ISO/IEC 27002:2022
(Main)Information security, cybersecurity and privacy protection — Information security controls
Information security, cybersecurity and privacy protection — Information security controls
This document provides a reference set of generic information security controls including implementation guidance. This document is designed to be used by organizations: a) within the context of an information security management system (ISMS) based on ISO/IEC27001; b) for implementing information security controls based on internationally recognized best practices; c) for developing organization-specific information security management guidelines.
Sécurité de l'information, cybersécurité et protection de la vie privée — Mesures de sécurité de l'information
Le présent document fournit un ensemble de référence de mesures de sécurité de l'information génériques, y compris des recommandations de mise en œuvre. Le présent document est conçu pour être utilisé par les organisations: a) dans le contexte d'un système de gestion de la sécurité de l'information (SMSI) selon l'ISO/IEC 27001; b) pour la mise en œuvre de mesures de sécurité de l'information basées sur les bonnes pratiques reconnues au niveau international; c) pour l'élaboration des recommandations de gestion de la sécurité de l'information spécifiques à une organisation.
Informacijska varnost, kibernetska varnost in varovanje zasebnosti - Kontrole informacijske varnosti
General Information
- Status
- Published
- Publication Date
- 14-Feb-2022
- Drafting Committee
- ISO/IEC JTC 1/SC 27/WG 1 - Information security management systems
- Current Stage
- 6060 - International Standard published
- Start Date
- 15-Feb-2022
- Due Date
- 26-Mar-2022
- Completion Date
- 15-Feb-2022
Relations
- Effective Date
- 09-Feb-2026
- Effective Date
- 09-Feb-2026
- Effective Date
- 07-Apr-2018
Overview - ISO/IEC 27002:2022 (Information security controls)
ISO/IEC 27002:2022 is an international guidance standard that provides a comprehensive reference set of information security controls and implementation guidance. It is designed to be used within an Information Security Management System (ISMS) based on ISO/IEC 27001, for implementing controls according to internationally recognized best practices, or for creating organization‑specific information security policies and procedures. The 2022 edition reorganizes controls into themes covering organizational, people, physical and technological controls.
Key topics and technical requirements
ISO/IEC 27002:2022 organizes controls and guidance across practical security domains. Major topics include:
- Organizational controls: policies, roles and responsibilities, asset inventory, classification, information transfer, supplier security, cloud services, legal and regulatory requirements, and incident management.
- People controls: screening, employment terms, awareness, training, remote working, reporting and disciplinary processes.
- Physical controls: perimeters, physical entry, secure areas, equipment protection, environmental threats, clear desk/screen, and secure disposal.
- Technological controls: endpoint security, privileged access, authentication, access restriction, malware protection, vulnerability management, configuration and patch management, cryptography, backups, logging and monitoring, network security, secure development lifecycle, and application security.
- Privacy and PII protection: controls for protecting personal data and aligning privacy measures with information security practices.
- Operational resilience: business continuity readiness, disruption management, evidence collection and learning from incidents.
The standard emphasizes implementation guidance rather than prescriptive technical specifications - helping organizations select and tailor controls to risk and context.
Applications - who uses it and why
ISO/IEC 27002 is used by:
- CISOs and security managers to design and benchmark controls within an ISMS.
- IT and cloud architects to apply secure architecture, cloud and network controls.
- Developers and DevSecOps teams for secure development practices and testing.
- Procurement and vendor managers to manage supplier and supply‑chain security.
- Compliance officers and auditors to assess control coverage against best practices.
- Consultants and implementers to map control sets to organizational risk profiles.
Practical uses include control selection for ISO/IEC 27001 certification, building control frameworks, preparing incident response playbooks, enforcing access and identity controls, and incorporating privacy protections.
Related standards
- ISO/IEC 27001 - ISMS requirements (primary companion standard)
- Other ISO/IEC 27000‑series guidance (risk management, audit and implementation guidance)
Keywords: ISO/IEC 27002:2022, information security controls, cybersecurity, privacy protection, ISMS, ISO/IEC 27001, control implementation, information security best practices.
ISO/IEC 27002:2022 - Information security, cybersecurity and privacy protection — Information security controls Released:3/23/2022
REDLINE ISO/IEC 27002:2022 - Information security, cybersecurity and privacy protection — Information security controls Released:3/23/2022
REDLINE ISO/IEC 27002:2022 - Information security, cybersecurity and privacy protection — Information security controls Released:9. 01. 2023
ISO/IEC 27002:2022 - Information security, cybersecurity and privacy protection — Information security controls Released:9. 01. 2023
REDLINE ISO/IEC 27002:2022 - Information security, cybersecurity and privacy protection — Information security controls Released:9. 01. 2023
Get Certified
Connect with accredited certification bodies for this standard

BSI Group
BSI (British Standards Institution) is the business standards company that helps organizations make excellence a habit.

Bureau Veritas
Bureau Veritas is a world leader in laboratory testing, inspection and certification services.

DNV
DNV is an independent assurance and risk management provider.
Sponsored listings
Frequently Asked Questions
ISO/IEC 27002:2022 is a standard published by the International Organization for Standardization (ISO). Its full title is "Information security, cybersecurity and privacy protection — Information security controls". This standard covers: This document provides a reference set of generic information security controls including implementation guidance. This document is designed to be used by organizations: a) within the context of an information security management system (ISMS) based on ISO/IEC27001; b) for implementing information security controls based on internationally recognized best practices; c) for developing organization-specific information security management guidelines.
This document provides a reference set of generic information security controls including implementation guidance. This document is designed to be used by organizations: a) within the context of an information security management system (ISMS) based on ISO/IEC27001; b) for implementing information security controls based on internationally recognized best practices; c) for developing organization-specific information security management guidelines.
ISO/IEC 27002:2022 is classified under the following ICS (International Classification for Standards) categories: 03.100.70 - Management systems; 35.030 - IT Security. The ICS classification helps identify the subject area and facilitates finding related standards.
ISO/IEC 27002:2022 has the following relationships with other standards: It is inter standard links to EN ISO 27799:2026, EN ISO/IEC 27019:2025, ISO/IEC 27002:2013. Understanding these relationships helps ensure you are using the most current and applicable version of the standard.
ISO/IEC 27002:2022 is available in PDF format for immediate download after purchase. The document can be added to your cart and obtained through the secure checkout process. Digital delivery ensures instant access to the complete standard document.
Standards Content (Sample)
INTERNATIONAL ISO/IEC
STANDARD 27002
Third edition
2022-02
Corrected version
2022-03
Information security, cybersecurity
and privacy protection — Information
security controls
Sécurité de l'information, cybersécurité et protection de la vie
privée — Mesures de sécurité de l'information
Reference number
© ISO/IEC 2022
© ISO/IEC 2022
All rights reserved. Unless otherwise specified, or required in the context of its implementation, no part of this publication may
be reproduced or utilized otherwise in any form or by any means, electronic or mechanical, including photocopying, or posting on
the internet or an intranet, without prior written permission. Permission can be requested from either ISO at the address below
or ISO’s member body in the country of the requester.
ISO copyright office
CP 401 • Ch. de Blandonnet 8
CH-1214 Vernier, Geneva
Phone: +41 22 749 01 11
Email: copyright@iso.org
Website: www.iso.org
Published in Switzerland
ii
© ISO/IEC 2022 – All rights reserved
Contents Page
Foreword . vi
Introduction .vii
1 Scope . 1
2 Normative references . 1
3 Terms, definitions and abbreviated terms . 1
3.1 Terms and definitions . 1
3.2 Abbreviated terms . 6
4 Structure of this document .7
4.1 Clauses . 7
4.2 Themes and attributes . 8
4.3 Control layout . 9
5 Organizational controls . 9
5.1 Policies for information security . . 9
5.2 Information security roles and responsibilities . 11
5.3 Segregation of duties. 12
5.4 Management responsibilities .13
5.5 Contact with authorities . 14
5.6 Contact with special interest groups . 15
5.7 Threat intelligence .15
5.8 Information security in project management . 17
5.9 Inventory of information and other associated assets . 18
5.10 Acceptable use of information and other associated assets . 20
5.11 Return of assets . 21
5.12 Classification of information . 22
5.13 Labelling of information .23
5.14 Information transfer . 24
5.15 Access control . 27
5.16 Identity management . 29
5.17 Authentication information . 30
5.18 Access rights . 32
5.19 Information security in supplier relationships . 33
5.20 Addressing information security within supplier agreements . 35
5.21 Managing information security in the ICT supply chain . 37
5.22 Monitoring, review and change management of supplier services .39
5.23 Information security for use of cloud services . 41
5.24 Information security incident management planning and preparation . 43
5.25 Assessment and decision on information security events . 45
5.26 Response to information security incidents . 45
5.27 Learning from information security incidents .46
5.28 Collection of evidence . . 47
5.29 Information security during disruption .48
5.30 ICT readiness for business continuity .48
5.31 Legal, statutory, regulatory and contractual requirements .50
5.32 Intellectual property rights . 51
5.33 Protection of records . 53
5.34 Privacy and protection of PII .54
5.35 Independent review of information security . 55
5.36 Compliance with policies, rules and standards for information security .56
5.37 Documented operating procedures . 57
6 People controls .58
6.1 Screening .58
6.2 Terms and conditions of employment . 59
iii
© ISO/IEC 2022 – All rights reserved
6.3 Information security awareness, education and training .60
6.4 Disciplinary process . 62
6.5 Responsibilities after termination or change of employment.63
6.6 Confidentiality or non-disclosure agreements .63
6.7 Remote working .65
6.8 Information security event reporting.66
7 Physical controls .67
7.1 Physical security perimeters . 67
7.2 Physical entry .68
7.3 Securing offices, rooms and facilities . 70
7.4 Physical security monitoring . . 70
7.5 Protecting against physical and environmental threats . 71
7.6 Working in secure areas .72
7.7 Clear desk and clear screen .73
7.8 Equipment siting and protection .74
7.9 Security of assets off-premises .75
7.10 Storage media . 76
7.11 Supporting utilities .77
7.12 Cabling security . 78
7.13 Equipment maintenance .79
7.14 Secure disposal or re-use of equipment .80
8 Technological controls .81
8.1 User endpoint devices . 81
8.2 Privileged access rights .83
8.3 Information access restriction .84
8.4 Access to source code .86
8.5 Secure authentication .87
8.6 Capacity management .89
8.7 Protection against malware .90
8.8 Management of technical vulnerabilities . 92
8.9 Configuration management . 95
8.10 Information deletion . 97
8.11 Data masking .98
8.12 Data leakage prevention .100
8.13 Information backup.101
8.14 Redundancy of information processing facilities .102
8.15 Logging .103
8.16 Monitoring activities .106
8.17 Clock synchronization .108
8.18 Use of privileged utility programs .109
8.19 Installation of software on operational systems . 110
8.20 Networks security . 111
8.21 Security of network services .112
8.22 Segregation of networks .113
8.23 Web filtering . 114
8.24 Use of cryptography .115
8.25 Secure development life cycle . 117
8.26 Application security requirements . 118
8.27 Secure system architecture and engineering principles .120
8.28 Secure coding.122
8.29 Security testing in development and acceptance .124
8.30 Outsourced development .126
8.31 Separation of development, test and production environments.127
8.32 Change management .128
8.33 Test information .129
8.34 Protection of information systems during audit testing .130
Annex A (informative) Using attributes . 132
iv
© ISO/IEC 2022 – All rights reserved
Annex B (informative) Correspondence of ISO/IEC 27002:2022 (this document) with ISO/
IEC 27002:2013 . 143
Bibliography . 150
v
© ISO/IEC 2022 – All rights reserved
Foreword
ISO (the International Organization for Standardization) and IEC (the International Electrotechnical
Commission) form the specialized system for worldwide standardization. National bodies that are
members of ISO or IEC participate in the development of International Standards through technical
committees established by the respective organization to deal with particular fields of technical
activity. ISO and IEC technical committees collaborate in fields of mutual interest. Other international
organizations, governmental and non-governmental, in liaison with ISO and IEC, also take part in the
work.
The procedures used to develop this document and those intended for its further maintenance
are described in the ISO/IEC Directives, Part 1. In particular, the different approval criteria
needed for the different types of document should be noted. This document was drafted in
accordance with the editorial rules of the ISO/IEC Directives, Part 2 (see www.iso.org/directives or
www.iec.ch/members_experts/refdocs).
Attention is drawn to the possibility that some of the elements of this document may be the subject
of patent rights. ISO and IEC shall not be held responsible for identifying any or all such patent
rights. Details of any patent rights identified during the development of the document will be in the
Introduction and/or on the ISO list of patent declarations received (see www.iso.org/patents) or the IEC
list of patent declarations received (see patents.iec.ch).
Any trade name used in this document is information given for the convenience of users and does not
constitute an endorsement.
For an explanation of the voluntary nature of standards, the meaning of ISO specific terms and
expressions related to conformity assessment, as well as information about ISO’s adherence to
the World Trade Organization (WTO) principles in the Technical Barriers to Trade (TBT) see
www.iso.org/iso/foreword.html. In the IEC, see www.iec.ch/understanding-standards.
’This document was prepared by Joint Technical Committee ISO/IEC JTC 1, Information technology,
Subcommittee SC 27, Information security, cybersecurity and privacy protection.
This third edition cancels and replaces the second edition (ISO/IEC 27002:2013), which has been
technically revised. It also incorporates the Technical Corrigenda ISO/IEC 27002:2013/Cor. 1:2014 and
ISO/IEC 27002:2013/Cor. 2:2015.
The main changes are as follows:
— the title has been modified;
— the structure of the document has been changed, presenting the controls using a simple taxonomy
and associated attributes;
— some controls have been merged, some deleted and several new controls have been introduced. The
complete correspondence can be found in Annex B.
This corrected version of ISO/IEC 27002:2022 incorporates the following corrections:
— non-functioning hyperlinks throughout the document have been restored;
— in the introductory table in subclause 5.22 and in Table A.1 (row 5.22), "#information_security_
assurance" has been moved from the column headed "Security domains" to the column headed
"Operational capabilities".
Any feedback or questions on this document should be directed to the user’s national standards
body. A complete listing of these bodies can be found at www.iso.org/members.html and
www.iec.ch/national-committees.
vi
© ISO/IEC 2022 – All rights reserved
Introduction
0.1 Background and context
This document is designed for organizations of all types and sizes. It is to be used as a reference for
determining and implementing controls for information security risk treatment in an information
security management system (ISMS) based on ISO/IEC 27001. It can also be used as a guidance
document for organizations determining and implementing commonly accepted information security
controls. Furthermore, this document is intended for use in developing industry and organization-
specific information security management guidelines, taking into consideration their specific
information security risk environment(s). Organizational or environment-specific controls other than
those included in this document can be determined through risk assessment as necessary.
Organizations of all types and sizes (including public and private sector, commercial and non-profit)
create, collect, process, store, transmit and dispose of information in many forms, including electronic,
physical and verbal (e.g. conversations and presentations).
The value of information goes beyond written words, numbers and images: knowledge, concepts, ideas
and brands are examples of intangible forms of information. In an interconnected world, information
and other associated assets deserve or require protection against various risk sources, whether natural,
accidental or deliberate.
Information security is achieved by implementing a suitable set of controls, including policies, rules,
processes, procedures, organizational structures and software and hardware functions. To meet its
specific security and business objectives, the organization should define, implement, monitor, review
and improve these controls where necessary. An ISMS such as that specified in ISO/IEC 27001 takes a
holistic, coordinated view of the organization’s information security risks in order to determine and
implement a comprehensive suite of information security controls within the overall framework of a
coherent management system.
Many information systems, including their management and operations, have not been designed to be
secure in terms of an ISMS as specified in ISO/IEC 27001 and this document. The level of security that
can be achieved only through technological measures is limited and should be supported by appropriate
management activities and organizational processes. Identifying which controls should be in place
requires careful planning and attention to detail while carrying out risk treatment.
A successful ISMS requires support from all personnel in the organization. It can also require
participation from other interested parties, such as shareholders or suppliers. Advice from subject
matter experts can also be needed.
A suitable, adequate and effective information security management system provides assurance to the
organization’s management and other interested parties that their information and other associated
assets are kept reasonably secure and protected against threats and harm, thereby enabling the
organization to achieve the stated business objectives.
0.2 Information security requirements
It is essential that an organization determines its information security requirements. There are three
main sources of information security requirements:
a) the assessment of risks to the organization, taking into account the organization’s overall business
strategy and objectives. This can be facilitated or supported through an information security-
specific risk assessment. This should result in the determination of the controls necessary to
ensure that the residual risk to the organization meets its risk acceptance criteria;
b) the legal, statutory, regulatory and contractual requirements that an organization and its
interested parties (trading partners, service providers, etc.) have to comply with and their socio-
cultural environment;
vii
© ISO/IEC 2022 – All rights reserved
c) the set of principles, objectives and business requirements for all the steps of the life cycle of
information that an organization has developed to support its operations.
0.3 Controls
A control is defined as a measure that modifies or maintains risk. Some of the controls in this document
are controls that modify risk, while others maintain risk. An information security policy, for example,
can only maintain risk, whereas compliance with the information security policy can modify risk.
Moreover, some controls describe the same generic measure in different risk contexts. This document
provides a generic mixture of organizational, people, physical and technological information security
controls derived from internationally recognized best practices.
0.4 Determining controls
Determining controls is dependent on the organization’s decisions following a risk assessment, with
a clearly defined scope. Decisions related to identified risks should be based on the criteria for risk
acceptance, risk treatment options and the risk management approach applied by the organization. The
determination of controls should also take into consideration all relevant national and international
legislation and regulations. Control determination also depends on the manner in which controls
interact with one another to provide defence in depth.
The organization can design controls as required or identify them from any source. In specifying such
controls, the organization should consider the resources and investment needed to implement and
operate a control against the business value realized. See ISO/IEC TR 27016 for guidance on decisions
regarding the investment in an ISMS and the economic consequences of these decisions in the context of
competing requirements for resources.
There should be a balance between the resources deployed for implementing controls and the potential
resulting business impact from security incidents in the absence of those controls. The results of a
risk assessment should help guide and determine the appropriate management action, priorities for
managing information security risks and for implementing controls determined necessary to protect
against these risks.
Some of the controls in this document can be considered as guiding principles for information security
management and as being applicable for most organizations. More information about determining
controls and other risk treatment options can be found in ISO/IEC 27005.
0.5 Developing organization-specific guidelines
This document can be regarded as a starting point for developing organization-specific guidelines.
Not all of the controls and guidance in this document can be applicable to all organizations. Additional
controls and guidelines not included in this document can also be required to address the specific needs
of the organization and the risks that have been identified. When documents are developed containing
additional guidelines or controls, it can be useful to include cross-references to clauses in this document
for future reference.
0.6 Life cycle considerations
Information has a life cycle, from creation to disposal. The value of, and risks to, information can vary
throughout this life cycle (e.g. unauthorized disclosure or theft of a company’s financial accounts is
not significant after they have been published, but integrity remains critical) therefore, information
security remains important to some extent at all stages.
Information systems and other assets relevant to information security have life cycles within which
they are conceived, specified, designed, developed, tested, implemented, used, maintained and
eventually retired from service and disposed of. Information security should be considered at every
stage. New system development projects and changes to existing systems provide opportunities to
improve security controls while taking into account the organization’s risks and lessons learned from
incidents.
viii
© ISO/IEC 2022 – All rights reserved
0.7 Related International Standards
While this document offers guidance on a broad range of information security controls that are
commonly applied in many different organizations, other documents in the ISO/IEC 27000 family
provide complementary advice or requirements on other aspects of the overall process of managing
information security.
Refer to ISO/IEC 27000 for a general introduction to both ISMS and the family of documents.
ISO/IEC 27000 provides a glossary, defining most of the terms used throughout the ISO/IEC 27000
family of documents, and describes the scope and objectives for each member of the family.
There are sector-specific standards that have additional controls which aim at addressing specific
areas (e.g. ISO/IEC 27017 for cloud services, ISO/IEC 27701 for privacy, ISO/IEC 27019 for energy,
ISO/IEC 27011 for telecommunications organizations and ISO 27799 for health). Such standards are
included in the Bibliography and some of them are referenced in the guidance and other information
sections in Clauses 5-8.
ix
© ISO/IEC 2022 – All rights reserved
INTERNATIONAL STANDARD ISO/IEC 27002:2022(E)
Information security, cybersecurity and privacy
protection — Information security controls
1 Scope
This document provides a reference set of generic information security controls including
implementation guidance. This document is designed to be used by organizations:
a) within the context of an information security management system (ISMS) based on ISO/IEC 27001;
b) for implementing information security controls based on internationally recognized best practices;
c) for developing organization-specific information security management guidelines.
2 Normative references
There are no normative references in this document.
3 Terms, definitions and abbreviated terms
3.1 Terms and definitions
For the purposes of this document, the following terms and definitions apply.
ISO and IEC maintain terminology databases for use in standardization at the following addresses:
— ISO Online browsing platform: available at https:// www .iso .org/ obp
— IEC Electropedia: available at https:// www .electropedia .org/
3.1.1
access control
means to ensure that physical and logical access to assets (3.1.2) is authorized and restricted based on
business and information security requirements
3.1.2
asset
anything that has value to the organization
Note 1 to entry: In the context of information security, two kinds of assets can be distinguished:
— the primary assets:
— information;
— business processes (3.1.27) and activities;
— the supporting assets (on which the primary assets rely) of all types, for example:
— hardware;
— software;
— network;
— personnel (3.1.20);
© ISO/IEC 2022 – All rights reserved
— site;
— organization’s structure.
3.1.3
attack
successful or unsuccessful unauthorized attempt to destroy, alter, disable, gain access to an asset (3.1.2)
or any attempt to expose, steal, or make unauthorized use of an asset (3.1.2)
3.1.4
authentication
provision of assurance that a claimed characteristic of an entity (3.1.11) is correct
3.1.5
authenticity
property that an entity (3.1.11) is what it claims to be
3.1.6
chain of custody
demonstrable possession, movement, handling and location of material from one point in time until
another
Note 1 to entry: Material includes information and other associated assets (3.1.2) in the context of ISO/IEC 27002.
[SOURCE: ISO/IEC 27050-1:2019, 3.1, modified — “Note 1 to entry” added]
3.1.7
confidential information
information that is not intended to be made available or disclosed to unauthorized individuals, entities
(3.1.11) or processes (3.1.27)
3.1.8
control
measure that maintains and/or modifies risk
Note 1 to entry: Controls include, but are not limited to, any process (3.1.27), policy (3.1.24), device, practice or
other conditions and/or actions which maintain and/or modify risk.
Note 2 to entry: Controls may not always exert the intended or assumed modifying effect.
[SOURCE: ISO 31000:2018, 3.8]
3.1.9
disruption
incident, whether anticipated or unanticipated, that causes an unplanned, negative deviation from the
expected delivery of products and services according to an organization’s objectives
[SOURCE: ISO 22301:2019, 3.10]
3.1.10
endpoint device
network connected information and communication technology (ICT) hardware device
Note 1 to entry: Endpoint device can refer to desktop computers, laptops, smart phones, tablets, thin clients,
printers or other specialized hardware including smart meters and Internet of things (IoT) devices.
3.1.11
entity
item relevant for the purpose of operation of a domain that has recognizably distinct existence
Note 1 to entry: An entity can have a physical or a logical embodiment.
© ISO/IEC 2022 – All rights reserved
EXAMPLE A person, an organization, a device, a group of such items, a human subscriber to a telecom
service, a SIM card, a passport, a network interface card, a software application, a service or a website.
[SOURCE: ISO/IEC 24760-1:2019, 3.1.1]
3.1.12
information processing facility
any information processing system, service or infrastructure, or the physical location housing it
[SOURCE: ISO/IEC 27000:2018, 3.27, modified — "facilities" has been replaced with facility.]
3.1.13
information security breach
compromise of information security that leads to the undesired destruction, loss, alteration, disclosure
of, or access to, protected information transmitted, stored or otherwise processed
3.1.14
information security event
occurrence indicating a possible information security breach (3.1.13) or failure of controls (3.1.8)
[SOURCE: ISO/IEC 27035-1:2016, 3.3, modified — “breach of information security” has been replaced
with “information security breach”]
3.1.15
information security incident
one or multiple related and identified information security events (3.1.14) that can harm an organization’s
assets (3.1.2) or compromise its operations
[SOURCE: ISO/IEC 27035-1:2016, 3.4]
3.1.16
information security incident management
exercise of a consistent and effective approach to the handling of information security incidents (3.1.15)
[SOURCE: ISO/IEC 27035-1:2016, 3.5]
3.1.17
information system
set of applications, services, information technology assets (3.1.2), or other information-handling
components
[SOURCE: ISO/IEC 27000:2018, 3.35]
3.1.18
interested party
stakeholder
person or organization that can affect, be affected by, or perceive itself to be affected by a decision or
activity
[SOURCE: ISO/IEC 27000:2018, 3.37]
3.1.19
non-repudiation
ability to prove the occurrence of a claimed event or action and its originating entities (3.1.11)
3.1.20
personnel
persons doing work under the organization’s direction
Note 1 to entry: The concept of personnel includes the organization’s members, such as the governing body, top
management, employees, temporary staff, contractors and volunteers.
© ISO/IEC 2022 – All rights reserved
3.1.21
personally identifiable information
PII
any information that (a) can be used to establish a link between the information and the natural person
to whom such information relates, or (b) is or can be directly or indirectly linked to a natural person.
Note 1 to entry: The “natural person” in the definition is the PII principal (3.1.22). To determine whether a PII
principal is identifiable, account should be taken of all the means which can reasonably be used by the privacy
stakeholder holding the data, or by any other party, to establish the link between the set of PII and the natural
person.
[SOURCE: ISO/IEC 29100:2011/Amd.1:2018, 2.9]
3.1.22
PII principal
natural person to whom the personally identifiable information (PII) (3.1.21) relates
Note 1 to entry: Depending on the jurisdiction and the particular data protection and privacy legislation, the
synonym “data subject” can also be used instead of the term “PII principal”.
[SOURCE: ISO/IEC 29100:2011, 2.11]
3.1.23
PII processor
privacy stakeholder that processes personally identifiable information (PII) (3.1.21) on behalf of and in
accordance with the instructions of a PII controller
[SOURCE: ISO/IEC 29100:2011, 2.12]
3.1.24
policy
intentions and direction of an organization, as formally expressed by its top management
[SOURCE: ISO/IEC 27000:2018, 3.53]
3.1.25
privacy impact assessment
PIA
overall process (3.1.27) of identifying, analysing, evaluating, consulting, communicating and planning
the treatment of potential privacy impacts with regard to the processing of personally identifiable
information (PII) (3.1.21), framed within an organization’s broader risk management framework
[SOURCE: ISO/IEC 29134:2017, 3.7, modified — Note 1 to entry removed.]
3.1.26
procedure
specified way to carry out an activity or a process (3.1.27)
[SOURCE: ISO 30000:2009, 3.12]
3.1.27
process
set of interrelated or interacting activities that uses or transforms inputs to deliver a result
[SOURCE: ISO 9000:2015, 3.4.1, modified— Notes to entry removed.]
3.1.28
record
information created, received and maintained as evidence and as an asset (3.1.2) by an organization or
person, in pursuit of legal obligations or in the transaction of business
Note 1 to entry: Legal obligations in this context include all legal, statutory, regulatory and contractual
requirements.
© ISO/IEC 2022 – All rights reserved
[SOURCE: ISO 15489-1:2016, 3.14, modified— “Note 1 to entry” added.]
3.1.29
recovery point objective
RPO
point in time to which data are to be recovered after a disruption (3.1.9) has occurred
[SOURCE: ISO/IEC 27031:2011, 3.12, modified — "must" replaced by "are to be".]
3.1.30
recovery time objective
RTO
period of time within which minimum levels of services and/or products and the supporting systems,
applications, or functions are to be recovered after a disruption (3.1.9) has occurred
[SOURCE: ISO/IEC 27031:2011, 3.13, modified — "must" replaced by "are to be".]
3.1.31
reliability
property of consistent intended behaviour and results
3.1.32
rule
accepted principle or instruction that states the organization’s expectations on what is required to be
done, what is allowed or not allowed
Note 1 to entry: Rules can be formally expressed in topic-specific policies (3.1.35) and in other types of documents.
3.1.33
sensitive information
information that needs to be protected from unavailability, unauthorized access, modification or public
disclosure because of potential adverse effects on an individual, organization, national security or
public safety
3.1.34
threat
potential cause of an unwanted incident, which can result in harm to a system or organization
[SOURCE: ISO/IEC 27000:2018, 3.74]
3.1.35
topic-specific policy
intentions and direction on a specific subject or topic, as formally expressed by the appropriate level of
management
Note 1 to entry: Topic-specific policies can formally express rules (3.1.32) or organization standards.
Note 2 to entry: Some organizations use other terms for these topic-specific policies.
Note 3 to entry: The topic-specific policies referred to in this document are related to information security.
EXAMPLE Topic-specific policy on access cont
...
INTERNATIONAL ISO/IEC
STANDARD 27002
Redline version
compares Third edition to
Second edition
Information security, cybersecurity
and privacy protection — Information
security controls
Sécurité de l'information, cybersécurité et protection de la vie
privée — Mesures de sécurité de l'information
Reference number
ISO/IEC 27002:r edline:2022(E)
© ISO/IEC 2022
ISO/IEC 27002:redline:2022(E)
IMPORTANT — PLEASE NOTE
This is a provisional mark-up copy and uses the following colour coding:
Text example 1 — indicates added text (in green)
— indicates removed text (in red)
Text example 2
— indicates added graphic figure
— indicates removed graphic figure
1.x . — Heading numbers containg modifications are highlighted in yellow in
the Table of Contents
All changes in this document have yet to reach concensus by vote and as such should only
be used internally for review purposes.
DISCLAIMER
This Redline version is not an official IEC Standard and is intended only to provide the
user with an indication of what changes have been made to the previous version. Only the
current version of the standard is to be considered the official document.
This Redline version provides you with a quick and easy way to compare all the changes
between this standard and its previous edition. A vertical bar appears in the margin
wherever a change has been made. Additions and deletions are displayed in red, with
deletions being struck through.
© ISO/IEC 2022
All rights reserved. Unless otherwise specified, or required in the context of its implementation, no part of this publication may
be reproduced or utilized otherwise in any form or by any means, electronic or mechanical, including photocopying, or posting on
the internet or an intranet, without prior written permission. Permission can be requested from either ISO at the address below
or ISO’s member body in the country of the requester.
ISO copyright office
CP 401 • Ch. de Blandonnet 8
CH-1214 Vernier, Geneva
Phone: +41 22 749 01 11
Email: copyright@iso.org
Website: www.iso.org
Published in Switzerland
ii
© ISO/IEC 2022 – All rights reserved
ISO/IEC 27002:redline:2022(E)
Contents Page
Foreword .viii
0 Introduction .ix
1 Scope . 1
2 Normative references . 1
3 Terms and definitions , definitions and abbreviated terms. 1
3.1 Terms and definitions . 1
3.2 Abbreviated terms . 6
4 Structure of this standard document . 8
4.1 Clauses . 8
4.2 Control categories Themes and attributes . 8
4.3 Control layout . 10
5 Information security policies .10
5.1 Management direction for information security . 10
5.1.1 Policies for information security . 10
5.1.2 Review of the policies for information security . 11
6 Organization of information security .12
6.1 Internal organization . 12
6.1.1 Information security roles and responsibilities . 12
6.1.2 Segregation of duties . 13
6.1.3 Contact with authorities . 13
6.1.4 Contact with special interest groups . 13
6.1.5 Information security in project management .14
6.2 Mobile devices and teleworking .14
6.2.1 Mobile device policy .14
6.2.2 Teleworking . 16
7 Human resource security .17
7.1 Prior to employment .17
7.1.1 Screening .17
7.1.2 Terms and conditions of employment . . 18
7.2 During employment . 18
7.2.1 Management responsibilities. 18
7.2.2 Information security awareness, education and training .19
7.2.3 Disciplinary process . 20
7.3 Termination and change of employment . 21
7.3.1 Termination or change of employment responsibilities . 21
8 5 Asset management Organizational controls .21
5.1 Policies for information security . 21
5.2 Information security roles and responsibilities . 24
5.3 Segregation of duties . 25
5.4 Management responsibilities . . 25
5.5 Contact with authorities . 26
5.6 Contact with special interest groups . 27
5.7 Threat intelligence . 28
5.8 Information security in project management . 29
8.1 5.9 Responsibility for Inventory of information and other associated assets . 31
8.1.1 Inventory of assets . 31
8.1.2 Ownership of assets . 31
8.1.3 Acceptable use of assets . 32
8.1.4 Return of assets . 32
5.10 Acceptable use of information and other associated assets . 34
5.11 Return of assets . 35
iii
© ISO/IEC 2022 – All rights reserved
ISO/IEC 27002:redline:2022(E)
8.2 5.12 Information classification Classification of information . 36
8.2.1 Classification of information. 36
8.2.2 Labelling of information . 37
8.2.3 Handling of assets . 37
5.13 Labelling of information . 39
5.14 Information transfer . 40
5.15 Access control . 43
5.16 Identity management . 45
5.17 Authentication information . 46
5.18 Access rights . 48
5.19 Information security in supplier relationships . 49
5.20 Addressing information security within supplier agreements.51
5.21 Managing information security in the ICT supply chain . 53
5.22 Monitoring, review and change management of supplier services . 55
5.23 Information security for use of cloud services . 57
5.24 Information security incident management planning and preparation . 59
5.25 Assessment and decision on information security events .61
5.26 Response to information security incidents .61
5.27 Learning from information security incidents . 62
5.28 Collection of evidence . 63
5.29 Information security during disruption . 64
5.30 ICT readiness for business continuity . 64
8.3 5.31 Media handling Legal, statutory, regulatory and contractual requirements . 66
8.3.1 Management of removable media . 66
8.3.2 Disposal of media . 66
8.3.3 Physical media transfer . 67
5.32 Intellectual property rights. 69
5.33 Protection of records . 70
5.34 Privacy and protection of PII . 72
5.35 Independent review of information security . 73
5.36 Compliance with policies, rules and standards for information security .74
5.37 Documented operating procedures . 75
9 Access control.76
9.1 Business requirements of access control .76
9.1.1 Access control policy .76
9.1.2 Access to networks and network services . 77
9.2 User access management . 78
9.2.1 User registration and de-registration . 78
9.2.2 User access provisioning. 78
9.2.3 Management of privileged access rights . 79
9.2.4 Management of secret authentication information of users . 80
9.2.5 Review of user access rights . 80
9.2.6 Removal or adjustment of access rights . 81
9.3 User responsibilities . 81
9.3.1 Use of secret authentication information. 81
9.4 System and application access control . 82
9.4.1 Information access restriction . 82
9.4.2 Secure log-on procedures . 83
9.4.3 Password management system . 84
9.4.4 Use of privileged utility programs . 84
9.4.5 Access control to program source code . 85
10 6 Cryptography People controls .85
6.1 Screening . 85
6.2 Terms and conditions of employment . 87
6.3 Information security awareness, education and training . 88
6.4 Disciplinary process . 89
6.5 Responsibilities after termination or change of employment . 90
iv
© ISO/IEC 2022 – All rights reserved
ISO/IEC 27002:redline:2022(E)
6.6 Confidentiality or non-disclosure agreements . 91
10.1 6.7 Cryptographic controls Remote working . 92
10.1.1 Policy on the use of cryptographic controls . 92
10.1.2 Key management . 93
6.8 Information security event reporting. 96
11 7 Physical and environmental security controls .97
11.1 7.1 Secure areas Physical security perimeters . 97
11.1.1 Physical security perimeter . 97
11.1.2 Physical entry controls . 98
11.1.3 Securing offices, rooms and facilities . 98
11.1.4 Protecting against external and environmental threats . 99
11.1.5 Working in secure areas . 99
11.1.6 Delivery and loading areas . 99
7.2 Physical entry .101
7.3 Securing offices, rooms and facilities .102
7.4 Physical security monitoring .103
7.5 Protecting against physical and environmental threats .104
7.6 Working in secure areas .105
7.7 Clear desk and clear screen .106
7.8 Equipment siting and protection .107
7.9 Security of assets off-premises .108
7.10 Storage media .109
7.11 Supporting utilities .110
7.12 Cabling security .111
7.13 Equipment maintenance .112
11.2 7.14 Equipment Secure disposal or re-use of equipment .113
11.2.1 Equipment siting and protection .113
11.2.2 Supporting utilities .113
11.2.3 Cabling security . 114
11.2.4 Equipment maintenance .114
11.2.5 Removal of assets .115
11.2.6 Security of equipment and assets off-premises .115
11.2.7 Secure disposal or re-use of equipment .116
11.2.8 Unattended user equipment .117
11.2.9 Clear desk and clear screen policy .117
12 8 Operations security Technological controls . 119
8.1 User endpoint devices .119
8.2 Privileged access rights . .121
8.3 Information access restriction .122
8.4 Access to source code .124
8.5 Secure authentication .125
12.1 8.6 Operational procedures and responsibilities Capacity management .127
12.1.1 Documented operating procedures .127
12.1.2 Change management .127
12.1.3 Capacity management .128
12.1.4 Separation of development, testing and operational environments .129
12.2 8.7 Protection from against malware .131
12.2.1 Controls against malware .131
8.8 Management of technical vulnerabilities .134
8.9 Configuration management .137
8.10 Information deletion .139
8.11 Data masking . .140
8.12 Data leakage prevention .142
12.3 8.13 Backup Information backup. 143
12.3.1 Information backup .143
8.14 Redundancy of information processing facilities .145
12.4 8.15 Logging and monitoring .146
v
© ISO/IEC 2022 – All rights reserved
ISO/IEC 27002:redline:2022(E)
12.4.1 Event logging .146
12.4.2 Protection of log information . 147
12.4.3 Administrator and operator logs .148
12.4.4 Clock synchronisation . .148
8.16 Monitoring activities .151
8.17 Clock synchronization .153
8.18 Use of privileged utility programs .154
12.5 8.19 Control of operational software Installation of software on operational systems .154
12.5.1 Installation of software on operational systems .155
8.20 Networks security .157
8.21 Security of network services .158
8.22 Segregation of networks .159
8.23 Web filtering .160
8.24 Use of cryptography .161
8.25 Secure development life cycle .163
8.26 Application security requirements .164
12.6 8.27 Technical vulnerability management Secure system architecture and
engineering principles .166
12.6.1 Management of technical vulnerabilities .166
12.6.2 Restrictions on software installation .167
8.28 Secure coding .169
8.29 Security testing in development and acceptance .172
8.30 Outsourced development .173
8.31 Separation of development, test and production environments . 174
8.32 Change management.176
8.33 Test information .177
12.7 8.34 Information systems audit considerations Protection of information systems
during audit testing .177
12.7.1 Information systems audit controls .178
13 Communications security . 179
13.1 Network security management .179
13.1.1 Network controls .179
13.1.2 Security of network services .179
13.1.3 Segregation in networks .180
13.2 Information transfer .181
13.2.1 Information transfer policies and procedures .181
13.2.2 Agreements on information transfer .182
13.2.3 Electronic messaging .183
13.2.4 Confidentiality or non-disclosure agreements .183
14 System acquisition, development and maintenance .184
14.1 Security requirements of information systems .184
14.1.1 Information security requirements analysis and specification .184
14.1.2 Securing application services on public networks .185
14.1.3 Protecting application services transactions .186
14.2 Security in development and support processes .187
14.2.1 Secure development policy .187
14.2.2 System change control procedures .188
14.2.3 Technical review of applications after operating platform changes .189
14.2.4 Restrictions on changes to software packages .189
14.2.5 Secure system engineering principles .189
14.2.6 Secure development environment.190
14.2.7 Outsourced development . 191
14.2.8 System security testing .191
14.2.9 System acceptance testing .192
14.3 Test data .192
14.3.1 Protection of test data .192
vi
© ISO/IEC 2022 – All rights reserved
ISO/IEC 27002:redline:2022(E)
15 Supplier relationships . 192
15.1 Information security in supplier relationships .192
15.1.1 Information security policy for supplier relationships .193
15.1.2 Addressing security within supplier agreements .194
15.1.3 Information and communication technology supply chain .195
15.2 Supplier service delivery management .196
15.2.1 Monitoring and review of supplier services .196
15.2.2 Managing changes to supplier services .197
16 Information security incident management . 197
16.1 Management of information security incidents and improvements.197
16.1.1 Responsibilities and procedures .197
16.1.2 Reporting information security events .198
16.1.3 Reporting information security weaknesses .199
16.1.4 Assessment of and decision on information security events .199
16.1.5 Response to information security incidents .200
16.1.6 Learning from information security incidents .200
16.1.7 Collection of evidence .201
17 Information security aspects of business continuity management . 202
17.1 Information security continuity .202
17.1.1 Planning information security continuity .202
17.1.2 Implementing information security continuity .202
17.1.3 Verify, review and evaluate information security continuity .203
17.2 Redundancies .204
17.2.1 Availability of information processing facilities .204
18 Compliance .204
18.1 Compliance with legal and contractual requirements .204
18.1.1 Identification of applicable legislation and contractual requirements .204
18.1.2 Intellectual property rights .204
18.1.3 Protection of records . .205
18.1.4 Privacy and protection of personally identifiable information .206
18.1.5 Regulation of cryptographic controls .207
18.2 Information security reviews .207
18.2.1 Independent review of information security .207
18.2.2 Compliance with security policies and standards .208
18.2.3 Technical compliance review .208
Annex A (informative) Using attributes . 210
Annex B (informative) Correspondence of ISO/IEC 27002:2022 (this document) with
ISO/IEC 27002:2013 . 221
Bibliography . 228
vii
© ISO/IEC 2022 – All rights reserved
ISO/IEC 27002:redline:2022(E)
Foreword
ISO (the International Organization for Standardization) and IEC (the International Electrotechnical
Commission) form the specialized system for worldwide standardization. National bodies that are
members of ISO or IEC participate in the development of International Standards through technical
committees established by the respective organization to deal with particular fields of technical
activity. ISO and IEC technical committees collaborate in fields of mutual interest. Other international
organizations, governmental and non-governmental, in liaison with ISO and IEC, also take part in the
work. In the field of information technology, ISO and IEC have established a joint technical committee,
ISO/IEC JTC 1.
International Standards areThe procedures used to develop this document and those intended for its
further maintenance are described in the ISO/IEC Directives, Part 1. In particular, the different approval
criteria needed for the different types of document should be noted. This document was drafted in
accordance with the rules given ineditorial rules of the ISO/IEC Directives, Part 2 (see www .iso .org/
directives or www .iec .ch/ members _experts/ refdocs 2).
ISO/IEC 27002 was prepared by Joint Technical Committee ISO/IEC JTC 1, Information technology,
Subcommittee SC 27, IT Security techniques.
Attention is drawn to the possibility that some of the elements of this document may be the subject
of patent rights. ISO and IEC shall not be held responsible for identifying any or all such patent
rights. Details of any patent rights identified during the development of the document will be in the
Introduction and/or on the ISO list of patent declarations received (see www .iso .org/ patents) or the IEC
list of patent declarations received (see patents.iec.ch).
Any trade name used in this document is information given for the convenience of users and does not
constitute an endorsement.
For an explanation of the voluntary nature of standards, the meaning of ISO specific terms and
expressions related to conformity assessment, as well as information about ISO’s adherence to the
World Trade Organization (WTO) principles in the Technical Barriers to Trade (TBT) see www .iso .org/
iso/ foreword .html. In the IEC, see www .iec .ch/ understanding -standards.
’This document was prepared by Joint Technical Committee ISO/IEC JTC 1, Information technology,
Subcommittee SC 27, Information security, cybersecurity and privacy protection.
third edition cancels and replaces the firstsecond edition (ISO/IEC 27002:20052013), which
This second
has been technically and structurally revised.revised. It also incorporates the Technical Corrigenda
ISO/IEC 27002:2013/Cor. 1:2014 and ISO/IEC 27002:2013/Cor. 2:2015.
The main changes are as follows:
— the title has been modified;
— the structure of the document has been changed, presenting the controls using a simple taxonomy
and associated attributes;
— some controls have been merged, some deleted and several new controls have been introduced. The
complete correspondence can be found in Annex B.
Any feedback or questions on this document should be directed to the user’s national standards body. A
complete listing of these bodies can be found at www .iso .org/ members .html and www .iec .ch/ national
-committees.
viii
© ISO/IEC 2022 – All rights reserved
ISO/IEC 27002:redline:2022(E)
0 Introduction
0.1 Background and context
This International Standarddocument is designed for organizations to useof all types and sizes. It is
to be used as a reference for selecting controls within the process of implementing an Information
Security Management Systemdetermining and implementing controls for information security risk
[10]
treatment in an information security management system (ISMS) based on ISO/IEC 27001 or. It
can also be used as a guidance document for organizations determining and implementing commonly
accepted information security controls. This standard is alsoFurthermore, this document is intended
...
ISO/IEC JTC 1/SC 27
Date : 2022-0210
Version corrigée : 2022-03
ISO IEC 27002:2022 (F)
ISO/IEC JTC 1/SC 27
Secrétariat : DIN
Sécurité de l'information, cybersécurité et protection de la vie privée — Moyens
de maîtrise de l'information
Information security, cybersecurity and privacy protection — Information security
controls
ICS : 35.030
Type du document: Norme internationale
Sous-type du document:
Stade du document: (60) Publication
Langue du document: F
Type du document: Norme internationale
Sous-type du document:
Stade du document: (60) Publication
Langue du document: F
DOCUMENT PROTÉGÉ PAR COPYRIGHT
© ISO 2022
Tous droits réservés. Sauf prescription différente ou nécessité dans le contexte de sa mise en œuvre,
aucune partie de cette publication ne peut être reproduite ni utilisée sous quelque forme que ce soit
et par aucun procédé, électronique ou mécanique, y compris la photocopie, l’affichage sur l’Internet
ou sur un Intranet, sans autorisation écrite préalable. Les demandes d’autorisation peuvent être
adressées à l’ISO à l’adresse ci-après ou au comité membre de l’ISO dans le pays du demandeur.
ISO copyright office
CP 401 •• Ch. de Blandonnet 8
CH-1214 Vernier, Genève
Tél. :.: + 41 22 749 01 11
Fax : + 41 22 749 09 47
E-mail : copyright@iso.org
Web : www.iso.org
Publié en Suisse
ii © ISO/IEC 2022 – Tous droits réservés
Sommaire
Avant-propos . vi
Introduction . viii
1 Domaine d'application . 1
2 Références normatives . 1
3 Termes, définitions et abréviations . 1
3.1 Termes et définitions . 1
3.2 Abréviations . 7
4 Structure du présent document . 9
4.1 Articles . 9
4.2 Thèmes et attributs . 9
4.3 Structure des moyens de maîtrise . 11
5 Moyens de maîtrise organisationnels . 11
5.1 Politiques de sécurité de l'information . 11
5.2 Fonctions et responsabilités liées à la sécurité de l'information . 14
5.3 Séparation des tâches . 15
5.4 Responsabilités de la direction . 16
5.5 Contacts avec les autorités . 17
5.6 Contacts avec des groupes d’intérêt spécifiques . 18
5.7 Renseignements sur les menaces . 19
5.8 Sécurité de l'information dans la gestion de projet . 21
5.9 Inventaire des informations et autres actifs associés . 23
5.10 Utilisation correcte des informations et autres actifs associés . 25
5.11 Restitution des actifs . 26
5.12 Classification des informations . 27
5.13 Marquage des informations . 29
5.14 Transfert des informations. 30
5.15 Contrôle d'accès . 33
5.16 Gestion des identités . 36
5.17 Informations d'authentification . 37
5.18 Droits d'accès . 39
5.19 Sécurité de l'information dans les relations avec les fournisseurs . 41
5.20 La sécurité de l'information dans les accords conclus avec les fournisseurs . 44
5.21 Gestion de la sécurité de l'information dans la chaîne d'approvisionnement TIC . 46
5.22 Surveillance, révision et gestion des changements des services fournisseurs . 49
5.23 Sécurité de l'information dans l'utilisation de services en nuage . 51
5.24 Planification et préparation de la gestion des incidents liés à la sécurité de
l'information . 53
5.25 Évaluation des événements liés à la sécurité de l'information et prise de décision . 55
5.26 Réponse aux incidents liés à la sécurité de l'information . 56
5.27 Tirer des enseignements des incidents liés à la sécurité de l'information . 57
5.28 Collecte des preuves . 58
5.29 Sécurité de l'information pendant une perturbation . 59
5.30 Préparation des TIC pour la continuité d'activité . 60
5.31 Exigences légales, statutaires, réglementaires et contractuelles . 61
5.32 Droits de propriété intellectuelle . 63
5.33 Protection des documents d'activité . 65
© ISO/IEC 2022 – Tous droits réservés iii
5.34 Protection de la vie privée et des DCP . 67
5.35 Révision indépendante de la sécurité de l'information . 68
5.36 Conformité aux politiques, règles et normes de sécurité de l'information . 69
5.37 Procédures d'exploitation documentées . 70
6 Moyens de maîtrise applicables aux personnes . 71
6.1 Sélection des candidats . 71
6.2 Termes et conditions du contrat de travail . 73
6.3 Sensibilisation, enseignement et formation en sécurité de l'information . 74
6.4 Processus disciplinaire . 76
6.5 Responsabilités après la fin ou le changement d’un emploi . 77
6.6 Accords de confidentialité ou de non-divulgation . 78
6.7 Travail à distance . 79
6.8 Déclaration des événements liés à la sécurité de l'information . 81
7 Moyens de maîtrise physique . 82
7.1 Périmètres de sécurité physique . 82
7.2 Les entrées physiques . 83
7.3 Sécurisation des bureaux, des salles et des installations . 86
7.4 Surveillance de la sécurité physique . 86
7.5 Protection contre les menaces physiques et environnementales . 88
7.6 Travail dans les zones sécurisées . 89
7.7 Bureau vide et écran vide . 90
7.8 Emplacement et protection du matériel . 91
7.9 Sécurité des actifs hors des locaux . 92
7.10 Supports de stockage . 93
7.11 Services supports . 95
7.12 Sécurité du câblage . 96
7.13 Maintenance du matériel . 97
7.14 Élimination ou recyclage sécurisé(e) du matériel . 98
8 Moyens de maîtrise technologiques . 100
8.1 Terminaux utilisateurs . 100
8.2 Droits d'accès privilégiés . 103
8.3 Restrictions d'accès aux informations . 104
8.4 Accès aux codes source . 107
8.5 Authentification sécurisée . 108
8.6 Dimensionnement . 110
8.7 Protection contre les programmes malveillants (malware) . 111
8.8 Gestion des vulnérabilités techniques . 113
8.9 Gestion des configurations . 117
8.10 Suppression des informations . 120
8.11 Masquage des données . 121
8.12 Prévention la fuite de données . 123
8.13 Sauvegarde des informations . 125
8.14 Redondance des moyens de traitement de l'information . 127
8.15 Journalisation . 128
8.16 Activités de surveillance . 132
8.17 Synchronisation des horloges . 134
8.18 Utilisation de programmes utilitaires à privilèges . 135
8.19 Installation de logiciels sur des systèmes opérationnels . 136
8.20 Sécurité des réseaux . 138
8.21 Sécurité des services réseau . 139
iv © ISO/IEC 2022 – Tous droits réservés
8.22 Cloisonnement des réseaux . 141
8.23 Filtrage web . 142
8.24 Utilisation de la cryptographie . 143
8.25 Cycle de vie de développement sécurisé. 145
8.26 Exigences de sécurité des applications . 146
8.27 Principes d'ingénierie et d'architecture des système sécurisés . 149
8.28 Codage sécurisé . 151
8.29 Tests de sécurité dans le développement et l'acceptation . 155
8.30 Développement externalisé . 156
8.31 Séparation des environnements de développement, de test et opérationnels . 157
8.32 Gestion des changements . 159
8.33 Informations de test . 161
8.34 Protection des systèmes d'information pendant les tests d'audit . 162
Annexe A (informative) Utilisation des attributs . 164
Annexe B (informative) Correspondance de l’ISO/IEC 27002:2022 (le présent document) avec
l'ISO/IEC 27002:2013 . 175
Bibliographie. 185
Avant-propos . viii
Introduction . xi
1 Domaine d'application . 1
2 Références normatives . 1
3 Termes, définitions et abréviations . 1
3.1 Termes et définitions . 1
3.2 Abréviations . 6
4 Structure du présent document . 8
4.1 Articles . 8
4.2 Thèmes et attributs . 9
4.3 Structure des moyens de maîtrise . 10
5 Moyens de maîtrise organisationnels . 11
5.1 Politiques de sécurité de l'information . 11
5.2 Fonctions et responsabilités liées à la sécurité de l'information . 14
5.3 Séparation des tâches . 15
5.4 Responsabilités de la direction . 16
5.5 Contacts avec les autorités . 17
5.6 Contacts avec des groupes d’intérêt spécifiques . 18
5.7 Renseignements sur les menaces . 19
5.8 Sécurité de l'information dans la gestion de projet . 21
5.9 Inventaire des informations et autres actifs associés . 23
5.10 Utilisation correcte des informations et autres actifs associés . 25
5.11 Restitution des actifs . 26
5.12 Classification des informations . 27
5.13 Marquage des informations . 29
5.14 Transfert des informations. 31
5.15 Contrôle d'accès . 34
5.16 Gestion des identités . 36
© ISO/IEC 2022 – Tous droits réservés v
5.17 Informations d'authentification . 38
5.18 Droits d'accès . 40
5.19 Sécurité de l'information dans les relations avec les fournisseurs . 42
5.20 La sécurité de l'information dans les accords conclus avec les fournisseurs . 45
5.21 Gestion de la sécurité de l'information dans la chaîne d'approvisionnement TIC . 47
5.22 Surveillance, révision et gestion des changements des services fournisseurs . 50
5.23 Sécurité de l'information dans l'utilisation de services en nuage . 52
5.24 Planification et préparation de la gestion des incidents liés à la sécurité de
l'information . 55
5.25 Évaluation des événements liés à la sécurité de l'information et prise de décision . 57
5.26 Réponse aux incidents liés à la sécurité de l'information . 58
5.27 Tirer des enseignements des incidents liés à la sécurité de l'information . 59
5.28 Collecte des preuves . 60
5.29 Sécurité de l'information pendant une perturbation . 61
5.30 Préparation des TIC pour la continuité d'activité . 62
5.31 Exigences légales, statutaires, réglementaires et contractuelles . 63
5.32 Droits de propriété intellectuelle . 65
5.33 Protection des documents d'activité . 67
5.34 Protection de la vie privée et des DCP . 69
5.35 Révision indépendante de la sécurité de l'information . 70
5.36 Conformité aux politiques, règles et normes de sécurité de l'information . 71
5.37 Procédures d'exploitation documentées . 72
6 Moyens de maîtrise applicables aux personnes . 74
6.1 Sélection des candidats . 74
6.2 Termes et conditions du contrat de travail . 76
6.3 Sensibilisation, enseignement et formation en sécurité de l'information . 77
6.4 Processus disciplinaire . 79
6.5 Responsabilités après la fin ou le changement d’un emploi . 80
6.6 Accords de confidentialité ou de non-divulgation . 81
6.7 Travail à distance . 82
6.8 Déclaration des événements liés à la sécurité de l'information . 85
7 Moyens de maîtrise physique . 86
7.1 Périmètres de sécurité physique . 86
7.2 Les entrées physiques . 87
7.3 Sécurisation des bureaux, des salles et des installations . 89
7.4 Surveillance de la sécurité physique . 90
7.5 Protection contre les menaces physiques et environnementales . 91
7.6 Travail dans les zones sécurisées . 93
7.7 Bureau vide et écran vide . 94
7.8 Emplacement et protection du matériel . 95
7.9 Sécurité des actifs hors des locaux . 96
7.10 Supports de stockage . 97
7.11 Services supports . 99
7.12 Sécurité du câblage . 101
7.13 Maintenance du matériel . 102
7.14 Élimination ou recyclage sécurisé(e) du matériel . 103
8 Moyens de maîtrise technologiques . 104
8.1 Terminaux utilisateurs . 104
8.2 Droits d'accès privilégiés . 107
8.3 Restrictions d'accès aux informations . 109
vi © ISO/IEC 2022 – Tous droits réservés
8.4 Accès aux codes source . 111
8.5 Authentification sécurisée . 112
8.6 Dimensionnement . 114
8.7 Protection contre les programmes malveillants (malware) . 116
8.8 Gestion des vulnérabilités techniques . 118
8.9 Gestion des configurations . 122
8.10 Suppression des informations . 125
8.11 Masquage des données . 127
8.12 Prévention la fuite de données . 129
8.13 Sauvegarde des informations . 131
8.14 Redondance des moyens de traitement de l'information . 132
8.15 Journalisation . 134
8.16 Activités de surveillance . 137
8.17 Synchronisation des horloges . 140
8.18 Utilisation de programmes utilitaires à privilèges . 141
8.19 Installation de logiciels sur des systèmes opérationnels . 142
8.20 Sécurité des réseaux. 144
8.21 Sécurité des services réseau . 146
8.22 Cloisonnement des réseaux . 147
8.23 Filtrage web . 148
8.24 Utilisation de la cryptographie . 149
8.25 Cycle de vie de développement sécurisé. 152
8.26 Exigences de sécurité des applications . 153
8.27 Principes d'ingénierie et d'architecture des système sécurisés . 156
8.28 Codage sécurisé . 158
8.29 Tests de sécurité dans le développement et l'acceptation . 162
8.30 Développement externalisé . 163
8.31 Séparation des environnements de développement, de test et opérationnels . 164
8.32 Gestion des changements . 167
8.33 Informations de test . 168
8.34 Protection des systèmes d'information pendant les tests d'audit . 169
Annexe A (informative) Utilisation des attributs . 171
Annexe B (informative) Correspondance de l’ISO/IEC 27002:2022 (le présent document) avec
l'ISO/IEC 27002:2013 . 183
Bibliographie. 193
© ISO/IEC 2022 – Tous droits réservés vii
Avant-propos
L'ISO (Organisation internationale de normalisation) et l'IECl’IEC (Commission électrotechnique
internationale) forment le système spécialisé de la normalisation mondiale. Les organismes nationaux
membres de l'ISO ou de l'IECl’IEC participent au développement de Normes Internationalesinternationales
par l'intermédiaire des comités techniques créés par l'organisation concernée afin de s'occuper des
domaines particuliers de l'activité technique. Les comités techniques de l'ISO et de l'IECl’IEC collaborent
dans des domaines d'intérêt commun. D'autres organisations internationales, gouvernementales et non
gouvernementales, en liaison avec l'ISO et l'IECl’IEC, participent également aux travaux.
Les procédures utilisées pour élaborer le présent document et celles destinées à sa mise à jour sont décrites
dans les Directives ISO/IEC, Partie 1. Il convient, en particulier de prendre note des différents critères
d'approbation requis pour les différents types de documents ISO. Le présent document a été rédigé
conformément aux règles de rédaction données dans les Directives ISO/IEC, Partie 2 (voir
www.iso.org/directiveswww.iso.org/directives ou www.iec.ch/members_experts/refdocs).
L'attention est attirée sur le fait que certains des éléments du présent document peuvent faire l'objet de
droits de propriété intellectuelle ou de droits analogues. L'ISO et l'IECl’IEC ne sauraient être tenues pour
responsables de ne pas avoir identifié de tels droits de propriété et averti de leur existence. Les détails
concernant les références aux droits de propriété intellectuelle ou autres droits analogues identifiés lors de
l'élaboration du document sont indiqués dans l'Introduction et/ou dans la liste des déclarations de brevets
reçues par l'ISO (voir www.iso.org/brevetswww.iso.org/brevets) ou dans la liste des déclarations de
brevets reçues par l'IEC (voir patents.iec.chhttps://patents.iec.ch).
Les appellations commerciales éventuellement mentionnées dans le présent document sont données pour
information, par souci de commodité, à l'intentionl’intention des utilisateurs et ne sauraient constituer un
engagement.
Pour une explication de la nature volontaire des normes, la signification des termes et expressions
spécifiques de l'ISO liés à l'évaluation de la conformité, ou pour toute information au sujet de l'adhésion de
l'ISO aux principes de l'Organisationl’Organisation mondiale du commerce (OMC) concernant les obstacles
techniques au commerce (OTC), voir le lien suivant : www.iso.org/iso/fr/avant-
proposwww.iso.org/iso/avant-propos. Pour l'IEC, voir www.iec.ch/understanding-standards.
Le présent document a été élaboré par le comité technique mixte ISO/IEC JTC 1, Technologies de
l'information, sous-comité SC 27, Sécurité de l'information, cybersécurité et protection de la vie privée.
Cette troisième édition annule et remplace la deuxième édition (ISO/IEC 27002:2013)), qui a fait l'objet
d'unel’objet d’une révision technique. Elle contientincorpore également les rectificatifsRectificatifs
techniques ISO/IEC 27002:2013/Cor. 1:2014 et ISO/IEC 27002:2013/Cor. 2:2015.
Les principales modifications sont les suivantes :
— le titre a été modifié ;
— la structure du document a été modifiée, présentant les moyens de maîtrise avec une taxonomie simple
et des attributs associés ;
— certains moyens de maîtrise ont été fusionnés, d'autres ont été supprimés, et plusieurs nouveaux
moyens de maîtrise ont été ajoutés. La correspondance complète se trouve à l'Annexe B.
viii © ISO/IEC 2022 – Tous droits réservés
© ISO/IEC 2022 – Tous droits réservés ix
La présente version corrigéefrançaise de l'ISO/IEC 27002:2022 comprend les corrections suivantes :
— les hyperliens qui ne fonctionnaient pas dans l'ensemble du document ont été restaurés ;
— danscorrespond à la version anglaise publiée le tableau introductif en 5.222022-02 et danscorrigé le
Tableau A.1 (ligne 5.22), « #Assurance_de_sécurité_de_l'information » a été déplacé de la colonne intitulée
« Domaines de sécurité » vers la colonne intitulée « Capacités opérationnelles ».2022-03.
Il convient que l'utilisateurl’utilisateur adresse tout retour d'informationd’information ou toute question
concernant le présent document à l'organismel’organisme national de normalisation de son pays. Une liste
exhaustive desdits organismes se trouve aux adressesà l’adresse
www.iso.org/fr/members.htmlwww.iso.org/members.html et www.iec.ch/national-committees.
x © ISO/IEC 2022 – Tous droits réservés
Introduction
0.1 Historique et contexte
Le présent document a été conçu à l'intention des organisations de tous types et de toutes dimensions. Il est
à utiliser comme document de référence pour déterminer et mettre en œuvre des moyens de maîtrise pour
le traitement des risques liés à la sécurité de l'information dans un système de management de la sécurité
de l'information (SMSI) basé sur l'ISO/IEC 27001. Il peut également être utilisé comme guide de bonnes
pratiques pour les organisations qui déterminent et mettent en œuvre les moyens de maîtrise de
l'information communément admis. De plus, le présent document a pour objet d'être utilisé lors de
l’élaboration des lignes directrices de gestion de la sécurité de l'information spécifiques aux organisations
et aux industries, en tenant compte de leur(s) environnement(s) spécifique(s) de risques liés à la sécurité
de l'information. Des moyens de maîtrise organisationnels ou spécifiques à l'environnement autres que ceux
qui figurent dans le présent document peuvent, si nécessaire, être déterminés par le biais de l’appréciation
du risque.
Des organisations de tous types et de toutes dimensions (y compris du secteur public et du secteur privé, à
but lucratif ou non lucratif) créent, collectent, traitent, stockent, transmettent et éliminent l'information sous
de nombreuses formes, notamment électronique, physique et verbale (par exemple, les conversations et les
présentations).
La valeur de l'information va au-delà des mots, chiffres et images écrits : la connaissance, les concepts, les
idées et les marques sont des exemples de formes intangibles d'information. Dans un monde interconnecté,
les informations et autres actifs associés méritent ou exigent une protection contre différentes sources de
risques, aussi bien naturelles, qu'accidentelles ou délibérées.
La sécurité de l'information est réalisée par la mise en œuvre d’un ensemble de moyens de maîtrise
appropriés, notamment des politiques, des règles, des processus, des procédures, des structures
organisationnelles, et des fonctions matérielles et logicielles. Pour atteindre ses objectifs métier et de
sécurité, il convient que l'organisation définisse, mette en œuvre, surveille, révise et améliore ces moyens de
maîtrise au besoin. Un système de management de la sécurité de l'information (SMSI) tel que celui spécifié
dans l'ISO/IEC 27001 appréhende les risques liés à la sécurité de l'information de l'organisation dans une
vision globale et coordonnée, afin de déterminer et mettre en œuvre un ensemble complet de moyens de
maîtrise de l'information dans le cadre global d'un système de management cohérent.
De nombreux systèmes d'information, y compris leur management et leurs opérations, n'ont pas été conçus
sécurisés au sens d'un système de management de la sécurité de l'information tel que spécifié dans
l'ISO/IEC 27001 et le présent document. Le niveau de sécurité qui peut être atteint seulement par des
mesures techniques est limité, et il convient de le renforcer par des processus organisationnels et activités
de management appropriés. L'identification des moyens de maîtrise qu'il convient de mettre en place
nécessite une planification minutieuse et une attention aux détails lors de la réalisation du traitement du
risque.
Un système de management de la sécurité de l'information réussi requiert l'adhésion de tout le personnel
de l'organisation. Il peut également nécessiter la participation d'autres parties intéressées, telles que des
actionnaires ou des fournisseurs. Des conseils d'experts en la matière peuvent aussi s'avérer nécessaires.
Un système de management de la sécurité de l'information approprié, adéquat et efficace procure la garantie
aux dirigeants de l'organisation et autres parties intéressées que leurs informations et autres actifs associés
sont suffisamment sécurisés et protégés contre les menaces et dommages, ce qui permet à l'organisation
d'atteindre les objectifs métier visés.
© ISO/IEC 2022 – Tous droits réservés xi
0.2 Exigences de sécurité de l'information
Il est essentiel qu'une organisation détermine ses exigences de sécurité de l'information. Il existe trois
principales sources des exigences de sécurité de l'information :
a) l'appréciation du risque de l'organisation, prenant en compte l'ensemble de sa stratégie et objectifs
métier. Cela peut être facilité ou appuyé par une appréciation du risque lié à la sécurité de l'information.
Il convient que cela aboutisse à la détermination les moyens de maîtrise nécessaires assurant que les
risques résiduels pour l'organisation correspondent à ses critères d'acceptation des risques ;
b) les exigences légales, statutaires, réglementaires et contractuelles auxquelles l'organisation et ses
parties intéressées (partenaires commerciaux, fournisseurs de services, etc.) doivent se conformer ainsi
que leur environnement socioculturel ;
c) l'ensemble des principes, d'objectifs et d'exigences métier pour toutes les étapes du cycle de vie de
l'information que l'organisation a élaboré pour appuyer son fonctionnement.
0.3 Moyens de maîtrise
Un moyen de maîtrise est défini comme une mesure qui modifie ou maintient un risque. Certains des
...
NORME ISO/IEC
INTERNATIONALE 27002
Troisième édition
2022-02
Sécurité de l'information,
cybersécurité et protection de la
vie privée — Mesures de sécurité de
l'information
Information security, cybersecurity and privacy protection —
Information security controls
Numéro de référence
© ISO/IEC 2022
DOCUMENT PROTÉGÉ PAR COPYRIGHT
© ISO/IEC 2022
Tous droits réservés. Sauf prescription différente ou nécessité dans le contexte de sa mise en œuvre, aucune partie de cette
publication ne peut être reproduite ni utilisée sous quelque forme que ce soit et par aucun procédé, électronique ou mécanique,
y compris la photocopie, ou la diffusion sur l’internet ou sur un intranet, sans autorisation écrite préalable. Une autorisation peut
être demandée à l’ISO à l’adresse ci-après ou au comité membre de l’ISO dans le pays du demandeur.
ISO copyright office
Case postale 401 • Ch. de Blandonnet 8
CH-1214 Vernier, Genève
Tél.: +41 22 749 01 11
Fax: +41 22 749 09 47
E-mail: copyright@iso.org
Web: www.iso.org
Publié en Suisse
ii
© ISO/IEC 2022 – Tous droits réservés
Sommaire Page
Avant-propos . vi
Introduction .vii
1 Domaine d'application .1
2 Références normatives .1
3 Termes, définitions et abréviations . 1
3.1 Termes et définitions . 1
3.2 Abréviations. 6
4 Structure du présent document. 8
4.1 Articles. 8
4.2 Thèmes et attributs . 8
4.3 Structure des mesures de sécurité . 9
5 Mesures de sécurité organisationnelles .10
5.1 Politiques de sécurité de l'information . 10
5.2 Fonctions et responsabilités liées à la sécurité de l'information .12
5.3 Séparation des tâches .13
5.4 Responsabilités de la direction . 14
5.5 Contacts avec les autorités . 15
5.6 Contacts avec des groupes d’intérêt spécifiques . 16
5.7 Renseignements sur les menaces . 17
5.8 Sécurité de l'information dans la gestion de projet . 18
5.9 Inventaire des informations et autres actifs associés . 20
5.10 Utilisation correcte des informations et autres actifs associés .22
5.11 Restitution des actifs .23
5.12 Classification des informations . 24
5.13 Marquage des informations .25
5.14 Transfert des informations . . 27
5.15 Contrôle d'accès .29
5.16 Gestion des identités . 31
5.17 Informations d'authentification . 33
5.18 Droits d'accès . 35
5.19 Sécurité de l'information dans les relations avec les fournisseurs .36
5.20 La sécurité de l'information dans les accords conclus avec les fournisseurs .39
5.21 Gestion de la sécurité de l'information dans la chaîne d'approvisionnement TIC . 41
5.22 Surveillance, révision et gestion des changements des services fournisseurs . 43
5.23 Sécurité de l'information dans l'utilisation de services en nuage .44
5.24 Planification et préparation de la gestion des incidents de sécurité de l'information . 47
5.25 Évaluation des événements de sécurité de l'information et prise de décision .49
5.26 Réponse aux incidents de sécurité de l'information .49
5.27 Tirer des enseignements des incidents de sécurité de l'information .50
5.28 Collecte des preuves . 51
5.29 Sécurité de l'information pendant une perturbation . 52
5.30 Préparation des TIC pour la continuité d'activité . 53
5.31 Exigences légales, statutaires, réglementaires et contractuelles .54
5.32 Droits de propriété intellectuelle .56
5.33 Protection des enregistrements . 57
5.34 Protection de la vie privée et des DCP . 59
5.35 Révision indépendante de la sécurité de l'information .60
5.36 Conformité aux politiques, règles et normes de sécurité de l'information . 61
5.37 Procédures d'exploitation documentées . 62
6 Mesures de sécurité applicables aux personnes .63
6.1 Sélection des candidats .63
6.2 Termes et conditions du contrat de travail .64
iii
© ISO/IEC 2022 – Tous droits réservés
6.3 Sensibilisation, enseignement et formation en sécurité de l'information .66
6.4 Processus disciplinaire . 67
6.5 Responsabilités après la fin ou le changement d’un emploi .68
6.6 Accords de confidentialité ou de non-divulgation . 69
6.7 Travail à distance . 70
6.8 Déclaration des événements de sécurité de l'information .72
7 Mesures de sécurité physique .73
7.1 Périmètres de sécurité physique .73
7.2 Les entrées physiques .74
7.3 Sécurisation des bureaux, des salles et des installations. 76
7.4 Surveillance de la sécurité physique .77
7.5 Protection contre les menaces physiques et environnementales . 78
7.6 Travail dans les zones sécurisées . 79
7.7 Bureau vide et écran vide .80
7.8 Emplacement et protection du matériel . 81
7.9 Sécurité des actifs hors des locaux .82
7.10 Supports de stockage .83
7.11 Services supports .85
7.12 Sécurité du câblage .86
7.13 Maintenance du matériel .87
7.14 Élimination ou recyclage sécurisé(e) du matériel .88
8 Mesures de sécurité technologiques .89
8.1 Terminaux finaux des utilisateurs .89
8.2 Droits d'accès privilégiés . . 91
8.3 Restrictions d'accès aux informations . 93
8.4 Accès aux codes source . 95
8.5 Authentification sécurisée .96
8.6 Dimensionnement .97
8.7 Protection contre les programmes malveillants (malware) .99
8.8 Gestion des vulnérabilités techniques . 101
8.9 Gestion des configurations .104
8.10 Suppression des informations .106
8.11 Masquage des données .108
8.12 Prévention de la fuite de données . 110
8.13 Sauvegarde des informations . 111
8.14 Redondance des moyens de traitement de l'information .113
8.15 Journalisation . 114
8.16 Activités de surveillance . 117
8.17 Synchronisation des horloges . 119
8.18 Utilisation de programmes utilitaires à privilèges .120
8.19 Installation de logiciels sur des systèmes opérationnels .121
8.20 Sécurité des réseaux . .122
8.21 Sécurité des services réseau .123
8.22 Cloisonnement des réseaux .125
8.23 Filtrage web.126
8.24 Utilisation de la cryptographie .127
8.25 Cycle de vie de développement sécurisé .129
8.26 Exigences de sécurité des applications .130
8.27 Principes d'ingénierie et d'architecture des système sécurisés .132
8.28 Codage sécurisé .134
8.29 Tests de sécurité dans le développement et l'acceptation .137
8.30 Développement externalisé .138
8.31 Séparation des environnements de développement, de test et opérationnels .139
8.32 Gestion des changements . . 141
8.33 Informations de test . 142
8.34 Protection des systèmes d'information pendant les tests d'audit . 143
Annexe A (informative) Utilisation des attributs .145
iv
© ISO/IEC 2022 – Tous droits réservés
Annexe B (informative) Correspondance de l’ISO/IEC 27002:2022 (le présent document)
avec l'ISO/IEC 27002:2013 . 156
Bibliographie . 164
v
© ISO/IEC 2022 – Tous droits réservés
Avant-propos
L'ISO (Organisation internationale de normalisation) et l’IEC (Commission électrotechnique
internationale) forment le système spécialisé de la normalisation mondiale. Les organismes
nationaux membres de l'ISO ou de l’IEC participent au développement de Normes internationales
par l'intermédiaire des comités techniques créés par l'organisation concernée afin de s'occuper des
domaines particuliers de l'activité technique. Les comités techniques de l'ISO et de l’IEC collaborent
dans des domaines d'intérêt commun. D'autres organisations internationales, gouvernementales et non
gouvernementales, en liaison avec l'ISO et l’IEC, participent également aux travaux.
Les procédures utilisées pour élaborer le présent document et celles destinées à sa mise à jour sont
décrites dans les Directives ISO/IEC, Partie 1. Il convient, en particulier de prendre note des différents
critères d'approbation requis pour les différents types de documents ISO. Le présent document a
été rédigé conformément aux règles de rédaction données dans les Directives ISO/IEC, Partie 2 (voir
www.iso.org/directives ou www.iec.ch/members_experts/refdocs).
L'attention est attirée sur le fait que certains des éléments du présent document peuvent faire l'objet
de droits de propriété intellectuelle ou de droits analogues. L'ISO et l’IEC ne sauraient être tenues pour
responsables de ne pas avoir identifié de tels droits de propriété et averti de leur existence. Les détails
concernant les références aux droits de propriété intellectuelle ou autres droits analogues identifiés
lors de l'élaboration du document sont indiqués dans l'Introduction et/ou dans la liste des déclarations
de brevets reçues par l'ISO (voir www.iso.org/brevets) ou dans la liste des déclarations de brevets
reçues par l'IEC (voir https://patents.iec.ch).
Les appellations commerciales éventuellement mentionnées dans le présent document sont données
pour information, par souci de commodité, à l’intention des utilisateurs et ne sauraient constituer un
engagement.
Pour une explication de la nature volontaire des normes, la signification des termes et expressions
spécifiques de l'ISO liés à l'évaluation de la conformité, ou pour toute information au sujet de
l'adhésion de l'ISO aux principes de l’Organisation mondiale du commerce (OMC) concernant les
obstacles techniques au commerce (OTC), voir www.iso.org/iso/avant-propos. Pour l'IEC, voir
www.iec.ch/understanding-standards.
Le présent document a été élaboré par le comité technique mixte ISO/IEC JTC 1, Technologies de
l'information, sous-comité SC 27, Sécurité de l'information, cybersécurité et protection de la vie privée.
Cette troisième édition annule et remplace la deuxième édition (ISO/IEC 27002:2013), qui
a fait l’objet d’une révision technique. Elle incorpore également les Rectificatifs techniques
ISO/IEC 27002:2013/Cor. 1:2014 et ISO/IEC 27002:2013/Cor. 2:2015.
Les principales modifications sont les suivantes:
— le titre a été modifié;
— la structure du document a été modifiée, présentant les mesures de sécurité avec une taxonomie
simple et des attributs associés;
— certaines mesures de sécurité ont été fusionnées, d'autres ont été supprimées, et plusieurs nouvelles
mesures de sécurité ont été ajoutées. La correspondance complète se trouve à l'Annexe B.
La présente version française de l'ISO/IEC 27002:2022 correspond à la version anglaise publiée le 2022-
02 et corrigé le 2022-03.
Il convient que l’utilisateur adresse tout retour d’information ou toute question concernant le présent
document à l’organisme national de normalisation de son pays. Une liste exhaustive desdits organismes
se trouve à l’adresse www.iso.org/members.html et www.iec.ch/national-committees.
vi
© ISO/IEC 2022 – Tous droits réservés
Introduction
0.1 Historique et contexte
Le présent document a été conçu à l'intention des organisations de tous types et de toutes dimensions.
Il est à utiliser comme document de référence pour déterminer et mettre en œuvre des mesures de
sécurité pour le traitement des risques de sécurité de l'information dans un système de management
de la sécurité de l'information (SMSI) basé sur l'ISO/IEC 27001. Il peut également être utilisé comme
guide de bonnes pratiques pour les organisations qui déterminent et mettent en œuvre les mesures
de sécurité de l'information communément admises. De plus, le présent document a pour objet d'être
utilisé lors de l’élaboration des lignes directrices de gestion de la sécurité de l'information spécifiques
aux organisations et aux industries, en tenant compte de leur(s) environnement(s) spécifique(s) de
risques de sécurité de l'information. Des mesures de sécurité organisationnelles ou spécifiques à
l'environnement autres que celles qui figurent dans le présent document peuvent, si nécessaire, être
déterminées par le biais de l’appréciation du risque.
Des organisations de tous types et de toutes dimensions (y compris du secteur public et du secteur
privé, à but lucratif ou non lucratif) créent, collectent, traitent, stockent, transmettent et éliminent
l'information sous de nombreuses formes, notamment électronique, physique et verbale (par exemple,
les conversations et les présentations).
La valeur de l'information va au-delà des mots, chiffres et images écrits: la connaissance, les concepts,
les idées et les marques sont des exemples de formes intangibles d'information. Dans un monde
interconnecté, les informations et autres actifs associés méritent ou exigent une protection contre
différentes sources de risques, aussi bien naturelles, qu'accidentelles ou délibérées.
La sécurité de l'information est réalisée par la mise en œuvre d’un ensemble de mesures de sécurité
appropriées, notamment des politiques, des règles, des processus, des procédures, des structures
organisationnelles, et des fonctions matérielles et logicielles. Pour atteindre ses objectifs métier et
de sécurité, il convient que l'organisation définisse, mette en œuvre, surveille, révise et améliore ces
mesures de sécurité au besoin. Un système de management de la sécurité de l'information (SMSI) tel que
celui spécifié dans l'ISO/IEC 27001 appréhende les risques de sécurité de l'information de l'organisation
dans une vision globale et coordonnée, afin de déterminer et mettre en œuvre un ensemble complet de
mesures de sécurité de l'information dans le cadre global d'un système de management cohérent.
De nombreux systèmes d'information, y compris leur management et leurs opérations, n'ont pas été
conçus sécurisés au sens d'un système de management de la sécurité de l'information tel que spécifié
dans l'ISO/IEC 27001 et le présent document. Le niveau de sécurité qui peut être atteint seulement par
des mesures techniques est limité, et il convient de le renforcer par des processus organisationnels
et des activités de management appropriés. L'identification des mesures de sécurité qu'il convient de
mettre en place nécessite une planification minutieuse et une attention aux détails lors de la réalisation
du traitement du risque.
Un système de management de la sécurité de l'information réussi requiert l'adhésion de tout le
personnel de l'organisation. Il peut également nécessiter la participation d'autres parties intéressées,
telles que des actionnaires ou des fournisseurs. Des conseils d'experts en la matière peuvent aussi
s'avérer nécessaires.
Un système de management de la sécurité de l'information approprié, adéquat et efficace procure la
garantie aux dirigeants de l'organisation et autres parties intéressées que leurs informations et autres
actifs associés sont suffisamment sécurisés et protégés contre les menaces et dommages, ce qui permet
à l'organisation d'atteindre les objectifs métier visés.
0.2 Exigences de sécurité de l'information
Il est essentiel qu'une organisation détermine ses exigences de sécurité de l'information. Il existe trois
principales sources des exigences de sécurité de l'information:
a) l'appréciation du risque de l'organisation, prenant en compte l'ensemble de sa stratégie et objectifs
métier. Cela peut être facilité ou appuyé par une appréciation du risque de sécurité de l'information.
vii
© ISO/IEC 2022 – Tous droits réservés
Il convient que cela aboutisse à la détermination des mesures de sécurité nécessaires assurant que
les risques résiduels pour l'organisation correspondent à ses critères d'acceptation des risques;
b) les exigences légales, statutaires, réglementaires et contractuelles auxquelles l'organisation et ses
parties intéressées (partenaires commerciaux, fournisseurs de services, etc.) doivent se conformer
ainsi que leur environnement socioculturel;
c) l'ensemble des principes, d'objectifs et d'exigences métier pour toutes les étapes du cycle de vie de
l'information que l'organisation a élaboré pour appuyer son fonctionnement.
0.3 Mesures de sécurité
Un mesure de sécurité est définie comme une mesure qui modifie ou maintient un risque. Certaines
des mesures de sécurité dans le présent document sont des moyens qui modifient les risques, tandis
que d'autres maintiennent les risques. Une politique de sécurité de l'information, par exemple, permet
seulement de maintenir les risques, tandis que la conformité à la politique de sécurité de l'information
peut modifier les risques. De plus, certaines mesures de sécurité décrivent la même mesure générique
dans différents contextes de risques. Le présent document propose une combinaison générique
de mesures de sécurité de l'information organisationnelles, liées aux personnes, physiques et
technologiques, issues des bonnes pratiques reconnues au niveau international.
0.4 Détermination des mesures de sécurité
La détermination des mesures de sécurité dépend des décisions de l'organisation suite à une
appréciation du risque, avec un périmètre clairement défini. Il convient de baser les décisions
relatives aux risques identifiés sur les critères d'acceptation des risques, les options de traitement des
risques et l'approche de gestion des risques appliqués par l'organisation. Il convient également que
la détermination des mesures de sécurité tienne compte de toutes les législations et réglementations
nationales et internationales pertinentes. La détermination des mesures de sécurité dépend aussi de la
manière dont les mesures de sécurité interagissent les unes avec les autres pour assurer une défense en
profondeur.
L'organisation peut concevoir des mesures de sécurité au besoin, ou bien les identifier à partir
de n'importe quelle source. Lors de la spécification de ces mesures de sécurité, il convient que
l'organisation tienne compte des ressources et investissements nécessaires pour mettre en œuvre et
opérer un mesure de sécurité par rapport à la valeur métier réalisée. Voir l'ISO/IEC TR 27016 pour les
recommandations sur les décisions concernant les investissements dans un SMSI et les conséquences
économiques de ces décisions dans le contexte d'exigences concurrentes en matière de ressources.
Il convient qu’il y ait un équilibre entre les ressources déployées pour mettre en œuvre les mesures
de sécurité et l'impact métier possible résultant des incidents de sécurité en l'absence de ces mesures
de sécurité. Il convient que les résultats de l'appréciation du risque aident à guider et à déterminer
les actions de gestion appropriées, les priorités pour gérer les risques de sécurité de l'information, et
pour mettre en œuvre les mesures de sécurité identifiées comme nécessaires pour protéger contre ces
risques.
Certaines mesures de sécurité dans le présent document peuvent être considérées comme des
principes de base pour la gestion de la sécurité de l'information et elles sont applicables à la plupart des
organisations. Plus d’informations sur la détermination des mesures de sécurité et autres options de
traitement du risque peuvent être trouvées dans l'ISO/IEC 27005.
0.5 Élaboration de lignes directrices spécifiques à une organisation
Le présent document peut être considéré comme point de départ pour l’élaboration de lignes directrices
spécifiques à une organisation. Toutes les mesures de sécurité et lignes directrices du présent document
peuvent ne pas être applicables à toutes les organisations. D'autres mesures de sécurité et lignes
directrices ne figurant pas dans le présent document peuvent être nécessaires pour traiter les besoins
spécifiques de l'organisation et les risques identifiés. Lors de la rédaction de documents contenant des
lignes directrices ou des mesures de sécurité supplémentaires, il peut être utile d'ajouter des références
croisées aux articles du présent document en vue d’une consultation ultérieure.
viii
© ISO/IEC 2022 – Tous droits réservés
0.6 Considérations relatives au cycle de vie
L'information a un cycle de vie, depuis sa création jusqu'à son élimination. La valeur de l'information
et les risques associés peuvent varier au cours de ce cycle de vie (par exemple, une divulgation non
autorisée ou le vol des comptes financiers d'une entreprise n'a pas d'impact significatif après la
publication de ces informations, mais l'intégrité demeure critique). Par conséquent, l'importance de la
sécurité de l'information subsiste à tous les stades.
Les systèmes d'information et autres actifs pertinents pour la sécurité de l'information ont des cycles
de vie durant lesquels ils sont pensés, spécifiés, conçus, développés, testés, mis en œuvre, utilisés,
maintenus et finalement retirés du service et mis au rebut. Il convient que la sécurité de l'information
soit considérée à chaque étape. Les projets de développement de nouveaux systèmes et les changements
apportés aux systèmes existants donnent l'occasion d'améliorer les mesures de sécurité tout en prenant
en compte les risques de l'organisation et les leçons tirées des incidents.
0.7 Normes internationales associées
Alors que le présent document propose des recommandations portant sur un vaste éventail de
mesures de sécurité qui sont communément utilisées dans plusieurs organisations différentes, d'autres
documents de la famille ISO/IEC 27000 proposent des conseils complémentaires ou des exigences
relatifs à d'autres aspects du processus global de gestion de la sécurité de l'information.
Se reporter à l'ISO/IEC 27000 pour une introduction générale à la fois aux SMSI et à la famille de
documents. L'ISO/IEC 27000 fournit un glossaire, définissant la plupart des termes utilisés dans la
famille des documents ISO/IEC 27000, et décrit le périmètre et les objectifs de chaque membre de la
famille.
Il existe des normes sectorielles qui comportent des mesures de sécurité supplémentaires destinées
à traiter des domaines spécifiques (par exemple, l'ISO/IEC 27017 pour les services en nuage,
l'ISO/IEC 27701 pour la protection de la vie privée, l'ISO/IEC 27019 pour l'énergie, l'ISO/IEC 27011
pour les organisations de télécommunications et l'ISO 27799 pour la santé). Ces normes figurent
dans la Bibliographie et certaines d'entre elles sont référencées dans les recommandations et autres
informations des Articles 5 à 8.
ix
© ISO/IEC 2022 – Tous droits réservés
NORME INTERNATIONALE ISO/IEC 27002:2022(F)
Sécurité de l'information, cybersécurité et protection de la
vie privée — Mesures de sécurité de l'information
1 Domaine d'application
Le présent document fournit un ensemble de référence de mesures de sécurité de l'information
génériques, y compris des recommandations de mise en œuvre. Le présent document est conçu pour
être utilisé par les organisations:
a) dans le contexte d'un système de gestion de la sécurité de l'information (SMSI) selon l'ISO/IEC 27001;
b) pour la mise en œuvre de mesures de sécurité de l'information basées sur les bonnes pratiques
reconnues au niveau international;
c) pour l'élaboration des recommandations de gestion de la sécurité de l'information spécifiques à
une organisation.
2 Références normatives
Le présent document ne contient aucune référence normative.
3 Termes, définitions et abréviations
3.1 Termes et définitions
Pour les besoins du présent document, les termes et définitions suivants s’appliquent.
L’ISO et l’IEC tiennent à jour des bases de données terminologiques destinées à être utilisées en
normalisation, consultables aux adresses suivantes:
— ISO Online browsing platform: disponible à l’adresse https:// www .iso .org/ obp
— IEC Electropedia: disponible à l’adresse https:// www .electropedia .org/
3.1.1
contrôle d'accès
moyens pour assurer que l'accès physique et logique aux actifs (3.1.2) est autorisé et limité selon les
exigences de sécurité de l'information et métiers
3.1.2
actif
tout ce qui a de la valeur pour l'organisation
Note 1 à l'article: Dans le contexte de la sécurité de l'information, on peut distinguer deux types d'actifs:
— les actifs essentiels:
— informations;
— processus (3.1.27) et activités métier;
— les actifs support (sur lesquels reposent les actifs essentiels) de tous types, par exemple:
— matériel;
— logiciel;
© ISO/IEC 2022 – Tous droits réservés
— réseau;
— personnel (3.1.20);
— site;
— structure de l'organisation.
3.1.3
attaque
tentative non autorisée, réussie ou non, de détruire, d’altérer, de désactiver, d'accéder à un actif (3.1.2)
ou toute tentative d’exposer, de voler ou de faire un usage non autorisé d'un actif (3.1.2)
3.1.4
authentification
provision d'assurance qu'une caractéristique revendiquée d'une entité (3.1.11) est correcte
3.1.5
authenticité
propriété selon laquelle une entité (3.1.11) est ce qu'elle revendique être
3.1.6
chaîne de traçabilité
possession démontrable, déplacement, manipulation et emplacement de matériel d'un moment donné à
un autre
Note 1 à l'article: La notion de matériel englobe les informations et les autres actifs (3.1.2) associés dans le
contexte de l'ISO/IEC 27002.
[SOURCE: ISO/IEC 27050-1:2019, 3.1, modifié — Ajout d'une Note 1 à l'article]
3.1.7
informations confidentielles
informations qui ne sont pas destinées à être rendues disponibles ou divulguées à des personnes, des
entités (3.1.11) ou des processus (3.1.27) non autorisés
3.1.8
mesure de sécurité
action qui maintient et/ou modifie un risque
Note 1 à l'article: Un mesure de sécurité du risque inclut, sans toutefois s’y limiter, n’importe quels processus
(3.1.27), politique (3.1.24), dispositif, pratique ou autres conditions et/ou actions qui maintiennent et/ou
modifient un risque.
Note 2 à l'article: Un mesure de sécurité du risque n’aboutit pas toujours nécessairement à la modification voulue
ou supposée.
[SOURCE: ISO 31000:2018, 3.8, modifié]
3.1.9
perturbation
incident, anticipé ou non, qui entraîne un écart négatif non planifié par rapport à la livraison de produits
et à la fourniture de services prévues selon les objectifs d'une organisation
[SOURCE: ISO 22301:2019, 3.10]
3.1.10
terminal final
terminal matériel de technologies de l'information et de la communication (TIC) connecté au réseau
Note 1 à l'article: Un terminal final peut faire référence à des ordinateurs de bureau, des ordinateurs portables,
des smartphones, des tablettes, des clients légers, des imprimantes ou autres matériels spécialisés y compris les
compteurs intelligents ou les terminaux Internet des Objets (IoT).
© ISO/IEC 2022 – Tous droits réservés
3.1.11
entité
élément pertinent aux fins de fonctionnement d'un domaine et qui possède une existence manifestement
distincte
Note 1 à l'article: Une entité peut avoir une matérialisation physique ou logique.
EXEMPLE Une personne, une organisation, un dispositif, un groupe d'éléments de cette nature, un abonné
humain à un service de télécommunications, une carte SIM, un passeport, une carte d'interface réseau, une
application logicielle, un service ou un site web.
[SOURCE: ISO/IEC 24760-1:2019, 3.1.1]
3.1.12
moyen de traitement de l'information
tout système, service ou infrastructure de traitement de l'information, ou le local les abritant
[SOURCE: ISO/IEC 27000:2018, 3.27, modifié — «moyens» a été remplacé par «moyen».]
3.1.13
violation de sécurité de l'information
compromission de la sécurité de l'information qui entraîne la destruction non souhaitée, la perte,
l'altération, la divulgation ou l'accès à des informations protégées transmises, stockées ou soumises à
un autre traitement
3.1.14
événement de sécurité de l'information
occurrence indiquant une possible violation de sécurité de l'information (3.1.13) ou une violation des
mesures de sécurité (3.1.8)
[SOURCE: ISO/IEC 27035-1:2016, 3.3, modifié — «violation de la sécurité de l'information» a été
remplacé par «violation de sécurité de l'information».]
3.1.15
incident de sécurité de l'information
un ou plusieurs événements de sécurité de l'information (3.1.14), pouvant porter préjudice aux actifs
(3.1.2) d'une organisation ou compromettre son fonctionnement
[SOURCE: ISO/IEC 27035-1:2016, 3.4, modifié]
3.1.16
gestion des incidents de sécurité de l'information
exercice d'une approche cohérente et efficace de la prise en charge des incidents de sécurité de
l'information (3.1.15)
[SOURCE: ISO/IEC 27035-1:2016, 3.5, modifié]
3.1.17
système d'information
ensemble d'applications, services, actifs (3.1.2) informationnels ou autres composants permettant de
gérer l'information
[SOURCE: ISO/IEC 27000:2018, 3.35]
3.1.18
partie intéressée
partie prenante
personne ou organisation susceptible d'affecter, d'être affecté ou de se sentir lui-même affecté par une
décision ou une activité
[SOURCE: ISO/IEC 27000:2018, 3.37]
© ISO/IEC 2022 – Tous droits réservés
3.1.19
non-répudiation
capacité à prouver l'occurrence d'un événement ou d'une action revendiqué(e) et des entités (3.1.11) qui
en sont à l'origine
3.1.20
personnel
personnes effectuant un travail sous le contrôle de l'organisation
Note 1 à l'article: Le concept de personnel inclut les membres de l'organisation, tels que l'organe de gouvernance,
la direction, les employés, le personnel temporaire, les sous-traitants et les bénévoles.
3.1.21
données à caractère personnel
DCP
toute information qui (a) peut être utilisée pour établir un lien entre les informations et la personne
physique à laquelle ces informations se rapportent, ou qui (b) est ou peut être associée directement ou
indirectement à une personne physique
Note 1 à l'article: La «personne physique» référencée dans la définition est la personne concernée (3.1.22). Pour
déterminer si une personne concernée est identifiable, il convient de tenir compte de tous les moyens pouvant
être raisonnablement utilisés par la partie prenante en matière de protection de la vie privée qui détient les
données, ou par toute autre partie, afin d'établir le lien entre l'ensemble de DCP et la personne physique.
[SOURCE: ISO/IEC 29100:2011/Amd.1:2018, 2.9]
3.1.22
personne concernée
personne physique à qui se rapportent les données à caractère personnel (DCP) (3.1.21)
Note 1 à l'article: Selon la juridiction et la loi applicable en matière de protection des données et de la vie privée, le
terme «sujet des données» peut également être employé en lieu et place de «personne concernée».
[SOURCE: ISO/IEC 29100:2011, 2.11]
3.1.23
sous-traitant de DCP
partie prenante en matière de protection de la vie privée qui traite des données à caractère personnel
(DCP) (3.1.21) pour le compte d'un responsable de traitement de DCP et conformément à ses instructions
[SOURCE: ISO/IEC 29100:2011, 2.12]
3.1.24
politique
intentions et orientations d'une organisation telles que formalisées par sa direction
[SOURCE: ISO/IEC 27000:2018, 3.53]
3.1.25
étude d'impact sur la vie privée
PIA
processus (3.1.27) global visant à identifier, analyser, évaluer, consulter, communiquer et planifier le
traitement des impacts potentiels sur la vi
...
NORME ISO/IEC
INTERNATIONALE 27002
Redline version
compare la Deuxième édition
à la Troisième édition
Sécurité de l'information,
cybersécurité et protection de la
vie privée — Moyens de maîtrise de
l'information
Information security, cybersecurity and privacy protection —
Information security controls
Numéro de référence
ISO/IEC27002:r edline:2023(F)
© ISO/IEC 2023
ISO/IEC27002:redline:2023(F)
IMPORTANT — PLEASE NOTE
This is a provisional mark-up copy and uses the following colour coding:
Text example 1 — indicates added text (in green)
— indicates removed text (in red)
Text example 2
— indicates added graphic figure
— indicates removed graphic figure
1.x . — Heading numbers containg modifications are highlighted in yellow in
the Table of Contents
All changes in this document have yet to reach concensus by vote and as such should only
be used internally for review purposes.
DISCLAIMER
This Redline version is not an official IEC Standard and is intended only to provide the
user with an indication of what changes have been made to the previous version. Only the
current version of the standard is to be considered the official document.
This Redline version provides you with a quick and easy way to compare all the changes
between this standard and its previous edition. A vertical bar appears in the margin
wherever a change has been made. Additions and deletions are displayed in red, with
deletions being struck through.
DOCUMENT PROTÉGÉ PAR COPYRIGHT
© ISO/IEC 2023
Tous droits réservés. Sauf prescription différente ou nécessité dans le contexte de sa mise en œuvre, aucune partie de cette
publication ne peut être reproduite ni utilisée sous quelque forme que ce soit et par aucun procédé, électronique ou mécanique,
y compris la photocopie, ou la diffusion sur l’internet ou sur un intranet, sans autorisation écrite préalable. Une autorisation peut
être demandée à l’ISO à l’adresse ci-après ou au comité membre de l’ISO dans le pays du demandeur.
ISO copyright office
Case postale 401 • Ch. de Blandonnet 8
CH-1214 Vernier, Genève
Tél.: +41 22 749 01 11
Fax: +41 22 749 09 47
E-mail: copyright@iso.org
Web: www.iso.org
Publié en Suisse
ii
© ISO/IEC 2023 – Tous droits réservés
ISO/IEC27002:redline:2023(F)
Sommaire Page
Avant-propos .ix
0 Introduction .xi
1 Domaine d’application d'application .1
2 Références normatives .1
3 Termes et définitions , définitions et abréviations . 1
3.1 Termes et définitions . 1
3.2 Abréviations. 7
4 Structure de la présente norme du présent document . 8
4.1 Articles. 8
4.2 Thèmes et attributs . 9
4.2 Catégories de mesures . 10
4.2 4.3 .
Structure des moyens de maîtrise . 10
5 Politiques de sécurité de l’information .11
5.1 Orientations de la direction en matière de sécurité de l'information . 11
5.1.1 Politiques de sécurité de l'information . 11
5.1.2 Revue des politiques de sécurité de l’information .12
6 Organisation de la sécurité de l'information .13
6.1 Organisation interne .13
6.1.1 Fonctions et responsabilités liées à la sécurité de l'information .13
6.1.2 Séparation des tâches . 14
6.1.3 Relations avec les autorités . 14
6.1.4 Relations avec des groupes de travail spécialisés . 14
6.1.5 La sécurité de l'information dans la gestion de projet .15
6.2 Appareils mobiles et télétravail . 15
6.2.1 Politique en matière d'appareils mobiles . 16
6.2.2 Télétravail . 17
7 La sécurité des ressources humaines .18
7.1 Avant l'embauche . 18
7.1.1 Sélection des candidats . 19
7.1.2 Termes et conditions d'embauche . 19
7.2 Pendant la durée du contrat . 20
7.2.1 Responsabilités de la direction . 20
7.2.2 Sensibilisation, apprentissage et formation à la sécurité de l’information . 21
7.2.3 Processus disciplinaire . .22
7.3 Rupture, terme ou modification du contrat de travail . 23
7.3.1 Achèvement ou modification des responsabilités associées au contrat de
travail . 23
8 Gestion des actifs .24
8.1 Responsabilités relatives aux actifs . 24
8.1.1 Inventaire des actifs . 24
8.1.2 Propriété des actifs . 24
8.1.3 Utilisation correcte des actifs . 25
8.1.4 Restitution des actifs .25
8.2 Classification de l'information .25
8.2.1 Classification des informations . 26
8.2.2 Marquage des informations. 27
8.2.3 Manipulation des actifs . 27
8.3 Manipulation des supports .28
8.3.1 Gestion des supports amovibles .28
8.3.2 Mise au rebut des supports .28
iii
© ISO/IEC 2023 – Tous droits réservés
ISO/IEC27002:redline:2023(F)
8.3.3 Transfert physique des supports .29
9 Contrôle d'accès .30
9.1 Exigences métier en matière de contrôle d'accès .30
9.1.1 Politique de contrôle d'accès .30
9.1.2 Accès aux réseaux et aux services en réseau . 31
9.2 Gestion de l’accès utilisateur . . 32
9.2.1 Enregistrement et désinscription des utilisateurs . 32
9.2.2 Maîtrise de la gestion des accès utilisateur . 32
9.2.3 Gestion des privilèges d’accès . 33
9.2.4 Gestion des informations secrètes d'authentification des utilisateurs .34
9.2.5 Revue des droits d'accès utilisateur . .34
9.2.6 Suppression ou adaptation des droits d'accès . 35
9.3 Responsabilités des utilisateurs . 36
9.3.1 Utilisation d'informations secrètes d'authentification .36
9.4 Contrôle de l'accès au système et aux applications . 37
9.4.1 Restriction d'accès à l'information . 37
9.4.2 Sécuriser les procédures de connexion . . 37
9.4.3 Système de gestion des mots de passe .38
9.4.4 Utilisation de programmes utilitaires à privilèges .39
9.4.5 Contrôle d’accès au code source des programmes .39
10 Cryptographie .40
10.1 Mesures cryptographiques .40
10.1.1 Politique d’utilisation des mesures cryptographiques .40
10.1.2 Gestion des clés. 41
11 Sécurité physique et environnementale.43
11.1 Zones sécurisées . 43
11.1.1 Périmètre de sécurité physique . 43
11.1.2 Contrôles physiques des accès .44
11.1.3 Sécurisation des bureaux, des salles et des équipements .44
11.1.4 Protection contre les menaces extérieures et environnementales . 45
11.1.5 Travail dans les zones sécurisées . 45
11.1.6 Zones de livraison et de chargement . 45
11.2 Matériels . .46
11.2.1 Emplacement et protection du matériel .46
11.2.2 Services généraux . 47
11.2.3 Sécurité du câblage . 47
11.2.4 Maintenance du matériel .48
11.2.5 Sortie des actifs .48
11.2.6 Sécurité du matériel et des actifs hors des locaux .49
11.2.7 Mise au rebut ou recyclage sécurisé(e) du matériel .50
11.2.8 Matériel utilisateur laissé sans surveillance .50
11.2.9 Politique du bureau propre et de l’écran vide . 51
12 Sécurité liée à l'exploitation .51
12.1 Procédures et responsabilités liées à l’exploitation . 51
12.1.1 Procédures d'exploitation documentées . 52
12.1.2 Gestion des changements . 52
12.1.3 Dimensionnement .53
12.1.4 Séparation des environnements de développement, de test et d'exploitation .54
12.2 Protection contre les logiciels malveillants. 55
12.2.1 Mesures contre les logiciels malveillants . 55
12.3 Sauvegarde .56
12.3.1 Sauvegarde des informations .56
12.4 Journalisation et surveillance . 57
12.4.1 Journalisation des événements . . 57
12.4.2 Protection de l'information journalisée .58
12.4.3 Journaux administrateur et opérateur . 59
iv
© ISO/IEC 2023 – Tous droits réservés
ISO/IEC27002:redline:2023(F)
12.4.4 Synchronisation des horloges . 59
12.5 Maîtrise des logiciels en exploitation . 59
12.5.1 Installation de logiciels sur des systèmes en exploitation .60
12.6 Gestion des vulnérabilités techniques . 61
12.6.1 Gestion des vulnérabilités techniques . 61
12.6.2 Restrictions liées à l'installation de logiciels . 62
12.7 Considérations sur l’audit du système d’information .63
12.7.1 Mesures relatives à l’audit des systèmes d’information .63
13 Sécurité des communications .63
13.1 Management de la sécurité des réseaux .63
13.1.1 Contrôle des réseaux .63
13.1.2 Sécurité des services de réseau .64
13.1.3 Cloisonnement des réseaux .64
13.2 Transfert de l'information .65
13.2.1 Politiques et procédures de transfert de l'information .65
13.2.2 Accords en matière de transfert d'information .66
13.2.3 Messagerie électronique. 67
13.2.4 Engagements de confidentialité ou de non-divulgation . .68
14 Acquisition, développement et maintenance des systèmes d’information .69
14.1 Exigences de sécurité applicables aux systèmes d’information .69
14.1.1 Analyse et spécification des exigences de sécurité de l’information .69
14.1.2 Sécurisation des services d'application sur les réseaux publics . 70
14.1.3 Protection des transactions liées aux services d'application . 71
14.2 Sécurité des processus de développement et d’assistance technique .72
14.2.1 Politique de développement sécurisé .72
14.2.2 Procédures de contrôle des changements apportés au système .73
14.2.3 Revue technique des applications après changement apporté à la
plateforme d’exploitation .74
14.2.4 Restrictions relatives aux changements apportés aux progiciels .74
14.2.5 Principes d’ingénierie de la sécurité des systèmes . 75
14.2.6 Environnement de développement sécurisé . 75
14.2.7 Développement externalisé . 76
14.2.8 Phase de test de la sécurité du système .77
14.2.9 Test de conformité du système .77
14.3 Données de test .77
14.3.1 Protection des données de test .77
15 Relations avec les fournisseurs .78
15 5 .
Moyens de maîtrise organisationnels .78
5.1 Politiques de sécurité de l'information . 78
5.2 Fonctions et responsabilités liées à la sécurité de l'information .80
5.3 Séparation des tâches .81
5.4 Responsabilités de la direction .82
5.5 Contacts avec les autorités .83
5.6 Contacts avec des groupes d’intérêt spécifiques .84
5.7 Renseignements sur les menaces .85
5.8 Sécurité de l'information dans la gestion de projet .86
5.9 Inventaire des informations et autres actifs associés .88
5.10 Utilisation correcte des informations et autres actifs associés .90
5.11 Restitution des actifs . 91
5.12 Classification des informations . 92
5.13 Marquage des informations .93
5.14 Transfert des informations . 95
5.15 Contrôle d'accès .97
5.16 Gestion des identités .99
5.17 Informations d'authentification .100
v
© ISO/IEC 2023 – Tous droits réservés
ISO/IEC27002:redline:2023(F)
5.18 Droits d'accès .102
5.19 Sécurité de l'information dans les relations avec les fournisseurs .104
5.20 La sécurité de l'information dans les accords conclus avec les fournisseurs .106
15.1 Sécurité de l’information dans les relations avec les fournisseurs .108
15.1.1 Politique de sécurité de l'information dans les relations avec les
fournisseurs . .108
15.1.2 La sécurité dans les accords conclus avec les fournisseurs .109
15.1.3 Chaine d’approvisionnement informatique . 111
15.1 5.21 .
Gestion de la sécurité de l'information dans la chaîne d'approvisionnement TIC .112
15.2 Gestion de la prestation du service . 114
15.2 5.22 .
Surveillance, révision et gestion des changements des services fournisseurs . 114
15.2.1 Surveillance et revue des services des fournisseurs . 114
15.2.2 Gestion des changements apportés dans les services des fournisseurs .115
5.23 Sécurité de l'information dans l'utilisation de services en nuage . 117
5.24 Planification et préparation de la gestion des incidents liés à la sécurité de
l'information .120
5.25 Évaluation des événements liés à la sécurité de l'information et prise de décision .122
5.26 Réponse aux incidents liés à la sécurité de l'information .122
5.27 Tirer des enseignements des incidents liés à la sécurité de l'information .123
5.28 Collecte des preuves .124
5.29 Sécurité de l'information pendant une perturbation .125
5.30 Préparation des TIC pour la continuité d'activité .126
5.31 Exigences légales, statutaires, réglementaires et contractuelles .127
5.32 Droits de propriété intellectuelle .129
5.33 Protection des documents d'activité .130
5.34 Protection de la vie privée et des DCP .132
5.35 Révision indépendante de la sécurité de l'information .133
5.36 Conformité aux politiques, règles et normes de sécurité de l'information .134
5.37 Procédures d'exploitation documentées .135
16 Gestion des incidents liés à la sécurité de l'information . 136
16 6 .
Moyens de maîtrise applicables aux personnes . 136
6.1 Sélection des candidats .136
6.2 Termes et conditions du contrat de travail .137
16.1 6.3 .
Gestion des incidents liés à la sécurité de l’information et améliorations .138
16.1 6.3 .
Sensibilisation, enseignement et formation en sécurité de l'information .138
16.1.1 Responsabilités et procédures .139
16.1.2 Signalement des événements liés à la sécurité de l’information .140
16.1.3 Signalement des failles liées à la sécurité de l’information . 141
16.1.4 Appréciation des événements liés à la sécurité de l'information et prise de
décision . 141
16.1.5 Réponse aux incidents liés à la sécurité de l’information . 141
16.1.6 Tirer des enseignements des incidents liés à la sécurité de l’information . 142
16.1.7 Recueil de preuves . 142
6.4 Processus disciplinaire . 145
6.5 Responsabilités après la fin ou le changement d’un emploi .146
6.6 Accords de confidentialité ou de non-divulgation . 147
6.7 Travail à distance .148
6.8 Déclaration des événements liés à la sécurité de l'information .150
17 Aspects de la sécurité de l’information dans la gestion de la continuité de l’activité . 151
17 7 .
Moyens de maîtrise physique . 151
vi
© ISO/IEC 2023 – Tous droits réservés
ISO/IEC27002:redline:2023(F)
7.1 Périmètres de sécurité physique . 151
7.2 Les entrées physiques .152
7.3 Sécurisation des bureaux, des salles et des installations.154
7.4 Surveillance de la sécurité physique .154
7.5 Protection contre les menaces physiques et environnementales .155
7.6 Travail dans les zones sécurisées .157
7.7 Bureau vide et écran vide .157
7.8 Emplacement et protection du matériel .158
7.9 Sécurité des actifs hors des locaux .159
17.1 Continuité de la sécurité de l’information.160
17.1 7.10 .
Supports de stockage .160
17.1.1 Organisation de la continuité de la sécurité de l'information . 161
17.1.2 Mise en œuvre de la continuité de la sécurité de l'information . 161
17.1.3 Vérifier, revoir et évaluer la continuité de la sécurité de l'information .162
7.11 Services supports .164
7.12 Sécurité du câblage .165
7.13 Maintenance du matériel .166
17.2 Redondances. 167
17.2 7.14 .
Élimination ou recyclage sécurisé(e) du matériel . 167
17.2.1 Disponibilité des moyens de traitement de l’information . 167
18 Conformité . 169
18 8 .
Moyens de maîtrise technologiques . 169
8.1 Terminaux utilisateurs .169
8.2 Droits d'accès privilégiés . . 171
8.3 Restrictions d'accès aux informations .173
8.4 Accès aux codes source . 175
18.1 Conformité aux obligations légales et réglementaires . 176
18.1 8.5 .
Authentification sécurisée . 176
18.1.1 Identification de la législation et des exigences contractuelles applicables . 176
18.1.2 Droits de propriété intellectuelle . 176
18.1.3 Protection des enregistrements .177
18.1.4 Protection de la vie privée et protection des données à caractère personnel .178
18.1.5 Réglementation relative aux mesures cryptographiques .179
8.6 Dimensionnement .181
8.7 Protection contre les programmes malveillants (malware) .182
8.8 Gestion des vulnérabilités techniques .184
8.9 Gestion des configurations .188
8.10 Suppression des informations .190
8.11 Masquage des données . 191
8.12 Prévention la fuite de données . 193
8.13 Sauvegarde des informations .194
8.14 Redondance des moyen
...



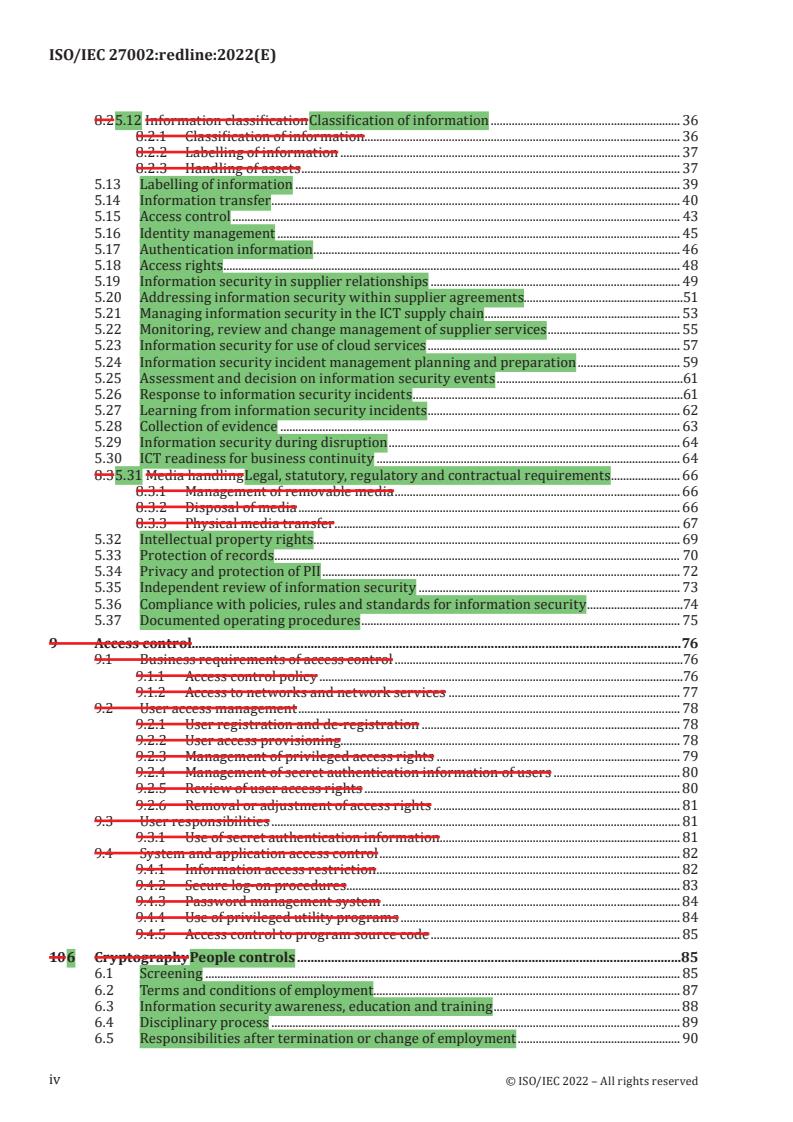





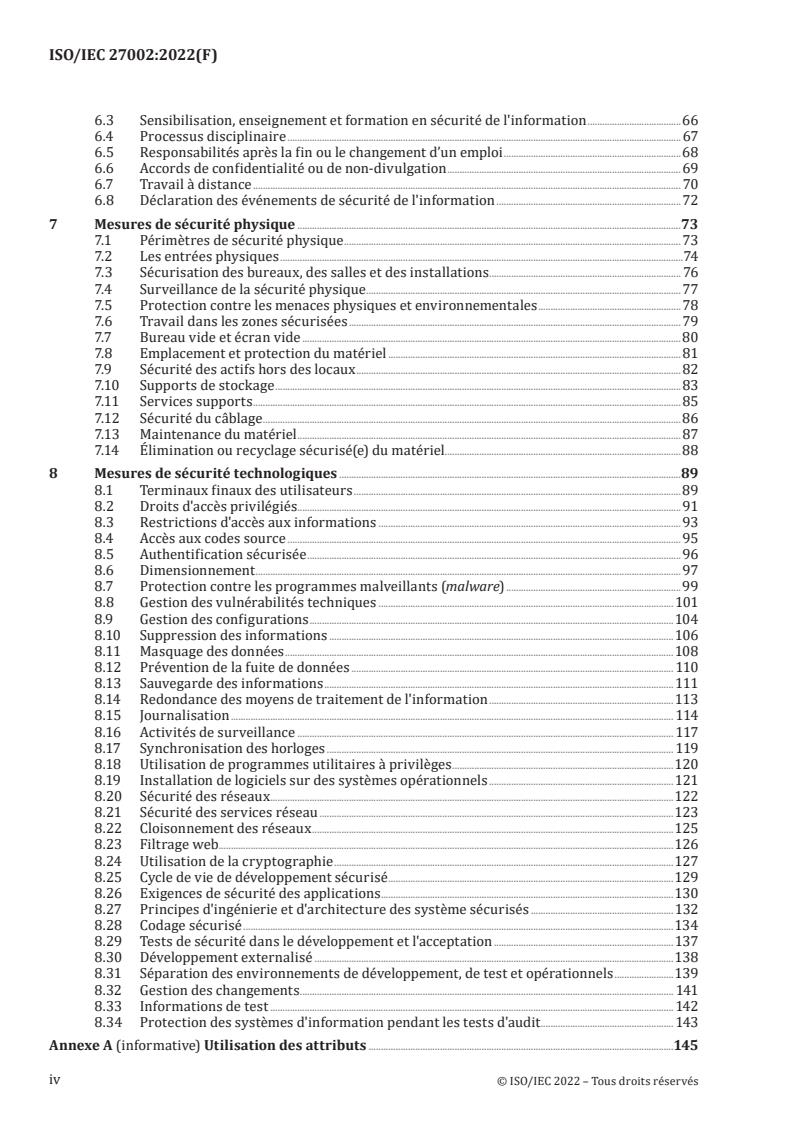
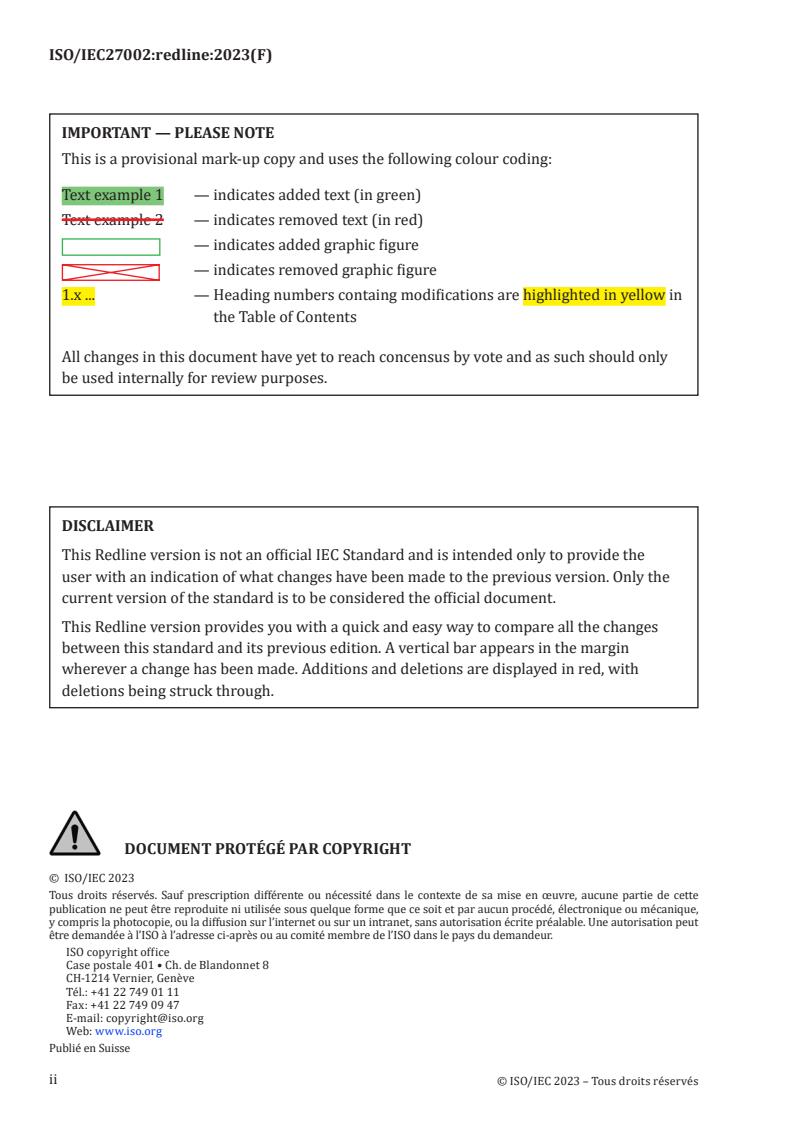
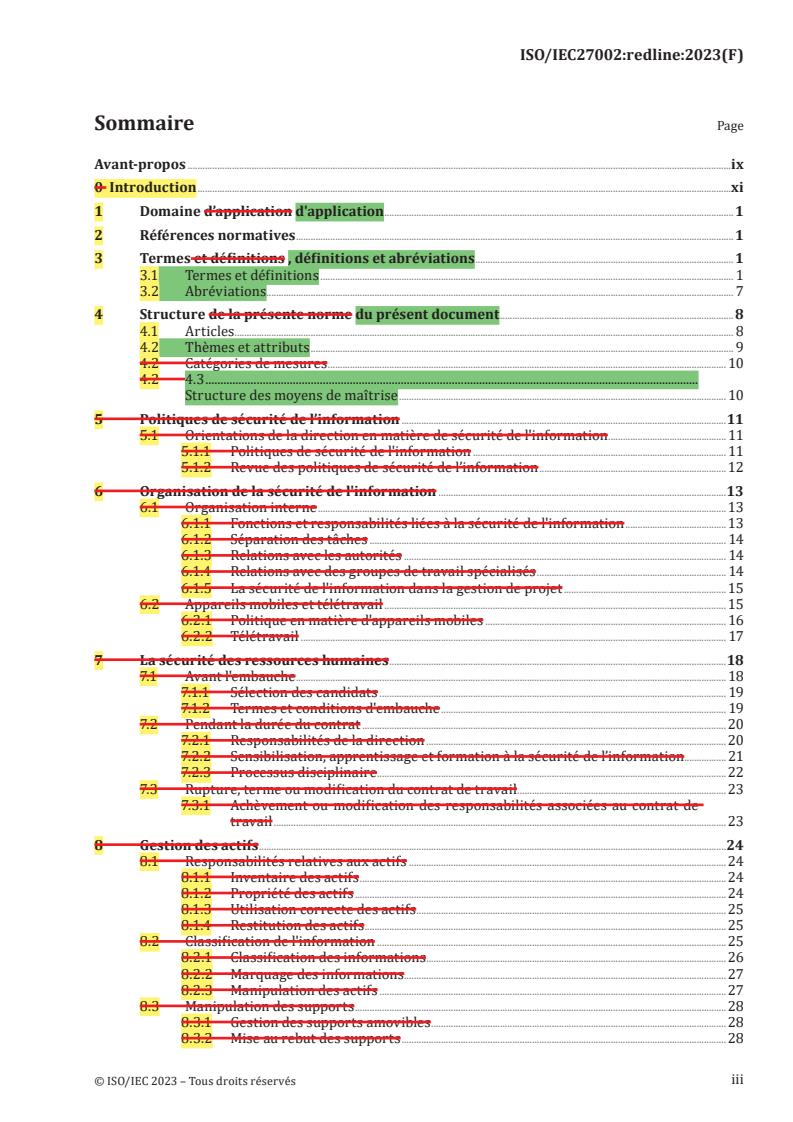
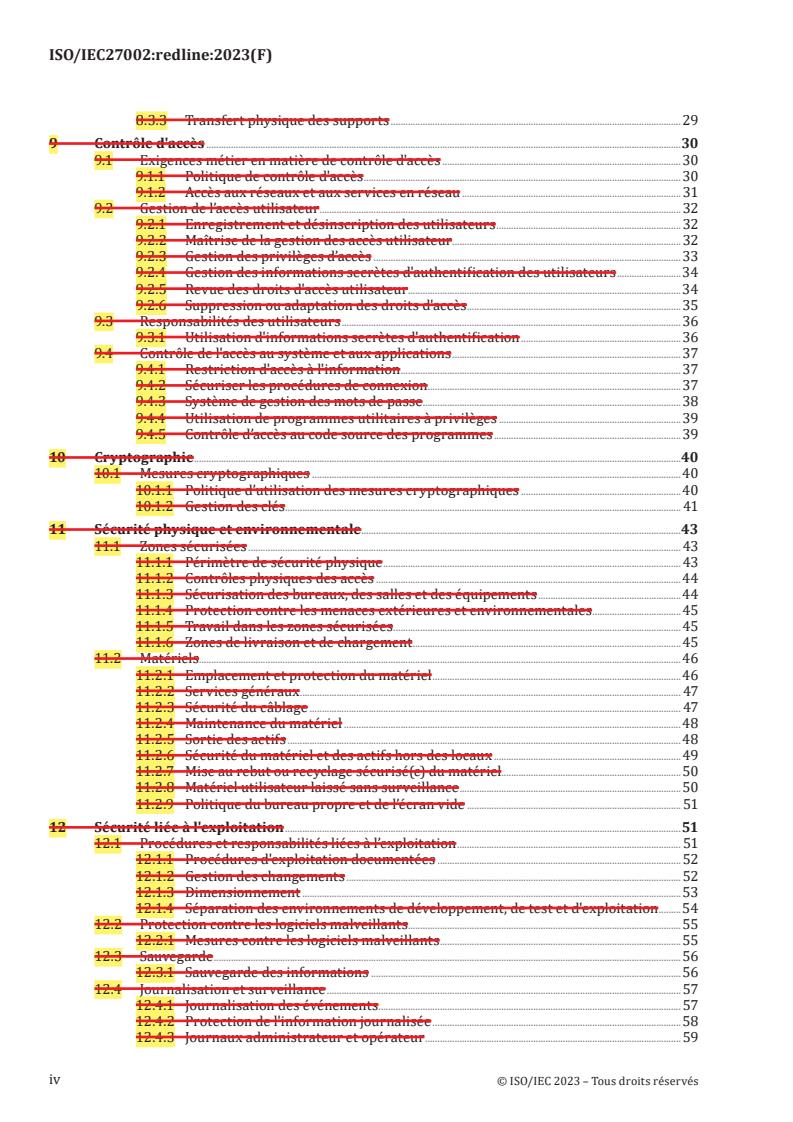
Questions, Comments and Discussion
Ask us and Technical Secretary will try to provide an answer. You can facilitate discussion about the standard in here.
Loading comments...