viii
0.1.1 ISO/IEC 14662 "Open-edi Reference Model" . viii
0.1.2 ISO/IEC 15944-1 “Business Agreement Semantic Descriptive Techniques” (“Business
Operational View (BOV”)) . x
0.2 Introducing the use of "Person", "organization" and "party" in the context of business
transaction and commitment exchange . xi
0.3 Importance and role of terms and definitions . xiii
0.4 Importance of the two classes of constraints of the Business Transaction Model (BTM) . xiii
0.5 Need for a standard based on rules and guidelines . xiv
0.6 Use of "jurisdictional domain", and "jurisdiction" (and "country") in the context of
business transaction and commitment exchange . xv
0.7 Use of "identifier" as "identifier (in business transaction)" to prevent ambiguity . xvi
0.8 Use of “privacy protection” in the context of business transaction and commitment
exchange . xvi
0.9 Organization and description of this document . xvii
1 Scope . 1
1.1 Statement of scope . 1
1.2 Exclusions . 2
1.2.1 Functional Services View (FSV) . 2
1.2.2 Internal behaviour of organizations (and public administration) . 2
1.2.3 “organization Person” . 2
1.2.4 Overlap of and/or conflict among jurisdictional domains as sources of privacy protection
requirements . 2
1.2.5 Publicly available personal information. 3
1.3 Aspects currently not addressed . 4
1.4 IT-systems environment neutrality . 7
2 Normative references . 9
2.1 ISO/IEC, ISO and ITU . 9
2.2 Referenced specifications . 10
3 Terms and definitions . 11
4 Symbols and abbreviations . 41
5 Fundamental principles and assumptions governing privacy protection requirements in
business transactions involving individuals (external constraints perspective) . 43
5.1 Introduction . 43
5.2 Exceptions to the application of the privacy protection principles . 46
5.3 Fundamental Privacy Protection Principles . 46
5.3.1 Privacy Protection Principle 1: Preventing Harm . 46
5.3.2 Privacy Protection Principle 2: Accountability . 47
5.3.3 Privacy Protection Principle 3: Identifying Purposes . 50
5.3.4 Privacy Protection Principle 4: Informed Consent . 50
5.3.5 Privacy Protection Principle 5: Limiting Collection . 52
5.3.6 Privacy Protection Principle 6: Limiting Use, Disclosure and Retention . 54
5.3.7 Privacy Protection Principle 7: Accuracy . 57
5.3.8 Privacy Protection Principle 8: Safeguards . 58
5.3.9 Privacy Protection Principle 9: Openness . 59
5.3.10 Principle Protection Principle 10: Individual Access . 60
5.3.11 Privacy Protection Principle 11: Challenging Compliance . 62
© ISO/IEC 2012 – All rights reserved iii
5.4 Requirement for tagging (or labelling) data elements in support of privacy protection
requirements .63
6 Collaboration space and privacy protection .65
6.1 Introduction .65
6.2 Basic Open-edi collaboration space: Buyer and seller .65
6.3 Collaboration space: The role of buyer (as individual), seller and regulator .66
7 Public policy requirements of jurisdictional domains .69
7.1 Introduction .69
7.2 Jurisdictional domains and public policy requirements .69
7.2.1 Privacy protection.70
7.2.2 Person and external constraints: Consumer protection .72
7.2.3 Individual accessibility .73
7.2.4 Human rights .74
7.2.5 Privacy as a right of an “individual” and not the right of an organization or public
administration .74
8 Principles and rules governing the establishment, management and use of identities of
an individual .77
8.1 Introduction .77
8.2 Rules governing the establishment of personae, identifiers and signatures of an
individual .78
8.3 Rules governing the assignment of unique identifiers to an individual by Registration
Authorities (RAs) .84
8.4 Rules governing individual identity, authentication, recognition, and use .85
8.5 Legally recognized individual identifies (LRIIs) .90
9 Person component – individual sub-type .93
9.1 Introduction .93
9.2 Role qualification of a Person as an individual .93
9.3 Persona and legally recognized names (LRNs) of an individual .94
9.4 Truncation of legally recognized names of individuals .94
9.5 Rules governing anonymization of individuals in a business transaction .95
9.6 Rules governing pseudonymization of personal information in a business transaction .97
10 Process component .99
10.1 Introduction .99
10.2 Planning .99
10.3 Identification .99
10.4 Negotiation . 100
10.5 Actualization . 100
10.6 Post-Actualization . 100
11 Data component . 101
11.1 Introduction . 101
11.2 Rules governing the role of Business Transaction Identifier (BTI) in support of privacy
protection requirements . 101
11.3 Rules governing state of change management of business transactions in support of
privacy protection requirements . 102
11.4 Rules governing records retention of personal information in a business transaction . 102
11.5 Rules governing time/date referencing of personal information in a business transaction . 103
12 Template for identifying privacy protection requirements on business transactions . 105
12.1 Introduction and basic principles . 105
12.2 Template structure and contents . 105
12.3 Template for specifying the scope of an Open-edi scenario . 106
12.4 Consolidated template of attributes of Open-edi scenarios, roles and information bundles . 113
13 Conformance statement . 119
13.1 Introduction . 119
13.2 Conformance to the ISO/IEC 14662 Open-edi Reference Model and the multipart
ISO/IEC 15944 eBusiness standard . 119
13.3 Conformance to ISO/IEC 15944-8 . 119
iv © ISO/IEC 2012 – All rights reserved
Annex A (normative) Consolidated list of terms and definitions with cultural adaptability: ISO
English and ISO French language equivalency . 120
A.1 Introduction . 120
A.2 ISO English and ISO French . 120
A.3 Cultural adaptability and quality control. 120
A.4 Organization of Annex A – Consolidated list in matrix form . 121
A.5 Consolidated list of ISO/IEC 15944-8 terms and definitions . 122
Annex B (normative) Consolidated set of rules in existing Parts of ISO/IEC 15944 of particular
relevance to privacy protection requirements as external constraints on business
transactions . 185
B.1 Introduction . 185
B.2 Organization of Annex B: Consolidated list in matrix form . 185
B.3 Consolidated list of rules in ISO/IEC 15944-1 pertaining to external constraints relevant to
supporting privacy protection requirements . 186
B.4 Consolidated list of rules in ISO/IEC 15944-2 pertaining to external constraints of
relevance to supporting privacy protection requirements . 189
B.5 Consolidated list of rules in ISO/IEC 15944-5 pertaining to external constraints of
relevance to supporting privacy protection requirements . 190
B.6 Consolidated list of rules in ISO/IEC 15944-7 pertaining to external constraints of
relevance to supporting privacy protection requirements . 194
Annex C (normative) Business Transaction Model (BTM): Classes of constraints . 200
Annex D (normative) Integrated set of information life cycle management (ILCM) principles in
support of information law compliance . 205
D.1 Introduction . 205
D.2 Purpose . 205
D.3 Approach . 206
D.4 Integrated set of information life cycle management (ILCM) principles . 206
Annex E (normative) Key existing concepts and definitions applicable to the establishment,
management, and use of identities of a single individual. 209
Annex F (normative) Coded domains for specifying state change and record retention
management in support of privacy protection requirements . 211
F.1 Introduction . 211
F.2 State changes . 212
F.2.1 Introduction . 212
F.2.2 Specification of state changes allowed to personal information . 213
F.2.3 Store change type . 214
F.3 Records retention . 216
F.4 Records destruction . 218
Bibliography . 220
© ISO/IEC 2012 – All rights reserved v
Figures Page
Figure 1 — Open-edi environment – Open-edi Reference Model . ix
Figure 2 — Integrated view - Business operational requirements: External constraints focus. xi
Figure 3 — Primary sources for privacy protection principles . 45
Figure 4 — Concept of a business collaboration . 66
Figure 5 — Privacy collaboration space (of a business transaction) including the role of a regulator . 68
Figure 6 — Common public policy requirements, i.e., external constraints, applying to a
business transaction where the “buyer” is an “individual” . 70
Figure 7 — Illustration of relationships of links of a (real world) individual to (its) persona (e)
to identification schemas and resulting identifiers to associated Person signatures —
in the context of different business transactions and governing rules . 80
Figure 8 — Illustration of range of links between personae and identifiers of an individual
identity(ies) of an individual . 86
Figure 9 — Illustration of two basic options for establishment of a recognized individual identity (rii) 89
Figure C.1 — Business Transaction Model - Fundamental components (Graphic illustration) . 200
Figure C.2 — UML-based Representation of Figure C.1 — Business Transaction Model . 201
Figure C.3 — Business Transaction Model: Classes of constraints . 204
Tables Page
Table 1 — Template for specifying the scope of an Open-edi scenario . 106
Table 2 — Consolidated template of attributes of Open-edi scenarios, roles and information
bundles . 113
Table F.1 — ISO/IEC 15944-5:05 Codes for specifying state changes allowed for the values of
Information Bundles and Semantic Components . 213
Table F.2 — ISO/IEC 15944-5:06 Codes representing store change type for Information Bundles and
Semantic Components . 215
Table F.3 — ISO/IEC 15944-5:02 Codes Representing Specification of Records Retention
Responsibility . 216
Table F.4 — ISO/IEC 15944-5:04 Codes representing retention triggers . 218
Table F.5 — ISO/IEC 15944-5:03 Codes representing disposition of recorded information . 219
vi © ISO/IEC 2012 – All rights reserved
Foreword
ISO (the International Organization for Standardization) and IEC (the International Electrotechnical
Commission) form the specialized system for worldwide standardization. National bodies that are members of
ISO or IEC participate in the development of International Standards through technical committees
established by the respective organization to deal with particular fields of technical activity. ISO and IEC
technical committees collaborate in fields of mutual interest. Other international organizations, governmental
and non-governmental, in liaison with ISO and IEC, also take part in the work. In the field of information
technology, ISO and IEC have established a joint technical committee, ISO/IEC JTC 1.
International Standards are drafted in accordance with the rules given in the ISO/IEC Directives, Part 2.
The main task of the joint technical committee is to prepare International Standards. Draft International
Standards adopted by the joint technical committee are circulated to national bodies for voting. Publication as
an International Standard requires approval by at least 75 % of the national bodies casting a vote.
Attention is drawn to the possibility that some of the elements of this document may be the subject of patent
rights. ISO and IEC shall not be held responsible for identifying any or all such patent rights.
ISO/IEC 15944-8 was prepared by Joint Technical Committee ISO/IEC JTC 1, Information technology,
Subcommittee SC 32, Data management and interchange.
ISO/IEC 15944 consists of the following parts, under the general title Information technology — Business
Operational View:
Part 1: Operational aspects of Open-edi for implementation
Part 2: Registration of scenarios and their components as business objects
Part 4: Business transaction scenarios — Accounting and economic ontology
Part 5: Identification and referencing of requirements of jurisdictional domains as sources of external
constraints
Part 6: Technical introduction to e-Business modelling [Technical Report]
Part 7: eBusiness vocabulary
Part 8: Identification of privacy protection requirements as external constraints on business transactions
Part 10: Coded domains
The following parts are under preparation:
Part 3: Open-edi description techniques (OeDTs)
Part 9: Traceability framework
© ISO/IEC 2012 – All rights reserved vii
0 Introduction
0.1 Purpose and overview
Modelling business transactions using scenarios and scenario components is done by specifying the
applicable constraints on the data content using explicitly stated rules. The Open-edi Reference Model
identified two basic classes of constraints, "internal constraints" and "external constraints". External
constraints apply to most business transactions. {See Clause 0.4 and Annex E}
Jurisdictional domains are the primary source of external constraints on business transactions. Privacy
protection requirements in turn are a common requirement of most jurisdictional domains, although they may
also result from explicit scenario demands from or on the parties involved in a business transaction.
(Requirements for secrecy or confidentiality are not addressed in this part of ISO/IEC 15944, unless they are
implicitly needed to apply privacy protection requirements to data).
This part of ISO/IEC 15944 describes the business semantic descriptive techniques needed to support privacy
protection requirements when modelling business transactions using the external constraints of jurisdictional
domains
In addition to the existing strategic directions of "portability" and "interoperability", the added strategic direction
of ISO/IEC JTC1 of "cultural adaptability" is also supported in this part of ISO/IEC 15944. The external
constraints of jurisdictional domains as a primary factor in choice and use of language and application of
public policy are also addressed.
0.1.1 ISO/IEC 14662 "Open-edi Reference Model"
The ISO/IEC 14662 Open-edi Reference Model states the conceptual architecture necessary for carrying out
electronic business transactions among autonomous parties. That architecture identifies and describes the
need to have two separate and related views of the business transaction.
The first is the Business Operational View (BOV). The second is the Functional Service View (FSV). Figure 1
from ISO/IEC 14662:2010 illustrates the Open-edi environment. {For definitions of the terms used in Figure 1,
please see Clause 3 below}
The ISO/IEC 14462 Open-edi Reference Model serves as the basis of the 2000 Memorandum of Understanding
(MOU) among ISO, IEC, ITU and the UN/ECE concerning standardization in the field of electronic business.
{See http://www.itu.int//ITU-T/e-business/files/mou.pdf }
ISO/IEC 14662:2010 (3rd ed. E/F) "Information technology — Open-edi Reference Model/Technologies de
l'information — Modèle de référence EDI-ouvert".
viii © ISO/IEC 2012 – All rights reserved
B
Open-edi Reference Model
U
S
Business
Operational View
I
Comply with
N
BOV RELATED
Business aspects
E Covered by
STANDARDS
of
S
business transactions
S
Viewed as
T
Inter-related
R
A
View
Functional Service
N
S
Information technology
Comply with
A
FSV RELATED
aspects of
C
Covered by
STANDARDS
Business transactions
T
I
O
N
S
Figure 1 — Open-edi environment – Open-edi Reference Model
ISO/IEC 14662:2010, Clause 5 states:
"The intention is that the sending, by an Open-edi Party, of information from a scenario, conforming to
Open-edi standards, shall allow the acceptance and processing of that information in the context of that
scenario by one or more Open-edi Parties by reference to the scenario and without the need for
agreement.
However, the legal requirements and/or liabilities resulting from the engagement of an organization in any
Open-edi transaction may be conditioned by the competent legal environment(s) of the formation of a
legal interchange agreement between the participating organizations. Open-edi Parties need to observe
rule-based behaviour and possess the ability to make commitments in Open-edi, (e.g., business,
operational, technical, legal, and/or audit perspectives)".
In addition, Annex A of the ISO/IEC 14662:2010 "Open-edi Reference Model" contains Figure A.1
"Relationships of Open-edi standardization areas with other standards and import of the legal environment".
This part of ISO/IEC 15944 is a BOV standard which focuses on the legal environment for the application of
privacy and/or data protection from an Open-edi perspective, and, as required follow-up standards
development in support of the "Open-edi Reference Model".
ISO/IEC 15944-5 is used to identify the means by which laws and regulations impacting scenarios and
scenario components, as external constraints, may be modelled and represented. The primary source of
these external constraints is jurisdictional domains.
ISO/IEC 15944-1 creates rules for creating the specification of external constraints when modelling business
transactions through scenarios, scenario attributes and scenario components. Several parts of ISO/IEC 15944
are used as input to this part. They are consolidated in this part of ISO/IEC 15944 in Annex B.
ISO/IEC 15944-1:2011 in Clause 7 "Guidelines for scoping Open-edi Scenarios" states in Clause 7.1:
"The approach taken is that of identifying the most primitive common components of a business
transaction and then moving from the general to the more detailed, the simplest aspects to the more
© ISO/IEC 2012 – All rights reserved ix
complex, from no external constraints on a business transaction to those which incorporate external
constraints, from no special requirements on functional services to specific requirements, and so on".
This part of ISO/IEC 15944 focuses on addressing commonly definable aspects of external constraints that
relate to privacy and data protection when the source is a jurisdictional domain. A useful characteristic of
external constraints is that, at the sectoral level, national and international levels, etc., focal points and
recognized authorities often already exist. The rules and common business practices in many sectoral areas
are already known. Use of this part of ISO/IEC 15944 (and related standards) addresses the transformation of
these external constraints (business rules) into specified, registered, and re-useable scenarios and scenario
components.
0.1.2 ISO/IEC 15944-1 “Business Agreement Semantic Descriptive Techniques” (“Business
Operational View (BOV”))
ISO/IEC 15944-1 states the requirements of the BOV aspects of Open-edi in support of electronic business
transactions. They shall be taken into account in the development of business semantic descriptive
techniques for modelling e-business transactions and components thereof as re-useable business objects.
They include:
commercial frameworks and associated requirements;
legal frameworks and associated requirements;
public policy requirements particularly those of a generic nature such as consumer protection, privacy,
accommodation of handicapped/disabled;
requirements arising from the need to support cultural adaptability. This includes meeting localization and
multilingual requirements, (e.g., as may be required by a particular jurisdictional domain or desired to
provide a good, service and/or right in a particular market. Here one needs the ability to distinguish, the
specification of scenarios, scenario components, and their semantics, in the context of making
commitments, between:
a) the use of unique, unambiguous and linguistically neutral identifiers (often as composite identifiers) at
the information technology (IT) interface level among the IT systems of participation parties on the
one hand; and, on the other,
b) their multiple human interface equivalent (HIE) expressions in a presentation form appropriate to the
Persons involved in the making of the resulting commitments.
Figure 2 shows an integrated view of these business operational requirements. It is based on Figure 3 from
ISO/IEC 15944-1. Since the focus of this part of ISO/IEC 15944 is that of external constraints for which
jurisdictional domains are the primary source these primary sources have been shaded in Figure 2 below).
x © ISO/IEC 2012 – All rights reserved
Sources of Requirements on the Business Operational View (BOV) aspects of Open-edi
which need to be integrated and/or taken into account
Business Transactions
Commercial Legal
(Open-edi based)
Framework & Framework &
Requirements Requirements
o Characteristics of Open-edi
Rule-Based
Commitment Exchange
Unambiguous Identification
Business Transaction
Model (BTM)
Key Components
Information
Technology
Public Policy
Person
Requirements
Req’mts
& Standards
(Privacy
Process
protection,
Consumer, c.) Data
Telecom-
Business Transaction Model:
munications
Classes of Constraints
Req’mts &
Specification, Identification &
Standards
Classification of Open-edi
scenarios (and components)
FSV Business Demands on
Sectoral (&
Open-edi Support Infrastructure
cross-sectoral)
Open-edi Scenario Templates
Req’mts
ISO & Other
Standards
Environments
Cultural Adaptability
Localization &
Multilingualism
(IT vs Human Interface)
Functional Services View (FSV)
Figure 2 — Integrated view - Business operational requirements: External constraints focus
0.2 Introducing the use of "Person", "organization" and "party" in the context of business
transaction and commitment exchange
In electronic business transactions, whether undertaken on a for profit or not-for-profit basis, the key element
is commitment exchange among Persons made among their Decision Making Applications (DMAs) of the
© ISO/IEC 2012 – All rights reserved xi
Information Technology Systems (IT Systems) acting on behalf of "Persons". "Persons" are the only entities
able to make commitments . Clause 0.4 in ISO/IEC 15944-1 states:
"When the ISO/IEC 14662 Open-edi Reference Model standard was being developed, the "Internet" and
"WWW" were an embryonic stage and their impact on private and public sector organizations was not
fully understood.”
The Business Operational View (BOV) was therefore defined as:
“perspective of business transactions limited to those aspects regarding the making of business
decisions and commitments among organizations which are needed for the description of a business
transaction".
The ISO/IEC 6523 definition of "organization" was used in the first edition (1997) of ISO/IEC 14662. The fact
that today Open-edi, through the Internet and WWW, also involves "individuals" has been taken into account
nd
in the development of the 2 and subsequent editions. ISO/IEC 15944-1 defines the term "commitment”.
However, the definition of the term "Open-edi Party" previously used proved not to be specific enough to
satisfy scenario specifications when the legal aspects of commitment were considered. In many instances
commitments were noted as being actually among IT systems acting under the direction of those legally
capable of making commitment, rather than actually the individuals acting in their own capacities. It was also
recognized that in some jurisdictions a commitment could be made by "artificial" persons such as corporate
bodies. Finally, it was noted that there are occasions where agents act, either under the instruction of a
principal, or as a result of requirement(s) laid down by a jurisdiction, or where an individual is prevented by a
relevant jurisdiction from being able to make a commitment in their own right, (e.g., a minor), and this must be
incorporated into the standard.
To address these extended requirements the additional concept and term of "Person", has been defined. A
Person is defined such that they are capable of having the appropriate legal and regulatory constraints applied
to them.
There are three categories of Person as a role player in Open-edi, namely: (1) the Person as "individual", (2)
the Person as "organization", and (3) the Person as "public administration". There are also three basic (or
primitive) roles of Persons in business transactions, namely: "buyer", "seller", and "regulator".
When modelling business transactions, jurisdictional domains prescribe their external constraints in the role of
"regulator" and execute them as "public administration". {See further below Clause 6.3}
While “public administration” is one of the three distinct sub-types of Person, most of the rules applicable to
“organization” also apply to “public administration”. In addition, an unincorporated seller is also deemed to
function as an “organization”. Consequently, the use of “organization” throughout this part of ISO/IEC 15944
also covers “public administration”. Where it is necessary to bring forward specific rules, constraints,
properties, etc., which apply specifically to “public administration”, this is stated explicitly.
The requirements of jurisdictional domains are specified through the use of sets of "Codes representing X.”
Such sets of codes are created and maintained by Source Authorities via a rulebase with resulting coded
domains in the form of data elements whose permitted values represent predefined semantics in a structured
form, i.e., as a type of semantic component. Jurisdictional domains serve as Source Authorities for such
coded domains.
These three categories of Person also identify the possible Source Authorities for coded domains. Source
Authorities for coded domains are therefore either "organizations" or "public administrations".
Throughout this part of ISO/IEC 15944:
rd
See further Clause 5.2 "Functional Services View" in ISO/IEC 14662:2010 "Open-edi Reference Model" (3 edition).
The text in this section is based on existing text in Section "0.3" in ISO/IEC 15944-1:2011 and ISO/IEC 14662:2010
rd
(3 edition).
xii © ISO/IEC 2012 – All rights reserved
the use of Person with a capital "P" represents Person as a defined term, i.e., as the entity within an
Open-edi Party that carries the legal responsibility for making commitment(s);
"individual", "organization", and "public administration" are defined terms representing the three common
sub-types of "Person"; and,
the words "person(s)" and/or "party(ies)" are used in their generic contexts independent of roles of
"Person" as defined in the ISO/IEC 14662 and ISO/IEC 15944-1 standards. A "party" to a business
transaction has the properties and behaviours of a "Person".
0.3 Importance and role of terms and definitions
ISO/IEC Directives Part 2 provide for “Terms and definitions” as a “Technical normative element,” necessary
for the understanding of certain terms used in the document, where the words have special, extended or
technical meaning.
The ISO/IEC 15944 multipart standard sets out the processes for achieving a common understanding of the
Business Operational View (BOV) from commercial, legal, ICT, public policy and cross-sectoral perspectives.
It is therefore important to check and confirm that a “common understanding” in any one of these domains is
also unambiguously understood as identical in the others.
This sub-clause is included in each part of ISO/IEC 15944 to emphasize that harmonized terms and
definitions are essential to the continuity of the overall standard. Definitions and their assigned terms should
be established as early as possible in the development process. Comments on any definition/term pair should
address the question of changes needed to avoid possible misinterpretation. Definitions may need to be
amended/improved as part of the harmonization of definitions and their assigned terms among the various
parts of ISO/IEC 15944.
In order to minimize ambiguity in the definitions and their associated terms, each definition and its associated
term has been made available in at least one language other than English in the part in which it is introduced.
In this context, it is noted that ISO/IEC 15944-7 eBusiness vocabulary already also contains human interface
equivalents (HIEs) in ISO Chinese, ISO French, and ISO Russian.
Normative Annex A “Consolidated list of terms and definitions with cultural adaptability: ISO English and ISO
French language equivalency” is derived from Clause 3 of each part of ISO/IEC 15944. Annex A is repeated
in each part of ISO/IEC 15944 as a convenient reference. The designation ISO before a natural language
refers to the use of that natural language in ISO standards, and has no other meaning.
0.4 Importance of the two classes of constraints of the Business Transaction Model (BTM)
The BTM has two classes of constraints; namely:
1) those which are "self-imposed" and agreed to as commitments among the parties themselves, i.e.,
"internal constraints"; and,
2) those which are imposed on the parties to a business transaction based on the nature of the good, service
and/or rights exchanged, the nature of the commitment made among the parties (including ability to make
All the terms and definitions of the current editions of the ISO/IEC 14669 Open-edi Reference Model and the
multipart ISO/IEC 15944 eBusiness standard have been consolidated in ISO/IEC 15944-7:2009. A primary reason for
having “Terms and definitions” in a standard is because one cannot assume that there exists a common understanding,
worldwide, for a specific concept. And even if one assumes that such an understanding exists, then having such a
common definition in Clause 3 serves to formally and explicitly affirm (re-affirm) such a common understanding, i.e.,
ensure that all parties concerned share this common understanding as stated through the text of the definitions in
Clause 3.
Canada has committed to maintain this comprehensive list in a database as the reference file for Annex A. This
Annex A reference file will insure the consistency of definitions and their assigned terms among the various parts in the
on-going harmonization effort. {See also ISO/IEC 15944-7 e-Business Vocabulary}
© ISO/IEC 2012 – All rights reserved xiii
commitments, the location, inf
...
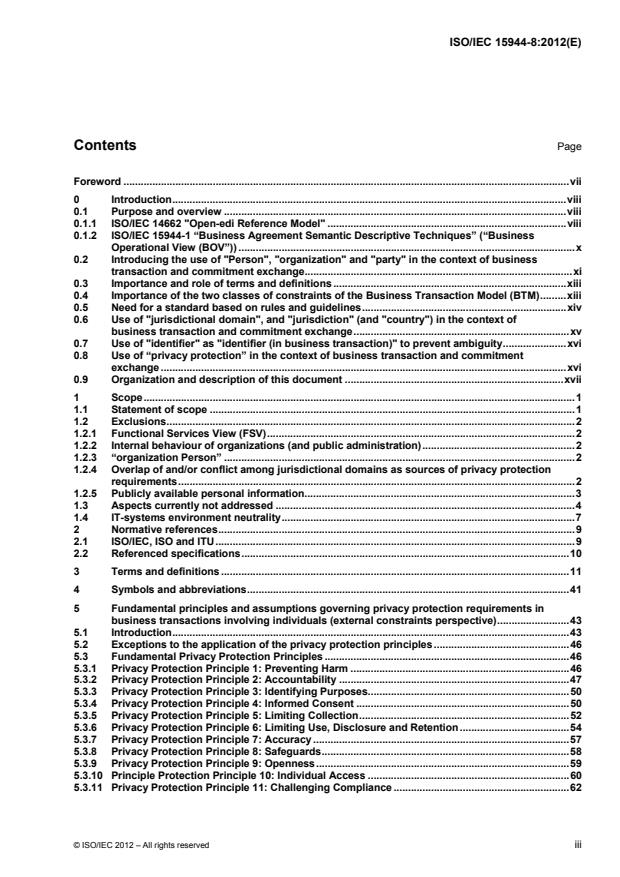
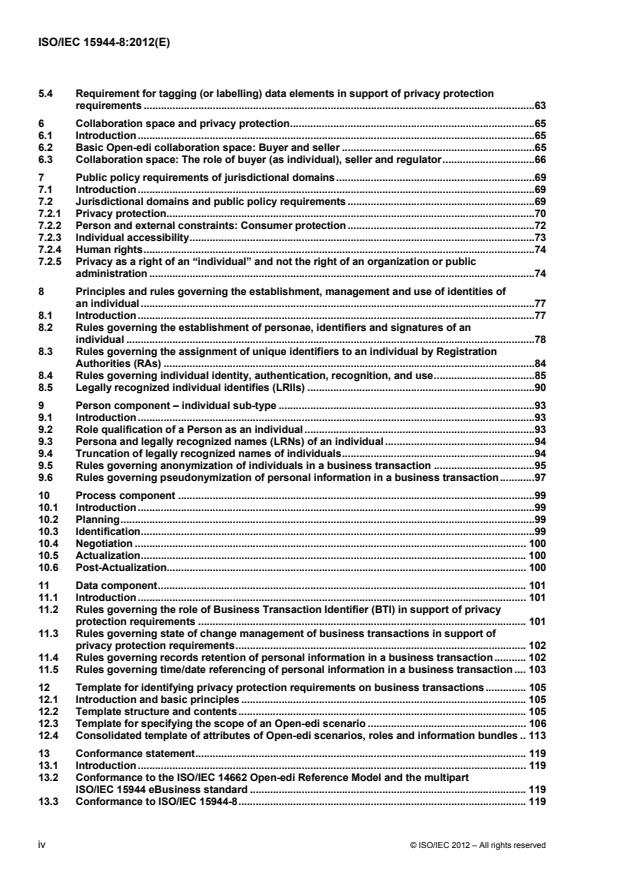
Questions, Comments and Discussion
Ask us and Technical Secretary will try to provide an answer. You can facilitate discussion about the standard in here.
Loading comments...