IEC 62325-451-2:2014/COR1:2016
(Corrigendum)Corrigendum 1 - Framework for energy market communications - Part 451-2: Scheduling business process and contextual model for CIM European market
Corrigendum 1 - Framework for energy market communications - Part 451-2: Scheduling business process and contextual model for CIM European market
Corrigendum 1 - Cadre pour les communications pour le marché de l'énergie - Partie 451-2: Processus métier de programmation et modèle contextuel pour le marché européen CIM
General Information
Relations
Standards Content (Sample)
IEC 2016
INTERNATIONAL ELECTROTECHNICAL COMMISSION
COMMISSION ÉLECTROTECHNIQUE INTERNATIONALE
____________
IEC 62325-451-2 IEC 62325-451-2
Edition 1.0 2014-05 Édition 1.0 2014-05
FRAMEWORK FOR ENERGY MARKET CADRE POUR LES COMMUNICATIONS POUR LE
COMMUNICATIONS – MARCHÉ DE L'ÉNERGIE –
Part 451-2: Scheduling business process and Partie 451-2: Processus métier de
contextual model for CIM European market programmation et modèle contextuel pour le
marché européen CIM
CO RRI G ENDU M 1
Corrections to the French version appear after the English text.
Les corrections à la version française sont données après le texte anglais.
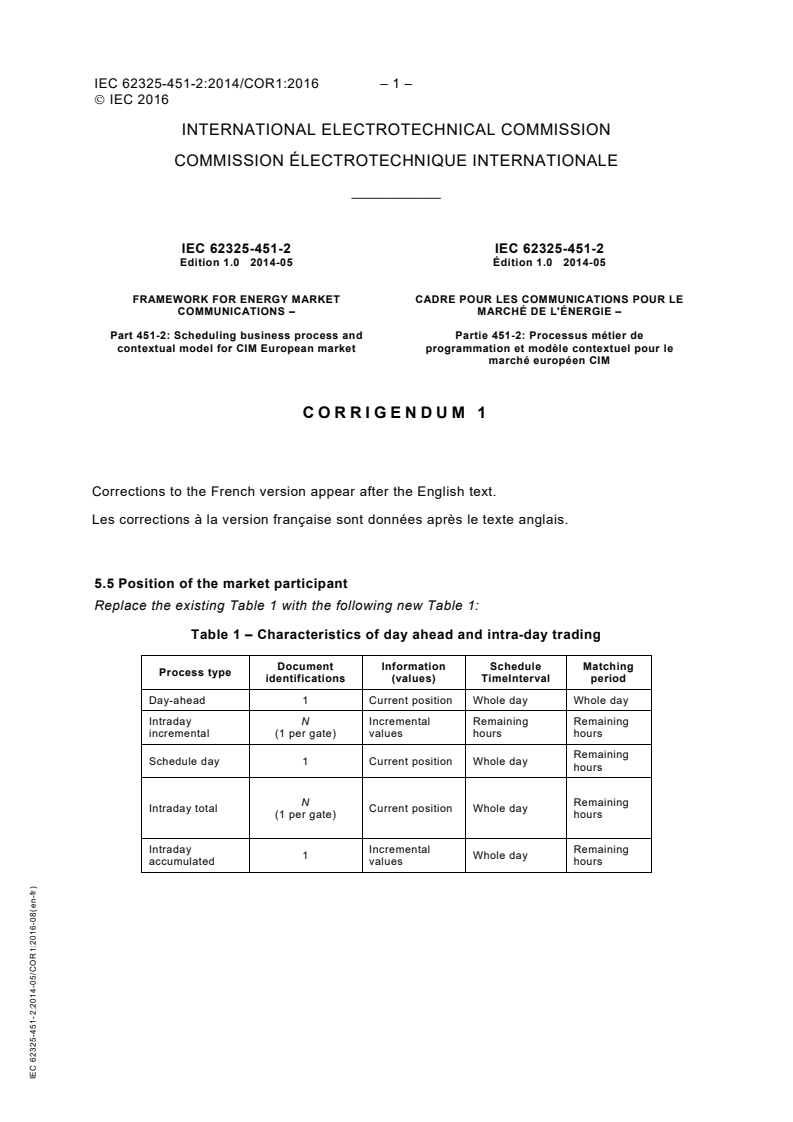
5.5 Position of the market participant
Replace the existing Table 1 with the following new Table 1:
Table 1 – Characteristics of day ahead and intra-day trading
Document Information Schedule Matching
Process type
identifications (values) TimeInterval period
Day-ahead 1 Current position Whole day Whole day
Intraday N Incremental Remaining Remaining
incremental (1 per gate) values hours hours
Remaining
Schedule day 1 Curren
...
This May Also Interest You
IEC TR 61850-90-30:2025, which is a Technical Report, describes extensions of the SCL Substation/Process Section allowing the creation of a comprehensive, IED and hardware independent specification of an IEC 61850 based power system.
It addresses how to:
• decompose functions in SCL
• show function classifications in SCL
• relate functions with the SCL Substation and Process Section
• relate functions to Logical Nodes and IEDs/Specification IEDs
• present information flow between functions in a hardware/implementation independent way
• position Functions in relation to "Application Schemes", "Distributed Functions", "Protection Schemes"
• consider the relationship to Basic Application Profiles (BAP) defined in IEC TR 61850-7-6
The document addresses the engineering process as far as it is related to the specification of Functions and their instantiation in IEC 61850 based power system. This includes the impact on the SCL Process Section during system configuration.
The engineering process related to the definition of Applications and their instantiation is addressed in the Basic Application Profile Document (BAP) in IEC TR 61850-7-6.
The System Configuration process is described in IEC 61850-6.
Modifications and extensions of SCL are done in a way to guarantee backwards compatibility.
In addition, this document introduces:
• Some further elements to SCL that improve the content and usefulness of SSD files and facilitate the handling of SCL files for engineering purposes,
• New variants of IED specific files: ISD file and FSD files,
• Evolution of the engineering rights management, to first improve the usage of SED and add a new concept of System Configuration Collaboration (SCC file) which allows collaboration on the same project with different engineers.
- Technical report184 pagesEnglish languagesale 15% off
IEC TR 61850-90-21:2025, which is a Technical Report, aims to provide background information, use cases, data models and guidance on the application of such a technique.
This document will
1) describe the principles of fault location based on travelling waves aided by communications;
2) specify use cases for this method under the following application scenarios:
a) Single-ended fault location,
b) Double-ended fault location through communications between two devices,
c) Double-ended fault location with communications to a master station,
d) Wide area fault location applications,
e) Pulse radar echo method,
f) Substation integration with other fault location and disturbance recording functions,
g) Testing and calibration;
3) describe the information model for each use case;
4) give guidance on scheme configuration.
- Technical report98 pagesEnglish languagesale 15% off
IEC 62746-4:2024 describes CIM profiles for Demand-Side Resource Interface and is based on the use case shown in Annex A of this document. Schemas associated with this document were generated using the CIM101 UML and leverages the Market package. This document defines profiles complimentary to other standards, namely those in IEC 61970, IEC 61968, and IEC 62325.
- Standard153 pagesEnglish and French languagesale 15% off
IEC TR 61850-90-22:2024, which is a Technical Report, aims to provide analysis, principles, use cases and guidance on how to use GOOSE/SV static-routing or auto-routing based on System Configuration Description (SCD) file to automated manage the substation network while without changing the requirements of IEDs. Furthermore, this document also intends to give novel practices on network and GOOSE/SV path condition monitoring which support visualization and supervision from higher level application side.
Using the concepts developed in the IETF's Transparent Interconnection of Lots of Links (TRILL) using IS-IS protocol that is defined in RFC 6326 and ISO/IEC 10589 standards, this document defines network and system management data object models that are specific to power system operations. These data objects will be used to monitor the health of networks and systems, to detect abnormal behaviours of IEDs which contradict SCD file, such as unexpected IEDs or unexpected GOOSE/SV flows, and to support the management of the performance and reliability of the information infrastructure
- Technical report109 pagesEnglish languagesale 15% off
IEC TR 61850-7-6:2024, which is a Technical Report, is focused on building application / function profiles and specifies a methodology to define Basic Application Profiles (BAPs), in textual documents (edition 1, 2019) or in a machine processable SCL format (current edition). These Basic Application Profiles provide a framework for interoperable interaction within or between typical substation automation functions. BAPs are intended to define a subset of features of IEC 61850 in order to facilitate interoperability in a modular way in practical applications.
It is the intention of this document to provide a common and generic way to describe the functional behavior of a specific application function in the domain of power utility automation systems as a common denominator of various possible interpretations/implementations of using IEC 61850.
The guidelines in this document are based on the functional definitions of:
• IEC 61850-5, Communication requirements for functions and device models, which gives a comprehensive overview of all application functions needed in a state-of-the-art substation automation implementation.
• IEC TR 61850-7-500, Basic information and communication structure – Use of logical nodes for modelling application functions and related concepts and guidelines for substations, which illustrates and explains application functions for the substation/protection domain of Logical Nodes in modelling simple and complex functions, to improve common understanding in modelling and data exchange, and finally to lead to interoperable implementations.
• IEC TR 61850-90-3, Using IEC 61850 for condition monitoring diagnosis and analysis, which gives use cases and data modelling for condition monitoring diagnosis and analysis functions for substation and power grid facilities.
• IEC TR 61850-90-30, IEC 61850 Function Modelling in SCL, which describes extensions of the SCL Substation/Process Section allowing to create a comprehensive, IED and hardware independent specification of an IEC 61850 based power system.
This document does not describe the applications and respective implementation requirements; the focus is on their typical information exchange including data and communication services and engineering conventions.
This second edition cancels and replaces the first edition published in 2019. This edition constitutes a technical revision.
This edition includes the following significant technical changes with respect to the previous edition:
a) New Clause 5 added to describe the way to express Basic Application Profile in SCL files;
b) New Annex F and Annex G added to list specific use cases and roles of the Concept Definition Tool.
- Technical report144 pagesEnglish languagesale 15% off
- Standard183 pagesEnglish and French languagesale 15% off
IEC 61850-6:2009 specifies a file format for describing communication-related IED (Intelligent Electronic Device) configurations and IED parameters, communication system configurations, switch yard (function) structures, and the relations between them. The main purpose of this format is to exchange IED capability descriptions, and SA system descriptions between IED engineering tools and the system engineering tool(s) of different manufacturers in a compatible way. The main changes with respect to the previous edition are as follows:
- functional extensions added based on changes in other Parts of IEC 61850, especially in IEC 61850-7-2 and IEC 61850-7-3;
- functional extensions concerning the engineering process, especially for configuration data exchange between system configuration tools, added;
- clarifications and corrections.
This publication is of core relevance for Smart Grid.
- Standard291 pagesEnglish languagesale 15% off
- Standard215 pagesEnglish languagesale 15% off
- Standard269 pagesEnglish languagesale 15% off
IEC 61970-457:2024 specifies a standard interface for exchanging dynamic model information needed to support the analysis of the steady state stability (small-signal stability) and/or transient stability of a power system or parts of it. The schema(s) for expressing the dynamic model information are derived directly from the CIM, more specifically from IEC 61970-302.
The scope of this document includes only the dynamic model information that needs to be exchanged as part of a dynamic study, namely the type, description and parameters of each control equipment associated with a piece of power system equipment included in the steady state solution of a complete power system network model. Therefore, this profile is dependent upon other standard profiles for the equipment as specified in IEC 61970-452: CIM static transmission network model profiles, the topology, the steady state hypothesis and the steady state solution (as specified in IEC 61970-456: Solved power system state profiles) of the power system, which bounds the scope of the exchange. The profile information described by this document needs to be exchanged in conjunction with IEC 61970-452 and IEC 61970-456 profiles’ information to support the data requirements of transient analysis tools. IEC 61970-456 provides a detailed description of how different profile standards can be combined to form various types of power system network model exchanges.
This document supports the exchange of the following types of dynamic models:
• standard models: a simplified approach to exchange, where models are contained in predefined libraries of classes interconnected in a standard manner that represent dynamic behaviour of elements of the power system. The exchange only indicates the name of the model along with the attributes needed to describe its behaviour.
• proprietary user-defined models: an exchange that would provide users the ability to exchange the parameters of a model representing a vendor or user proprietary device where an explicit description of the model is not described in this document. The connections between the proprietary models and standard models are the same as described for the standard models exchange. Recipient of the data exchange will need to contact the sender for the behavioural details of the model.
This document builds on IEC 61970-302, CIM for dynamics which defines the descriptions of the standard dynamic models, their function block diagrams, and how they are interconnected and associated with the static network model. This type of model information is assumed to be pre-stored by all software applications hence it is not necessary to be exchanged in real-time or as part of a dynamics model exchange.
This second edition cancels and replaces the first edition published in 2021. This edition constitutes a technical revision.
This edition includes the following significant technical changes with respect to the previous edition:
a) The majority of issues detected in IEC 61970-302:2018 and fixed in IEC 61970-302:2022 led to update of this document;
b) IEEE 421.5-2016 on Excitation systems is fully covered;
c) IEEE turbine report from 2013 was considered and as a result a number of gas, steam and hydro turbines/governors are added;
d) IEC 61400-27-1:2020 on wind turbines is fully incorporated;
e) WECC Inverter-Based Resource (IBR) models, Hybrid STATCOM models and storage models are added;
f) The user defined models approach was enhanced in IEC 61970-302:2022 adding a model which enables modelling of a detailed dynamic model. This results in the creation of two additional profiles in this document. These are the Detailed Model Configuration profile and Detailed Model Parameterisation profile;
g) A model to enable exchange of simulation results was added in IEC 61970-302:2022. This results in the creation of two additional profiles in this document. These are the Simulation Settings profile and Simulation Results profile;
h) The work on the
- Standard1549 pagesEnglish and French languagesale 15% off
IEC TR 61850-80-5:2024, which is a Technical Report, specifies the mapping rules for building and configuring a system using both IEC 61850 and IEC 61158-6 (Industrial communication networks - Fieldbus specification, CPF Type 15, Modbus) protocols by utilizing gateways between IEC 61850 and IEC 61158-6 IEDs / subsystems. The objective is to enable operational run-time data exchange among these IEDs / subsystems, and to automate the configuration of a gateway as much as possible.
Please note that for the purposes of this document, "Modbus" is used to represent both serial Modbus (Modbus RTU) and IEC 61158-6 (Modbus TCP).
Within the capability of each protocol, some configuration attributes (IEC 61850-7-3:2010+AMD1:2020 attributes with functional constraint CF) are also mapped in addition to the operational real-time data.
The rules specified in this document are based on the published standards and do not make any proposed changes to IEC 61850 or 61158-6. This standard does not specify any rules for an IEC 61850 IED to directly communicate with a Modbus IED and vice versa, except through a gateway.
This document does not mandate which data items that a particular IED shall support, regardless of whether the implementation uses Modbus or IEC 61850. Instead this document provides rules specifying how a gateway maps any given data item from one protocol to the other, given that the data item is already available and is transmitted using one of the protocols.
Similarly, this document does not mandate which mapping rules a given gateway shall support. When this document is republished as a Technical Specification, conformance requirements will be identified.
This document recognizes that there will be situations in which a user will require that a gateway perform non-standard protocol mappings. Non-standard mappings are outside the scope of this document.
This document also recognizes that gateways typically manipulate the data passing through them in a variety of ways. Some of these functions include alarm trigger grouping, data suppression, interlocking and command blocking. Conformance to this document does not preclude a gateway from performing such functions, even though this document primarily specifies "straight through" mapping of Modbus data to IEC 61850-7-3:2010+AMD1:2020 data. Subclause 7.4 of this document describes how some of these functions may be specified to a gateway by a mapping tool using equation notation in XML. However, some of these functions may be too complex for a mapping tool to specify in an automated manner.
The mapping architecture for the exchange of the run-time information consists of four parts:
1) Conceptual architecture of a gateway and associated use case
2) Mapping of the information model (Assign semantic to the Modbus data)
3) Mapping of the data (which is in fact part of the information model)
4) Mapping of the services (out of scope for this document)
- Technical report47 pagesEnglish languagesale 15% off
IEC 61970-302:2024 specifies a Dynamics package which contains part of the CIM to support the exchange of models between software applications that perform analysis of the steady-state stability (small-signal stability) or transient stability of a power system as defined by IEEE / CIGRE, Definition and classification of power system stability IEEE/CIGRE joint task force on stability terms and definitions.
The model descriptions in this document provide specifications for each type of dynamic model as well as the information that needs to be included in dynamic case exchanges between planning/study applications.
The scope of the CIM Dynamics package specified in this document includes:
• standard models: a simplified approach to describing dynamic models, where models representing dynamic behaviour of elements of the power system are contained in predefined libraries of classes which are interconnected in a standard manner. Only the names of the selected elements of the models along with their attributes are needed to describe dynamic behaviour.
• proprietary user-defined models: an approach providing users the ability to define the parameters of a dynamic behaviour model representing a vendor or user proprietary device where an explicit description of the model is not provided by this document. The same libraries and standard interconnections are used for both proprietary user-defined models and standard models. The behavioural details of the model are not documented in this document, only the model parameters.
• A model to enable exchange of models’ descriptions. This approach can be used to describe user defined and standard models.
• A model to enable exchange of simulation results.
This second edition cancels and replaces the first edition published in 2018. This edition constitutes a technical revision.
This edition includes the following significant technical changes with respect to the previous edition:
a) The majority of issues detected in IEC 61970-302:2018 are addressed;
b) IEEE 421.5-2016 on Excitation systems is fully covered;
c) The IEEE turbine report from 2013 was considered and as a result a number of gas, steam and hydro turbines/governors are added;
d) IEC 61400-27-1:2020 on wind turbines is fully incorporated;
e) WECC Inverter-Based Resource (IBR) models, Hybrid STATCOM models and storage models are added;
f) The user defined models are enhanced with a model which enables modelling of detailed dynamic model;
g) A model to enable exchange of simulation results is added;
h) The work on the HVDC models is not complete. The HVDC dynamics models are a complex domain in which there are no models that are approved or widely recognised on international level, i.e. there are only project-based models. At this stage IEC 61970-302:2022 only specifies some general classes. However, it is recognised that better coverage of HVDC will require a further edition of this document;
i) Models from IEEE 1547-2018 "IEEE Standard for Interconnection and Interoperability of Distributed Energy Resources with Associated Electric Power Systems Interfaces" are added.
j) Statements have been added to certain figures, tables, schemas, and enumerations throughout the document that indicate that they are reproduced with the permission of the UCA International User Group (UCAIug). These items are derived from the CIM.
- Standard1752 pagesEnglish and French languagesale 15% off






Questions, Comments and Discussion
Ask us and Technical Secretary will try to provide an answer. You can facilitate discussion about the standard in here.