CEN/TS 419261:2015
(Main)Security requirements for trustworthy systems managing certificates and time-stamps
Security requirements for trustworthy systems managing certificates and time-stamps
1.1 General
This Technical Specification establishes security requirements for TWSs that can be used by a TSP in order to issue QCs and Non-Qualified Certificates (NQCs) as well as electronic time-stamps in accordance with Dir.1999/93/EC and with [Reg.910/2014/EU].
Security requirements for the Subject Device Provision Service, which includes SCDev/QSCD provision to subjects, are defined in this TS. However, requirements specific to SCDev/QSCD devices, as used by subjects of the TSP, are outside the scope of this TS. These requirements are defined as Common Criteria [CC] Protection Profiles (PP) in the EN 419211 series.
Recommendations for the cryptographic algorithms to be supported by TWSs are provided in ETSI/TS 119 312.
Although this TS is based on the use of public key cryptography, it does not require or define any particular communication protocol or format for electronic signatures, certificates, certificate revocation lists, certificate status information and time-stamp tokens. It only assumes certain types of information to be present in the certificates in accordance with Annex I of Dir.1999/93/EC and of [Reg.910/2014/EU]. Interoperability between TSP systems and subject systems is outside the scope of this document.
The use of TWSs that are already compliant to relevant security requirements of this TS should support TSPs in reducing their burden to establish conformance of their policy to ETSI TS 119 411-1, 119 411-2, and 119 421 (or equivalent ENs to be subsequently published) and in meeting the Annex I and Annex II requirements of Dir.1999/93/EC as well as the requirements from Annex I and Article 24.2 (e) of [Reg.910/2014/EU].
1.2 European Regulation-specific
The main focus of this document is on the requirements in Article 24.2 (e) of [Reg.910/2014/EU] whilst still facilitating the meeting of requirements in Dir.1999/93/EC, Annex II (f). In considering [Reg.910/2014/EU] it is important to take into account the following requirements of particular relevance to TSP trustworthy systems:
a) Article 24.2 (f) – “use trustworthy systems to store data provided to it, in a verifiable form so that:
(i) they are publicly available for retrieval only where the consent of the person to whom the data relates has been obtained,
(ii) only authorised persons can make entries and changes to the stored data,
(iii) the data can be checked for authenticity”;
b) Article 24.2 (g) – “take appropriate measures against forgery and theft of data”;
c) Article 24.2 (h) – “record and keep accessible for an appropriate period of time, including after the activities of the qualified trust service provider have ceased, all relevant information concerning data issued and received by the qualified trust service provider, in particular, for the purpose of providing evidence in legal proceedings and for the purpose of ensuring continuity of the service. Such recording may be done electronically”;
d) Article 24.2 (j) – “ensure lawful processing of personal data in accordance with Directive 95/46/EC”;
e) Article 24.2 (k) – “in case of qualified trust service providers issuing qualified certificates, establish and keep updated a certificate database”;
f) Article 24.3 – “If a qualified trust service provider issuing qualified certificates decides to revoke a certificate, it shall register such revocation in its certificate database and publish the revocation status of the certificate in a timely manner, and in any event within 24 hours after the receipt of the request. The revocation shall become effective immediately upon its publication”;
g) Article 24.4 – "With regard to paragraph 3, qualified trust service providers issuing qualified certificates shall provide to any relying party information on the validity or revocation status of qualified certificates issued by them.
Sicherheitsanforderungen für vertrauenswürdige Systeme zur Verwaltung von Zertifikaten für elektronische Signaturen und Zeitstempel
1.1 Allgemeines
Diese Technische Spezifikation legt Sicherheitsanforderungen an TWS fest, die durch einen TSP genutzt werden können, um QC und nicht qualifizierte Zertifikate (NQC, en: non-qualified certificates) wie auch elektronische Zeitstempel nach der Richtlinie 1999/93/EG und [Verordnung 910/2014/EU] auszugeben.
Die Sicherheitsanforderungen an den Bereitstellungsdienst für Signaturerstellungseinheiten für Zertifikat-inhaber, der die Bereitstellung von SCDev/QSCD an Zertifikatinhaber umfasst, sind in dieser TS definiert. Die für SCDev/QSCD spezifischen Anforderungen, wie sie von den Zertifikatinhabern der TSP angewendet werden, liegen jedoch außerhalb des Anwendungsbereichs dieser TS. Die entsprechenden Anforderungen sind in der Reihe EN 419211 als Schutzprofile (PP, en: Protection Profiles) nach den Common Criteria (CC) definiert.
Empfehlungen hinsichtlich der durch TWS zu unterstützenden kryptographischen Algorithmen sind in ETSI/TS 119 312 angegeben.
Obwohl diese TS auf der Public-Key-Kryptografie beruht, verlangt oder definiert sie kein bestimmtes Kommunikationsprotokoll oder -format für elektronische Signaturen, Zertifikate, Zertifikatsperrslisten, Zertifikatstatusinformationen und Zeitstempel-Token. Ihr liegt ausschließlich die Annahme zugrunde, dass die Zertifikate bestimmte Arten von Informationen nach Richtlinie 1999/93/EG, Anhang I und nach [Verordnung 910/2014/EU], enthalten. Die Interoperabilität zwischen TSP-Systemen und Zertifikatinhaber-Systemen liegt außerhalb des Anwendungsbereichs dieses Dokuments.
Die Nutzung von TWS, die bereits die relevanten Sicherheitsanforderungen dieser TS erfüllen, sollte den TSPs das Erreichen der Übereinstimmung ihrer Grundsätze mit ETSI/TS 119 411-1, 119 411-2 und 119 421 (oder entsprechender Europäischer Normen die zu einem späteren Zeitpunkt veröffentlicht werden) (sowie die Erfüllung der Anforderungen nach Richtlinie 1999/93/EG, Anhang I und Anhang II, als auch der Anforderungen nach [Verordnung 910/2014/EU], Anhang I und Artikel 24.2 (e), erleichtern.
1.2 Spezifisch für die Europäische Verordnung
Der Hauptfokus dieses Dokuments liegt auf den Anforderungen nach [Verordnung 910/2014/EU], Artikel 24.2 (e) während weiterhin die Erfüllung der Anforderungen nach Richtlinie 1999/93/EG, Anhang II (f) unterstützt wird. Unter Beachtung der [Verordnung 910/2014/EU] ist jedoch die Berücksichtigung der folgenden Anforderungen, die teilweise für vertrauenswürdige Systeme von TSP Relevanz haben, erforderlich:
a) Artikel 24.2 (f) — „vertrauenswürdige Systeme für die Speicherung der ihnen übermittelten Daten in einer überprüfbaren Form, so dass
i) diese nur mit Zustimmung der Person, auf die sich die Daten beziehen, öffentlich abrufbar sind;
ii) nur befugte Personen Daten eingeben und gespeicherte Daten ändern können;
iii) die Daten auf Ihre Echtheit hin überprüft werden können;
b) Artikel 24.2 (g) — „geeignete Maßnahmen gegen Fälschung und Diebstahl von Daten ergreifen“;
c) Artikel 24.2 (h) — „alle einschlägigen Informationen über die von dem qualifizierten Vertrauens-dienstanbieter ausgegebenen und empfangenen Daten aufzeichnen und sie so aufbewahren, dass sie über einen angemessenen Zeitraum, auch über den Zeitpunkt der Einstellung der Tätigkeit des qualifizierten Vertrauensdienstanbieters hinaus, verfügbar sind, um insbesondere bei Gerichtsverfahren entsprechende Beweise liefern zu können und die Kontinuität des Dienstes sicherzustellen. Die Aufzeichnung kann in elektronischer Form erfolgen;
d) Artikel 24.2 (j) — „eine rechtmäßige Verarbeitung personenbezogener Daten gemäß Richtlinie 95/46/EG sicherstellen;
e) Artikel 24.2 (k) — „im Falle qualifizierter Vertrauensdiensteanbieter, die qualifizierte Zertifikate ausstellen, eine Zertifikatsdatenbank erstellen und auf dem neuesten Stand halten“.
Exigences de sécurité pour systèmes de confiance gérant des certificats et des horodatages
Varnostne zahteve za zaupanja vredne sisteme, ki upravljajo potrdila za elektronsko podpisovanje
General Information
- Status
- Published
- Publication Date
- 24-Mar-2015
- Drafting Committee
- CEN/TC 224/WG 17 - Protection Profiles in the context of SSCD
- Current Stage
- 9093 - Decision to confirm - Review Enquiry
- Start Date
- 28-Nov-2023
- Completion Date
- 11-Feb-2026
Relations
- Effective Date
- 28-Jan-2026
- Effective Date
- 28-Jan-2026
- Effective Date
- 28-Jan-2026
- Effective Date
- 28-Jan-2026
- Effective Date
- 28-Jan-2026
- Refers
EN 419211-1:2014 - Protection profiles for secure signature creation device - Part 1: Overview - Effective Date
- 28-Jan-2026
Overview - what CEN/TS 419261:2015 covers
CEN/TS 419261:2015 defines security requirements for trustworthy systems (TWS) used by Trust Service Providers (TSPs) to issue and manage qualified certificates, non‑qualified certificates (NQCs) and electronic time‑stamps under Directive 1999/93/EC and Regulation (EU) No 910/2014 (eIDAS). It specifies system‑level controls (management, operational, physical and network) and service‑specific requirements for certificate and time‑stamp lifecycle management. The document is a CEN Technical Specification intended for designers, implementers and customers of TWS components.
Key topics and technical requirements
Highlights of the technical scope and requirements in CEN/TS 419261:2015:
Core TSP services covered
- Registration Service (identity and attribute verification)
- Certificate Generation Service
- Dissemination Service (certificate and policy distribution)
- Revocation Management Service
- Revocation Status Service
- Subject Device Provision Service (SCDev/QSCD provisioning)
- Time‑stamping Service
General security areas
- Management and governance of TWS
- Systems & operations security
- Identification & authentication of operators and subjects
- System access control and authorization
- Key management (storage, generation, protection)
- Accounting & auditing (logging, evidence preservation)
- Archiving, backup & recovery
- Network and physical security for the operational environment
Regulatory alignment
- Focus on Article 24.2(e) of Regulation 910/2014 (eIDAS) and relevant provisions from Dir.1999/93/EC
- Supports meeting Annex I/II requirements and timely publication/recording of revocation information (e.g., within 24 hours)
Interoperability & cryptography
- Recommends cryptographic algorithms via ETSI/TS 119 312
- Does not mandate specific protocols or certificate formats; assumes certificate content consistent with Annex I of the Directive/Regulation
Practical applications - who uses this standard
- Trust Service Providers (TSPs) and Certification Service Providers (CSPs) implementing certificate/time‑stamp infrastructures
- System architects & developers designing TWS components
- Security officers & compliance teams demonstrating conformance to eIDAS
- Conformity assessors and auditors evaluating TWS against European regulatory requirements
- Providers of secure device provisioning (SCDev/QSCD) and managed PKI services
Adoption of CEN/TS 419261:2015 helps reduce the burden of proving policy conformance to ETSI TS 119 411‑1/‑2 and TS 119 421 and supports legal evidence preservation and secure certificate lifecycle operations.
Related standards
- ETSI/TS 119 312 (cryptographic algorithm recommendations)
- ETSI TS 119 411‑1 / 119 411‑2 and ETSI TS 119 421 (certificate/time‑stamp policy standards)
- EN 419221 (Common Criteria protection profiles for signature creation devices)
Get Certified
Connect with accredited certification bodies for this standard

BSI Group
BSI (British Standards Institution) is the business standards company that helps organizations make excellence a habit.

Bureau Veritas
Bureau Veritas is a world leader in laboratory testing, inspection and certification services.

DNV
DNV is an independent assurance and risk management provider.
Sponsored listings
Frequently Asked Questions
CEN/TS 419261:2015 is a technical specification published by the European Committee for Standardization (CEN). Its full title is "Security requirements for trustworthy systems managing certificates and time-stamps". This standard covers: 1.1 General This Technical Specification establishes security requirements for TWSs that can be used by a TSP in order to issue QCs and Non-Qualified Certificates (NQCs) as well as electronic time-stamps in accordance with Dir.1999/93/EC and with [Reg.910/2014/EU]. Security requirements for the Subject Device Provision Service, which includes SCDev/QSCD provision to subjects, are defined in this TS. However, requirements specific to SCDev/QSCD devices, as used by subjects of the TSP, are outside the scope of this TS. These requirements are defined as Common Criteria [CC] Protection Profiles (PP) in the EN 419211 series. Recommendations for the cryptographic algorithms to be supported by TWSs are provided in ETSI/TS 119 312. Although this TS is based on the use of public key cryptography, it does not require or define any particular communication protocol or format for electronic signatures, certificates, certificate revocation lists, certificate status information and time-stamp tokens. It only assumes certain types of information to be present in the certificates in accordance with Annex I of Dir.1999/93/EC and of [Reg.910/2014/EU]. Interoperability between TSP systems and subject systems is outside the scope of this document. The use of TWSs that are already compliant to relevant security requirements of this TS should support TSPs in reducing their burden to establish conformance of their policy to ETSI TS 119 411-1, 119 411-2, and 119 421 (or equivalent ENs to be subsequently published) and in meeting the Annex I and Annex II requirements of Dir.1999/93/EC as well as the requirements from Annex I and Article 24.2 (e) of [Reg.910/2014/EU]. 1.2 European Regulation-specific The main focus of this document is on the requirements in Article 24.2 (e) of [Reg.910/2014/EU] whilst still facilitating the meeting of requirements in Dir.1999/93/EC, Annex II (f). In considering [Reg.910/2014/EU] it is important to take into account the following requirements of particular relevance to TSP trustworthy systems: a) Article 24.2 (f) – “use trustworthy systems to store data provided to it, in a verifiable form so that: (i) they are publicly available for retrieval only where the consent of the person to whom the data relates has been obtained, (ii) only authorised persons can make entries and changes to the stored data, (iii) the data can be checked for authenticity”; b) Article 24.2 (g) – “take appropriate measures against forgery and theft of data”; c) Article 24.2 (h) – “record and keep accessible for an appropriate period of time, including after the activities of the qualified trust service provider have ceased, all relevant information concerning data issued and received by the qualified trust service provider, in particular, for the purpose of providing evidence in legal proceedings and for the purpose of ensuring continuity of the service. Such recording may be done electronically”; d) Article 24.2 (j) – “ensure lawful processing of personal data in accordance with Directive 95/46/EC”; e) Article 24.2 (k) – “in case of qualified trust service providers issuing qualified certificates, establish and keep updated a certificate database”; f) Article 24.3 – “If a qualified trust service provider issuing qualified certificates decides to revoke a certificate, it shall register such revocation in its certificate database and publish the revocation status of the certificate in a timely manner, and in any event within 24 hours after the receipt of the request. The revocation shall become effective immediately upon its publication”; g) Article 24.4 – "With regard to paragraph 3, qualified trust service providers issuing qualified certificates shall provide to any relying party information on the validity or revocation status of qualified certificates issued by them.
1.1 General This Technical Specification establishes security requirements for TWSs that can be used by a TSP in order to issue QCs and Non-Qualified Certificates (NQCs) as well as electronic time-stamps in accordance with Dir.1999/93/EC and with [Reg.910/2014/EU]. Security requirements for the Subject Device Provision Service, which includes SCDev/QSCD provision to subjects, are defined in this TS. However, requirements specific to SCDev/QSCD devices, as used by subjects of the TSP, are outside the scope of this TS. These requirements are defined as Common Criteria [CC] Protection Profiles (PP) in the EN 419211 series. Recommendations for the cryptographic algorithms to be supported by TWSs are provided in ETSI/TS 119 312. Although this TS is based on the use of public key cryptography, it does not require or define any particular communication protocol or format for electronic signatures, certificates, certificate revocation lists, certificate status information and time-stamp tokens. It only assumes certain types of information to be present in the certificates in accordance with Annex I of Dir.1999/93/EC and of [Reg.910/2014/EU]. Interoperability between TSP systems and subject systems is outside the scope of this document. The use of TWSs that are already compliant to relevant security requirements of this TS should support TSPs in reducing their burden to establish conformance of their policy to ETSI TS 119 411-1, 119 411-2, and 119 421 (or equivalent ENs to be subsequently published) and in meeting the Annex I and Annex II requirements of Dir.1999/93/EC as well as the requirements from Annex I and Article 24.2 (e) of [Reg.910/2014/EU]. 1.2 European Regulation-specific The main focus of this document is on the requirements in Article 24.2 (e) of [Reg.910/2014/EU] whilst still facilitating the meeting of requirements in Dir.1999/93/EC, Annex II (f). In considering [Reg.910/2014/EU] it is important to take into account the following requirements of particular relevance to TSP trustworthy systems: a) Article 24.2 (f) – “use trustworthy systems to store data provided to it, in a verifiable form so that: (i) they are publicly available for retrieval only where the consent of the person to whom the data relates has been obtained, (ii) only authorised persons can make entries and changes to the stored data, (iii) the data can be checked for authenticity”; b) Article 24.2 (g) – “take appropriate measures against forgery and theft of data”; c) Article 24.2 (h) – “record and keep accessible for an appropriate period of time, including after the activities of the qualified trust service provider have ceased, all relevant information concerning data issued and received by the qualified trust service provider, in particular, for the purpose of providing evidence in legal proceedings and for the purpose of ensuring continuity of the service. Such recording may be done electronically”; d) Article 24.2 (j) – “ensure lawful processing of personal data in accordance with Directive 95/46/EC”; e) Article 24.2 (k) – “in case of qualified trust service providers issuing qualified certificates, establish and keep updated a certificate database”; f) Article 24.3 – “If a qualified trust service provider issuing qualified certificates decides to revoke a certificate, it shall register such revocation in its certificate database and publish the revocation status of the certificate in a timely manner, and in any event within 24 hours after the receipt of the request. The revocation shall become effective immediately upon its publication”; g) Article 24.4 – "With regard to paragraph 3, qualified trust service providers issuing qualified certificates shall provide to any relying party information on the validity or revocation status of qualified certificates issued by them.
CEN/TS 419261:2015 is classified under the following ICS (International Classification for Standards) categories: 03.120.20 - Product and company certification. Conformity assessment; 35.030 - IT Security; 35.040 - Information coding; 35.240.30 - IT applications in information, documentation and publishing. The ICS classification helps identify the subject area and facilitates finding related standards.
CEN/TS 419261:2015 has the following relationships with other standards: It is inter standard links to EN 419211-2:2013, EN 419211-6:2014, EN 419211-5:2013, EN 419211-4:2013, EN 419211-3:2013, EN 419211-1:2014. Understanding these relationships helps ensure you are using the most current and applicable version of the standard.
CEN/TS 419261:2015 is associated with the following European legislation: Standardization Mandates: M/460. When a standard is cited in the Official Journal of the European Union, products manufactured in conformity with it benefit from a presumption of conformity with the essential requirements of the corresponding EU directive or regulation.
CEN/TS 419261:2015 is available in PDF format for immediate download after purchase. The document can be added to your cart and obtained through the secure checkout process. Digital delivery ensures instant access to the complete standard document.
Standards Content (Sample)
SLOVENSKI STANDARD
01-julij-2015
Varnostne zahteve za zaupanja vredne sisteme, ki upravljajo potrdila za
elektronsko podpisovanje
Security requirements for trustworthy systems managing certificates for electronic
signatures
Sicherheitsanforderungen für vertrauenswürdige Systeme zur Verwaltung von
Zertifikaten für elektronische Signaturen
Exigences de sécurité pour systèmes de confiance gérant des certificats pour signature
électronique
Ta slovenski standard je istoveten z: CEN/TS 419261:2015
ICS:
35.040 Nabori znakov in kodiranje Character sets and
informacij information coding
35.240.30 Uporabniške rešitve IT v IT applications in information,
informatiki, dokumentiranju in documentation and
založništvu publishing
2003-01.Slovenski inštitut za standardizacijo. Razmnoževanje celote ali delov tega standarda ni dovoljeno.
TECHNICAL SPECIFICATION
CEN/TS 419261
SPÉCIFICATION TECHNIQUE
TECHNISCHE SPEZIFIKATION
March 2015
ICS 03.120.20; 35.040; 35.240.30
English Version
Security requirements for trustworthy systems managing
certificates and time-stamps
Exigences de sécurité pour systèmes de confiance gérant Sicherheitsanforderungen für vertrauenswürdige Systeme
des certificats et des horodatages zur Verwaltung von Zertifikaten für elektronische Signaturen
und Zeitstempel
This Technical Specification (CEN/TS) was approved by CEN on 18 November 2014 for provisional application.
The period of validity of this CEN/TS is limited initially to three years. After two years the members of CEN will be requested to submit their
comments, particularly on the question whether the CEN/TS can be converted into a European Standard.
CEN members are required to announce the existence of this CEN/TS in the same way as for an EN and to make the CEN/TS available
promptly at national level in an appropriate form. It is permissible to keep conflicting national standards in force (in parallel to the CEN/TS)
until the final decision about the possible conversion of the CEN/TS into an EN is reached.
CEN members are the national standards bodies of Austria, Belgium, Bulgaria, Croatia, Cyprus, Czech Republic, Denmark, Estonia,
Finland, Former Yugoslav Republic of Macedonia, France, Germany, Greece, Hungary, Iceland, Ireland, Italy, Latvia, Lithuania,
Luxembourg, Malta, Netherlands, Norway, Poland, Portugal, Romania, Slovakia, Slovenia, Spain, Sweden, Switzerland, Turkey and United
Kingdom.
EUROPEAN COMMITTEE FOR STANDARDIZATION
COMITÉ EUROPÉEN DE NORMALISATION
EUROPÄISCHES KOMITEE FÜR NORMUNG
CEN-CENELEC Management Centre: Avenue Marnix 17, B-1000 Brussels
© 2015 CEN All rights of exploitation in any form and by any means reserved Ref. No. CEN/TS 419261:2015 E
worldwide for CEN national Members.
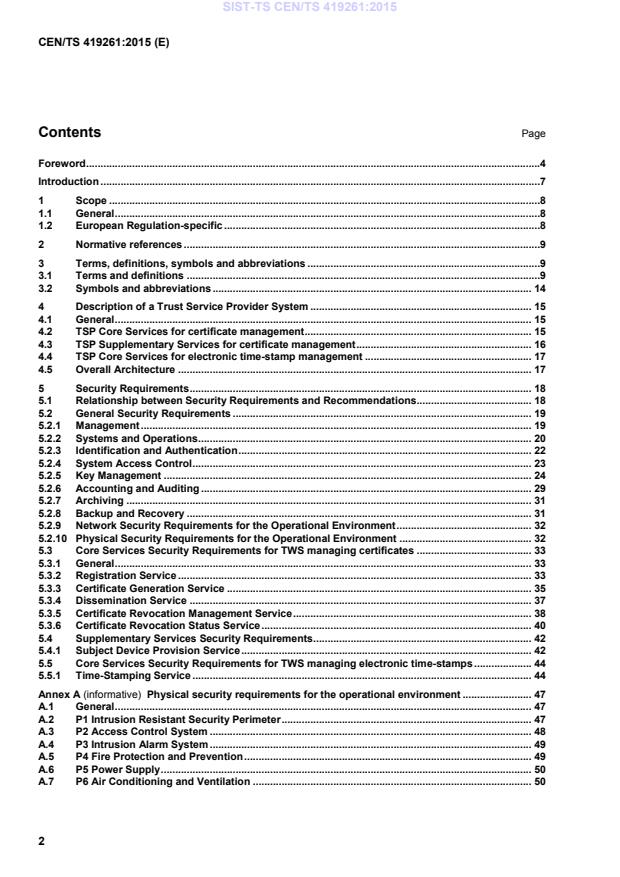
Contents Page
Foreword .4
Introduction .7
1 Scope .8
1.1 General .8
1.2 European Regulation-specific .8
2 Normative references .9
3 Terms, definitions, symbols and abbreviations .9
3.1 Terms and definitions .9
3.2 Symbols and abbreviations . 14
4 Description of a Trust Service Provider System . 15
4.1 General . 15
4.2 TSP Core Services for certificate management . 15
4.3 TSP Supplementary Services for certificate management . 16
4.4 TSP Core Services for electronic time-stamp management . 17
4.5 Overall Architecture . 17
5 Security Requirements . 18
5.1 Relationship between Security Requirements and Recommendations. 18
5.2 General Security Requirements . 19
5.2.1 Management . 19
5.2.2 Systems and Operations . 20
5.2.3 Identification and Authentication . 22
5.2.4 System Access Control . 23
5.2.5 Key Management . 24
5.2.6 Accounting and Auditing . 29
5.2.7 Archiving . 31
5.2.8 Backup and Recovery . 31
5.2.9 Network Security Requirements for the Operational Environment . 32
5.2.10 Physical Security Requirements for the Operational Environment . 32
5.3 Core Services Security Requirements for TWS managing certificates . 33
5.3.1 General . 33
5.3.2 Registration Service . 33
5.3.3 Certificate Generation Service . 35
5.3.4 Dissemination Service . 37
5.3.5 Certificate Revocation Management Service . 38
5.3.6 Certificate Revocation Status Service . 40
5.4 Supplementary Services Security Requirements . 42
5.4.1 Subject Device Provision Service . 42
5.5 Core Services Security Requirements for TWS managing electronic time-stamps . 44
5.5.1 Time-Stamping Service . 44
Annex A (informative) Physical security requirements for the operational environment . 47
A.1 General . 47
A.2 P1 Intrusion Resistant Security Perimeter . 47
A.3 P2 Access Control System . 48
A.4 P3 Intrusion Alarm System . 49
A.5 P4 Fire Protection and Prevention . 49
A.6 P5 Power Supply . 50
A.7 P6 Air Conditioning and Ventilation . 50
Annex B (informative) Network Security Requirements for the Operational Environment . 52
B.1 General . 52
B.2 NET1 Protected TWS Architecture . 52
B.3 NET2 Logging . 53
B.4 NET3 Monitoring and Alerting . 53
Bibliography . 55
Foreword
This document (CEN/TS 419261:2015) has been prepared by Technical Committee CEN/TC 224 “Personal
identification, electronic signature and cards and their related systems and operations”, the secretariat of
which is held by AFNOR.
This document has been prepared under a mandate given to CEN by the European Commission and the
European Free Trade Association.
Successful implementation of European Directive 1999/93/EC on a Community framework for electronic
signatures [Dir.1999/93/EC] and of REGULATION (EU) No 910/2014 OF THE EUROPEAN PARLIAMENT
AND OF THE COUNCIL of 23 July 2014 on electronic identification and trust services for electronic
transactions in the internal market and repealing Directive 1999/93/EC [Reg.910/2014/EU] requires standards
for services, processes, systems and products related to electronic signatures as well as guidance for
conformity assessment of such services, processes, systems and products.
NOTE According to Article 50 of Reg.910/2014/EU Directive 1999/93/EC is repealed with effect from 1 July 2016 and
references to the repealed Directive shall be construed as references to the Regulation.
In 1999 the European Information and Communications Technologies Standards Board, with the support of
the European Commission, undertook an initiative bringing together industry and public authorities, experts
and other market players, to create the European Electronic Signature Standardization Initiative (EESSI).
Within this framework the Comité Européen de Normalization / Information Society Standardization System
(CEN/ISSS) and the European Telecommunications Standards Institute / Electronic Signatures and
Infrastructures (ETSI/ESI) were entrusted with the execution of a work programme to develop generally
recognized standards to support the implementation of [Dir.1999/93/EC] and development of a European
electronic signature infrastructure.
The CEN/ISSS Workshop on electronic signatures (WS/E-SIGN) resulted in a set of deliverables, CEN
Workshop Agreements (CWA), which contributed towards those generally recognized standards.
In 2011 the European Commission (EC) with the support of the European Free Trade Association has signed
a specific grant agreement with the European Committee for Standardization (CEN) regarding the update of
the existing European e-Signature CEN Workshop Agreements (CWAs) in the framework of Phase 1 of the
mandate M/460. The present document is such a CEN Workshop Agreement that was first created as a CWA
and then updated into a Technical Specification (TS).
The purpose of this TS is to describe the security requirements for trustworthy systems managing certificates
for electronic signatures and to define overall system security requirements, whereas EN 419221 specifies
security requirements for cryptographic devices. The requirements were partly inspired by Common Criteria
[CC] Part 2, but the TS is not compliant to [CC], as e.g. EN 419221. In consequence, this TS cannot be used
to perform Common Criteria certifications of products.
The TS is intended for use by designers and developers of systems managing certificates and time-stamps,
as well as customers of such systems.
Executive Summary
This Technical Specification specifies security requirements on products and technology components, used by
Trust Service Providers (TSPs) for issuing and managing certificates as well as electronic time-stamps in the
sense of the REGULATION (EU) No 910/2014 OF THE EUROPEAN PARLIAMENT AND OF THE COUNCIL
of 23 July 2014 on electronic identification and trust services for electronic transactions in the internal market
and repealing Directive 1999/93/EC [Reg.910/2014/EU].
The term TSP includes certification service providers (CSPs) issuing qualified certificates as defined in the
Directive “Directive 1999/93/EC of the European Parliament and of the Council of 13 December 1999 on a
community framework for electronic signatures” [Dir.1999/93/EC]. These certificates are used in conjunction
with electronic signatures and advanced electronic signatures in accordance with Directive 1999/93/EC
[Dir.1999/93/EC]. Additionally, electronic time-stamps issued by a TSP provide evidence that the stamped
data existed at a given time.
This Technical Specification contains the same requirements for TWS used by CSPs according to
[Dir.1999/93/EC] and for TWS used by TSPs according to [Reg.910/2014/EU]. However, [Reg.910/2014/EU]
allows TSPs to manage electronic time-stamps without managing certificates. This is not allowed for CSPs
according to [Dir.1999/93/EC]. Therefore, this Technical Specification distinguishes between CSPs and TSPs
with respect to the provided services where necessary.
TSPs need to use Trustworthy Systems (TWSs) for securely providing the following services, which are
defined in this TS:
a) Registration Service - to verify the identity and, if applicable, any specific attributes of a subject;
b) Certificate Generation Service - to create certificates;
c) Dissemination Service - to provide certificates and policy information to subjects and relying parties;
d) Revocation Management Service - to allow the processing of revocation requests;
e) Revocation Status Service - to provide certificate revocation status information to relying parties;
f) Subject Device Provision Service – to prepare and provide a Signature Creation Device (SCDev) to
subjects. This includes Qualifed electronic Signature and Seal Creation Device (QSCD) provision;
g) Time-stamping Service – provides a Time-stamping Service which may be needed for signature
verification purposes.
TSP shall follow:
h) “General Security Requirements” specified in 5.2 that are applicable to all previously mentioned services;
i) Security requirements specified in 5.3, 5.4 and 5.5 that are specific to some of the previously mentioned
services.
In accordance with Directive1999/93/EC, CSPs need to establish and maintain the first five core services
relevant for the issuance and management of qualified certificates (Registration Service, Certificate
Generation Service, Dissemination Service, Revocation Management Service, and Revocation Status
Service). The other two services (Subject Device Provision Service and Time-stamping Service) are optional
ones and are not required to be established and maintained by CSPs, because of having not being specifically
addressed in Directive1999/93/EC.
TSPs managing certificates and operating in accordance with Regulation (EU) No 910/2014
[Reg.910/2014/EU] will need to establish and maintain the first five core services relevant for the issuance and
management of qualified certificates (Registration Service, Certificate Generation Service, Dissemination
Service, Revocation Management Service, and Revocation Status Service). The Subject Device Provision
Service is an optional service for such a TSP. TSP managing electronic time-stamps need to establish and
maintain the Time-stamping Service relevant for the issuance and management of electronic time-stamps.
TSPs issuing:
j) Certificates according to ETSI/TS 119 411-1 or TS 119 411-2 (or equivalent ENs to be subsequently
published) and/or
k) Time-stamps according to ETSI/TS 119 421 (or equivalent EN to be subsequently published)
may use TWSs that have been independently assessed against the relevant security requirements defined in
this Technical Specification and declared as being compliant to these requirements. In this case, TSP may
reduce their burden to establish conformance of their policy to the relevant standards and in meeting the
requirements of Dir.1999/93/EC and/or [Reg.910/2014/EU].
Guidance for conformity assessment to the security requirements defined in this TS can be found in
CWA 14172-3.
According to the CEN-CENELEC Internal Regulations, the national standards organizations of the following
countries are bound to implement this Technical Specification: Austria, Belgium, Bulgaria, Croatia, Cyprus,
Czech Republic, Denmark, Estonia, Finland, Former Yugoslav Republic of Macedonia, France, Germany,
Greece, Hungary, Iceland, Ireland, Italy, Latvia, Lithuania, Luxembourg, Malta, Netherlands, Norway, Poland,
Portugal, Romania, Slovakia, Slovenia, Spain, Sweden, Switzerland, Turkey and the United Kingdom.
Introduction
The European Directive 1999/93/EC and the Regulation (EU) No 910/2014 [Reg.910/2014/EU] establish a
framework of requirements for the use of electronic signatures which are legally equivalent to hand-written
signatures. This is the case for “advanced electronic signatures” which are based on a “qualified certificate”
and which are created by a “secure-signature-creation device” according to Article 5.1 of 1999/93/EC and
qualified signatures according to Article 25.2 of [Reg.910/2014/EU].
In particular, Annex II of Dir. 1999/93/EC and Article 24.2 (e) of [Reg.910/2014/EU] provide the requirements
to be followed by TSP when issuing qualified certificates (QCs) and qualified TSP providing qualified trust
services. More specifically, they shall
• use trustworthy systems and products which are protected against modification and ensure the technical
security of the processes supported by them.
This Technical Specification defines security requirements for TWSs within the scope of the services a TSP
needs to provide. It is assumed that TWSs being compliant to relevant security requirements of this TS may
be adopted by TSPs to reduce their effort in deploying systems meeting Dir.1999/93/EC and/or
[Reg.910/2014/EU]. This approach should support industry in developing systems which meet the
requirements laid down in Annex II (f) of Dir.1999/93/EC and in Article 24.2 (e) of [Reg.910/2014/EU].
ETSI TS 119 411-1, 119 411-2, and 119 421 have been taken into account as reference. As a consequence,
TWSs already compliant to relevant security requirements of this TS will require minimal configuration by
TSPs using them, to meet the security requirements for TWS defined in ETSI TS 119 411-1, 119 411-2, and
119 421 (or equivalent ENs to be subsequently published). In addition, compliant TWS may be used by
different TSPs without the need to repeat the conformity assessment.
TWSs for TSPs managing certificates shall comply with the security requirements defined in 5.2 and 5.3 to
support TSPs in providing the following core services:
a) Registration of subject information (Registration Service);
b) Certificate generation (Certificate Generation Service);
c) Certificate dissemination (Dissemination Service);
d) Certificate revocation management (Revocation Management Service);
e) Certificate revocation status provision (Revocation Status Service).
TWS for TSPs managing certificates may comply with the other security requirements defined in 5.4 and 5.5
to support TSPs in providing the following supplementary services:
f) SCDev / QSCD production (Subject Device Provision Service);
g) Time-stamping functions (Time-Stamping Service).
TWS for TSPs managing electronic time-stamps shall comply with requirements defined in 5.5 to provide the
Time-Stamping Service and may provide the other services, either a) – e) or a) – f) and comply with the
corresponding requirements, defined in 5.2 and 5.3 or 5.2, 5.3, and 5.4, respectively.
All security requirements defined in this TS are either:
h) mandatory (indicated by SHALL (NOT) or SHALL (NOT));
i) recommended (indicated by SHOULD (NOT) or (NOT) RECOMMENDED); or
j) optional (MAY or MAY (NOT)).
1 Scope
1.1 General
This Technical Specification establishes security requirements for TWSs that can be used by a TSP in order
to issue QCs and Non-Qualified Certificates (NQCs) as well as electronic time-stamps in accordance with
Dir.1999/93/EC and with [Reg.910/2014/EU].
Security requirements for the Subject Device Provision Service, which includes SCDev/QSCD provision to
subjects, are defined in this TS. However, requirements specific to SCDev/QSCD devices, as used by
subjects of the TSP, are outside the scope of this TS. These requirements are defined as Common Criteria
[CC] Protection Profiles (PP) in the EN 419211 series.
Recommendations for the cryptographic algorithms to be supported by TWSs are provided in
ETSI/TS 119 312.
Although this TS is based on the use of public key cryptography, it does not require or define any particular
communication protocol or format for electronic signatures, certificates, certificate revocation lists, certificate
status information and time-stamp tokens. It only assumes certain types of information to be present in the
certificates in accordance with Annex I of Dir.1999/93/EC and of [Reg.910/2014/EU]. Interoperability between
TSP systems and subject systems is outside the scope of this document.
The use of TWSs that are already compliant to relevant security requirements of this TS should support TSPs
in reducing their burden to establish conformance of their policy to ETSI TS 119 411-1, 119 411-2, and
119 421 (or equivalent ENs to be subsequently published) and in meeting the Annex I and Annex II
requirements of Dir.1999/93/EC as well as the requirements from Annex I and Article 24.2 (e) of
[Reg.910/2014/EU].
1.2 European Regulation-specific
The main focus of this document is on the requirements in Article 24.2 (e) of [Reg.910/2014/EU] whilst still
facilitating the meeting of requirements in Dir.1999/93/EC, Annex II (f). In considering [Reg.910/2014/EU] it is
important to take into account the following requirements of particular relevance to TSP trustworthy systems:
a) Article 24.2 (f) – “use trustworthy systems to store data provided to it, in a verifiable form so that:
(i) they are publicly available for retrieval only where the consent of the person to whom the data
relates has been obtained,
(ii) only authorised persons can make entries and changes to the stored data,
(iii) the data can be checked for authenticity”;
b) Article 24.2 (g) – “take appropriate measures against forgery and theft of data”;
c) Article 24.2 (h) – “record and keep accessible for an appropriate period of time, including after the
activities of the qualified trust service provider have ceased, all relevant information concerning data
issued and received by the qualified trust service provider, in particular, for the purpose of providing
evidence in legal proceedings and for the purpose of ensuring continuity of the service. Such recording
may be done electronically”;
d) Article 24.2 (j) – “ensure lawful processing of personal data in accordance with Directive 95/46/EC”;
e) Article 24.2 (k) – “in case of qualified trust service providers issuing qualified certificates, establish and
keep updated a certificate database”;
f) Article 24.3 – “If a qualified trust service provider issuing qualified certificates decides to revoke a
certificate, it shall register such revocation in its certificate database and publish the revocation status of
the certificate in a timely manner, and in any event within 24 hours after the receipt of the request. The
revocation shall become effective immediately upon its publication”;
g) Article 24.4 – "With regard to paragraph 3, qualified trust service providers issuing qualified certificates
shall provide to any relying party information on the validity or revocation status of qualified certificates
issued by them. This information shall be made available at least on a per certificate basis at any time
and beyond the validity period of the certificate in an automated manner that is reliable, free of charge
and efficient”;
h) Article 42.1 – “A qualified electronic time stamp shall meet the following requirements:
(i) it binds the date and time to data in such a manner as to reasonably preclude the possibility of
the data being changed undetectably;
(b) it is based on an accurate time source linked to Coordinated Universal Time; and
(c) it is signed using an advanced electronic signature or sealed with an advanced electronic seal of
the qualified trust service provider, or by some equivalent method”;
i) Annexes I, III, IV – requirements on data in qualified certificates
2 Normative references
The following documents, in whole or in part, are normatively referenced in this document and are
indispensable for its application. For dated references, only the edition cited applies. For undated references,
the latest edition of the referenced document (including any amendments) applies.
EN 419211 (all parts), Protection profiles for secure signature creation device
ETSI TS 119 411-1, Electronic Signatures and Infrastructures (ESI); Policy and security requirements for Trust
Service Providers issuing certificates; Part 1: General Requirements
ETSI TS 119 411-2, Electronic Signatures and Infrastructures (ESI); Policy and security requirements for Trust
Service Providers issuing certificates; Part 2: Policy Requirements for trust service providers issuing EU
qualified certificates
ETSI TS 119 421, Electronic Signatures and Infrastructures (ESI); Policy and security requirements for Trust
Service Providers issuing Electronic Time-Stamps
NOTE Equivalent ENs will be published in 2015.
3 Terms, definitions, symbols and abbreviations
3.1 Terms and definitions
For the purposes of this document, the following terms and definitions apply.
3.1.1
activation data
data values, other than keys, that are required to operate cryptographic devices and that need to be protected
(e.g., a PIN, a passphrase, or a manually-held key share)
[SOURCE: RFC 3647:2014, Clause 2]
3.1.2
advanced electronic signature
electronic signature which meets the following requirements:
a) it is uniquely linked to the signatory;
b) it is capable of identifying the signatory;
c) it is created using means that the signatory can, with a high level of confidence, use under his sole
control; and
d) it is linked to the data signed therewith in such a way subsequent change in the data is detectable
[SOURCE: Reg.910/2014/EU]
3.1.3
authentication data
data used to verify the claimed identity of a user requesting services from TWS
3.1.4
certificate
electronic attestation which links signature-validation-data to a person and confirms the name or the
pseudonym of that person
[SOURCE: Reg.910/2014/EU]
3.1.5
certificate generation service
service that creates and signs certificates based on the identity and other attributes verified by the registration
service
3.1.6
certificate policy
named set of rules that indicates the applicability of a certificate to a particular community and/or class of
application with common security requirements.
[SOURCE: ISO/IEC 9594-8:2014, 3.5.10 ITU-T X.509; modified — An example in the original definition has
not been included here.]
3.1.7
certification authority
CA
authority trusted by one or more users to create and assign certificates and which optionally may create the
users’ keys
[SOURCE: ISO/IEC 9594-8:2014, 3.5.16; ITU-T X.509, modified — The definition has been altered.]
3.1.8
certification-service-provider
entity or a legal or natural person who issues certificates or provides other services related to electronic
signatures
[SOURCE: Dir.1999/93/EC]
3.1.9
cryptographic device
hardware-based cryptographic device that generates stores and protects cryptographic keys and provides a
secure environment for the execution of cryptographic functions
3.1.10
digital signature
data appended to, or a cryptographic transformation (see cryptography) of, a data unit that allows a recipient
of the data unit to prove the source and integrity of the data unit and protect against forgery e.g. by the
recipient
[SOURCE: ISO 7498-2:1989, 3.3.26]
3.1.11
dissemination service
service that disseminates certificates to subjects, and if the subject consents, to relying parties and that also
disseminates the CA’s policy & practice information to subjects and relying parties
3.1.12
electronic seal
data in electronic form, which is attached to or logically associated with other data in electronic form to ensure
the latter’s origin and integrity
[SOURCE: Reg.910/2014/EU]
3.1.13
electronic signature
data in electronic form which is attached to or logically associated with other data in electronic form and which
is used by the signatory to sign
[SOURCE: Reg.910/2014/EU]
3.1.14
electronic signature / seal creation device
configured software or hardware used to create an electronic signature / seal
[SOURCE: Reg.910/2014/EU]
3.1.15
end-entity
certificate subject which uses its private key for purposes other than signing certificates
[SOURCE: ISO/IEC 9594-8:2014, 3.5.26; ITU-T X.509, modified — One out two possible definitions in the
original text has been retained here.]
3.1.16
hash function
function which maps string of bits to fixed-length strings of bits, satisfying the following two properties:
a) it is computationally infeasible to find for a given output an input which maps to this output;
b) it is computationally infeasible to find for a given input a second input which maps to the same output.
[SOURCE: ISO/IEC 10118-1:2000, 3.5; modified — A note that was part of the original definition is not kept
here.]
3.1.1715
nonce
randomly-generated value used in a communication protocol to ensure old messages cannot be reused in
replay attacks
3.1.18
private key
key of an entity's asymmetric key pair which should only be used by that entity
[SOURCE: ISO/IEC 9798-1:2010, 3.22; modified — A small part of the original definition has been cut.]
3.1.19
public key
key of an entity’s asymmetric key pair which can be made public
[SOURCE: ISO/IEC 9798-1:2010, 3.25]
3.1.20
qualified certificate
certificate that is issued by a qualified trust service provider and which meets the requirements laid down in
Annex I of Reg.910/2014/EU
[SOURCE: Reg.910/2014/EU]
3.1.21
qualified electronic signature
advanced electronic signature that is created by a qualified signature / seal creation device and which is
based on a qualified certificate
[SOURCE: Reg.910/2014/EU]
3.1.22
qualified electronic signature / seal creation device
electronic signature creation device that meets the requirements laid down in Annex II of Reg.910/2014/EU
[SOURCE: Reg.910/2014/EU]
3.1.23
registration service
service that verifies the identity and, if applicable, any specific attributes of a subject, and the results of which
are passed to the Certificate Generation Service
3.1.24
relying party
user or agent that relies on the data in a certificate in making decisions
[SOURCE: RFC 5280:2008]
3.1.25
revocation management service
service that processes requests and reports relating to revocation to determine the necessary action to be
taken, and the results of which are distributed through the Revocation Status Service
3.1.26
revocation status service
service that provides certificate revocation status information to relying parties and that may be a real-time
service or may be based on revocation status information which is updated at regular intervals
3.1.27
secure-signature-creation device
signature-creation device which meets the requirements laid down in Annex III of Dir.1999/93/EC
[SOURCE: Dir.1999/93/EC]
3.1.28
security perimeter
one or more areas that are not necessarily co-located, where TWS are sited with relevant ancillary equipment
(power supply, air conditioning, access control system, intrusion alarm system, fire protection and prevention
system)
3.1.29
security policy
set of rules laid down by the security authority governing the use and provision of security services and
facilities
[SOURCE: ISO/IEC 9594-8:2014, 3.5.60; ITU-T X.509]
3.1.30
self-signed certificate
certificate for one CA signed by that CA
[SOURCE: RFC 5280:2008]
3.1.31
signatory
person who creates an electronic signature
Note 1 to entry: The term signer is sometimes used as a synonym.
[SOURCE: Reg.910/2014/EU]
3.1.32
signature-creation data
unique data which is used by the signatory to create an electronic signature
[SOURCE: Dir.1999/93/EC and Reg.910/2014/EU]
3.1.33
signature-creation device
configured software or hardware used to create an electronic signature
[SOURCE: Reg.910/2014/EU]
3.1.34
subject
entity identified in a certificate as the holder of the private key associated with the public key given in the
certificate
3.1.35
subject device provision service
service that prepares and provides a Signature Creation Device to subjects
3.1.36
trustworthy system
information system or product implemented as either hardware and/or software that produces reliable and
authentic records which are protected against modification and additionally ensures the technical and
cryptographic security of the processes supported by it
3.1.37
time-stamp token
data object that binds a representation of a datum to a particular time, thus establishing evidence that the
datum existed before that time
3.1.38
time-stamping service
service that generates and provides time-stamp tokens
3.1.39
TSP IT network systems
IT network systems consisting of network components such as firewalls, routers, switches and cabling
3.1.40
validation data
data, that is used to validate an electronic signature or an electronic seal
[SOURCE: Reg.910/2014/EU]
3.2 Symbols and abbreviations
For the purposes of this document, the following symbols and abbreviations apply.
ARL Authority Revocation List
CA Certification Authority
CC Common Criteria
CEN Comité Européen de Normalisation (European Committee for
Standardization)
CEN/ISSS CEN Information Society Standardization System
CP Certificate Policy
CRL Certificate Revocation List
CSP Certification Service Provider
EC European Commission
EN European Norm
EESSI European Electronic Signature Standardization Initiative
ETSI European Telecommunications Standards Institute
ISSS Information Society Standardization System
NQC Non-Qualified Certificate
OCSP Online Certificate Status Protocol
OS Operating System
PKI Public Key Infrastructure
PP Protection Profile
QC Qualified Certificate
QSCD Qualified electronic Signature / Seal Creation Device
SCDev Signature-Creation Device
TS Technical Specification
TSA Time-Stamping Authority
TSP Trust Service Provider
TSS Time-Stamping Service
TST Time-Stamp Token
TWS Trustworthy System
UPS Uninterruptable Power Supply
UTC Coordinated Universal Time
WORM Write Once Read Many
WS/E-SIGN CEN/ISSS Electronic Signatures workshop
4 Description of a Trust Service Provider System
4.1 General
A Trust Service Provider (TSP), within this specification, provides and manages certificates used for the
support of electronic signatures, prepares signature creation devices and/or issues time-stamp tokens. It is a
primary assumption that a TSP will use a Public Key Infrastructure (PKI) for the management of certificates.
The approach adopted in this specification is for a TSP to offer a number of services, each service having
defined functions to facilitate service delivery. Each defined function is required to meet minimum security
standards thus achieving trustworthy status.
The TSP’s TWSs may consist of a number of subsystems each providing specific TSP services. Although this
specification considers security requirements for the subsystems involved in the TSP’s service, the aim is to
provide the subject (signatory) and relying party a single view of the TSP and hence a single view of the
TWSs employed by it. To ensure this, the customer interface, in this specification, is to the ‘TSP Service’ and
not directly to the individual services offered by the TSP. As subsystems are further decomposed any
functionality defined by other acceptable standards has been referenced.
In the context of the present document, a TSP SHALL provide its services by deploying TWSs that SHOULD
be assessed beforehand to be compliant to this TS. TSPs SHALL implement relevant core services as
described in section 4.2 when managing certificates and core services as described in section 4.4 when
managing electronic time-stamps. A TSP may choose to implement any supplementary or additional service
as deemed necessary by national, business and market requirements. However, if a TSP managing
certificates implements the optional Subject Device Provision Service the TSP SHALL implement the General
Security Requirements in 5.2 plus all security requirements for that service as specified in 5.4.
TWSs used for issuing and managing certificates are required to fulfil the General Security Requirements in
5.2 as well as specific Core Services Security Requirements in 5.3, and if applicable Supplementary Services
Security Requirements in 5.4. TWSs used for issuing and managing electronic time-stamps are required to
fulfil the General Security Requirements in 5.2 as well as specific Core Services Security Requirements in 5.3.
In summary, a TSP SHALL deploy TWSs meeting all General and Core Security Requirements. It is important
to note that this technical/security integration does not necessarily impede on the freedom of the TSP to run
the different components of the service using different business entities.
4.2 TSP Core Services for certificate management
The core services for certificate management a TSP MAY provide and that CSPs in accordance to
Dir.1999/93/EC and TSPs managing certificates in accordance to Reg.910/2014/EU SHALL implement are:
— Registration Service: verifies the identity and, if applicable, any specific attributes of a subject. The
results of this service are passed to the Certificate Generation Service.
— Certificate Generation Service: creates and signs certificates based on the identity and other attributes
of a subject as verified by the Registration Service.
— Dissemination Service: disseminates certificates to the CA, certificates to subjects, and if the subject
consents, to relying parties. This service also disseminates the CA's policy and practice information to
subjects and relying parties.
— Revocation Management Service: processes requests and reports relating to revocation and
suspension (if used) to determine the necessary action to be taken. The results of this service are
distributed through the Revocation Status Service.
— Revocation Status Service: provides certificate revocation status information to relying parties. This
service may be a real-time service or may be based on revocation status information which is updated at
regular intervals.
The figure below shows the relationship between the Revocation Management Service and the Revocation
Status Service. In the figure, message A updates the TSP Certificate Status Database whereas Message B is
either data ‘pushed’ to the Revocation Status Service or is a query/response message.
Figure 1 — Messaging between Revocation Management Service and Revocation Status Service
4.3 TSP Supplementary Services for certificate management
The supplementary service a TSP managing certificates in accordance to Reg.910/2014/EU may provide is:
Subject Device Provision Service: Prepares and provides a Signature Creation Device (SCDev) to subjects.
NOTE Examples of this service are:
a) a service which generates the subject’s key pair and distributes the private key to the subject;
b) a service which prepares the subject’s QSCD and device enabling codes and distributes the QSCD to the
registered subject.
It is important to note that this service may provide a SCDev and/or a QSCD. Within this document the
security requirements applicable to SCDevs are equally applicable to QSCDs, where QSCDs meet the
additional requirements stated in Annex III of Dir.1999/93/EC and in Annex II of Reg.910/2014/EU. No
distinction is made whether the SCDev/QSCD is implemented in hardware or software.
4.4 TSP Core Services for electronic time-stamp management
The core service for electronic time-stamp management a TSP MAY provide and that TSP managing
electronic time-stamps in accordance to Reg.910/2014/EU SHALL implement are:
Time-Stamping Service: a third party, trusted to generate and provide time-stamp tokens. A time-stamp
token provides evidence that a data item existed before a certain point of time.
Within this document, security requirements are only provided for the time-stamping service, which
cryptographically binds time values to
...

Questions, Comments and Discussion
Ask us and Technical Secretary will try to provide an answer. You can facilitate discussion about the standard in here.
Loading comments...